Q7: Match the following to one or more layers of the TCP/IP protocol suite: a. Route determination b. Connection to transmission media c. Providing services for the end user d. Creating user datagrams e. Responsibility for handling frames between adjacent nodes f. Converting the data from Bangla to Chinese
Q7: Match the following to one or more layers of the TCP/IP protocol suite: a. Route determination b. Connection to transmission media c. Providing services for the end user d. Creating user datagrams e. Responsibility for handling frames between adjacent nodes f. Converting the data from Bangla to Chinese
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 2TC
Related questions
Question
#7 needed
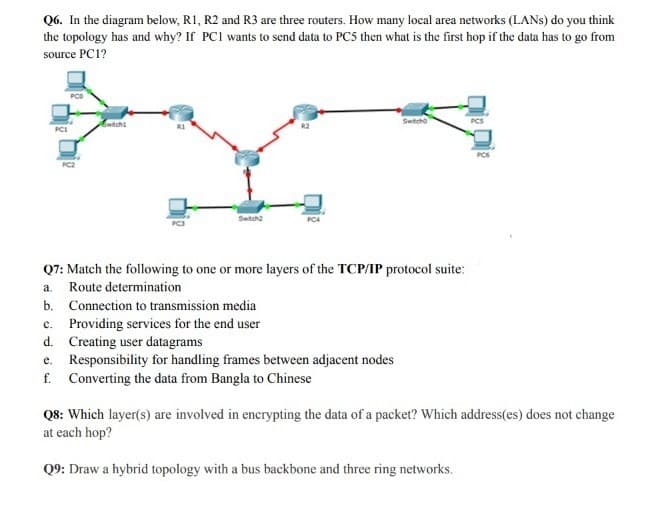
Transcribed Image Text:Q6. In the diagram below, R1, R2 and R3 are three routers. How many local area networks (LANS) do you think
the topology has and why? If PCI wants to send data to PC5 then what is the first hop if the data has to go from
source PC1?
PCI
Switch1
Switch2
PC4
Switcho
Q7: Match the following to one or more layers of the TCP/IP protocol suite:
Route determination
a.
b.
Connection to transmission media
c. Providing services for the end user
d.
Creating user datagrams
e.
Responsibility for handling frames between adjacent nodes
f. Converting the data from Bangla to Chinese
Q8: Which layer(s) are involved in encrypting the data of a packet? Which address(es) does not change
at each hop?
Q9: Draw a hybrid topology with a bus backbone and three ring networks.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning