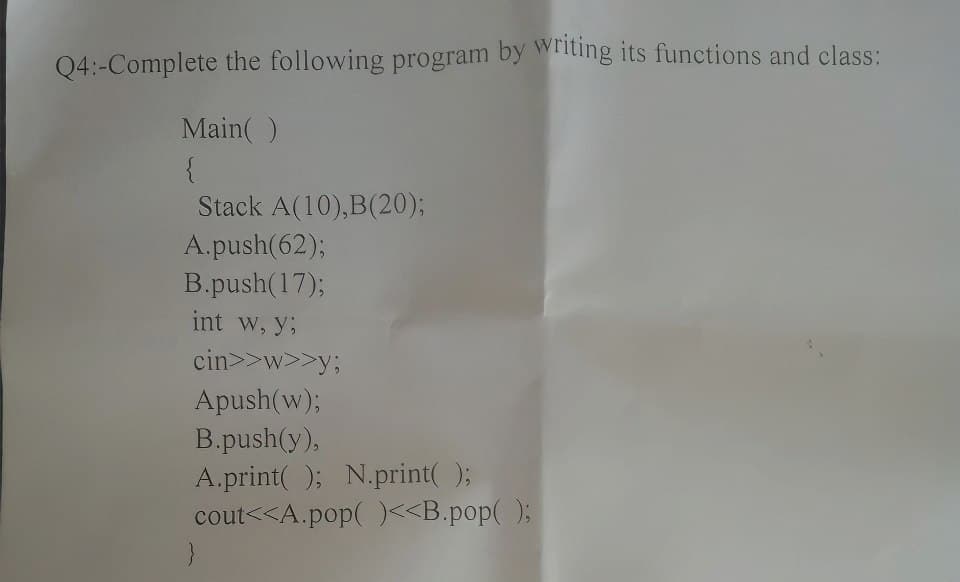
Q4:-Complete the following program by writing its functions and class: Main() { Stack A(10), B(20); A.push(62); B.push(17); int w, y; cin>>w>>y; Apush(w); B.push(y), A.print(); N.print(); cout<
Q: Directories can be implemented either as "special files" that can only be accessed in limited ways,…
A: Introduction Directories are the areas utilized for putting away the files in the PC system.
Q: When using a procedure the calling code sends data via the: Select one: a. formal parameter to the…
A: The answer to this question is in step 2
Q: Outline a simple implementation of a fault-tolerant JavaSpace.
A: Fault tolerance refers to the ability of a system (computer, network, cloud cluster, etc.) to…
Q: 172.16.0.0 (class B IP address) into four subnets. Describe each step and show the result at each
A: The answer is
Q: Please make a Sequence diagram based on State Diagram from a Bank System below :
A: Here is the Sequence diagram based on State Diagram from a Bank System above. See below steps for…
Q: What is the difference between status meetings and decision meetings? Should they always be kept…
A:
Q: What are the relative advantages of flat staffing versus gradual staffing?
A: A flat organization refers to an organization structure with few or no levels of management between…
Q: 3 Configuration management systems such as RCS, CVS, and Perforce use file names and their paths to…
A:
Q: Compare and contrast byte-stuffing and bit-stuffing. Which technique is used in byte-oriented…
A: Answer: We need to write the differences between the byte-stuffing and bit-stuffing . so we will see…
Q: Briefly describe the issues involved in using ATM technology in LANS.
A: ATM stands for Asynchronous Transfer Mode. For transmission of data from source to destination it…
Q: How does IPSec create a set of security parameters?
A:
Q: The following example is a valid compound do-while condition: do while time 0 Select one: True…
A: Basically a do-while loop synatx is a do loop is followed by a while condition. But in the above…
Q: Briefly describe the issues involved in using ATM technology in LANS.
