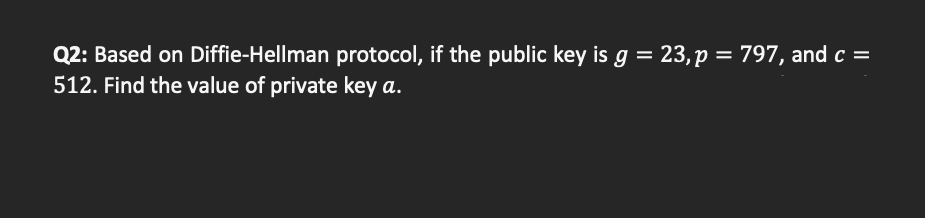
Q2: Based on Diffie-Hellman protocol, if the public key is g = 23,p = 797, and c = 512. Find the value of private key a.
Q: 8, 5, 1, 2, 5, 3, 5, 6, 2, 6 Assuming that all frames are initially empty, indicate the contents of…
A: In optimal page replacement algorithm, pages which will be not referred for longest time in future…
Q: What are the benefits of documenting source code?
A: According to the question documenting is most important for give the presentation of the software of…
Q: What methods are used in the creation of computer programmes
A: Given: We have to discuss What methods are used in the creation of computer programmes.
Q: re particularly concerned about the need to learn certain data warehousing skills prior to building…
A: In computing, a data warehouse (DW or DWH), otherwise called an enterprise data warehouse (EDW), is…
Q: Is there a list of software configuration management activities that a project requires?
A: Management of Software Configuration Software Configuration Management (SCM) is a method for…
Q: What are the four essential activities of software development, according to you?
A: Given: Specification, development, validation, and evolution are the four main process tasks that…
Q: Write a program that takes verbs and forms their past tense on the basis of these rules: a. If verb…
A: Please find the answer below :
Q: if we have the IP 192.168.0.0/26 1. Find subnet mask? 2. How many subnets I need? 3. How many valid…
A: Here are the the description regrading to IPV4 address above:
Q: What is it that software engineering's basic ideas don't take into account? explain?
A: Software engineering: Software engineering is a comprehensive study of engineering applied to…
Q: Each stage of the software development process should be examined for mistakes.
A: stages of software development process examined mistake.
Q: Locate two GSS software options that can be utilized to aid group decision-making over the internet.
A: Technology: An application programming interface allowing applications to access security services…
Q: Digit 2,4,1 of HTTP status code represents : Success, Clienterror, Servererror Success, Clienterror,…
A: Answer :
Q: Your data warehousing project team is contemplating whether to construct a data warehouse prototype…
A: It is the collection of data utilized for decision-making and business intelligence in a data…
Q: "Decrypting an encrypted document" An employee of your company has left the organization on poor…
A: The conversion of an encrypted file into its original form is called decryption. Because only a…
Q: Why does displaying file extensions aid in malware protection?
A: Answer: Introduction: The file extension is one of the important things that everyone notices…
Q: What are the two interprocess communication models? What are the advantages and disadvantages of…
A: Inter process communication methods are helpful to use the common resources between the processes.…
Q: Make a list of the four services that a transport protocol can offer. Indicate whether a service is…
A: TCP The transport layer protocol is TCP. A protocol is a set of principles or regulations that must…
Q: Write a Java class that populates an array of 20 random ints between 0 and 100. Write two methods:…
A: Step 1 : Start Step 2 : Define a method getLargest() which accepts an array and returns the largest…
Q: Describe TWO applications on how is artificial intelligence used in social media, such
A: Artificial intelligence is the reenactment of human intelligence processes by machines, particularly…
Q: When developing software, what are the four most important activities?
A: The Answer is given below step.
Q: Computer science Describe the PowerShell script in your own words. In PowerShell, how will you…
A: The answer is as follows.
Q: With the help of appropriate examples, discuss the memory representations of 1D and 2D arrays in…
A: A 1D array is a collection of variables of the same data type. It is sometimes referred to as a…
Q: Problem 1 Define the matrix A = [1:4 5:8 ones(Int64,4)1. Predict the result of performing the…
A:
Q: Consider the relational schemas given below and the respective sets of functional dependencies valid…
A: “Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: The OSI model divides the process of internetworking into seven tiers, referred known as a vertical…
A: Given: The ISO-OSI model is an Open System Interconnection model based on the International…
Q: Create a program using a loop in C++ and ARM Assembly language that executes the following: The…
A: Program in c++: #include <iostream> using namespace std; int main() { int a=-30,b=96;…
Q: Using the code below, answer the following questions: 1) What are each of the 3 functions…
A: NOTE - As per our guidelines we are supposed to answer only the first three parts, please re-submit…
Q: Describe the following GPS applications and their standards and specifications. a. GPS in…
A: The term GPS refers to the Global Positioning System. It is a radio-controlled navigation system. It…
Q: What is a database management system (DBMS)? Using a coffee shop as an example, how can we maintain…
A: Database Management System(DMS): A database management system (DBMS) stores and retrieves user data…
Q: Name three virtualization tools. Contrast them
A: VIRTUALIZATION TOOLS(Software) 1) SolarWinds Virtualization Manager SolarWinds Virtualization…
Q: Which of the following is false in reference to python ? O Tuple is an unordered sequence and…
A: The question requires to Identify which of the given option/s is/are false with reference to python.…
Q: During the process of making software, what is the "lifecycle"?
