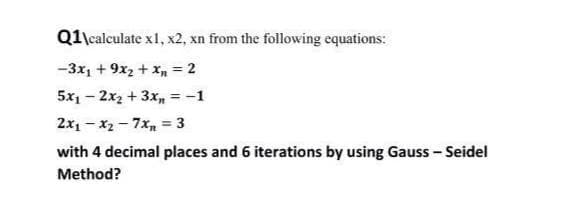
Q1\calculate x1, x2, xn from the following equations: -3x1 + 9x2 + xn = 2 5x1 - 2x2 + 3x,n = -1 2x1 - x2 - 7x = 3 with 4 decimal places and 6 iterations by using Gauss - Seidel Method?
Q: Construct a pda that accepts the language defined by the grammar S --> aSSSA | λ A --> aB B --> b
A:
Q: When part of the characteristics are missing, how can we use Bayesian classification?
A: Statement: In the instance of Bayesian-Classification, we must describe how to deal with missing…
Q: How do you choose a node to be "supernode" in a peer to peer network?
A: A super-peer is a peer-to-peer (P2P) network node that acts as a server for both a network of…
Q: A solid cyber security strategy should contain what?"
A: Cyber Security: Cyber security refers to the collection of methodologies, technologies, and…
Q: What does it mean to say that a firewall is in place?
A: According to the question the firewall is a software for preventing unauthorized to access the…
Q: What are the most recent technological advancements in information technology, information systems,…
A: Introduction: The facilities and services that a company need are referred to as infrastructure.…
Q: Do you agree with the assertion that "there is no sense of client and server sides of a…
A: Session of communication A dialogue session is an immersive information exchange between two…
Q: Pascal Program to display all powers of 2 that are less than 2000 and display five numbers per line?
A: Here our task is to write a pascal program to display all powers of 2 that are less than 2000. We…
Q: What are the potential drawbacks and issues of relying on a disjointed information system?
A: Computer failure and loss: A failure is a word that refers to a problem with a computer or equipment…
Q: Q16. Which character is at the top of the stack after performing the operations: Push ('X'), Push…
A: An stack is a abstract datatype.The stack follows the Last In First Out order. The stack contains…
Q: Show the implementation of Linear Queue queue size =6 Enqueue(1) Enqueue(5) Enqueue(8) Enqueue(0)…
A: Here in the given code, we have an implementation of the queue. A queue is a linear data structure…
Q: Please help me modified my c++ code, it has some problems and I do not know how to fix. Thank you
A: After fixing the code , I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT…
Q: Ruby language are allowed to return more than one value, and parallel assignment is helpful in…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Explain how the black box works!
A: The Answer is in step-2.
Q: Why has computer security progressed from a purely theoretical concept to a modern-day information…
A: GIVEN: Why has computer security progressed from a purely theoretical concept to a modern-day…
Q: First stage of our program Readln (base, height); area: 0.5 base height : Writeln(area):
A: Program Approach:- 1. Declare variables 2. Take the input from the user 3. Perform the calculation…
Q: Explain what you understand by The Cloud Hosting Services.
A: INTRODUCTION: Cloud hosting is ideal for websites that deal with enormous volumes of traffic at…
Q: Is there a problem with a variety of different information systems in the workplace? Is there a way…
A: Users can acquire, store, organize, and distribute data using information systems, which can be used…
Q: Qs. Choose the correct answer from the atuen four 1. In a Gollege, 30 1 stucknt fail in Phy SPcs,…
A: Answer: option B is correct
Q: Design a recursive function that accepts two arguments into the parameters x and y. The function…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: What is the importance of Firewalls in an Extranet Service?
A: A firewall is a device used for network security.
Q: Is it necessary for an IT professional to know the binary numbering system? Apart from the examples…
A: A binary number system consists of data representation using 1 and 0 . Even though programming…
Q: 3. Find all the roots of the polynomial P(x) = 3x² + 11x² + 8x – 4
A: Answer
Q: What is heuristic evaluation, and how is it used? What's the point of this thing?
A: Heuristic evaluation: As part of an iterative design process, heuristic evaluation (Nielsen and…
Q: In this program, we get the size of an array of integers from the user. Write a function which…
A: In this C++ program. - We have defined a function named which accepts the int parameter and returns…
Q: Examine how consumers react to programme and application errors on their computers and mobile…
A: We need to emphasize tactics for mitigating user annoyance caused by program malfunctions.
Q: A rectangle has a perimeter of 20. If the area of the rectangle is to be maximized, the length of…
A: Answer
Q: Discuss advantages and disadvantages of centralized database architecture
A: In Centralised database all tye data are stored in one physical location. Here are some important…
Q: etermines how all those features are to be developed. Actually this action plan is based on the…
A: Plan-driven development is a software development technique which endeavors to plan and foster…
Q: FileProcessing: Write a program that reads all the characters in a text file (“input.txt") and…
A: Code: import java.io.*;import java.util.*; public class Main { public static void main(String[]…
Q: This question is about graph data structure. Draw the data structures for the graph above. Draw the…
A: Here, we are given a directed weighted disconnected graph and we are asked to represent this in…
Q: If we want to encrypt 40 letters stored in Unicode format, how many data blocks will be created if…
A: In UNICODE Format , one letter is encoded in one byte i.e 8 bits. So, 40 letters = 40 byte= 320 bits…
Q: What types of attacks are handled when it comes to message authentication?
A: Introduction: Message authentication protects you from what kinds of attacks Changes to the…
Q: Explain the distinction between hardwired control and microprogrammed control.
A: Hardwired Control : Hardwired and microprogrammed control are now available. Hardwired control units…
Q: You've begun photographing a computer drive at a crime scene. A little fire has started in the…
A: Start: A man is murdered in his home's backroom. When the investigating agency arrives at the crime…
Q: Recognize the various types of information systems and their associated users
A: Given: Basic types of information systems include the following:Management information…
Q: Explain how you plan to create a GIS database, including data sources, funding, and Quality…
A: Data quality is assessed using different evaluation techniques by different users. The…
Q: A length of at least 8 characters • At least 1 uppercase letter At least 2 numbers • At least 1…
A: Step-1: StartStep-2: Declare variable upper, num, ch, containSpecial and passwordStep-3: Start a…
Q: Design the logic (flowchart and pseudocode) using arrays for a program. It allows a user to enter 10…
A: The question can be solved by very simple steps: create an array of size 10 create a variable "sum"…
Q: Explain data security in detail, as well as the three forms of data ownership and the…
A: Data Backup: Data backup, encryption, and antivirus software are just a few examples of data…
Q: Packet switching is more appropriate for mobile networks than circuit switching.
A: Inauguration: Appropriate for mobile networks rather than circuit switchingTraditional telephone…
Q: What are the best risk management practices to employ when migrating to the cloud?
A: Introduction: As a result, a cloud provider must manage the risks associated with the cloud…
Q: How many begin with 111?
A: To find the number of strings which begin with "111" in the set of strings of length 8 made up of 2…
Q: eries: A triangle number counts the objects that can form an equilateral triangle. The nth triangle…
A: code : #include<iostream>using namespace std;int main(){ int n,i=1; cout<<"Enter…
Q: Which XXX is valid for the following code? int CalcSum(int a, int b) { return a + b; } int main() {…
A: Solution:- A method CalcSum, which accepts two numbers a and b as integers and returns their sum in…
Q: Model consistency, fl exibility, and documentation are critical.
A: Given: Describe the significance of model accuracy, adaptability, and documentation. The…
Q: What are the two most compelling arguments for layered protocol design, in your opinion?
A: layered protocols: What are two reasons why layered protocols are used? 1) Changes to one layer have…
Q: Explain what a challenge–response system is and how it works in the context of authentication. It's…
A: System of provocation–response Password-based authentication is often used in client-server systems.…
Q: Consider a situation in which a threat actor modifies the extension of files in order to prevent…
A: Slack space: The vacant space within a file allocation block or memory page could be used to store…
Step by step
Solved in 3 steps with 3 images

- A B C D X1 a1 b1 c3 L X2 a2 b1 c1 L X3 a2 b2 c1 H X4 a2 b2 c2 H X5 a2 b1 c1 L X6 a2 b2 c1 H X7 a2 b1 c2 H X8 a1 b2 c2 L Using the table above, calculate the following, there measures (1) Kulczynski, (2) Lift, and (3) Cosine. a) A1 ==> L b) A2, B2 ==> H c) A2, C2 ==> HWhat is the value of x in the following system of equations: -x + 8 = -y2x – 2 = -5y x= 1 x= 2 x= 3 x= 4 x= 61. Show that xy' + yz' + x'z = x'y + y'z + xz'
- Q4:) Given that y(x) =x* - x>+ 8x + 10 1:-Use polynomial form to find y and its derivative for x = =312, L1, 2:- Use symbolic expression to find y and its derivative for x = matlapWhich among the following is an example of quadratic function? 2 + (10 * X) (3+4) *(4*X) 24 + (56 × X2) (5.3 × X2) + ( 21.6 × X3)Determine the value of each of the following expressions. (For decimal numbers, round your answer to two decimal places.) (1) abs(-18) fabs(20.5) fabs(-87.2) pow(4, 2.0) pow(8.4, 3.5) sqrt(7.84) sqrt (196.0) sqrt (38.44)* pow(2.4, 2) / fabs(-3.2) floor(27.37) ceil(19.2) floor(12.45) + ceil(6.7) floor (-8.9) + ceil (3.45) floor(9.6) / ceil(3.7) pow(-4.0, 6.0) pow(10, -2.0) pow(9.2, 1.0 / 2)
- Two trigonometric identities are given by: (sin x + cos x)2 = 1+ 2 sin x cos x 1- 2 cos x - 3cos2 x = 1- 3cos x sin2 x 1- cos x For each part, verify that the identity is correct by calculating the values of the left and right sides of the equation using MATLAT, substituting x=200 Find the solution to the systems + = ... .. . y + 3 y + 2 y y u Where y (0) =0; y’ (0) =0. u (t) is a square wave.Compute the following values: d) P(5,5) e) P(6,0)f) P(100,2)Two points on line 1 are given as (x1, y1) and (x2,y2) and on line 2 as (x3, y3) and (x4, y4), as shown in Figure 3.8a and b.The intersecting point of the two lines can be found by solving the following linearequations:(y1 - y2)x - (x1 - x2)y = (y1 - y2)x1 - (x1 - x2)y1(y3 - y4)x - (x3 - x4)y = (y3 - y4)x3 - (x3 - x4)y3This linear equation can be solved using Cramer’s rule . If the equation has no solutions, the two lines are parallel (see Figure). Write a program that prompts the user to enter four points and displays the intersectingpoint. Here are sample runs:
- % Define the function f(x) f = @(x) -1*(x < 0) + 1*(x >= 0 & x <= 2); % Set the maximum value of N Nmax = 512; % Initialize the x-axis values for plotting x = linspace(-1,3,1000); % Compute the Fejér sums for various values of N F = zeros(length(x), Nmax); for N = 1:Nmax % Compute the Nth Fejér sum Sn = @(x) 0; for n = 1:N bn = (-1)^(n+1) / (n*pi); Sn = @(x) Sn(x) + bn*sin(n*pi*x); end FN = @(x) (1/N) * Sn(x); % Evaluate the Fejér sum at each point on the x-axis I tried to submit this to MATLAB, but can't seem to get it right.PLEASE USE PYTHON METHOD The function y(x) represented by the data below has a maximum at x = 0.7692. Compute this maximum by Nevilles interpolation over four nearest neighbor data points. x = 0, 0.5, 1, 1.5, 2, 2.5, 3 y = 1.8421, 2.4694, 2.4921, 1.9047, 0.8509, -0.4112, -1.5727Given f(x)=x2+6x and g(x)=1−x2, find f+g, f−g, fg, and fg. Enclose numerators and denominators in parentheses. For example, (a−b)/(1+n).