A:
Q: Uniform Electronic Transactions Act (UETA), E-SIGN Act, and the Principles of the Law of Software…
A: The 1999-adopted Uniform Electronic Transactions Act (UETA) is known by the initials UETA. It was…
Q: ime you are part of the IEEE committee that will revise the IEE task of modeling communication as an…
A: Q SummaryLogging practices IEEE automatically records the Internet Protocol( IP) addresses of…
Q: What is the difference between status meetings and decision meetings? Should they always be kept…
A: Status meetings are regularly scheduled events at various levels where information about a project…
Q: Case Study Hello Holidays Management System Hello Holidays is a travel company based in Selangor.…
A: The question has been answered in step2
Q: 1.10 LAB: Warm up: Basic output with variables This zyLab activity prepares a student for a full…
A: Here I have taken input from the user and stored it into a variable. Next, I have printed the number…
Q: What are the relative advantages of flat staffing versus gradual staffing?
A: Here we have given a brief note on advantages of flat staffing versus gradual staffing. You can find…
Q: Q: Consider a distributed implementation of a JavaSpace in which tuples are replicated across…
A:
Q: A stream of data is being carried by STS-1 frames. If the data rate of the stream is 49.540 Mbps,…
A:
Q: Problem 1. Suppose you have to design software for the Oscar Jury members where they can ate the…
A: Code is given below #include <stdio.h>#include <stdlib.h>#include <string.h>…
Q: Linux, developed using the bazaar model, is more reliable and more responsive than many operating…
A: Linux Linux is an OS. Truth be told, quite possibly the most well-known stage on earth, Android is…
Q: (Guess the Number Modification) Modify the program of Exercise 5.32 to count the number of guesses…
A: (Guess the Number Modification) Modify the program of Exercise 5.32 to count the number of guesses…
Q: Explain why multiple-choice questionnaires, as a primary means of extracting information from the…
A: Answer : Multiple choice questionnaires is not an effective way for extracting information from…
Q: (Perfect Numbers) An integer number is said to be a perfect number if its factors, including1 (but…
A: Lets see the solution.
Q: 29. The number of combinations Chr of taking r objects out of n objects is given by: n! r!(n-r)! Cnr…
A: To find the number of combinations(C59,5 * C35,10 in the powerball lottery. Factorial(n) is a…
Q: 1. Perform encryption and decryption using the RSA algorithm for p=3, q=5, e-7, d=3, M=13, where p,…
A:
Q: . What does ESP add to the IP packet?
A:
Q: Solve the recurrence relation an = 11an-1 = 18an 2 with initial conditions ao = 0 and a₁ = 7.
A: The above question is solved in step 2 :-
Q: Q1- Write a program that create two objects (C, D) from the queue class and do the following: Add…
A: As no specific language is mentioned so I provide the code in Java along with output and code…
Q: algorithm factorial input: integer n >= 0 output: n! if n = 0: return 1 else return n * factorial(n…
A: Answer: Algorithms Step1: we have create a factorial function and pass the arguments as n Step2: if…
Q: class Solution { public: }; char repeated Character(string s) { } unordered_set u; char ans;…
A: Introduction The given code snippet is a class in which we are finding the repeated character of…
Q: 9. We discussed fixed and one-time passwords as two extremes. What about frequently changed…
A: Answer: We have explain brief in how to keep keep secure fixed password and one time password. so we…
Q: Older compilers were designed according to a pipe and filter architecture, in which each stage would…
A: Older compilers trace their lineage to batch systems, in which a stack of cards were fed to the…
Q: Older compilers were designed according to a pipe and filter architecture, in which each stage would…
A: A compiler is a special program which translates the high level source code into machine…
Q: Write a program that asks any number of students to enter their final grade and enables you to store…
A: I have provided PYTHON CODE along with TXT FILE SCREENSHOT, CODE SCREENSHOT and OUTPUT…
Q: What is the maximum number of simultaneous calls in each cell in an IS-136 (D-AMPS) system, assuming…
A:
Q: You are developing a system that stores its data on a Unix file system. You anticipate that you will…
A: User must have a bridge pattern for subsystem breakdown for the specified issue. A design pattern…
Q: How can you interpret the solution in the context of the problem?
