Question 21 If a user visits a web page with an embedded video, leaves without clicking on anything, and the session times out, how will Google Analytics report the session? (A) As an exit B) As a session As an interaction (D) As a bounce Question 22 What report shows which types of mobile devices visited a website? A Site Content > Landing Page report (B) Technology > Network report All traffic > Source/Medium report Mobile > Devices report =
Question 21 If a user visits a web page with an embedded video, leaves without clicking on anything, and the session times out, how will Google Analytics report the session? (A) As an exit B) As a session As an interaction (D) As a bounce Question 22 What report shows which types of mobile devices visited a website? A Site Content > Landing Page report (B) Technology > Network report All traffic > Source/Medium report Mobile > Devices report =
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter8: Cryptography
Section: Chapter Questions
Problem 3E
Related questions
Question
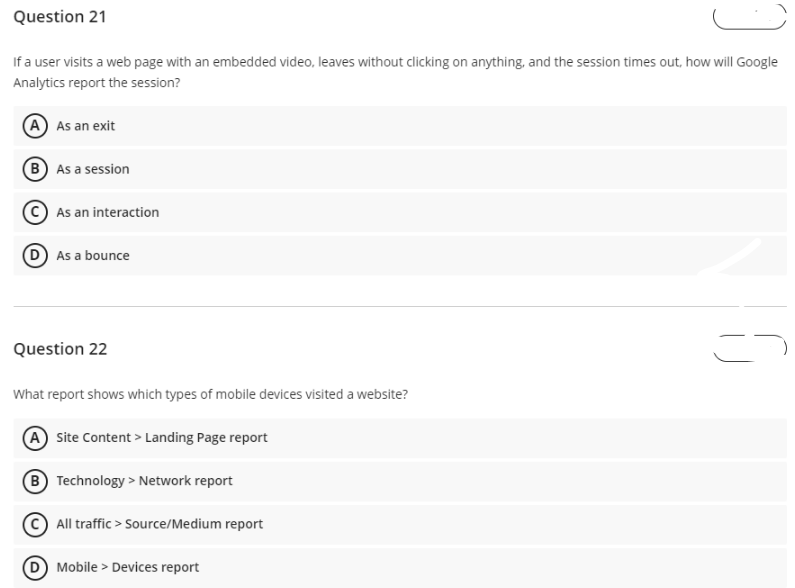
Transcribed Image Text:Question 21
If a user visits a web page with an embedded video, leaves without clicking on anything, and the session times out, how will Google
Analytics report the session?
(A) As an exit
B As a session
As an interaction
D As a bounce
Question 22
What report shows which types of mobile devices visited a website?
A Site Content> Landing Page report
B
Technology > Network report
All traffic > Source/Medium report
D Mobile Devices report
=
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage