Question 2: Write a Program to calculate max and min of rain fall over 12 months, with below requirement • Asks the user to enter amount of rain for each month of year ● For each input make sure the value must be between 0 and 100 If the user enters invalid value ask the user to enter again Use a List to save this information Use the List methods to show the minimum and maximum rain amount. ● . . Program should use List and loops to achieve the task.
Question 2: Write a Program to calculate max and min of rain fall over 12 months, with below requirement • Asks the user to enter amount of rain for each month of year ● For each input make sure the value must be between 0 and 100 If the user enters invalid value ask the user to enter again Use a List to save this information Use the List methods to show the minimum and maximum rain amount. ● . . Program should use List and loops to achieve the task.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter17: Linked Lists
Section: Chapter Questions
Problem 8PE
Related questions
Question
100%
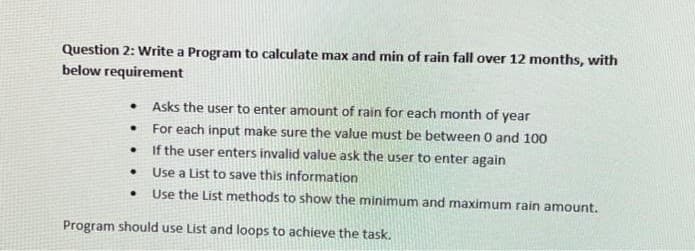
Transcribed Image Text:Question 2: Write a Program to calculate max and min of rain fall over 12 months, with
below requirement
●
.
●
●
.
Asks the user to enter amount of rain for each month of year
For each input make sure the value must be between 0 and 100
If the user enters invalid value ask the user to enter again
Use a List to save this information
Use the List methods to show the minimum and maximum rain amount.
Program should use List and loops to achieve the task.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage