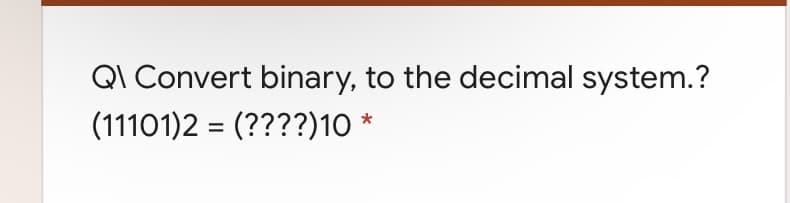
QI Convert binary, to the decimal system.? (11101)2 = (????)10 *
Q: The task of detecting a cat present in a given image or not. To finish this task, you create two net...
A: Multilayer perception is a feedforward neural network has one or more inputs and output. This is bac...
Q: Day 11 Criteria Write a program to generate the below series: 24,60,120,210,… Input Format: Inpu...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read n value Iterat...
Q: The following recursion occurs when there are more than two calls for each non-base case: : c)Multi...
A: Introduction: Recursion: The process in which a function calls itself directly or indirectly is call...
Q: The data structures help mostly to: b)Debug programs c)Create inheritance hierarchies a)Organize ...
A: The data structures help mostly to:
Q: 1. Write a program that implements the Newton method to solve f(x) = 0, where both f and x are vecto...
A: Answer is given below:
Q: Assume the size of an integer array is stored in $s0 and the address of the first element of the ar...
A: Answer: .datafibs: .word 0 : 40prompt2: .asciiz "The series is as below\n"prompt3: .asciiz " "prompt...
Q: Networks 172.16.0.0/16, 172.20.0.0/16 and 172.23.0.0/16 can all be reached out of port S0/1/0 of a r...
A: For the given network as 172.16.0.0/16, 172.20.0.0/16 and 172.23.0.0/16 can all be reached out of po...
Q: Employee class is having three properties known as name, EmployeeID, address. Write a Java program t...
A: Algorithm: Start Create a class named Employee with name, EmployeeID and address as its attributes ...
Q: The value of the candidate key cannot uniquely identify each tuple in a relation. True O False Quest...
A: 1. The Value of the Candidate key is used to Identify the unique tuple in the relation. Your Answer ...
Q: What type of protocol is BGP? a. Link State Protocol b. Distance Vector protocol c. Brigde Gateke...
A: BGP PROTOCOL: A BGP stands for Border Gateway Protocol.The BGP protocol is the one of the most impor...
Q: What is the output of the following program? Explain why?
A: Program Explanation: Define a class for boy with the instance variable age having a default value o...
Q: ____ the number of arrangements of n objects in a given order of the objects r at a time.
A: Introduction: The answer is Permutations
Q: ethod GetLarge
A: Syntax of GetLargestConsoleWindowSize: COORD WINAPI GetLargestConsoleWindowSize( _In_ HANDLE hConso...
Q: 9. Based on the below Verilog statements, how many bits are there in the variable Y? Reg [15:0] A; R...
A: Verilog, standardized as IEEE 1364, is a hardware description language (HDL) used to model electroni...
Q: Find the error in each of the following code segments and explain how to correct it. а) x = 1; while...
A: a) x = 1; while(x <= 10); x++; } In this code we have several errors: x datatype is...
Q: Complete this sentence: IPv6 addresses… a. … are 64 bits long and written in hexadecimal b. … ...
A: The correct answer will be option(d) Explanation:- ipv6 addresses are 128 bits long and written in ...
Q: What kind of rule protect every right when we use each other content?
A: The rule to protect every right when we use each other content is Fair use. It is the rule which def...
Q: ufferInfo method des
A: Syntax of GetConsoleScreenBufferInfo: BOOL WINAPI GetConsoleScreenBufferInfo( _In_ HANDLE ...
Q: e a function called multiplyMe which has a variable number of integers as arguments and returns the ...
A: It is defined as the function definition starts with the keyword def. It must be followed by the fun...
Q: Python can you give me some examples and explanation step by step for the following difference with ...
A: Boolean values in python is represented by True and False. Float operations are also allowed in pyt...
Q: Part 2 1. Design an algorithm to test whether there is at least one common element between two sets ...
A: Due to company policies I am compelled to solve only 1 question and that is the first question. Plea...
Q: Write an algorithm and flowcharts for the following: a. Sum the even numbers for n numbers.
A: As per our guidelines we are suppose to answer only first question. Kindly repost other question sep...
Q: 9. Use the Dijkstra's algorithm to find the shortest path between the nodes A and Z in the diagram s...
A: Dijkstra's algorithm to find shortest path of the given graph From A we can move to four direction i...
Q: Write a PYTHON Script to find y from the below equations depending on your entry. tan(4)-cos (0) sin...
A:
Q: Create a class called Matrix that represents a 3x3 matrix. This matrix contains a two-dimensional in...
A: Algorithm: Start Create a class named Matrix with a 2d integer array 'a' of size 3x3 as an attribut...
Q: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark we...
A: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark ...
Q: he following recursion occurs when there are more than two calls for each non-base case: : c)Multip...
A: SUMMARY: -Hence, we discussed all the points.
Q: Write 20 examples of variable declaration
A: Note:- No programming language is mentioned in the question that's why I consider the c++ programmi...
Q: Problem 5 :Recursion Tree Time Complexity Find the Worst case time Complexity of the following recur...
A: as per company guidelines, if multiple quesions posted then only first question answer can be given....
Q: What is the main goal of two application software?
A: The two application software are Database software:-A database software programme or utility is a...
Q: 20. Which of the following two data manipulation operators, AND and OR, will retrieve the most recor...
A: The employees table CREATE TABLE employees ( empid INTEGER PRIMARY KEY, empname TEXT NOT NULL, ...
Q: In the uniform cost algorithm, which values are stored in the priority queue for each cell? ...
A: In the uniform cost algorithm, which values are stored in the priority queue for each cell?
Q: Explair
A: given - explain briefly how the switch dynamically build the MAC address table (learn process)
Q: When forming a public key for an RSA cipher, real applications involve pairs of long prime numbers, ...
A: RSA is a type of asymmetric encryption which uses both public and private keys but these two keys mu...
Q: Write a program that inputs a sequence of non negative numbers terminated by a negative value and sh...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read a sequence of ...
Q: What does the facebook reveal about the culture and time period in which it was invented and used? H...
A: Given: What does the invention and usage of Facebook tell about the society and historical period in...
Q: In general terms, describe the main logical database design techniques and how they relate to each o...
A: In general terms, describe the main logical database design techniques and how they relate to each o...
Q: 4. Build a Max-Heap on the following array A = Show all the steps.
A: I'm providing the answer to above question. I hope this will be helpful for you
Q: Create a java program 1. Broken Record Looping strings works like playing a broken record – it repea...
A: Program explanation: Import the Scanner class Define a public class to implement the logic asked ...
Q: int sum (int n) {//assume n is non-negative if (0 == n) return 0; else n+ sum (n-1); |
A: the correct code should be like that
Q: Clustering and classification are two different things. What is the difference between them?
A: Introduction: In general, machine learning algorithms use either unsupervised or supervised learning...
Q: Which of the following are elements of a good Mobile Device Management (MDM) policy? Select all that...
A: To find elements of a good Mobile Device Management (MDM) policy.
Q: 5. Consider the following modification of the independent set problem. As input, you receive an undi...
A: An Unaffiliated Group S is a collection of vertices in the given Graph = (V, E) in which no two vert...
Q: Let's say that B is an array with a size of n > 6 that has integers from 1 to n-5, inclusive, in it....
A: Introduction: Complexity of algorithms: There are various methods for calculating algorithm complexi...
Q: Provide a detailed description of the AllocConsole function.
