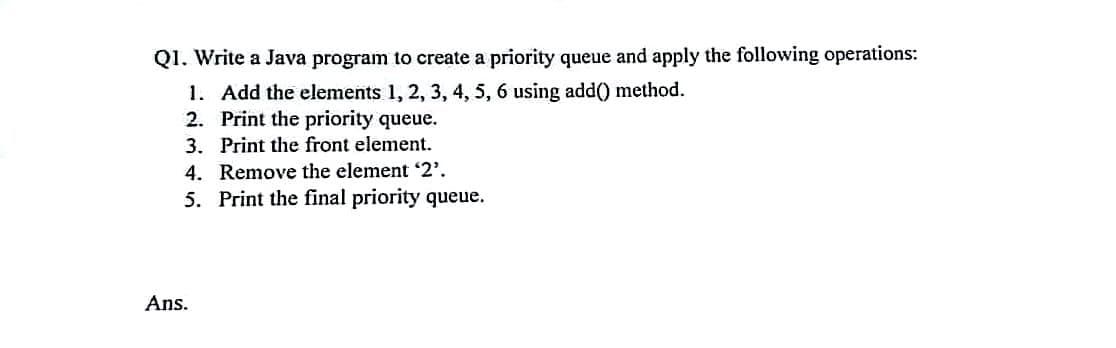
Q1. Write a Java program to create a priority queue and apply the following operations: 1. Add the elements 1, 2, 3, 4, 5, 6 using add() method. 2. Print the priority queue. 3. Print the front element. 4. Remove the element '2'. 5. Print the final priority queue.
Q: Q.2.1 Classify each of the two software packages as either application or systems software. (a)…
A: NOTE: Student asked only either or option in first question. So I answered as per student needed…
Q: What are the benefits of using a computer that has logical divisions as well as subsystems?
A: You may spread resources inside a single system using logical partitions to make it work as if it…
Q: Why do you think the method area of a JVM is shared by all of the threads executing in the virtual…
A: A Java virtual machine ( JVM) A Java virtual machine, commonly known as a JVM, is a kind of virtual…
Q: How can we check the history of ?commands used by only clicking the up direction button using the…
A: Answer:
Q: In what kind of situation would it make sense to make the assumption that two select statements…
A: It is possible to have union compatibility if both tables include the same number of characteristics…
Q: Q5/ What is the impulse response of a system whose transfer function is that of pulse function? Q5/…
A: Solution: Since after t=4 the impulse response is zero and below 0 also, the function is zero.…
Q: Vrite a program using MATLAB to multiply any number of numbers by the numbers between 1-49
A: Given:
Q: Within the framework of computer security, how does ransomware function
A: The Internet of Things may be used in several ways in our everyday lives, including: Smart locks,…
Q: A comprehensive and in-depth explanation of how the Domain Name System (DNS) works, including topics…
A: Domain Name System (DNS): The principal function of the DNS, which is also known as the domain name…
Q: Give two real-life problems / scenarios where you can use a graph algorithm to solve it. Explain how…
A: Graph is a very important data structure that is used to solve various real-life problems.
Q: Interprocess communication may be used as an alternative to storing structures shared by several…
A: Interprocess communication: A different approach might include storing shared structures in the…
Q: Consider the importance of wireless networks in today's emerging nations. In a variety of…
A: WLAN is a wireless computer network that connects two or more devices using wireless communication…
Q: Explain in detail three benefits and drawbacks of paging as a memory management approach.
A: Introduction: Explain three pros and downsides of using paging as a memory aid in detail.
Q: What is the relevance of multithreading with fine threads?
A: Given: Multithreading's Advantages Throughput has increased. Use of many processors for computation…
Q: type of sort is represented by the following code? public void sort(int arrayToSort[]) { =…
A: Answer: Correct option (E) Insertion Explanation: The insertion sort is like we sort the card.…
Q: Describe a few different methods that may be used to hijack a session. How would one defend…
A: Introduction: Depending on their location and vector, attackers have many ways for hijacking a…
Q: (If-else) Write a PYTHON program that will determine the user input value according to the below…
A: Your python program is given below as you required with an output.
