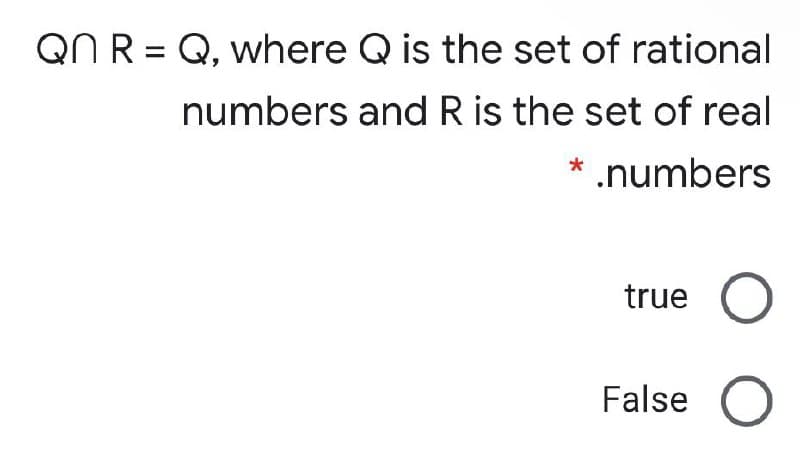
QN R = Q, where Q is the set of rational numbers and R is the set of real * .numbers true False
Q: Retail price calculator Write a program that asks the user to enter an item’s wholesale cost and its...
A: Step 1 : Start Step 2 : Define a method calculateRetail() to calculate and return the retail price o...
Q: In order for a TryParse method to work,
A: we have three choices : Parse, Convert, and TryParse. My idea is use which have three choices : Par...
Q: How does Oracle 12c distinguish between clauses in a SELECT statement that belong to an outer query ...
A: Introduction: In SQL, the from clause may be used to provide a sub-query phrase. The sub-result que...
Q: One of the most common types of cybercrime is identity theft. Explain how hackers can steal your ide...
A: Intro Today cyber crime is one of the most prevalent crimes in the era of the digital world.
Q: Describe the notion of completeness of R in layman's term
A: Describe the notion of completeness of R in layman's term
Q: Explain, using at least one example, distributed databases and distributed processes. Explain at ...
A: Introduction: Distributed Databases:- The distributed database is a collection of databases that re...
Q: a common task for which a logic paradigm would make sense a common task for which a functional para...
A: Logic programming paradigms -It can be called an invisible calculation model. It can solve logical p...
Q: design and debug a program to calculate an approximation of the value of π = 4 x (1 – 1/3+1/5-1/7+1/...
A: PROGRAM INTRODUCTION: Include the required header files. Start the definition of the main function....
Q: Users can interact with a telephone menu system by speaking instead of pressing buttons on the dial ...
A: Two arguments in support of speech recognition technology: Talking is faster than typing! Voice com...
Q: What model comes to mind first when you think about the Verification and Validation Model?
A: Introduction: Validation and verification The techniques for assessing and gaining confidence in mod...
Q: int i; for (i=0;i=2){ GPIOD_ODR &=~(1<<(i-2)); } } At each iteration what is LEDS that will be on fr...
A: According to the question, we have to explain that at each iteration which LED will be ON. In Step 2...
Q: What exactly is the TextAlign property?
A: Introduction: "TextAlign" property: The property used for determining the alignment of the text i...
Q: (RS + R)* RS = (RR*S)* true or false prove and explain
A: Here, we have to check whether given regular expressions are equivalent or not. Using basic regular ...
Q: The services of two transport-layer protocols are available to some application programs (UDP or TCP...
A: Introduction: TCP is engaged in the communication if the devices are directly linked. If data is sha...
Q: What is the most effective strategy for memory management, and why is it the most successful?
A: Introduction: This website has been diverted from the phrase "effective." Side Effect's CD is effect...
Q: Describe the technique for views to save reprogramming time.
A: Let us see the answer Introduction The state preservation and restoration procedure relies heavily o...
Q: Why is the central processing unit (CPU) the most crucial component in a computer
A: Introduction: The central processing unit (CPU), or microprocessor, is the most critical of these co...
Q: What governance mechanisms need to be put in place to ensure common customer data and a shared custo...
A: Let's see the solution in the next steps
Q: In what ways does knowing about compressed zip files and folders help you in your professional life.
