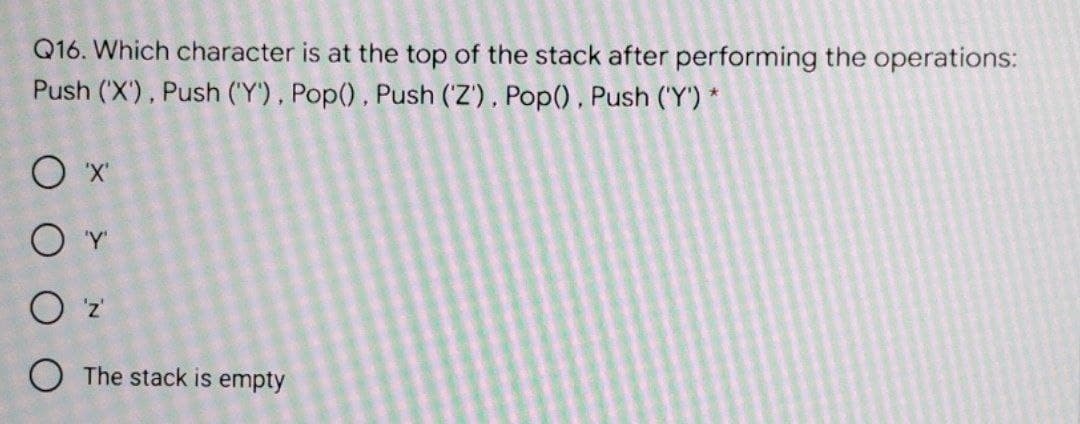
Q16. Which character is at the top of the stack after performing the operations: Push ('X'), Push ('Y'), Pop(), Push (Z'), Pop(), Push ('Y') * O The stack is empty
Q: Is there anything bad about how cell phones charge?
A: Cell Phones Charge: While the phone is charging, you can use it. Using your phone while it is…
Q: Explain the concerns with ISPS limiting Internet usage.
A: Introduction: A user's personal computer, netbook, or notebook can be connected to the internet with…
Q: less has become so prevalent in the modern netwo
A: Why Wireless has become so prevalent in the modern networking environments
Q: Discuss CSMA/CA/CD. Describe each one's function and intended network. Describing the benefits and…
A: It manages communication when several users utilize a single shared channel or media. There are…
Q: In order for a data hierarchy to function properly, all of its components must be recognised up to…
A: To function correctly, the components of a data hierarchy must be recognized up to the database…
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Introduction: AWS Global Infrastructure is a service provided by Amazon Web Services.AWS is a cloud…
Q: Why would a 1000MB CAT6E cable be a terrible choice for a 32 for high data throughput? What would be…
A: Cat6e is a shortened form for "cat6 upgrade." Cat6e link has the property of accomplishing 600 MHz…
Q: Comment on how pipelining can make computers faster, how pipeline dangers can be mitigated, and how…
A: Here we have given a brief note on how pipelining works and given appropriate answers. you can find…
Q: social engineering hacker
A: With regards to information security, social engineering is the mental control of individuals into…
Q: You are tasked with deploying websites on EC2 instances. The solution should be scalable and the…
A: I have provided the solution in step 2.
Q: What is the difference between symmetric key cryptography and asymmetric key cryptography, and how…
A: The answer to the following question:-
Q: A motorcy tion. The PASCAL km
A: Ac. to given: Let us take 3 variables, m for milage= 48 c for cost of petrol per liter= 20.30 d for…
Q: I have a c++ program where I want to add movies to an existing textfile and show all the movies with…
A: Solution: C++ Program: #include <iostream> #include <fstream> #include <string>…
Q: Why would a 1000Mb CAT6e cable be a terrible choice for a 328-foot length pull for high data…
A: Introduction: "Cat6e" is an abbreviation for "cat6 enhancement." Cat6e cable has the property of…
Q: en your computer or personal c e secret, sensitive but unclass of misuse or embarrassment?
