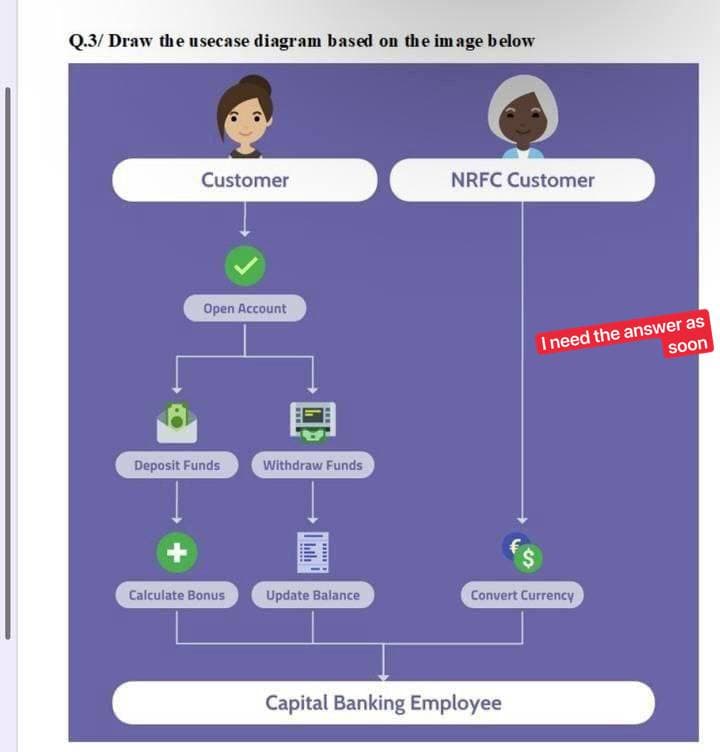
Q.3/Draw the usecase diagram based on the image below Customer Open Account Deposit Funds Withdraw Funds + 414 NRFC Customer I need the answer as soon
Q: Kindly provide us with three specific examples of how the procedures involved in running a company…
A: Below are three examples where a company is benefitted from cloud computing. 1. Helps in scaling up…
Q: Is it possible to tell the difference between deadlock prevention and deadlock avoidance?
A: A deadlock arises when a group of processes each has a resource and waits for a resource held by…
Q: Q1/ Talk in details about functions of MIS in school
A: Introduction: MIS stands for management information system and is a focal information vault equipped…
Q: Can you explain what the difference is between the constrained and unbounded version of the stack?
A: Stack: Stack is a linear data structure that adheres to a predefined insertion and deletion order…
Q: Don't only make a case based on speed; explain why deep access is better than shallow access from…
A: Given: Only when a procedure can be sent as an argument to a function does deep/shallow binding make…
Q: If you're doing any Web testing, you should know the distinction between Authorization and…
A: Web testing is process of testing all elements of web page based system. At admin level access,…
Q: Examine the differences and similarities between Governance and Management with regard to IT…
A: Given: The governance function of an organisation is the part of the organisation that is…
Q: C# language Create a Product class then create an object from that class using User Input. The…
A: Below is the program implementation in C# with driver code which generates the required output.…
Q: One of the key ideas that guides software engineering practice is "divide and conquer," where…
A: Split and Conquer is an algorithmic pattern. The architecture is algorithmically built to handle a…
Q: They are entirely reliant on firewalls, which are an essential component of both the security of…
A: Introduction A firewall is a network security device that monitors and filters incoming and outgoing…
Q: Which access control approach controls a user's access to the exact information required to execute…
A: POLP should be the right answer. Now I'll go through it in more depth. Check it out: POLP)…
Q: 1) Write a C++ program that use the OOD to define and implements the class Robot1DType. The Class…
A: As per question statement, We need to write c++ program to create given class. As per bartleby…
Q: Q.1/Draw an activity diagram for the following scenario: Passenger who needs to purchase a travel…
A: Answer has been explained below:-
Q: Write a C++ Class to read marks of seven subjects and calculate total, average and percentage.
A: here in given question ask for program in c++ which find sum,average and percentage of 7 subject's…
Q: Think about the benefits and drawbacks of using the cloud for your computer. A migration to the…
A: The above question is solved in step 2 :-
Q: Java's method parameters are supplied by value rather than via reference. What exactly does this…
A: All object references in Java are passed by value.
Q: d be a data structure or an ADT. Explain what this means. (How ca
A: Introduction: Searching and sorting are the most common tree uses, but a graph has a network model.…
Q: A computer's malleability enables it to do information creation and analysis in a variety of…
A: Given: Computers process information as humans do.CPU is a computer's brain. The CPU runs the…
Q: Learn what a file extension is and what function it serves in the document you're working on. This…
A: A file extension can be categorized as a type of metadata.
Q: 5. WAP that inputs the size and elements of a 2-D array and checks if the array is row-magic (this…
A: Write a C++ program that inputs the size and elements of a 2-D array and checks if the array is…
Q: What are some of the reasons for the popularity of alternative computer architecture gaming…
A: The solution to the given question is: Because computer architecture handle the way for…
Q: What are some of the technological advantages that a company may benefit from by selling their items…
A: There are a number of technical benefits to selling a product on Amazon rather than on one's own…
Q: What is a model of a perceptron network? How could a model like this be used to do simple linear…
A: There are neural network units called perceptrons that do specific calculations to uncover hidden…
Q: Why are alternative computer architecture gaming programs so popular?
A: In gaming applications dual bus architecture with microprocessor is mostly used, in gaming is all…
Q: What's the difference between privileged commands and user-level commands?
A: Find the required answer given as below :
Q: What types of obstacles do cloud-based businesses face? Is there an advantage or disadvantage to…
A: Could based businesses are growing like never before. With rise in cloud computing technologies and…
Q: Balance Symbol Checker CLOSE RETRY Tags: Stack Problem Description Compilers check your programs for…
A:
Q: Find five elements that have led to the growth of business-to-consumer them briefly. (B2C) internet…
A: 1. Mobile inflexibility Smartphones and tablets, which fuel ecommerce transactions, constitute a…
Q: Describe the hosting mechanism used for cloud-based services and applications.
A: Given: Cloud hosting is all about using cloud resources to improve the accessibility of services,…
Q: What are the most important responsibilities of the Compiler Phases? Provide some instances for each…
A: Introduction: Passes refer to the number of times the compiler traverses the source code, whereas…
Q: Give one example for each type of associations in the domain of class diagram. Show you answers on…
A: Classes are interrelated to each other in specific ways. In particular, relationships in class…
Q: Is there any way to avoid having to build your own data center and stock it with either Windows or…
A: What is the definition of an in-house data center? When a firm keeps its own servers, networking…
Q: What precautions can you take to protect your computer from being harmed by power surges, and what…
A: Power surges are sudden increases in the amount of energy provided to typical equipment; when this…
Q: What are the company's protocols for disclosing information in the case of a security breach?
A: Given: These individual notifications must be made without undue delay and no later than 60 days…
Q: What makes multicore architecture unique in comparison to other types of architectures
A: A multicore architecture is one whereby a single physical processor comprises the logic cores of…
Q: Which of the two operating systems, Linux or Windows, do you believe has a simpler method for…
A: Linux is a free and open-source operating system, whereas Microsoft Windows is a paid-for system.…
Q: Q.1/Draw an activity diagram for the following scenario: Passenger who needs to purchase a travel…
A: Let's see the diagram in the next steps
Q: What does it imply precisely when someone refers to a "storage area network system"?
A: Given: We have to discuss What does it imply precisely when someone refers to a "storage area…
Q: What are the primary responsibilities of each Phase of the Compiler, and how do they carry out their…
A: Prpose of a compiler: A compiler is a software program that transforms high-level source code that…
Q: What, exactly, does it mean when someone talks about "system security"?
A: A computer system's security is a critical duty. It is a procedure for protecting the…
Q: What security strategy would lessen purposeful attacks if there was no division of responsibilities…
A: let us see the answer:- Introduction:- if there was no division of responsibilities or required…
Q: Is the run-time of a multi-threaded program faster than a single-threaded program?
A: => The Answer is in step-2.
Q: What exactly is an ADT, and how does it carry out the tasks that are assigned to it? Is there a…
A: Type of Abstract Data: The abstract data type (ADT) is a mathematical construct that may represent a…
Q: Show the output of the following code: String array = {"red", "green", "blue"}; ArrayList list = new…
A: In the above code, we are adding "red" at 0 index of the list so output of the code will be
Q: Although Microsoft has ended support for Windows Server, it is estimated that hundreds of thousands…
A: Windows 10 released in the 2021 year, and then windows server 2019 was reached the end of service.…
Q: What kind of information is essential for the ExitProcess method to have?
A: Introduction: Exit Process should: Once all connected DLLs have finished their process termination…
Q: What is the purpose of a virtual private network (VPN) and how does it work
A: Your answer is given below. Introduction :- A virtual private network (VPN) creates a secure…
Q: Why are operating systems important and how do they operate? The batch operating system may be…
A: answer is
Q: Describe the differences, advantages, and limitations of cloud computing (e.g.,…
A: Find the required answer given as below :
Q: Make a case for why you should use deep access instead of shallow access from the standpoint of a…
A: Make a case for why you should use deep access instead of shallow access from a programmer's…
Types of Loop
Loops are the elements of programming in which a part of code is repeated a particular number of times. Loop executes the series of statements many times till the conditional statement becomes false.
Loops
Any task which is repeated more than one time is called a loop. Basically, loops can be divided into three types as while, do-while and for loop. There are so many programming languages like C, C++, JAVA, PYTHON, and many more where looping statements can be used for repetitive execution.
While Loop
Loop is a feature in the programming language. It helps us to execute a set of instructions regularly. The block of code executes until some conditions provided within that Loop are true.
Step by step
Solved in 2 steps with 1 images

- Create/draw an ERD for the following: 1) During some period of time, a customer can download many ebooks from Books Online. Each of the ebooks can be downloaded by many customers during that period of time. 2) An airliner can be assigned to fly many flights, but each flight is flown by only one airliner.HOW WOULD I SET UP THIS CODE AS A (FLOW CHART) LAYOUT. I NEED TO GET THIS PYTHON CODE AND SET UP A FLOW CHART FOR IT. class Patient: def __init__(self,fname,mname,lanme,zipcode,phone,addess,city,state): self.firstName = fname self.middleName = mname self.lastName = lanme self.zip = zipcode self.phoneNumber=phone self.add = addess self.city = city self.state = state def __str__(self): return "Name: " +self.firstName+ " "+ self.middleName +" "+self.lastName+"\n"+"Address: "+self.add+" city: "+self.city class Procedure: def __init__(self, procedure, date, practitioner, charges): self.procedureName = procedure self.procedureDate = date self.practitionerName = practitioner self.charg = charges def __str__(self): x= float(eval(str(self.charg))) return "Procedure Name: "+ self.procedureName+"\nDate: "+ self.procedureDate+"\nPractioner: "+…Q1)Write a program to create a GUI application class named CustomerRegistration byextending the JFrame class as shown in Figure 1.
- create a code about supermarket inventory system using c++ a. supermarket inventory b. supermarket employee report c. supermarket billing system(POS-point of sale) d. promotions and senior citizen discountsPlease do it in c++ as soon as possible.Little Johnny Bubbles appreciates going through hours before his PC playing computer games. His #1 game is Bubble Strike, speedy air pocket shooting internet game for two players. Each game is set in one of the N maps, each having diverse landscape setup. First period of each game settles on which map the game will be played. The game framework arbitrarily chooses three guides and shows them to the players. Every player should pick one of those three guides to be disposed of. The game framework then, at that point, arbitrarily chooses one of the guides that were not picked by any of the players and starts the game. Johnny is profoundly energetic with regards to the game and needs to invest some energy concentrating on maps, in this manner expanding opportunities to dominate matches played on those guides. Nonetheless, he likewise needs to get his work done, so he doesn't have the opportunity to concentrate on every one of the guides. That is the…Please do it in c++ as soon as possible. Little Johnny Bubbles appreciates going through hours before his PC playing computer games. His #1 game is Bubble Strike, speedy air pocket shooting internet game for two players. Each game is set in one of the N maps, each having diverse landscape setup. First period of each game settles on which map the game will be played. The game framework arbitrarily chooses three guides and shows them to the players. Every player should pick one of those three guides to be disposed of. The game framework then, at that point, arbitrarily chooses one of the guides that were not picked by any of the players and starts the game. Johnny is profoundly energetic with regards to the game and needs to invest some energy concentrating on maps, in this manner expanding opportunities to dominate matches played on those guides. Nonetheless, he likewise needs to get his work done, so he doesn't have the opportunity to concentrate on every one of the guides. That is…
- This exercise will be about processing a collection of bank transactions using an iterator. A particular account owner may have multiple transactions. Assume a classed named BankXA that contains info about a customer's transaction. The class has 4 public attributes:string acctOwner //The name of the account's ownerstring xaDetail //some detail on the transactionstring type // assume the value will always be either "dep" for a deposit or "withd" for withdrawal, no other values double amt //the amount of the transaction. The amount will always be 0 or more Note that these attributes are public therefore you will NOT need setters and getters for this exercise. Your program will obtain a pointer to a list of BankXA. Your program must iterate the list using an iterator and the result must be like the following: J. Faune withdrew -$485.00 I. Boesky withdrew -$42885.50 J. Faune deposited +$2.50 Where J. Faune and I. Boesky are the acctOwners,the withdrew and deposited refer to the type "dep"…In main(), prompt the user for a customer's name and today's date. Output the name and date. Create an object of type ShoppingCart. Ex. Enter Customer's Name: John Doe Enter Today's Date: February 1, 2016 Customer Name: John Doe Today's Date: February 1, 2016final big report project for java. 1.Problem Description Student information management system is used to input, display student information records. The GUI interface for inputing ia designed as follows : The top part are the student imformation used to input student information,and the bottom part are four buttonns, each button meaning : (2) Total : add java score and C++ score ,and display the result; (3) Save: save student record into file named student.dat; (4) Clear : set all fields on GUI to empty string; (5) Close : close the win
- arrow_back Starting Out With Visual C# (5th Edition) 5th Edition Chapter 11, Problem 1PP arrow_back_ios PREVIOUS NEXT arrow_forward_ios Question share_out_linedSHARE SOLUTION Chapter 11, Problem 1PP Program Plan Intro Employee and ProductionWorker Classes Program plan: Design the form: Place a three text boxes control on the form, and change its name and properties to get the employee name, number, and hourly pay rate from the user. Place a four label boxes control on the form, and change its name and properties. Place a two radio buttons control on the form, and change its name and properties. Place a one group box control on the form, and change its name and properties. Place a command button on the form, and change its name and properties to retrieve the object properties and then display the values into label box. In code window, write the code: Program.cs: Include the required libraries. Define the namespace “Program11_1”. Define a class “Program”. Define a constructor for the…Using C# in visual studio help complete the TODOs: // TODO: comment Header// TODO: add regions to organize your code using System;using System.Collections.Generic;using System.ComponentModel;using System.Data;using System.Drawing;using System.Linq;using System.Text;using System.Threading.Tasks;using System.Windows.Forms; namespace ICE2_DiseaseCases{public partial class Form1 : Form{public Form1(){InitializeComponent();} // Global VariablesLabel[] weekDays;TextBox[] infections; // TODO: Add an event (ValueChanged) to the DateTimePicker control such that the weekday names are updated to match the chosen date. Note: the custom method to enter the names is already created, just call it. private void Form1_Load(object sender, EventArgs e){// initialize the weekdays label array and populate with the appropriate labelsweekDays = new Label[] { lblDay1, lblDay2, lblDay3, lblDay4, lblDay5, lblDay6, lblDay7 }; // TODO: initialize the infections textbox array and populate with the appropriate…This is my question and assignemnt. Any and all help would be great! Create a PHP file named User.php. Create a class User with two attributes: $username (containing username) and $roles (containing a string array of roles such as admin or customer). Create a constructor that accepts a string username. Assign the username to the username attribute. Code example: $this->username = $username; Assign the role of 'admin' to the roles attribute. Code example: $this->roles = array('admin'); Create a function to retrieving user roles. Name it getRoles() that returns the $roles object. Do a test Create a new User and insert a username. Code example: $user = new User('groot'); Retrieve the roles from the user and print_r the content. Code example: $roles = $user->getRoles() and print_r($roles);

