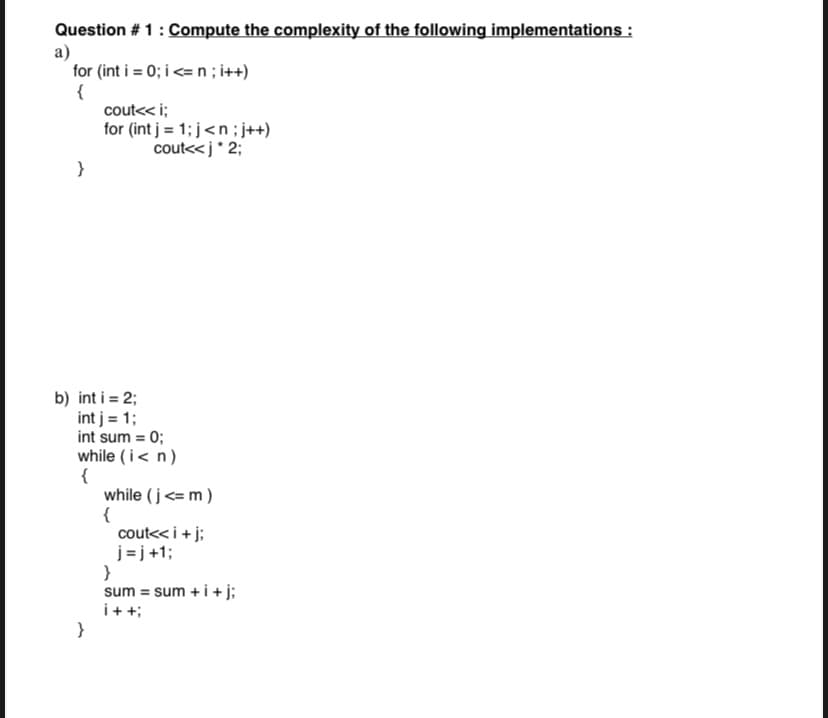
Question #1: Compute the complexity of the following implementations : a) for (int i = 0; i
Q: 2. 2. Suppose a computer using direct-mapped cache has 2³2 bytes of byte-addressable main memory and…
A: Given Data Main Memory Size = 232 Bytes Number of Cache Blocks = 1024 = 210 Block Size = 32 Bytes =…
Q: Write an efficient Selection Structure that accomplishes the following task: Covid-19 Vaccination…
A: The complete python code is below:
Q: Create a left rotation and a right rotation function that returns all the left rotations and right…
A: In this problem, we need to design the code to get the expected output. Please use the below logic…
Q: When I go to type my input it does let me add a single space also the second line here m =…
A: After updating the code, I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT…
Q: Design the code for the below expected outcome and argument
A: Start define a function named "mod" with two parameters 'm' and 'n' Now, return the value of '((n %…
Q: Explain Interacting Cognitive Subsystems (ICS) model.
A:
Q: Write the command that will show all the files in the guitars directory from the question above that…
A: This is very simple. The solution provided is completely wrong. Here is the complete solution.…
Q: 8 59 40 41 42 Bookmarks 43 44 45 Structure 46 ' 48 49 50 51 D T W B // initialize the notebook…
A: notebook.clearNote(); while (true) { System.out.println("Please type your note: "); String…
Q: 3. The city of Mawroke maintains a constant voter of 300,000 people per year. Apolitical science…
A: SOLUTION
Q: 6. What is the MARIE instruction for the following register tra
A: What is the MARIE instruction for the following register transfer language (RTL): MAR← X MBR ←…
Q: What is the use of Conventional memory in the system?
A: Given To know about the conventional memory in the system.
Q: What is the use of Conventional memory in the system?
A: Use of conventional memory in the system
Q: Customers SSNO PK name addr phone 1..1 0..* PK Bookings row seat PK 0..* 1..1 Flights number PK day…
A: Explanation:1. Supporting relationships are represented by the Relations, which are the many-to-one…
Q: Declare an array of 10 integers named arr and initialize the array so that all 10 integers are 0.…
A: The c++ program is given below:
Q: List advantages and disadvantages of user centered design.
A: A product can be designed using various types of strategies.
Q: While useful, the modulo operator in JavaScript is not infallible when negative numbers are thrown…
A: Algorithm - Create a function with two argument. Now use the below logic - if…
Q: Consider the following grammar : S a|b|(T) T T,S | S a) Whatisthetypeofthisgrammar? b)…
A: A parse tree is made up of nodes and branches.
Q: Give a specific example of the use of AI and ML technique for Big Data Digital Forensics application
A: Introduction: Machine learning and AI includes no earlier presumptions with respect to the hidden…
Q: 2. Show how the following values would be stored by byte- addressable machines with 32-bit words,…
A: The complete answer is below:
Q: ompany makes items. Each item has a name, ID and component y item contains many components. Each…
A: Description: 1- Yes, the user can use Lucidchart to draw the ERD.2- There are many platform user…
Q: Create a function that takes a string and returns it back in camelCase. Examples camelCasing ("Hello…
A: Python Introduction:-Python is an interpretive, dynamic, and bytecode-compiled language. The kinds…
Q: onsider the following context-free grammar: Give the four elements of this grammar{T,N,S,P} Show…
A: The context-free languages are a larger set of languages than the regular languages that we have…
Q: Can you help write an assembly language program that will read a string of ASCII characters from the…
A: python introduction Python is a high-level, interpreted programming language that may be used for…
Q: Linux Questions: What is this an example of? What is the stream number of the output?…
A: T o solve this question, one needs to have knowledge regarding Linux OS, and executing commands at…
Q: the following lab by one dimensional array(not vector) define two lists of numbers (arrays) and ask…
A: Question1: Do the following lab by one dimensional array(not vector) define two lists of numbers…
Q: Q.8 When systems are not designed to match the way people actually work, then users end up having to…
A:
Q: 8. 8. A 2-way set-associative cache consists of four sets. Main memory contains 2K blocks of 8 bytes…
A: Given:- Number of blocks in the main memory = 2K Number of bytes of each block = 8 bytes The…
Q: I'm getting this progm to run but vis producing no out put.
A: After fixing some errors, I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT…
Q: Define ANN. Advantages of working with ANN
A: ANN, also known as "Artificial Neural Network". It is a field of Artificial Intelligence. It mimics…
Q: Write a program that outputs all integers within a range. The program takes three integer inputs.…
A:
Q: Describe the two paradigms (approaches) for architecture development. Mention at least one example…
A: Answer: We need to write the two approach for the architecture development . so we will see in the…
Q: (b) If each stage has 4 bits, what is minimum number of bits (N) needed in order for the…
A: Answers:- Given data:- Each stage has 4 bit n=4 tsetup=tsum=2tcarry=tmux=1
Q: The code you submit should apply all three findPath functions to each map, one after the other. The…
A: solution
Q: Explain limitations keystroke-level model.
A: Limitations of Keystroke Model Level (KML)
Q: P-6.40 Give a complete implementation of the Deque ADT using a fixed-capacity array, so that each of…
A: Explanation:A fixed-size array is used to implement the Deque abstract data type in the previous…
Q: C program A decimal number between 0 and 32 exclusive can be expressed in binary system as…
A: Solution- An C program that accept the decimal number in particular range of 0 to 32 and print out…
Q: Simulated annealing requires a very small amount of memory, just enough to store two states: the…
A: Given: Simulated annealing requires a very small amount of memory, just enough to store two states:…
Q: What command can I use to add these two files together and place them in a new file called whhaatt?…
A: Answer is attached in step 2 along with explanation.
Q: Show exact output?
A: In step 2, I have provided ANSWER with breif explanation----------- In further steps , I have…
Q: Briefly explain in your own words, describing the use case example of machine learning for…
A: Solution: Given, Briefly explain in your own words, describing the use case example of machine…
Q: Convert the number 83 to 2's complement (Binary form)
A: Number : 83 Let's convert this to two's complement binary 83 Since this is a positive number. we can…
Q: 1. The fundamental cause of XSS vulnerabilities is that HTML allows JavaScript code to be mixed…
A: Solution -The primary reason for XSS vulnerabilities is that HTML enables the blending of data and…
Q: Consider the following recursive algorithm. Algorithm Mystery A[0..n-1]) //Input: An array A[0..n-1]…
A: I answerd only a-question and d-question as far my knowledge a) The algorithm computes the value…
Q: Write a program that uses one loop to process the integers from 300 down to 200, inclusive. The…
A: Java programming language : Web apps can be created using the popular programming language Java.…
Q: can you use Raptor program?
A: I attached your answer below.