A: The database schema is its design depicted in a conventional language upheld by the database…
Q: What exactly is information privacy? Describe five different ways to keep your personal information…
A: answer is
Q: Calculate the turnaround for each job 2.Find the average turnaround 3.How faster is the SRT than the…
A: in the following section we will solve the above stated question
Q: What are the specific goals of authentication? Compare and contrast the benefits and drawbacks of…
A: Authentication is the process of determining the identity of an individual process or entity seeking…
Q: What is the mechanism through which interrupt-driven I/O operates?
A: Interrupt-driven I/O operates: The interrupt-driven approach is an alternate way for dealing with…
Q: Give two examples of how various versions of a system based on software diversity may fail in a…
A: INTRODUCTION: A set of instructions, data, or programs used to control computers and perform…
Q: Compare US cyberlaws to foreign Cyberlaws.
A: Compare US cyberlaws to foreign Cyberlaws.
Q: Recognize and categorize the data on your computer or personal digital assistant. What information…
A: The many types of data stored on a personal computer The data categorization methodology classifies…
Q: When constructing globally dispersed data environments, what compromises do you have to make?
A: When constructing globally dispersed data environments, what compromises do you have to make?
Q: Discuss in detail the importance of architectural design in software development.
A: importance of architectural design in software development. Architectural design in software…
Q: What is a link list?
A: Justification: An association list, often known as an a-list, is a common data structure in Lisp.…
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: INTRODUCTION: Amazon Web Services, Inc. (AWS) is an Amazon company that offers metered…
Q: Describe the security model that the cnss employs to protect its data. What are the object's…
A: Security model : Because of the growing threat of cyber-attacks, governments and businesses have…
Q: Expand to an unsimplified Boolean Function: F= D + AB'C + A'D
A: Given unsimplified Boolean Function: F= D + AB'C + A'D A+A'=1 A+A=A
Q: What is the most important goal of normalization? What part do determin the process of…
A: Below the normalization and determinants play in the process of normalization.
Q: After doing the following statement, the linked list becomes Head P Head 3000 4800 10 4900 15 5000…
A: Here in this question we have given a linked list with an operation to do on this.and We have asked…
Q: Software engineering is a field of engineering which is concerned with all aspects of software…
A: One of the computer programming definition is "the utilization of a precise, trained, quantifiable…
Q: How is data from a wristwatch, bike computer, and smartphone all synced up to a single user account…
A: Which Internet of Things is a wireless protocol used to synchronize data from a wristwatch, bike…
Q: Let B = {0,1}. Give a recurrence relation for the strings of length n in B * that do not contain 01.…
A: We are going to find out the recurrence relation for the strings of length n in B * that do not…
Q: Discuss the Importance of business intelligence (BI)
A: Business intelligence refers to the procedural and technical infrastructure that collects, stores,…
Q: When it comes to database recovery, what are the three sorts of backups that may be utilised? In a…
A: Database Recovery: In the case of a failure, database recovery is the process of returning the…
Q: Write a function called chop that takes a list, modifies it by removing the first and last elements,…
A: We will be seeing the simple program for implementing our classes. We will be having comments which…
Q: Background You are a systems analyst contracted by Earth Friendly Babies, a mail-order company that…
A:
Q: Is it possible that friend functions are in conflict with the concept of Object Oriented…
A: In object oriented programming, a friend function that is a 'Friend' of a given class is allowed…
Q: Which of the following is designed to control the operations of a Computer? a) User b) Application…
A: Which of the following is designed to control the operations of a computer?a) User b) Application…
Q: eiver receive if th
A: given - In a digital transmission, the receiver clock is 0.1 percent faster than the sender clock.…
Q: What are the two functions of an op
A: Solution - In the given question, we have to tell about two operating system modes, two fundamental…
Q: Assume you want to keep an attacker from detecting a hash function collision. The attacker has…
A: Introduction: Consider the case where you wish to prevent an opponent from detecting a hash function…
Q: Examine how consumers react to programme and application errors on their computers and mobile…
A: We need to emphasize tactics for mitigating user annoyance caused by program malfunctions.
Q: Why would a 1000MB CAT6E cable be a terrible choice for a 328-foot length pull for high data…
A: Throughput is high: Because high throughput often suggests that a firm can manufacture a product or…
Q: Explain why change is unavoidable in complex systems, and provide examples of software process…
A: Reasons, why change is unavoidable in a complex system, include the following: Modifications to the…
Q: List all auxiliary devices and divide them into four categories: pointing devices, scanning devices,…
A: According to the question, these are all devices that we use in our everyday lives and that assist…
Q: What is the most important goal of normalization? What part do determinants play in the process of…
A: The most important goal of normalization An goal of normalization is to minimize the quantity of…
Q: What is the difference between 00 and FP programming? - Describe the benefits and drawbacks of each…
A: Statement: A functional approach to creating and implementing software is emphasised in functional…
Q: Explain what causes a system to become stuck in a stalemate.
A: In a Stalemate, the King is unable to move since he does not have any Safe Squares, similar to a…
Q: Recognize and categorize the data on your computer or personal digital assistant. What information…
A: Information: Information stored on a personal computer may be of several types. The data…
Step by step
Solved in 2 steps with 1 images

- 54. What is the difference between the top and pop operations of a stack? Group of answer choices The top operation removes the top item of the stack. The pop operation returns a reference to the top item on the stack and remove it. The top operation removes the top item of the stack. The pop operation returns a reference to the top item on the stack without removing it. The pop operation removes the top item of the stack. The top operation returns a reference to the top item on the stack without removing it. The pop and top operations are doing the same thing which removes the top item of the stack. The pop operation removes the top item of the stack. The top operation returns a reference to the top item on the stack and remove it.assume we use the STL of the stack, with the following code stack<char>s; string word=”stack”; int i; while (word[i]!=0) s.push(word[i]); while (!s.empty()) { Cout<<s.top(); s.pop(); } the output is a. stack b. kcats c. kcsta d. ackassume we use the STL of the stack, with the following code stack<char>s; string word=”stack”; int i; while (word[i]!=0) s.push(word[i]); while (!s.empty()) { Cout<<s.top(); s.pop(); } the output is a. stack b. kcats c. ack d. kcsta
- (Printing a Sentence in Reverse Order with a Stack) Write a program that inputs a line of text and uses a stack object to print the line reversed.if a stack contained the entries 128, 90, 56, 341 (from top to bottom), what would be at the top of the stack after the statement push(106) is executed?Draw a stack: We start with an empty stack and then execute the following commands: push 4 push 7 pop push 5 push 5 push 8 push 7 push 8 pop pop pop push 7 push 6 pop pop push 8
- A stack has following variables initialized, answer question 5 &6 using these values int size = 7; int top = —1; int [ ] arr = new int [size] ; Q5. What will be value of the top variable when the stack is empty? Q6. What will be value of the top variable when the stack is full?The following operations are performed on a stack:PUSH A, PUSH B, POP, PUSH C, PUSH D, POP, PUSH E, POP, POP, PUSH FWhat does the stack contain after the PUSH F?a. Fb. A B C D E Fc. A C Fd. A Fe. none of the above.What will be the stack content after following operations: Push 5 Push 8 Pop Push 1 Push 12 Pop
- Assume that the input sequence is ABC, and the output sequence is CBA. What are the operations performed on the stack? (A) push, pop, push, pop, push, pop (B) push, push, push, pop, pop, pop (C) push, push, pop, pop, push, pop (D) push, pop, push, push, pop, popConsider the following statements: stackType<int> stack; int x; Suppose that the input is: 14 53 34 32 13 5 -999 Show what is output by the following segment of code: cin >> x; while (x != -999) { if (x % 2 == 0) { if (!stack.isFullStack()) stack.push(x); } else cout << "x = " << x << endl; cin >> x; } cout << "Stack Elements: "; while (!stack.isEmptyStack()) { cout << " " << stack.top(); stack.pop(); } cout << endl;Machine organization The following operations are performed on a stack: PUSH A, PUSH B, POP, PUSH C, POP,POP,PUSH D, PUSH E, POP, PUSH F. What does the stack contain after each operation?