A: Compressed files and folders take up less space on your computer and are easier to access than their...
Q: n algorith
A: given - What are the main steps of the resolution algorithm?
Q: Write a Java program to take an array of ints, print the number of 9's in that array.
A: Write a JAVA program to take an array of integers and print the number of 9's in the array.
Q: PUSH and POP instruction always transfer one byte of data : TRUE or FALSE?
A: answer is
Q: What are the benefits of virtual private networks in terms of a company's commercial needs?
A: Introduction: The VPN uses tunnelling, also known as virtual point-to-point connection technology, t...
Q: The authors claim "Poorly crafted law in this area aimed at protecting imperfect technological solut...
A: The paper "Poorly crafted law in this area aimed at protecting imperfect technological solutions res...
Q: Provide a description for Clrscr.
A: Intro Description for Clrscr- During the working on the console screen, we should keep clean and sob...
Q: How many bytes are in a zettabyte?
A: 1 zettabyte = 1021 bytes
Q: What exactly is the meaning of cloud scalability? What are some of the characteristics of cloud comp...
A: Let us see the answer:- Introduction:- In cloud computing, scalability refers to the capacity to sc...
Q: e a Python program that prints all the numbers from 0 to 6 except 3 a
A: I have written code below:
Q: Give a DFA (both state transition diagram and table as well as a description of each state) for the ...
A: The full DFA for the given problem statement is mentioned below. You can check for all cases the DFA...
Q: What is the best method for determining the function of an application that is currently executing o...
A: Introduction: Utility programmes are the tools that helped us analyse the programme and provide info...
Q: Recognize the type of information system that clerical staff in a company are most likely to use and...
A: Find the answer given as below :
Q: 10. Largest and Smallest Write a program with a loop that lets the user enter a series of integers. ...
A:
Q: Item Counter Assume that a file containing a series of names (as strings) is named names.dat and ex...
A: Here is your program that displays the number of names that are stored in the file.
Q: Given a BST, Jlven heap insertion
A: import java.util.ArrayList;class Test {static class Node {int info; Node left, right;Node(){ this.i...
Q: following strategies to prevent a race condition on the variable hits. The first strategy is to...
A: First Method int hits; mutex lock hit lock; hit lock.acquire(); hit lock.release(); System call is r...
Q: Explain clearly and state TWO reasons why writing user-defined functions is a good idea while design...
A: INTRODUCTION: A function is a code block that does a certain purpose. User-defined functions are fu...
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A: 1st bit represent sign 2-9th bit represent exponent 10-32 represent Mantissa or Fraction part
Q: Consider utilising structured language to describe processes that are not part of a systems analysis...
A: Introduction: Structured analysis employs data flow and entity connection models, process requiremen...
Q: (In Multisim) In this assignment, you design a Hex to 7-segment decoder to be used in building a 3-d...
A: According to the question we need to design a Hex to 7-segment decoder to be used in building a 3-di...
Q: We can use an array to create a priority queue. Choose from the following options: a. sort the objec...
A: Introduction: Priority Queue is an abstract data type, similar to a queue, except each member in the...
Q: Consider the set of vectors S = (9, 6, −1), (1, −7, 3), (−6, 9, 5), (3, 1, 5). (a) Create a linear p...
A: The Algebraic Method, introduced at the outset, has its limitations in that it results in every deta...
Q: An SR flip-flop accepts 2 inputs at S and R respectively, and produces 2 outputs Q and Q. Currently,...
A: Please refer below for your reference: The truth table for S-R flip flop is: S R Q Q' 0 0 memor...
Q: Part 1: Create a class named Supermarket representing an items show in a supermarket sections with t...
A: 1) Below is C++ Program to define Supermarket class with data memebers, constructor and methods It ...
Q: 30=To for K in range(0,To) IF k%4==0: print (K*4) clse
A: Let us see the answer:- To=30 for K in range(0, To) : If K%4==0: print(K*4) else: ...
Q: Computer Programming Java Write a method named FirstHalf that receives a String parameter named wo...
A: ALGORITHM:- 1. Take input from the user as string. 2. Compute the first half of the string using sub...
Q: What exactly is a wireless infrastructure network, and how does it function? When the network is not...
A: Introduction: A Wi-Fi network in infrastructure mode is one in which a Wi-Fi router produces the net...
