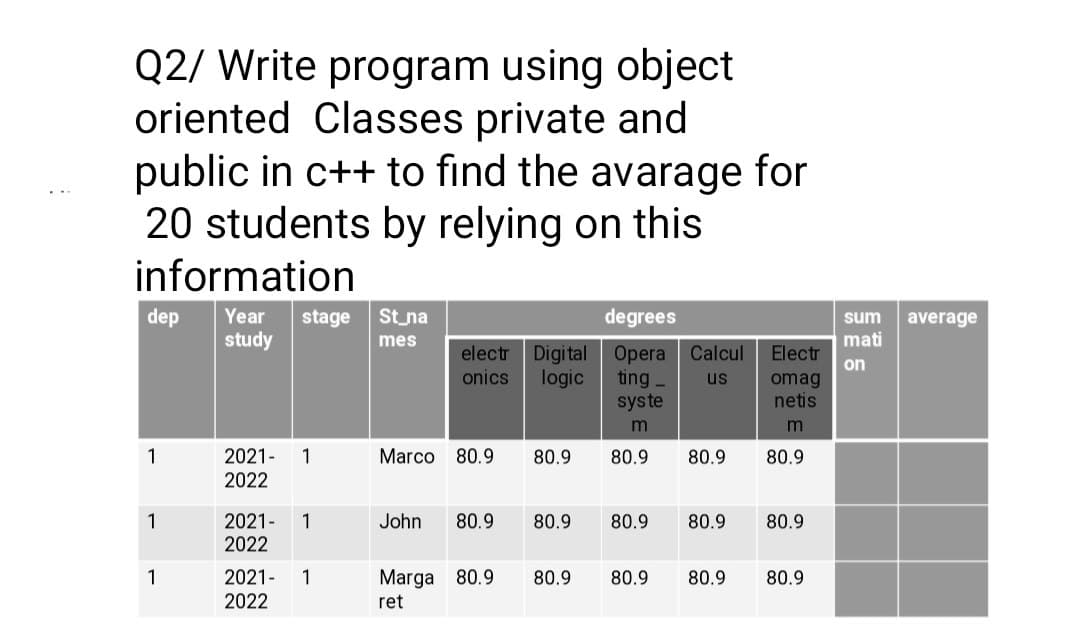
Q2/ Write program using object oriented Classes private and public in c++ to find the avarage for 20 students by relying on this
Q: Question 18 Name an example of a VoIP feature that must guarantee a specific level of service and…
A: Given question are multiple choice selected question.
Q: Is there a list of the four most important traits for software developers? Take a look at the other…
A: To Do: to list the four most crucial qualities Answer: The four most crucial aspects of software…
Q: What does data warehousing's "Hybrid Approach" entail?
A: One may define a hybrid warehouse as one that combines a variety of jobs (such as reception, storage…
Q: Which factors, if any, contribute to the growth of the whole scope of the information repository…
A: Which factors, if any, contribute to the growth of the whole scope of the information repository…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Introduction: The unique characteristics of wireless networks provide a variety of issues. Give…
Q: Convert the following IEEE 754 single-precision numbers in hexadecimal into their decimal values…
A: Ans: first of all you need to understand the format of IEEE 754 single pricision floting point…
Q: The operating system's memory-resident components are known as what? How long does it take for these…
A: Everything on a computer is controlled by the kernel, the central software component of the…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: Part-a There are essentially two methods for network maintenance: Internal IT staff: With support…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: The intrinsic characteristics of wireless networks produce a variety of obstacles.
Q: Based on your reading, what do you think was Kevin Mitnick’s motivation? What was his favorite…
A: According to Bartleby Guidelines we need to answer only one question so I have answered first…
Q: Why did the original Linux developers decide to build a kernel that does not support preemption?…
A: The non-preemptible kernel was the choice of the original Linux developers for what reason? What is…
Q: Included in the package need to be a rundown of the top five sorts of network topologies in terms of…
A: Advantages of Using a Star Topology: When compared to Bus topology, it offers significantly improved…
Q: Are there numerous sorts of technical systems and how far has technology come in the previous…
A: The answer is as below:
Q: int a int b = int tmp a = b; b = tmp; if (a < b) { = 5; } else { 12; = a; System.out.print (a +…
A: Java programming which refers to the object oriented programming languages that are used to create…
Q: Describe how a firewall resembles a data stream that has been divided into packets.
A: the answer of the question is given below
Q: Research should be done to determine the usefulness of wireless network technologies in emerging…
A: Intro In some networks, physical cabling is not used. Wireless networks are gaining popularity…
Q: Does the operating system's microkernel conform to any design principles? When compared to the…
A: Does the operating system's microkernel compared to the modular approach,
Q: Non-systems analytical techniques may benefit from structured language.
A: Definition: A system's processes can be logically understood by the analyst by using diagrams in the…
Q: An advanced UML diagram for a booking system with classes such as online booking site, reservation,…
A: We have to create UML diagram for the boking system.
Q: Question 4 What is the one and only correct value for the initial state of a mutex, and how can one…
A: The question 4 has been answered in step2, please post rest of questions separately
Q: Let's say your child uses the school's wireless LAN to connect to the internet and types in…
A: The wireless local area network is the wireless distribution method for the two or more devices.…
Q: What printers can be allocated an IP address, and which ones can't?
A: Introduction: The IP address of the printer may be printed on a network configuration page, which…
Q: Write a function NewArray.m which takes two input arguments, m and n, and returns one output…
A: We need to write a Matlab code for the given scenario.
Q: Linux partitions have an impact on the operating system's
A: Summary No. It only affects how important the zilches has to add to get to the correct LBA.…
Q: When using the waterfall process, why is there a limit set on the total number of iterations that…
A: The waterfall approach uses a linear strategy called a software development sequence. The project is…
Q: Please describe the differences between the Linux clone operating system and the conventional UNIX…
A: UNIX is an operating system which is built using set of programs. These set of programs act as a…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Given: There are several difficulties brought on by the characteristics of wireless networks. Give…
Q: 4. Write a LMC program that begins by accepting an input number. With each input instance, the…
A: 4) : Here is a program to copy : INP STO MAXloop INP BRZ…
Q: Is there anything specific to look for when it comes to software development? What are the potential…
A: Software development refers to the set of computer science activities devoted to the process of…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Given: The intrinsic characteristics of wireless networks present a variety of issues. Explain three…
Q: Operating systems with the term "kernel mode" go hand in hand.
A: The answer of the question is given below
Q: What is the process through which a virtual network interface card (vNIC) obtains a MAC address?
A: Process through which a virtual network interface card (vNIC) obtains a MAC address:- Virtual…
Q: int x = 1; String res = ""; while (res.length() if (res.length () } else { res = res + x; res < 7) {…
A: //creating variable with value x=1 int x=1; //creating empty string String res=""; //this loop…
Q: Investigate the application of Structured English in non-systematic techniques of analysis.
A: The question has been answered in step2
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: Given: Wireless networks' fundamental properties produce a variety of issues. Give examples of three…
Q: What printers can be allocated an IP address, and which ones can't?
A: Introduction The IP address is novel to the printer. It goes about as an identifier and advises a PC…
Q: Give an explanation of the advantages as well as the disadvantages that are associated with the…
A: ANSWER:-
Q: What JavaScript code belongs in the blank to create an object literal named shoes? let shoes = new…
A: In this question we have to select the correct option for the java script code to create the object…
Q: When adopting object-oriented design, everything is framed in terms of objects. How can a large (or…
A: Decomposition Using Objects Decomposition is the process of breaking down an overly complex system…
Q: What harm may spoofing do to a victim?
A: Introduction: An importer, also known as a spoofer, is a cybercriminal who poses as a reputable…
Q: For the grammar S → a ABC A → aBla BbA|b C⇒a obtain the equivalent PDA.
A:
Q: What does the word "kernel mode" signify in terms of operating systems?
A: Introduction: Kernel mode: Kernel mode and system mode are the two working modes of the central…
Q: Is there a perceptible difference between operating systems that support real-time apps and those…
A: Real-time operating systems: Are a unique kind of OS where each task has a deadline and must be…
Q: Penetration testing vs. vulnerability scanning What are a few examples of when they'd require new…
A: Introduction: Penetration is critical in business because Financial institutions such as banks,…
Q: Before deciding on a plan for the protection of a physical network, there are a few things that need…
A: Topology covers the physical: And logical configuration of a local area network in terms of the…
Q: After the SHR instruction is executed in the code sequence below, what is the final value for AL?…
A: Correct Option is B⇒ 0010_1011
Q: Question 16 Replacing long segments of coaxial cable and large amplifier cascades with optical fiber…
A: Replacing long segments of coaxial cable and large amplifier cascades with optical fiber will reduce…
Q: t utilizing the SQL programming language to change the format of an existing table? Which of these…
A: Summary First, you will start with a brief overview of the significance of learning SQL for data…
Q: Is it feasible to distinguish between computer-based architecture and computer-based management?
A: Computer architecture is a functional: Description of the specifications and design implementation…
Q: 1. Write a class "Ball" which extends the class disk. It has deltax and deltay attributes. 2. Write…
A: Code in Java Language : - class disk { } class Ball extends disk { private int deltaX, deltaY;…
Step by step
Solved in 2 steps with 2 images

- C#: PLease add inheritance and polymorphism in the code. And display the vehicle/s. Thanks!using System;using System.Collections.Generic;using System.Linq;using System.Text;using System.Threading.Tasks;namespace DemoApplication{ public class Vehicle { protected int VehicleID; protected string VehicleName; public void SetTutorial(int pID,string pName) { VehicleID=pID; VehicleName=pName; } public String GetVehicle() { return VehicleName; } } public class VehicleDetails:Vehicle { public void RenameVehicle(String pNewName) { VehicleName=pNewName; } static void Main(string[] args) { VehicleDetails VD=new VehicleDetails(); VD.RenameVehicle("CarName:Audi"); VD.RenameVehicle("Number of doors:4"); VD.RenameVehicle("Number of wheels:4"); VD.RenameVehicle("Maxspeed:180 KMPH"); VD.RenameVehicle("Fuel capacity:50 lts"); Console.WriteLine(VD.GetVehicle()); Console.ReadKey(); } }}In c++ implement function getPercentage that takes two inputs: grade and total Grade and outputsthe gradepercentage as follows: percentage = (grade/total grade)*100 . (Assume a student can notget a grade above 100%)Define your own exception classes:1. DivideByZeroException as a derived class of Standard Library class runtime_error,that is used to detect division by zero run time error.2. NegativeNumberException as a derived class of Standard Library class logic_error,that is used to detect if the user entered a negative number as a grade.3. InvalidGradeException as a derived class of Standard Library class logic_ error, thatis used to detect if a user entered an invalid input (grade greater than total grade).Use the above exception classes after implementing them to apply exception handling foryour getPercentage function.Writing the setbank functionsSetbalanceSetaccontIn order to enter the creditcard data instead of entering it into the constructor functionand execute it in the main class public class CreditCard { private String customer; private String bank; private String account; protected double balance; public CreditCard(String cust,String bk, String acnt,double initialBal) { customer=cust; bank=bk; account=acnt; balance=initialBal; } public CreditCard(String cust, String bk, String acnt) { this(cust,bk,acnt,0.0); } public String getCustomer() { return customer; } public String getBank() { return bank; } public String getAccount() { return account; } public double getBalance() { return balance; } // Update methods: public void charge(double price) { // make a charge balance += price; } public void makePayment(double amount) { // make a payment balance -= amount; }…
- Subject : object Orieted Programming Q: Find the error in the following given codes and rewrite. a). public interface intt { public void P1 (String p) { System.out.println ("figure is " + p ); } public double p2 ( ) ; } b). class B { final void r() { System.out.println("run");} } class H implements B { void r() { System.out.println("run run"); } public static void main(String args[]) { H h= new H(); h.r(); } }error on python code: File "/root/sandbox/MyMotorcycleClassProgram.py", line 11, in <module> motorcycleOne = Motorcycle(90.0)TypeError: Motorcycle.__init__() takes 1 positional argument but 2 were given from Vehicle import Vehicle # Write the Motorcycle class here class Motorcycle(Vehicle): def__init__(self): Vehicle.__init__(self) self._sidecar = sidecar defset_sidecar(self,sC): self._sidecar = sidecar defget_sidecar(self): returnself._sidecar defaccelerate(self,mph): ifself._speed + mph >self._max_speed: self._speed =self._speed + mph else: print("This motorcycle cannot go that fast.")Q1: Implement a class called Vehicle.a) A class named Vehicleb) Two private data members: brand (string), model (string), price (int).c) Accessors and Mutators function for brand, value, and price.Use following main() to test your class.int main(){Vehicle a;a.setBrand("BMW");a.setModel("X5");a.setPrice(60000);cout<<a.getBrand()<<endl; // print BMWcout<<a.getModel()<<endl; // print X5cout<<a.getPrice()<<endl; // print 60000} Q2: Continue with Vehicle class:a) Copy the previous program to a new file.b) Write Constructor with three parameter, and assign to brand, model, and price.c) Write default constructor, initialize brand to “TBD”, model to “TBD”, price to 0,Implement constructor delegationUse following main() to test your class.int main(){Vehicle a,b("Honda","Civic",25000);cout<<a.getBrand()<<endl; //print TBDcout<<a.getModel()<<endl; // print TBDcout<<a.getPrice()<<endl; //print…
- Write a program in C++ that reads a list of enrollments from a file and prints a class roster for the teacher. The program would use files, functions, and classes.Here's what the output should look like: $ ./enroll.out Welcome to the Roster Generator Program!!! Please enter the name of your names file: bob.dat I'm sorry, I could not open 'bob.dat'. Please enter another name: csc442 File 'csc442' opened successfully! Name | Major | Phone # | Town ----------------+--------------------+---------------+------------------- Jason James | Computer Science | 555/555-1122 | Westfalia, HI 665 Faruk Ahmed | Medeaval French Po | 332-4546 | Slimsville, PQ 22 Sean Ramirez | Underwater Basket | 1-444/411-441 | Fritter, HO 44331 Happy Gilmore | Yellow Tail Migrat | | Simonton, SZ 1124 Total Enrollment: 4 Thank you for using the RGP!! Endeavor to have a gyroscopic day! $Q3: Write a program in C++ using OOP to create a class (A) , that contain integer number(x) , contain the iilnction (FACT) to calculate the factorial of (x!)and create a class (B) , that contain integer number (n ) , contain the functions (POWER),to calculate ( .xü).-Illen create a Class (C) , with public visibility mode inherit from class (A)and public visibility mode inherit from class (B),contain the tunction that findQ1: Implement a class called Vehicle.a) A class named Vehicleb) Two private data members: brand (string), model (string), price (int).c) Accessors and Mutators function for brand, value and price.Use following main() to test your class.int main(){Vehicle a;a.setBrand("BMW");a.setModel("X5");a.setPrice(60000);cout<<a.getBrand()<<endl; // print BMWcout<<a.getModel()<<endl; // print X5cout<<a.getPrice()<<endl; // print 60000}
- Write a Java class Student inherited from Person class. Your class must have the following features: Student - major: String + Student() + Student(name: String, id: int, major: String) + getMajor(): String + Override toString() method: you have to return needed data Fields values. Note: major data members can take only CS for Computer Science, CIS for Computer and Information Systems, CPE for Computer Engineering, SE for Software Engineering, and NES for Network Engineering and Security.The Java Programming class has two types – remote and in-person. For remote students, the weighted score comprises of midterm, final, assignments and discussion. The weights for each are 30%, 30%, 30% and 10% respectively. For in-person students, the weighted score comprises of midterm, final and assignments. The weights for each are 30%, 30% and 40%. Write a generic class Students.java which has a constructor that takes three parameters – id, name, and type. Type will represent if the student is ‘remote’ or ‘in-person’. A toString() method in this class will display these details for any student. A generic method score() will be part of this class and it will be implemented by inherited classes. Write accessors and mutators for all data points. Write two classes RemoteStudents.java and InPersonStudents.java that inherits from Student class. Show the use of constructor from parent class (mind you, RemoteStudents have one additional parameter – discussion). Implement the abstract method…Reuse your Car class . In a main, build an object of that class, and print out the object using System.out.println(). Notice that this simply reports the memory address of the object in question, and we’d like to do something more useful. To replace (or override) the toString (or equals) function. Now, build a toString function that prints out the make, model, and odometer reading for a vehicle object. public class Car { //instance variables private int odometer; private String make; private String model; //overloading //constructors public Car(int odometer,String make, String model) { this.odometer = odometer; this.make = make; this.model = model; } public Car(String make, String model) { this.make = make; this.model = model; } public Car(String make) { this.make = make; } /* *getter & setter methods */ public int getOdometer() { return odometer; } public void…