A: How should the solution be interpreted in relation to the issue?
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A: Testing activity’s can be initiated well before implementations activity’s using requirements,…
Q: There are three major differences between software products and other industrial products. 1.…
A: ANSWER:-
Q: A message is made of 10 numbers between 00 and 99. A hash algorithm creates a digest out of this…
A:
Q: How many times would “Programming is fun” be displayed when the following is executed?…
A: Given code: ProgrammingIsFun x = 2 y = 3 do x = x + 1 do while y <=5 display…
Q: Find (49.3)10 - (00110110.0010) BCD = (?), BCD
A: The answer is
Q: Write code to get the following output using c++ languange. Unsure how to write the code in order…
A: There are three programs in the above question. Program 1: To print "Hello" along with your name.…
Q: rite a program that asks the user to enter an integer consisting of 4 digits only, and check w many…
A: Code is given below #include <iostream>using namespace std;int main() { int num,…
Q: How does IPSec create a set of security parameters?
A: Introduction: IPsec was at first evolved on the grounds that the most well-known web convention,…
Q: What is the purpose of the pointer in the line overhead?
A:
Q: Define the concept of a unified memory architecture.
A: The answer for the above mentioned question is given in the below steps for your reference.
Step by step
Solved in 6 steps with 4 images

- Assume the function: void F(stack<T> &S){ } and we send a stack S to the function F, as a result of it إختر أحد الخيارات: a. Both (copy constructor and destructor) should be called b. Both (copy constructor and destructor) should not be called c. Destructor should be called d. Copy constructor should be calledin C++ Suppose we have class named NumberList that holds a linked list of double values. In this section you will modify the class by adding recursive member functions. The functions will use recursion to traverse the linked list and perform the following operations:• Count the number of nodes in the list.To count the number of nodes in the list by recursion, we introduce two new member functions: numNodes and countNodes. countNodes is a private member function that uses recursion, and numNodes is the public interface that calls it.• Display the value of the list nodes in reverse order.To display the nodes in the list in reverse order, we introduce two new member functions: displayBackwards and showReverse. showReverse is a private member function that uses recursion, and displayBackwards is the public interface that calls it.write a program in C++ , (Postfix Evaluation) Write a program that evaluates a valid postfix expression such as 6 2 + 5 * 8 4 / -The program should read a postfix expression consisting of digits and operators into a string. Using modified versions of the stack functions implemented earlier in this chapter, the program should scan the expression and evaluate it. The algorithm is as follows: While you have not reached the end of the string, read the expression from left to right. If the current character is a digit, Push its integer value onto the stack (the integer value of a digit character is its value in the computer’s character set minus the value of '0' in the computer’s character set). Otherwise, if the current character is an operator, Pop the two top elements of the stack into variables x and y. Calculate y operator x. Push the result of the calculation onto the stack. When you reach the end of the string, pop the top value of the stack. This is the result of the postfix…
- In the following code, assume myStack is a stack that holds integers. What would be the contents of the stack after the following operations, indicating what element is currently at the top and the bottom of the stack. myStack.push(1);myStack.push(2);myStack.push(3);myStack.pop();myStack.push(4);myStack.push(5);myStack.pop(); Group of answer choices 4 <- Top21 <- Bottom 5 <- Top31 <- Bottom 4 <- Top32 <- Bottom 5 <- Top21 <- BottomTrue or False For each statement below, indicate whether you think it is True or False. If you like, you can provide a description of your answer for partial credit in case you are incorrect. Given a stack implemented as an array, and the following functions performed: Push(A), Push (B), Push(C), Pop(), Push(D), Push(E), Pop(), Push(F) The array will be [A][B][D][F] and the “top” of the stack will be at index 3 