A: AllocConsole() The name itself sugggest the meaning of the function. Alloc is the allocation . Henc...
Q: Write a mini forensics tool to collect identifying information from PDF metadata. please explain the...
A: In order to extract PDF metadata, we’ll use Aspose.PDF for C++ API which is a feature-rich, powerf...
Q: Using Access, an employee at JC Consulting tried to delete TaskID CODE01 from the TaskMasterList tab...
A: The solution is given below for the above-given question.
Q: sing Columnar transposition encrypt the message “MUSCAT IS THE CAPITAL CITY OF OMAN ", using key MAD...
A: Columnar transposition is a kind of transposition cipher. The message which has to be encrypted is w...
Q: the for..next, do..loop and wh
A: We need to read in user input and compute the Vowel count and display the result.
Q: Write a c++ code that takes a 4-digit binary number as an input and converts it into decimal then ou...
A: Input : 4 digit binary number Output : Print the number in decimal Programming Language : C++ Exa...
Step by step
Solved in 2 steps

- How can binary values be converted into unsigned and signed integers?Question 1. Convert the following numbers from one base to another, all steps must be shown Convert (7139)16to ( ? )10 Convert (02114)16to ( ? )2 Convert (913E)16to ( ? )2 Convert (063)8to ( ? )2 Convert (7FACD)16to ( ? )8What decimal value does the 8-bit binary number 00010001have if: 1. a) It is interpreted as an unsigned number?2. b) It is on a computer using signed-magnituderepresentation?3. c) It is on a computer using one’s complementrepresentation?4. d) It is on a computer using two’s complementrepresentation?5. e) It is on a computer using excess-127 representation?
- PLEASE EXPLAIN THE PROBLEM BEOW AND THE ANSWER Given the following structs, how many bytes would a single A take up? Answer in decimal only. struct A { char* str1; char ch; int* i, j; B a, b, c; }; struct B { A* a; }; Answer =What decimal value does the 8-bit binary number 10011110have if:1. a) It is interpreted as an unsigned number?b) It is on a computer using signed-magnituderepresentation?2. c) It is on a computer using one’s complementrepresentation?3. d) It is on a computer using two’s complementrepresentation?4. e) It is on a computer using excess-127 representation?Answer it correctly and explain well. Type answer please. I ll rate. What bitwise operator do you use to remove the last bit? How do you turn 101 into 10? 101 _____ 1 Fill in the blank
- How many 88-bit binary strings are there subject to each of the following restrictions? 1. The string starts with 001001. 2. The string starts with 001001 or 1010. 3. The string has exactly 4 zero’s. 4. The string has exactly 4 zeros’s and the first bit is 1.FILL IN THE BLANKS: Q. 3104: Before data can be transmitted, they must be transformed to ________.Convert the following Decimal numbers into Binary, Hex and Octal Your street number address or any other address you prefer to use. 1160 Hialeah LN Your favorite actor's year of birth june 5th 1971 The sum of the course numbers you are taking this semester. 6048 The length in seconds of your favorite song. 3.23 The number of bytes available on your hard drive. 164 The population of a city or state you choose. 12.67 million The distance in miles from your home to COD. 14.7 m The IP address of your favorite website. google IPv4: 8.8.8.8 Convert your firstname and lastname into ASCII and show respective values in 4 numbering systems (bin, oct, dec, hex) Michael Anzuini
- Binary numerals are used to assign each item in a store's inventory a distinct binary sequence. What is the minimum number of bits required for each binary sequence if the store has between 75 and 100 items in stock?Upvote for correct answer.Thanks. (5) Please perform the following Binary arithmetic. SHOW ALL WORK (5.1) 00111 + 11101 = ? (5.2) 11011 * 10101 = ?a. What decimal number is represented by the following single precisionfloat?1 0111 1100 0110 0000 0110 0000 0000 000b. What decimal number is represented by the following single precisionfloat?1 0101 1100 0110 0010 0110 0000 0000 000c. How many bits are needed to represent 57B(Hex) in binary?