Q: A computer uses a mapping procedure between main and cache memory. If the main memory has 128 blocks...
A: (1) Block 15,31,47 and 63 are the block addresses of main memory that may be placed in location 15 o...
Q: Why is it only possible to use TCP on endpoint devices?
A: TCP stands for Transmission Control Protocol, which is a type of communication protocol used by netw...
Q: What is pseudocode, and how does it work
A: What is pseudo code, and how does it work? Answer: Pseudo code is a term which is often used in pro...
Q: Write ONLY Header (No body{}) of function for each question. You can use any valid variable name for...
A: A constructor is a special function that has name same as that of class So the function name here wi...
Step by step
Solved in 2 steps

- n and n+1 are integers with the same number of positive divisions. Find the integers n from 1<n<107. For example, the positive divisors of 14 are 1, 2, 7, 14, and 15 are 1, 3, 5, 15. (P.s.: You have to done it by C++.)1. Let L = {w {a, b}* : w contains bba as a substring that starts in an odd numbered position in the string (where numbering starts at 1)}. For example, bbbbaaaab L, while bbbaaaab L. Show an NDFSM that accepts LReturns the missing number from a sequence of unique integers in range [0..n] in O(n) time and space. The difference between consecutive integers cannot be more than 1. If the sequence is already complete, the next integer in the sequence will be returned. For example: Input: nums = [4, 1, 3, 0, 6, 5, 2] Output: 7"""def find_missing_number(nums): missing = 0 for i, num in enumerate(nums): missing ^= num missing ^= i + 1 return missing.
- PLEASE CODE IN PYTHON Crypto Columns The columnar encryption scheme scrambles the letters in a message (or plaintext) using a keyword as illustrated in the following example: Suppose BATBOY is the keyword and our message is MEET ME BY THE OLD OAK TREE. Since the keyword has 6 letters, we write the message (ignoring spacing and punctuation) in a grid with 6 columns, padding with random extra letters as needed: MEETME BYTHEO LDOAKT REENTH Here, we've padded the message with NTH. Now the message is printed out by columns, but the columns are printed in the order determined by the letters in the keyword. Since A is the letter of the keyword that comes first in the alphabet, column 2 is printed first. The next letter, B, occurs twice. In the case of a tie like this we print the columns leftmost first, so we print column 1, then column 4. This continues, printing the remaining columns in order 5, 3 and finally 6. So, the order the columns of the grid are printed would be 2, 1, 4, 5, 3, 6, in…4. True or FalseFor any two elements define [a,b] = { {a}, {a,b} } and check the true statementsa ∈ [a,b] T [ ] F [ ]{a} ∈ [a,b] T [ ] F [ ]{a.b} ∈ [a,b] T [ ] F [ ]{b} ∈ [a,b] T [ ] F [ ][a,b] = [b,a] T [ ] F [ ][a,a] = { {a} } T [ ] F [ ]Consider the given pmgqgh finclude(iostren} using namespace std; int main(){ //int n=2 take of y for(int i=0;i
- java: Run length coding is a method to represent a string in a more compact manner. Each character that occurs more than 2 times in a row is represented by the character and a number following it. Two examples are: "abba" → "abba""abcccbbbba" → "abc3b4a"Write a function that calculates how many characters the encoded string is shorter than the original.Q 3 Computer Science Modify the permutation code such that the program can handle finding unique passwords of string that contains potentially duplicate letters. How many unique passwords are there that use all the letters of "eelrstt"?equality (5)/(9)x+(0)/(2)>=(5)/(2)x+(1)/(6). Enter your answer using int
- Write a java code for search number using divide and conquer with the help of the Fibbonaci numbersint i cannot be changed with int pos I have to fill in the program that is missing in the middle by using what is already there in C++. Started with this but does not like it cout << "Enter passwdStr: "; getline(cin, passwdStr); while (passwdStr.find("qwerty") != string::npos) { passwdStr.replace(int i, 6, "mvhnkl"); i = passwdStr.find("qwerty"); }def find_root4(x, epsilon): ''' IN PYTHON Assume: x, epsilon are floating point numbers and epsilon > 0 Use bisection search to find the following root of x such that If x >=0, return y such that x - epsilon <= y ** 2 <= x + epsilon Else, return y such that x - epsilon <= y ** 7 <= x + epsilon Note: You must use bisection search to implement the function. ''' pass



