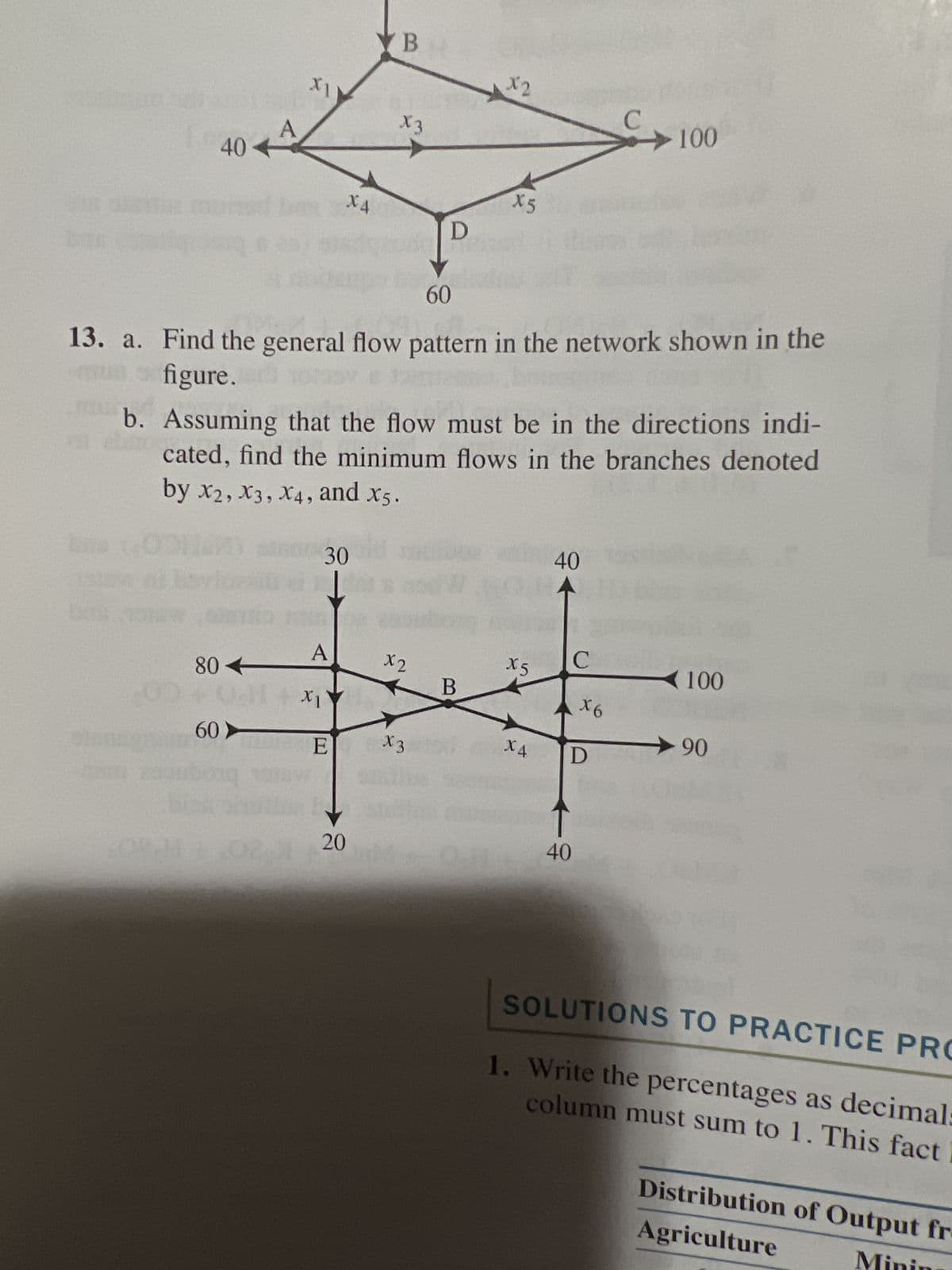
60 13. a. Find the general flow pattern in the network shown in the figure. br bas CHE b. Assuming that the flow must be in the directions indi- cated, find the minimum flows in the branches denoted by X2, X3, X4, and x5. 80- 60 30 A X1 E 20 x2 X3 B X5 X4 40 X6 D 40 100 - 90
Q: Consider a multi-granularity locking system, with lock modes S, X, IS, IX, and SIX as in lecture and…
A: For the scenario described, T3 would need to obtain an IX (Intention Exclusive) lock on file-level…
Q: Construct an NFA that recognizes each of the following languages. c. ? = {? ∈ {?, ?, ?} ∗ | ?…
A: Given language c. ? = {? ∈ {?, ?, ?} ∗ | ? starts and ends with a different symbol} States: q0, q1,…
Q: Design and implement class Patron It should
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------------
Q: Which of the following is NOT a benefit of collaboration networks? Group of answer choices protect…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: Give a quick overview of the compiler and talk about the concept of testability
A: An experiment might be conducted to verify or disprove a hypothesis or idea. The term "testability"…
Q: owing functions i Z= 1 2ny X e-y/2x Z= w = sin(x) In(y) √x
A: Here from the question, we have to write a MATLAB Code for the given problem statement using if-else…
Q: Print out this figure by using only for loops or nested loops in java. Don't use any conditional…
A: Print the given pattern using 'for' loops or nested loops in Java programming language. About the…
Q: WRITE CODE 1) To begin your assignment, find the src/homework/01_data_types folder. In this folder:…
A: Algorithm of the code: 1. Create a function called multiply_numbers that takes an int parameter…
Q: Can you walk me through the steps of executing a SQL query on the command prompt to import a MySql…
A: Use the mysql command to run the mysql command line tool from the Windows command line.
Q: Plaease give me the answer with proper solution Use the bubble sort method to show the first pass…
A: Introduction Bubble sort is a simple sorting algorithm used to sort a list of items. It works by…
Q: Property Number PG4 Property Address Inspection Date Inspection Time 18-Oct-2014 10:00 15-April-2015…
A: Normalization:- Normalization is a process used to organize data in a database. It is the process of…
Q: The most prevalent kind of cybercrime is identity theft. Can your identity be stolen by hackers,…
