Question 17: The following figure shows the TCP congestion window size as a function of time. Assume that the TCP implementation supports fast retransmit/ fast recovery. Answer the following questions: A. Identify the intervals of time when TCP slow start is operating. B. Identify the intervals of time when TCP congestion avoidance is operating. C. After the round 16, is segment loss detected by duplicate ACKS or by a timeout? D. After the round 22, is segment loss detected by duplicate ACKS or by a timeout? E. What is the initial threshold for the first transmission round? F. What is the threshold at the 18th transmission round? G. What is the threshold at the 24th transmission round? H. During what transmission round is the 70th segment sent? 45 40 35 30 25 Congestion Window 20
Question 17: The following figure shows the TCP congestion window size as a function of time. Assume that the TCP implementation supports fast retransmit/ fast recovery. Answer the following questions: A. Identify the intervals of time when TCP slow start is operating. B. Identify the intervals of time when TCP congestion avoidance is operating. C. After the round 16, is segment loss detected by duplicate ACKS or by a timeout? D. After the round 22, is segment loss detected by duplicate ACKS or by a timeout? E. What is the initial threshold for the first transmission round? F. What is the threshold at the 18th transmission round? G. What is the threshold at the 24th transmission round? H. During what transmission round is the 70th segment sent? 45 40 35 30 25 Congestion Window 20
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter6: Security Technology: Access Controls, Firewalls, And Vpns
Section: Chapter Questions
Problem 2RQ
Related questions
Question
100%
Answer only part G,H. Other parts are already answered.
Solve it , only if you are good in
Computer science
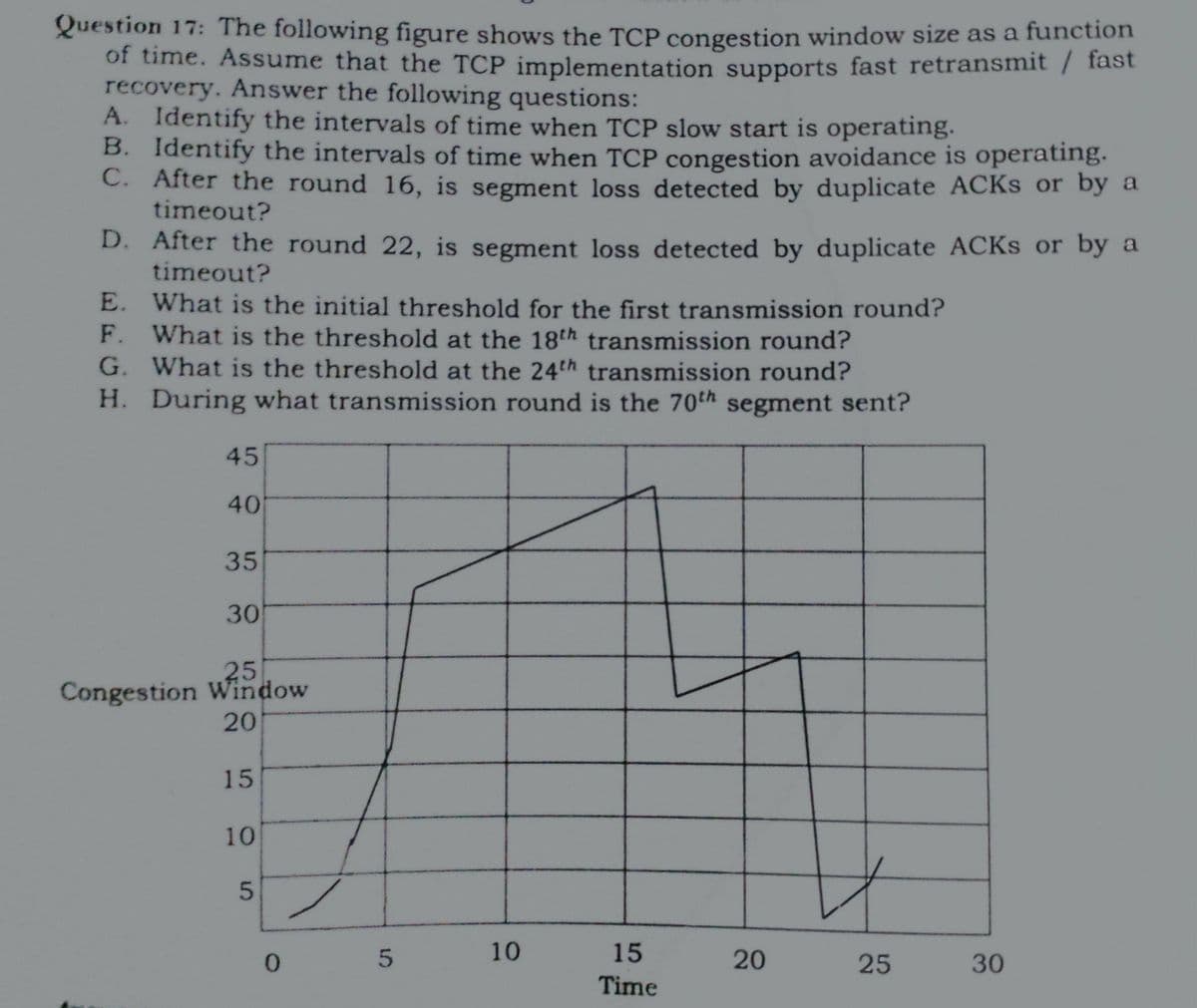
Transcribed Image Text:Question 17: The following figure shows the TCP congestion window size as a function
of time. Assume that the TCP implementation supports fast retransmit / fast
recovery. Answer the following questions:
A. Identify the intervals of time when TCP slow start is operating.
B. Identify the intervals of time when TCP congestion avoidance is operating.
C. After the round 16, is segment loss detected by duplicate ACKS or by a
timeout?
D. After the round 22, is segment loss detected by duplicate ACKS or by a
timeout?
E. What is the initial threshold for the first transmission round?
F. What is the threshold at the 18th transmission round?
G. What is the threshold at the 24th transmission round?
H. During what transmission round is the 70th segment sent?
45
40
35
30
25
Congestion Window
20
15
10
10
15
0.
25
30
Time
20
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning