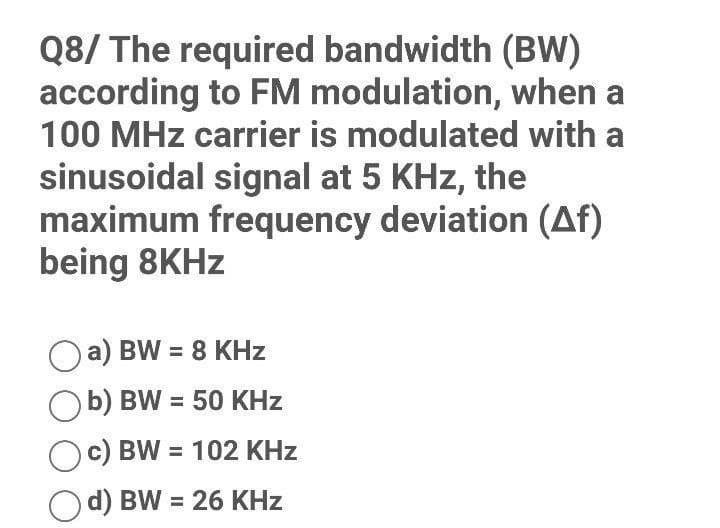
Q8/ The required bandwidth (BW) according to FM modulation, when a 100 MHz carrier is modulated with a sinusoidal signal at 5 KHz, the maximum frequency deviation (Af) being 8KHz a) BW = 8 KHz b) BW = 50 KHz c) BW= 102 KHz d) BW = 26 KHz
Q: What is the address of a private network on the public Internet? If a datagram that contains the…
A: Address of a private network: The address that your network router gives to your device is known as…
Q: Determine which of the programming codes has less time (perform algorithmic complexity calculation…
A: Solution: Code 1, has less time.
Q: What what is meant by the term "object-oriented analysis," and what are some of the advantages…
A: Object-oriented analysis and design (OOAD) is a technical method for analyzing and designing an…
Q: Operating systems on laptops and mainframes are very different. What are the commonalities and…
A: Start: In answer to your query, The mainframe operating system is a piece of network software that…
Q: How do you display the string value of an enumerator?
A: Introduction: To obtain a list of all the values contained in an enum, you may make use of the…
Q: Give an explanation of the connection between Boolean logic and the workings of computer circuits.…
A: Logic gates: Logic gates are the building blocks of computer circuits. Current flows through the…
Q: On a practical level, which network topologies do you recommend?
A: A Mesh Topology network has the most fabulous links, making it the most practical alternative.…
Q: A serious accident occurred on the National Highway, so an ambulance arrived immediately and the…
A: Input/Output Process: First line contains five space separated integers N, M, R, X and Y denoting…
Q: . If a five-digit number is input through the keyboard, write a progra ew number by adding one to…
A: solution in below step
Q: Explain the AI Turing test in a nutshell? Briefly describe the role of the Turing test in the…
A: Explain the AI Turing test in a nutshell? Briefly describe the role of the Turing test in the…
Q: What precisely is voting technology, and why is it so crucial? What are the implications for…
A: Voting technology: Voting technology is only a phrase for the tools or procedures used to gather and…
Q: Q1. Identify and discuss the various ways that Reconnaissance can be achieved by an attacker or a…
A: As I have read the guidelines I can provide answers to only 1 part of the questions in case of…
Q: What are the main characteristics of business software? What about multimedia?
A: Introduction: The utilisation of the software is essential for the automation of the operations…
Q: lease Answer all of the following questions for MSP-432 processor with detailed calculations. Thank…
A: Introduction Please Answer all of the following questions for MSP-432 processor with detailed…
Q: Propose and describe ONE (1) existing MVC framework. Explain the following information: ONE (1)…
A: Following is the one example of an existing MVC Framework-: Spring MVC: A Spring MVC is a Java…
Q: Write a java program to calculate the Gross, Tax, Net for 10 employees. Assuming: The input is…
A: import java.util.Scanner; public class Main{ public static void main(String[] args) {…
Q: Given the following array and output statement: int [] num = new int [size]; System.out.println( _);…
A: In Java, the array length is the quantity of elements that an array can holds. There is no…
Q: What does it mean when you talk about "indexed addressing?"