A: Identity theft is a type of fraud in which an individual's personal information, such as their name,…
Q: Use the Pandas DataFrame describe() method on our forestfire_df to get a statistical summary for…
A: The code snippet is checking the statistical summary of numerical features in a Pandas DataFrame…
Q: If you want your network to function optimally, what are the three things you need? Can you give me…
A: The three things that we need in networking are :- Routers Firewall Switches
Q: Defining the firewall's role in maintaining the security of the network is a prerequisite to moving…
A: Introduction: A firewall is a type of security system that keeps track of and regulates both…
Q: What are the best six reasons to educate yourself about compilers?
A: Compilers are specialised software tools that convert the source code of one programming language…
Q: Convert a binary search tree into a min-heap. Demonstrate the method on the following binary search…
A: A Min Heap is a special type of binary heap data structure where each parent node is smaller than or…
Q: In the context of creating and maintaining software, how do cohesion and coupling relate to one…
A: Cohesion is the degree to which all methods and data structures in a class or module are…
Q: A description of the firewall's role in maintaining the security of a network is required. Don't…
A: security:- Security is a concept that encompasses the processes, technologies, and controls that are…
Q: The benefits of a binary search tree are evident when compared to other data structures like a…
A: Given: Think about the following operations: You may access every component. Assume that the binary…
Q: Throughout the process of planning and executing a training session, it is important to assess the…
A: Introduction: It is the kind of ability we use to communicate in daily life, such as speaking,…
Q: Contrast the dangers and attacks that may be encountered in the realm of information security. Give…
A: Information security refers to the protection of sensitive and confidential information from…
Q: PROBLEMS: 1. Perform a logical AND using the following two binary numbers: 10111011 AND 11100111.…
A: Introduction Binary number: A binary number is a number representation system based on the use of…
Q: Examine the difficulties of information systems by use of technological and data analysis tools.
A: Introduction: System of Information Introduction: Information systems are those that gather,…
Q: i. For a second benchmark, libquantum, assume an execution time of 960 ns, CPI of 1.61, and clock…
A: CPU time: It is also called process time. It is the time taken by the CPU for processing the…
Q: Managers need to know what they're shooting for if they want to build stronger relationships with…
A: The followings are some comparable CRM objectives: Improving customer satisfaction: One of the…
Q: What is the most important thing to keep in mind when making an operating system's microkernel? What…
A: Introduction : An operating system (OS) is a piece of software that stands between a computer's user…
Q: shows the UserManagement class that contains the main method of program. It creates and adds several…
A: Individual User objects are saved in a HashMap object in the Users class, with a user id (string) as…
Q: More work is needed to clarify the connection between object-oriented programming and design…
A: Please refer to the following step for the complete solution to the problem above.
Q: Enter your weekly caloric budget ==> 21000 Enter calories for a meal (as an integer or 0 to quit)…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: 1 [Start, T1] 2 [Start, T2] 3 [T1, Bounce, 500, 1000] 4 [T2, Salary, 4000,4400] 5 [Checkpoint,…
A: - We have to work on the transactional data amd provide the values of salary, tax, MangN. Also, we…
Q: Prepare an appropriate flowchart for this Arduino Uno code: Pls do fast its urgent.. give solution…
A: Here is a flowchart representation of the given Arduino Uno code:
Q: Where does access security software fit in?
A: The intention is to provide users access to just the information that has been determined to be…
Q: We are using Amdahl’s Law and Gustafson’s Law to calculate overall speedup and scaled speedup. Given…
A: Amdahl's Law states that the maximum possible improvement to the overall performance of a system is…
Q: How can you help an employee who isn't putting up their best effort?
A: Improve their ability to see well. In order to provide assistance in the accomplishment of their…
Q: Compare and contrast the performance of Binary Search Trees and AVL Trees. Is it really feasible to…
A: The binary search tree is a binary tree in which the left child has a lower value than the parent,…
Q: A clear definition of "security service" would be much appreciated.
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Is a precise definition of Object Oriented required? The Practice of Developing Object-Oriented…
A: The supplied details are How would you define and explain what Object-Orientation is in detail? The…
Q: Please explain the benefits of data profiling.
A: Data profiling enhances user comprehension of data, boosts data quality, and speeds up the…
Q: Explain what you mean by "application security."
A: Introduction of Security: Security in terms of computers is the protection of data from unauthorized…
Q: What problems may arise from using a set of data systems that aren't cohesive with one another?
A: Cohesive data sets have a uniform structure and format, and they integrate well with one another.…
Q: Wema kkrmoa.
A: I have written the code below: Algorithm: Read the string from the user Use for loop to find the…
Q: Basis for Comparison Memory/Cache Number of cores Clocking frequency (GHz) Size (length & width in…
A: Here is a comparison of the AMD Ryzen 9 5950X CPU and the NVIDIA GeForce RTX 3080 GPU:
Q: a. (n²+1) 10 b. √10n²+7+3 c. 2n Ig(n + 2)² + (n + 2)² lg d. 2+¹+34-1 e. [log₂ n]
A: limn→∞f(n)g(n)=x Case 1: x is constant f(n)=θ(g(n)) Case 2: x is ∞ f(n)=ω(g(n)) Case 3: x is 0…
Q: Explain what you mean by "information security."
A: Security: Security is the state of being protected or safe from harm or threats. It is a process…
Q: Specify why firewalls are so crucial to preserving the safety of online communities and internal…
A: Introduction Firewall: A firewall is a type of security device used to stop unauthorised users from…
Q: 3. Suppose that we want to know which agents are connected by a walk of length two in a given…
A: Please refer to the following step for the complete solution to the problem above.
Q: What is the concentration of A after 43.1 minutes for the reaction A → Products when the initial…
A: Here is the formula for the concentration of A after t minutes: [A] = [A]0 * e^(-kt) where: [A] is…
Q: Determine a number of different back-end compiler designs, then evaluate and compare them.
A: Answer: There are several back-end compiler designs: Register Transfer Language (RTL) design: This…
Q: You are asked to predict weather temperature. You only know the linear regression model and luckily…
A: import numpy as np import pandas as pd import random from sklearn.model_selection import…
13
Step by step
Solved in 3 steps with 3 images

- Consider the function g(x)=2x^(2)+12x+16 What i(s)/(a)re the x-intercept (s) of g(x) ? Select all that apply.Computer Science Hand-execute the Ford-Fulkerson algorithm on the transport network. Find the maximum flow through the network. Identify the cut whose capacity equals the maximum flow. Your answer should include all the details of the execution clearly.IN PYTHON Given the following six-node wide area network for which the numbers attached to the links are a measure of the “delay” in using that link (e.g., some lines could be more heavily used than others and therefore have a longer wait time), answer the following question. What is the shortest path from node A to node D, where shortest path is defined as the path with the smallest sum of the delays on each individual link? Explain exactly how you went about finding that path.
- In this link: https://edaplayground.com/ , Provide VHDL codes using Dataflow Modeling with the given problem below. PROBLEM: In a simple copy machine, a stop signal, S, is to be generated to stop the machine operation and energize an indicator light whenever either of the following conditions exists: (A) there is no paper in the paper feeder tray; (B) the two microswitches in the paper path are activated, indicating a jam in the paper path. The presence of paper in the feeder tray is indicated by a HIGH at logic signal P. Each of the microswitches produces a logic signal (Q and R) that goes HIGH whenever paper is passing over the switch to activate it.Delivery person wants to deliver the courier from senders location to receivers location. There exists a path from area1 to area2 but there is no direct route between area1 and area5. This routes are bidirectional. To reach area5, delivery person can take any route like 1-2-4-5 or 1-2-3-4-5. Please provide python code to find all possible routes in between area1 and area5 in the graph using the given matrix. I have a doubt in this question of finding all routes in this graph from 1 to 5 i.e 1-2-3-4-5 and 1-2-4-5. I tried solving it but getting an Index Error in my python code. Please provide python code of finding all routes from 1 to 5 in the given graph using this matrix.Compute the output of the above toy Feistel network on input “12a” (in hex).Write of the steps of your computation, i.e., input and output of each function [Toy example of the inverse Feistel network] Compute an inverse of the above network to verify your result. Write of the steps of your computation, i.e., input and output of each function.
- The network in figure below gives the distances in miles between pairs of cities 1, 2, …, and 8. Use Dijkstra’s algorithm to find the shortest route between the following cities: a.) Cities 1 and 8 b.) Cities 4 and 8 c.) Cities 2 and 6As we learned in the lecture, computer software uses decimal degrees (DD), as they are much easier to handle in complex algorithms for various mapping applications. Your task is to convert Lat-Long from DMS to DD and vice versa. Remember: when using DD, the cardinal direction are replaced by positive and negative numbers . The "+" sign is omitted (it is implied) and only the minus sign "--" is mandatory . (See lecture) Washington Monument in DC has the following coordinates, in DMS: LAT: 38 deg 53 min 22 sec North ; LONG: 77 deg 02 min 19 sec West. Use an online converter (such as https://www.latlong.net/degrees-minutes-seconds-to-decimal-degreesLinks to an external site.) and find the coordinates in decimal degrees. Choose the correct coordinates in DD for the Washington Monument: 38.88944444 , 77.03861111 38.88944444 , --77.03861111 --38.88944444 , 77.03861111 --38.88944444 , --77.03861111c) Distinguish between Distance vector routing and Link State routing. Givean example each of their implementation in real-world systems.
- Computer Science The subject is teletraffic theory. The traffic load of 2 erl is offered to M/M/2. Calculate the mean A and the variance V of overflow calls.Based on the given data: a) Determine the total number of paths in the precedence network b) Which of the following is NOT one of the paths? Explain ABC GHI BGI GEF c) What is the duration of the CRITIAL PATH(s)? d) What is the duration of the SHORTEST PATH?Explain how the maximum-flow problem for a network with several sources and sinks can be transformed into the same problem for a network with a single source and a single sink.