where [F] is The next element that will be removed when Pop is called will be A If we Push(G), [G] will be inserted at index 0 Given a queue implemented as an array with a maximum capacity of 5 elements and O(1) insert and remove, and the following functions are performed: Insert(7), Insert(6), Insert(5), Insert(4), Remove(), Remove(), Insert(3), Insert(2), Insert(1), Remove() The removeIndex value will be index 4 The array will be [2][1][ ][4][3] The insertIndex value will be index 2 Given a priority queue implemented as a standard linked list with only a…Task3: Some of the scientific calculators are capable of identifying errors based on the imbalance of parentheses used in mathematical equations. (4+6)*[7/(9-3)] ==> ()[()] ==> BALANCED (4+6)*7/(9-3)] ==> ()()] ==> IM-BALANCED From the above-mentioned example, we can clearly see that the checking of balance in an equation is simple, which is comparing opening parentheses with the closing ones. As a developer, you are required to write a code that checks an equation for being balanced or not.(HINT: use stack) in c++
- Project 4: Maze Solver (JAVA) The purpose of this assignment is to assess your ability to: Implement stack and queue abstract data types in JAVA Utilize stack and queue structures in a computational problem. For this question, implement a stack and a queue data structure. After testing the class, complete the depth-first search method (provided). The method should indicate whether or not a path was found, and, in the case that a path is found, output the sequence of coordinates from start to end. The following code and related files are provided. Carefully ready the code and documentation before beginning. A MazeCell class that models a cell in the maze. Each MazeCell object contains data for the row and column position of the cell, the next direction to check, and a bool variable that indicates whether or not the cell has already been visited. A Source file that creates the maze and calls your depth-first search method. An input file, maze.in, that may be used for testing. You…Stacks 1- Write a Python function that takes a user input of a word and returns True if it is a Palindrome and returns False otherwise (Your function should use a Stack data structure). A palindrome is a word that can be read the same backward as forward. Some examples of palindromic words are noon, civic, radar, level, rotor, kayak, reviver, racecar, redder, madam, and refer. 2- Write a Python function that takes a stack of integer numbers and returns the maximum value of the numbers in the stack. The stack should have the same numbers before and after calling the function. 3- Write a main function that tests the functions you wrote in 1 and 2 above and make sure that your code is well documented.Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…
- Can anyone convert this c++ code to python? //THIS PROGRAM IS CREATED TO DEMONSTRATE THE OPERATIONS PERFORMED ON STACK & ITS IMPLEMENTATION USING ARRAYS #include <iostream>#include <stdio.h>#include <conio.h>#include <stdlib.h>#include <process.h> //Defining the maximum size of the stack#define MAXSIZE 7 using namespace std; //A class initialized with public and private variables and functionsclass STACK_ARRAY { int stack[MAXSIZE]; int Top; public: //constructor is called and Top pointer is initialized to -1 when an object is created for the class STACK_ARRAY() { Top = -1; } void push(); void pop(); void traverse(); }; //This function will add/insert an element to Top of the stackvoid STACK_ARRAY::push(){ int item; //if the top pointer already reached the maximum allowed size then we can say that the stack is full or overflow if (Top == MAXSIZE-1) { cout << "\nThe Stack Is Full"; }…6. Write the prototype and definition of a new non-member function int size(…..) to the class Stack based on compile array which returns the current size (number of actual items) in your object of type StackTrue or False For each statement below, indicate whether you think it is True or False. provide a description of your answer for partial credit in case you are incorrect. 1) Given a stack implemented as an array, and the following functions performed: Push(A), Push (B), Push(C), Pop(), Push(D), Push(E), Pop(), Push(F) a. The array will be [A][B][D][F] and the “top” of the stack will be at index 3 where [F] is b. The next element that will be removed when Pop is called will be A c. If we Push(G), [G] will be inserted at index 0