A: Find Your Answer Below
Q: Is it possible to explain how integrated circuits evolved into microcomputers?
A: Intro Yes, it is possible to make sense of the incorporated circuits prompted by microcomputers.…
Q: What is ODbc, and how is it used
A: Database management system is software that is used to manage the database.
Q: Various Operating Systems:The four memory allocation strategies presented in the course will be…
A: Introduction: The process of allocating physical or virtual memory space to computer applications…
Q: Building operating systems for ordinary PCs is distinct from designing operating systems for…
A: Building operating systems for ordinary PCs is distinct from designing operating systems for…
Q: What exactly is meant by the phrase "Rational Unified Process"?
A: Rational unified process is an iterative software development process framework. This process is…
Q: "My favorite number is " + 7correct data type that the above expression evaluates to in C#
A: C# (pronounced "See Sharp") is a cutting edge, object-oriented, and type-safe programming language.…
Q: It is critical to understand what a semaphore is and the many forms.
A: INTRODUCTION Semaphore is an innovation that allows processes to facilitate their activities and…
Q: For a 4 bit parallel adder with inputs A & B, if you want to perform subtraction, which one of the…
A:
Q: Consider the kind of wireless connection you'd want to use, WAN. Is it better than the other options…
A: Consider the kind of wireless connection you'd want to use, WAN. Is it better than the other options…
Q: A serious accident occurred on the National Highway, so an ambulance arrived immediately and the…
A: Program Process: Firstly we will take the value integers N, M, R, X and Y denoting the number of…
Q: In the process of developing software, a number of different models are used, and the usefulness of…
A: Developing software: Software development involves generating, designing, delivering, and supporting…
Q: How difficult is it for organisations to make the switch to a cloud computing platform? What are the…
A: The operating system and hardware of a server in a data centre connected to the Internet are…
Q: Sequentially or immediately, data may be accessed from the memory of the computer. In what ways and…
A: Memory access: Direct and sequential memory access methods are also used. Direct access is used by…
Q: What distinguishes ubiquitous computing, also known as pervasive computing, from traditional desktop…
A: Introduction: Computing Pervasive Pervasive computing refers to the incorporation of computer…
Q: Explain the process of video recording and how it relates to multimedia creation.
A: Introduction: When the circumstances and resources are appropriate, filming video is an effective…
Q: Suppose you're using WPA2 as your wireless connection. Describe why this choice is better than the…
A: WiFi-Protected Access 2 (WPA2): WPA2 adds to WPA's wireless network security. It improves data and…
Q: What do you know about wireless security? Discuss and evaluate your thoughts.
A: Examine and discuss your knowledge of wireless security. ANSWER: Unauthorized access to devices or…
Q: In terms of system maintenance, what are a splitstream upgrade, a patch, a release, and a version?
A: Introduction: Upkeep of the system System maintenance is used to meet the needs of users and the…
Q: Write only the nested for loop that prints the following numbers in columns and rows using only the…
A: We need to write a Java program using nested for loops that prints the given pattern. Algorithm : 1.…
Q: The acronym CAM refers to a memory that has the ability to check whether or not a certain datum is…
A: Find Your Answer Below
Q: What will be the result of this code? x = np.array([-2, -1, 0, 1, 2]) abs(x)
A: given array = -2,-1,0,1,2 Applying abs function will make all negative number to positive. Hence new…
Q: For the purpose of offering customers the most value for their money, an airline sought a system…
A: The Pareto Principle is almost universally used. The income generated by 20% of your customers…
Q: From the following weighted graph, which edge you will choose as a third edge using Kruskal's…
A: We need to find the 3rd chosen edge using Kruskals algorithm for the given graph.
Q: In contrast to building operating systems for PCs, designing operating systems for mainframe…
A: After being loaded into the computer by a boot program, an operating system (OS) is the program that…
Q: Create a Java program. Write statements that will output: Hello, my name is “put your name here.”,…
A: Java program with required specifications, is attached in the article. This Java program imports…
Q: Ada Lovelace is best known for what, exactly?
A: Ada Lovelace: Ada Lovelace was born on December 10, 1815. Her father was a famed poet Lord Byron.…
Q: It is imperative that the topic of network security be addressed. Is there a difference between big…
A: This same integrity, confidentiality, and accessibility of computer networks and data are protected…
Q: In what situations is cloud computing appropriate for a big and small company to use? an example of…
A: Cloud computing is a kind of computing that uses the Cloud computing is the delivery of numerous…
Q: Why do Chrome OS devices need less internal storage than machines running other desktop operating…
A: Introduction: OS (Operating System): The word "operating system" refers to the software that serves…
Q: Let G be the grammar SaA, A Abb b. Show that G is an LR(0) grammar.
A: grammar S→aA, A→Abb |bG is an LR(0) grammar explaination:
Q: For the purpose of offering customers the most value for their money, an airline sought a system…
A: Introduction: The Pareto Principle is almost universally used. The income generated by 20% of your…
Q: Take a look at business social media sites like Facebook and Twitter for ideas. What distinguishes…
A: OSN Research Introduction: Social media platforms are the simplest way to get information. Research…
Step by step
Solved in 2 steps with 2 images

- Computer Science Describe the capabilities and bandwidth efficiency of codes in terms of their coding rate, hamming distance and coding gain. And explain the relationships between bandwidth and spreading bit rate.Computer Science Q1(a) Wi-Fi host based on 802.11g@2.4GHz transmits signal with maximum Tx power 30 dBm and antenna gain 6 dBi,then calculate feasible radio range above sensivity level, - 105dBm. (b) from (a) we would like to apply modulation scheme QAM64 to the receiver host at the end of the range.How much BER will the receiver have?2. Suppose a modem uses Quadrature Amplitude Modulation described by the constellation pattern and bit assignment given below. Draw the corresponding encoding of the digital data given below. Assume that the previous signal ended at phase theta = pi . Label each signal modulation with the bit pattern it represents. 0 1 0 1 0 1 0 0 0 1 1 1 1 1 0
- Assume having a low-pass channel that spans from a Frequency of 0Hz to 110Hz, to attain a bit-rate value that is not less than 1Kbps, then among the following, the minimum value of the signal to noise ratio must be: Select one: A. None of the mentioned choices is correct B. 1023 C. 511 D. 15 E. 31 F. 127 G. 255 H. 63Networking price Consider the following bit stream-a. 00000000 b. 11111111 c. 01010101 d. 00110011 Draw the graph of the i. Manchester using each of the given data streams, assuming that the last signal level has been positive. From thegraphs, guess the bandwidth for this scheme using the average number of changes in the signal level.Subject: Data Communication Networks Q2) Suppose that the following 12-bit Hamming code bit stream 101100101101 arrives at receiver. Show how you compute the error syndrome. What is the original sent bit stream? Q3) For the bit stream 010110011010, sketch the waveform for each of the following digital encoding schemes: NRZ, NRZI, Manchester and Manchester Differential Thanks in advance
- Networking question: Consider the following bit stream-a. 00000000 b. 11111111 c. 01010101 d. 00110011 Draw the graph of thei. NRZ-Lii. NRZ-Iiii. Manchesteriv. differential Manchester schemeusing each of the given data streams, assuming that the last signal level has been positive. From the graphs, guess the bandwidth for this scheme using the average number of changes in the signal level.A digitized voice channel is made by digitizing a 4-kHz bandwidthanalog voice signal. We need to sample the signal at twice the highestfrequency. We assume that each sample requires 16 bits. What is therequired bit rate?The bandwidth of 200 kHz is available which spans from 300 to 500 kilohertz. Calculate the bit rate ifthe data modulation is performed by using ASK and FSK with d = 0? (need answer in hurry)
- For the following stream of digital signal which is being transmitted by bit rate 5 Kbps: 101100000000110 a) Draw the waveform for all line codes you studied. b) Determine if the line code is self synchronized or not. c) Determine if the code can be used with ac coupling or not d) Determine the Bandwidth of the line code e) Which code is used in magnetic recording f) Which code is used in LANA Wi-Fi station with one antenna is connected to an Access Point with a PHY rate of 65 Mbps. The channel is using 52 subcarriers, the coding rate is 1/2 and the symbol duration is configured for 4 microseconds. How many amplitude modulation levels are used by this radio?133. Baseband is a. a signal all of whose energy is contained within a finite frequency range b. the simultaneous transmission of data to a number of stations c. transmission of signals without modulation d. All of the above