Q: How does today's era of artificial intelligence compare to that of Al from 50 years ago, in terms of…
A: How does the present era of AI vary from that of 50 years ago with regard to machine learning and…
Q: In the transport layer, which protocol is used for point-to-point communication via the tunneling…
A: PPTP (Point to Point Tunneling Protocol) is a tunneling protocol that may be used to create a VPN…
Q: Q3\Write a program using MATLAB to multiply any number of numbers by the numbers between 1-49
A: Please refer below for your reference: Language used is Matlab: clc; a=3;%assuming number of…
Q: Suppose you are given a weighted graph with vertices labeled from A to E. After completely…
A: Solution is given below :
Q: Q3/ What is the output of the following: Unit Sample Sequence 02 Angude
A: Given:
Q: If you are concerned about the impact that incorrect data could have on a database, what are the…
A: Introduction: Inaccurate reports and dashboards make it hard for the sales and marketing teams to…
Q: Use "snapshot isolation" as an example for an airline database. In the event that airlines can…
A: A transaction executing its private copy of the data is never blocked at the isolation level.…
Q: Describe three ways information systems are being applied at the colleges.
A: Introduction: Information systems are assortments of different data assets (e.g., programming,…
Q: SAMPLE DISPLAY OUTPUT: Arithmetic Operation Enter number 1: 10 Enter number 2: 5 [A] [+] Addition…
A: The elif allows us to check for multiple expressions.
Q: Detailed information on the Domain Name System (DNS), including iterated and non-iterated searches,…
A: The goal of DNS is to translate a domain name into an IP address. This is done by getting the DNS…
Q: Please help me, what should I add to this code for me to be able to resize the each of the images…
A: By using Open CV we could able to solve this problem.
Q: The rerouting of malicious data across VLANs is one technique that might be used to infiltrate a…
A: Institution: The physical network is shared by a virtual local area network (VLAN), which creates…
Q: In order for a data hierarchy to work correctly, its components have to be recognized all the way up…
A: Given: For a data structure to function correctly, it must identify its components up to the…
Q: Consider a virtual memory system providing 32 pages for each user program; the size of each page is…
A:
Q: What are the many forms of malicious software that have a worldwide impact, and what are their…
A: Given: Malware, often known as a malicious software, is any programme or file designed to damage a…
Q: What is dynamic memory allocation and how is it implemented? When it comes to the user, what are the…
A: Dynamic Memory Allocation: When a running application requests a block of main memory from the OS,…
Q: Problem: A Hamiltonian cycle, also called a Hamiltonian circuit, Hamilton cycle, or Hamilton…
A:
Q: If two network interfaces have the same MAC address, is it possible? Is there a reason for this? Is…
A: Launch: When a computer connects to a private or public network, it uses a network interface. A…
Q: Is there anything more hard than working with time-variant data when it comes to the design of…
A: Database architecture is a visual representation of the design of a database management system. It…
Q: Using a router, a company's network may link up to 70 distinct workstations in three separate…
A: Introduction: Two sorts of issues will develop if 100Mbps NICs are replaced with 1000Mbps NICs. The…
Q: What are the key differences between beginning a data modeling project using a packaged data model…
A: Answer: 1. Better caliber Similarly as draftsmen consider outlines prior to developing a…
Q: According to a recent research conducted by IBM, which surveyed 585 mobile application developers…
A: Mobile apps have gained a reputation for facilitating effective communication and business…
Q: What role does linear programming have in financial decision-making?
A:
Q: Do you believe that each of the virtual machines' threads uses the same method area of a JVM?
A: JavaME (JVM): JVM runs Java code. It translates Java to machine language. Compiling Java to…
Q: Q12/ The odd parts of the signal x (t) in MATLAB is
A: As per the question statement, We need to find the odd part of the signal x(t).
Q: In a JVM, the method area is shared by all executing threads. Why is this?
A: A Java virtual machine (JVM) is a virtual machine that allows a computer to execute both Java…
Q: What function does MVC play in the building of web applications in the big scheme of things? What…
A: Introduction: What function does MVC play in the building of web applications in the big scheme of…
Q: t comes to security, what is the difference between integrity and authorisation?