Q: In this lab the completed program should print the numbers 0 through 10, along with their values…
A: public class NewMultiply { public static void main(String args[]) { String head1…
Q: Question 4 I’m asking you to think how you’ll take ownership of your engineering career, products…
A: The above question is solved in step 2 :-
Q: Convert the following truth table to a Boolean equation: a 0 0 0 b 0 O|0|-|-|O 1 1 10 1 C 0 1 0 1 0…
A: terms where value is 1 a=0,b=0,c=0 term= a=0,b=1,c=1 term= a=1,b=0,c=0 term= a=1,b=1,c=0 term= We…
Q: II. Write single line equivalent code using list comprehension: list1 = [1, 3, 5, 7, 9] length =…
A: Given Code:
Q: Brainstorming is a group process designed to stimulate the discovery of new solutions to problems.…
A: Design teams often employ brainstorming to come up with solutions to properly defined design…
Step by step
Solved in 2 steps

- write java codes to do the following: Write a recursive function to check if an integer array is negative symmetric, for example, an array of 10, 20, 30, 90, -30, -20, -10 is considered as negative symmetric, while an array of 10, 20, 30, 90, 30, 20, 10 is not considered as negative symmetric. public static boolean checkArraySym(int [ ] A, int first, int last) that receives an array A, first index, last index and checks if the array is negative symmetricDevelop the desktop proof of the following recursive exercise with V = [3,5,2,7] and num = 4 (Logically without the use of programs)Write a classifier algorithm for p(Y |X,α)
- What is the running time for this java code? I want the complexity and asymptotic upper bound using Big-Oh notation class lcs { static void LongestCommonArraySubsequence(int X[], int Y[], int n, int m) { // dp[][] array int[][] dp = new int[n + 1][m + 1]; // dp matrix initialization for (int i = 0; i <= n; i++) for (int j = 0; j <= m; j++) dp[i][j] = 0; for (int i = n - 1; i >= 0; i--) { for (int j = m - 1; j >= 0; j--) { if (X[i] == Y[j]) dp[i][j] = dp[i + 1][j + 1] + 1; // bottom up fill } } int max = 0; // maximum length int Xindex = 0; // starting index of array X int Yindex = 0; // starting index of array Y for (int i = 0; i < n; i++) { for (int j = 0; j < m; j++) { // calculating the maximum value in dp matrix if (dp[i][j] > max) {…The three integers n, I and j, with I and j being between 1 and 2n, are the prerequisites to the issue. You have a board of squares that is 2n by 2n squares. Each tile has an adequate amount of pieces and the desired form. With the exception of the solitary square at position I j, you must cover every 2n 2n tile on the board by placing nonoverlapping tiles. Provide a recursive method for this issue where you lay one tile on your own and then enlist the aid of four buddies. a case is a phrase, right?Problem 2: a) (Java language) Write a recursive method int SumMethod(int i, int n) that calculates the following sum: Σ(3+?)??=1. The method takes two integer parameters n and i. b) (Java language) Write the recurrence expression T(n) and find its time complexity.
- Question#1: Let P and Q be integers and suppose F (P, Q) is recursively defined by: F(int P, int Q) if (P == 0) return Q else return F(P- 1, P + Q) Find and Trace F(8,1)Which is the base case of the following recursion function: def mult3(n): if n == 1: return 3 else: return mult3(n-1) + 3 else n == 1 mult3(n) return mult3(n-1) + 3program c++ Given the following recursive definition implement the coresponding program: T(0) = 1,T(1) = 2,T(n) = 3∗T(n−1) + 2∗T(n−2)
- Question 99 Define set S recursively as follows:Base Case: 8∈SRecursion: if a∈S and b∈S then a∗b∈S Prove using structural induction that any element in S can be written as 8^n for some n≥1. Full explain this question and text typing work only thanksGive a recursive definition of the following set of ordered pairs of positive integers: S = {(a, b)| (a is element of positive integer), (b is an integer multiplied by 3)}Write a recursive function in f#, named specialSum, that has the followeing signature: int * int -> int, where sum(m,n) = m + (m +1) + (m+2) + ... + (m + (n-1)) + (m+n) for m >= 0 and n >= 0: (Hint use two clauses with (m,0) and (m,n) A PATTERNS.) start code with let rec specialSum (m,n) match m,n with | m,0 -> | m,n - >