A: Life cycle is a structured process that enables the production of high-quality, low-cost software,…
Q: How will an organization evaluate a system if it wishes to employ another company to develop…
A: The Answer is given below step.
Q: Question3: Write a program that adds the even numbers between 1 and 100, and save it as an M-file.
A: find your code below
Q: differences and similarities between an applic I) and an application binary interface (ABI) (A
A: Below the differences and similarities between and application Programming interface API and an…
Q: t software engineering do
A: Fundamental software principles Software is a series of programming instructions that are performed…
Q: Compilers and assemblers can be built to optimize the rearrangement of assembly language…
A: Hazards/Pipeline: A pipeline is a method of programming in which numerous instructions are executed…
Q: B C - Fi D a. Derive the Boolean expressions for T1 through T4 and F1 and F2 b. List the truth table…
A: 1. a. Boolean expression for T1: T1 = B'C Boolean expression for T2: T2 = A'B Boolean expression for…
Q: Could you kindly provide an overview of the important components of the operating system? in…
A: Introduction : The components of an operating system play a critical role in ensuring that the…
Q: User-centered design and the software development lifecycle are closely linked.
A: Software life cycle models (sometimes called process models) depict the software development life…
Q: The OSI model divides the process of internetworking into seven tiers, referred known as a vertical…
A: Explanation: The ISO-OSI model is an open system interconnection paradigm developed by the…
Q: Consider what data mining entails. Examples of data mining applications should be provided.
A: Data mining includes extricating and analysing large blocks of information to identify patterns,…
Q: Consider what data mining entails. Examples of data mining applications should be provided.
A: Answer
Q: What are the key distinctions between a packet switch network and a circuit switch network?
A: Circuit Switch and Packet Switch: In order to connect the various communication devices, two…
Q: In order for R to have a primary key of P, we need P -> R. Is this statement correct or incorrect?
A: A primary key is a minimal set of attributes (columns) in a table that uniquely identifies tuples…
Q: 1) Registers 2) Program Structure (Data and Code declaration)
A: The answer is
Q: Design a regular expression for {w ∈ {a, b}*: no two adjacent symbols are the same as each other.}
A: Regular Expression: A regular expression is exists for all the regular languages. A regular…
Q: A system with byte addressable memory , 64-bit logical address,4 kilobyte page size and page entries…
A: Solution : Given Logical Address : 64 kb page size : 4kb page entry : 4byte
Q: what is the output of this windows form application? using System; using…
A: Compilation Error
Q: Why does displaying file extensions aid in malware protection?
A: Malware protection filters the file that it thinks consists of some form of malware.
Step by step
Solved in 3 steps

- Can you please help me with this: RSA can be used for: Digital Signature Encryption and Decryption Key exchange All the above RSA is secure because: Factoring large integers is easy Factoring large integers is hard Modular arithmetic is hard Modular arithmetic is easy Which description about the Diffie-Hellman Protocol is NOTcorrect? Diffie-Hellman Protocol is used to negotiate a key over a public channel. The base gand modulus pare publicly known. Diffie-Hellman Protocol authenticates each party. Diffie-Hellman Protocol is vulnerable to the Man-In-The-Middle Attack.In a public key, cryptosystem using RSA algorithm, user uses two prime numbers 5 and 7. He chooses 11 as Encryption key, find out decryption key. What will be the cipher text, if the plaintext is 2? Decrypt the cipher text, what will be the value of plain text?In a public key cryptosystem using RSA algorithm, a user uses two prime numbers 11 and 17. He chooses 7 as the encryption key, e. 12. Find the decription key.
- q12- The security of symmetric encryption depends on the secrecy of the algorithm, not the secrecy of the key as the key is shared between the sender and receiver. Select one: True FalseIn the use of RSA Cryptography, if the public key under RSA Cryptography is (11,65), find the private key.Cryptography: Alice and Bob are going to establish a secure session key utilizing Diffie-Hellman key exchange. The agreed upon public prime is, 10477, Alice’s secret is 997, Bob’s secret is 1137. The public base is 31. What is their session key?
- What is the Diffie-Hellman algorithm for exchanging a secret session key?Please enumerate and elaborate on the ideal qualities of a cryptographic hash function.In the use of RSA Cryptography, if the public key under RSA Cryptography is (11, 65), find the private key You must show all the detailed steps.
- Suppose p=5 and q=11. Which of the following is the private key of an RSA cryptosystem with public key (n,e)=(55,7)? a. (55, 23) b. (55, 15) c. (55, 39) d. None of the AboveCorrect answer will be Upvoted else downvoted. Thank you! Monoalphabetic ciphers are stronger than Polyalphabetic ciphers because frequency analysis is tougher on the former. i) True ii) False1. Asymmetric Encryption and Message Authentication: a) The primitive root of a prime number is the basic principle of Diffie-Hellman. i) Is 3 the primitive root of 11? Show the proof with your calculation. ii) What are the important criteria for selecting a prime number in cryptography? Is 11 a good choice for such a purpose? b) Find the parameters stated using the Diffie-Hellman methods, given the user A and B shared a prime number and its primitive root of 23 and 5, respectively. i) If user A public key value is 8, find the A’s private key. ii) If user B public key value is 19, what is the common secret key? c) In the following scenario, we will compare the security services that are given by digital signatures (DS) and message authentication codes (MAC). We assume that James can read all messages send from Chan to Badrul and the other way around, too. James has no knowledge of any keys but the public one in the case of DS. State whether and…