A: Although , integrity and authorization work parallelly accompanied together .But , both these term…
Q: Examine the different development methodologies utilized to create the Windows and Android operating…
A: Windows is a group of various proprietary graphical operating systems which is provided by Microsoft…
Q: What exactly is the difference between architecture and computer organization when it comes to the…
A: The architecture of a computer determines what it can do, whereas the organization of a computer…
Q: What exactly does it mean when people refer to something as a "operating system"? Give a description…
A: The operating system is in charge of two major tasks: This comprises the management and control of…
Q: How, as a database designer, are you able to alter the performance of the database in different…
A: Foundation: The database designer is responsible for defining all of the specific database…
Q: Do you have any examples to back up your contention that a relational database cannot allow…
A: Given: Use a join table to split the many-to-many connection into two one-to-many relationships. A…
Step by step
Solved in 2 steps with 1 images

- 1a. What is a stack? b. Write an algorithm for all operations in the stack? 2a.What is a queue? b. Write an algorithm for all operations in the queue?What is the difference between a stack and a queue in computer science, and how are they implemented? Provide examples of scenarios where using a stack or a queue would be the most appropriate data structure choice.Please answer the following, #3. Write clearly please. If postfix math is easy to analyze with a stack, would prefix math like ”/ * + 2 2 8 4” (which equals 8) be easy to analyze with a queue? How would you attempt to analyze this math with a queue? Lay out assumptions and use those in your solution as well.
- computer science~Java Show the state of the queue with the corresponding characters during the following sequence of queue operations, if executed on an initially empty queue? DA*T*AP*L*US (NB: A letter means "Enqueue() while an asterisks means "Dequeue()"). Show your steps of execution)Create a Queue Class and write a main() program to instantiate and use this class. Use arrays and java PL for this implementation. Ensure that your classhas the following attributes and methods: *Attributes: rear, front and any others which you deem necessary *Methods: queue(), enqueue(), dequeue(), isFull(), isEmpty(), peek()This is a java data structures question -> Answer YES or NO to the following: Would it make sense to call a queue? - a FILO structure? - a LILO structure? -> What is the main advantage of implementing a queue using a linked list rather than an array ?
- ANSWER ASAP. C++ LANGUAGE ONLY. (NOT C, NOT JAVA, NOT C#) CPP ONLY Using the double-ended linked list C language syntax code below, convert it into C++ and use it as the base. Modify the provided program into the ff: create a new class named student_queue. and then.. Implement the following methods for the class: front() - returns the pointer to the front element of the queue back() - returns the pointer to the back element of the queue push() - allocates memory for a new node and connects it to the existing queue pop() - retrieves the oldest node in the queue, copies the data to a structure, and frees up the memory from the queue empty() - returns 1 or 0 depending on whether the queue is empty or not size() - returns the number of elements in the queue Program code: #include <stdio.h>#include <stdlib.h>typedef struct se_list_type {int num;struct se_list_type* prev;struct se_list_type* next;} se_list;int main() {// Start the listse_list* head = NULL;se_list* cur =…Write a Java program to implement a stack by using array. o Define a Stack interface.o Define an ArrayStack class.o Define a Test class to test all methods 2. Write a Java program to implement a queue by using array o Define a Queue interface.o Define an ArrayQueue class.o Define a Test class to test all methods 3. Write a Java program to determine if a string is a palindrome by using stack. I need help with number 3Implement in Python a double-ended queue (deque): A double-ended queue is a data structure (ordered collection of items) similar to a traditional queue. It has two ends, front and end, but it is not restricted to adding or removing items. New items can be added on the front or on the end. Existing items can be removed from either end. The image graphically shows how the structure is. - Implement the requested structure using a single linked list, which implements the following functions: enterFront, enterEnd, removeFront, removeEnd- The data to be entered are animal-type objects; name, type of animal, age- Create a Main function with the available operations
- Show the results of the following sequence of events, by drawing the state of the data structure: add(4), add(8), add(1), add(6), remove(), remove() where add and remove are the operations that correspond to the basic operations in a: Stack [5] Queue [5]Assume you have a queue with a maximum size of 100 elements and you want to perform the following operations: Enqueue 50 elements into the queue. Dequeue 20 elements from the queue. Enqueue 80 elements into the queue. Dequeue 60 elements from the queue. Enqueue 40 elements into the queue. What is the final size of the queue after performing all these operations?In C++, Write a program which is menudriven ( i) Enque, ii) Deque, iii) Peek iv) Print). It will create a circularQueue of integer type data using array. You have to implement the followingoperations.a. Enqueue (Insert a data to the queue)b. Dequeue (Remove an item from the queue and printit)c. Peek (Print the item at the Front)Print (Print the elements present at the queue)

