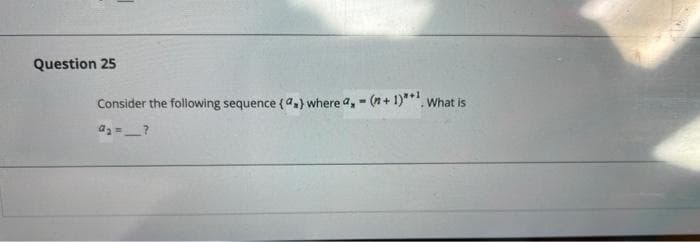
Question 25 Consider the following sequence (a,) where a,- (n+ 1)**', What is
Q: Find context-free grammars for the following languages (with n > 0, m 2 0, k 2 0). (a) L = {w €{a,b)...
A: Below is the answer to above question. I hope this will meet your requirement...
Q: What do you think is the most difficult component of the autolayout system to implement?
A: According to the information given:- We have to define the most difficult component of the autolayou...
Q: In the knight’s tour problem, we are looking for a path of knight’s moves from a square of the n×n c...
A: A chess board which is the size of n x n, the initial position of knight and final position of knigh...
Q: When creating a database, are there any ethical considerations to keep in mind? Whether sensitive pe...
A: Introduction: The database management system (DBMS) organises and maintains incoming data, as well a...
Q: Write Programm using oop in c++ Some form of simplified physics simulation, e.g. multiple interactio...
A: Some form of simplified physics simulation.multiple interactions in an ideal gas.
Q: What are the advantages of employing an Open and/or Save As dialogue box in a file-related applicati...
A: Introduction: Open Dialogue box: In this dialog box, you can specify what kind of file you want to o...
Q: Create a context-s e nsit
A: Given: L=0^2^i
Q: Which command is used to list the contents of the current working directory including the hidden fil...
A: Hidden File in Linux: The easiest way to show hidden files on Linux is to use the ls command with t...
Q: Q3. Write a C program that displays the menu shown in the example run, to the user, with the operati...
A: C-programming is a general-purpose,procedural,imperative computer programming language.
Q: BINARY SEARCH: PYTHON CODE #Binary Search Algorithm def BinarySearch(sampleList, value): low = 1 hig...
A: find the error in code and write correct code in Binary Search using python
Q: How does a compiler deal with an inline member function of a class?
A: Introduction: When you write code in one programming language (the source language), you can use com...
Q: A computer is a piece of technology that consists of numerous components and does not require any en...
A: Introduction: Computer: One of the primary functions of the modern-day computer is data storage and ...
Q: convert dhe given binany numben into decimal number System. humker : (110-011 = (? ), humber %3D
A:
Q: Q1: Givenx=[315912-10-12 9 6 1], provide the command(s) that will set values that are multiples of 3...
A: The following step provides the MATLAB command to set values that are multiples of 3 to zero
Q: Calculate the results (both binary and hexadecimal values) with calculation step and show the status...
A:
Q: What are the advantages of platform-independent operating systems?
A: INTRODUCTION: Here we need to tell the advantages of platform-independent operating systems.
Q: In a few words, describe two significant technological breakthroughs in computer history?
A: The Answer for the given question in step-2.
Q: Do in C Program In the military, they have these military dogs that help them in their missions. To ...
A: First let's understand what is enum in c programming . When we have to create some integer in c how ...
Q: Your output looks correct apart from the whitespace. DIFF SPLIT DIFF YOUR OUTPUT EXPECTED Welcome to...
A: Here I have printed the menu to the console. Next, I have taken input from the user and then stored ...
Q: Carry out the given computation Y = (UN) + (W * (X-Z)) using (i) One Operand Instruction (ii) Two Op...
A: We need to carry out given computation using given types of instructions.
Q: Consider the time displayed on a digital clock( 07:30:00) with 3 main components hours, minutes and ...
A: public class q3() { private int hour; private int minute; private i...
Q: Urite a java program to take three ints, a b c, print true if b is greater than a, and c is greater ...
A: We are going to write a java code which will ask user to enter 3 integers a,b,c and then print "True...
Q: Use the optimized division hardware to perform 1100100100. In the input box below , show the bit val...
A: The Answer in step-2.
Q: How do you tell the difference between Agile and XP as system development methodologies?
A: Introduction: Even while Agile approaches are based on well-defined procedures (such as change manag...
Q: e a session with a host at 208.85.40.44:443. For this session, what protocol is being used?
A: HTTP HyperText Transfer Protocol (HTTP) is an acronym that stands for HyperText Transfer Protocol.I...
Q: How were usability and user experience objectives broken down in the evaluation?
A: Please find the detailed answer and explanation in the following steps.
Q: Which of the following statements is(are) true? (Check all that apply.) A. Hashing is reversible, bu...
A: Cryptography, which comes in a variety of forms, is one of the most essential parts of cyber securit...
Q: Do object-oriented programming and abstract data types go hand in hand, or should they be seen as tw...
A: Introduction: Object-Oriented Programming (OOP) is a programming language that is centred on objects...
Q: Discuss about the different types of parsers ad different terms involved in the grammar symbols.
A: The second phase of a compiler is parsing or syntax analysis. The program that breaks the data extra...
Q: Explain how a cloud storage program differs from typical client storage software in terms of pros an...
A: I am a proponent of the ease and value that cloud technology provides, since I now use Google Drive ...
Q: conditional structures Create a program that will ask three (3) numbers from the user then display ...
A: C++ program to print largest among the tree number
Q: When a program uses a file, what three steps must it take?
A: There are three ways to create programs that write data to files and read data to files. If a file i...
Q: Computer Science ** Unique answer** ** hand answer or photo not accept ** There are four types ...
A: The Four Primary Types of Network Threats In an attempt to categorize threats both to understand the...
Q: True or False? An action query is accomplished by putting AS and an alternative name after the table...
A: We are given a statement in sql query and we are going to see if the statement is correct or not.
Q: What is the output of the following code: class Car{ public double speed; public String model; publi...
A: Introduction What is the output of the following code:class Car{public double speed;public String mo...
Q: Create a loop that will print all of the even numbers between 3 and 10001 inclusive, one per line.
A: Start for i=4:1001:2 do print i value on console endfor Stop
Q: What is polymorphism, and how does it affect you? How can operator overloading help with polymorphis...
A: Introduction: Polymorphism: The word polymorphism means having many forms. In simple words, we can d...
Q: What kind of situation necessitates the use of a subquery?
A: A subquery is used to return data that will be used in the main query as a condition to further rest...
Q: Write a C++ program to check whether an alphabet is a vowel or consonant. using switch statement
A: - We need to check if an inputed character is vowel or a consonant.
Q: 4. Exercise. Q1. Consider transferring a file of 5000 bytes from Host A to Host B. Assume an MSS of ...
A: The solution to the given question is:
Q: Automatic employee scheduling system
A: Automated scheduling is a way of using artificial intelligence to create an optimal schedule for you...
Q: explain with iamge and outputs that how we can use every thing in wireshark
A: Wireshark is the world's preeminent and generally utilized network convention analyzer. It allows yo...
Q: Assume you are going to make an online shop database. Draw the database ER diagram with correct rela...
A:
Q: Create a JAVA program that reads input a string from the user and prints the Unicode values of all t...
A: Required:- Create a Java program that reads input a string from the user and prints the Unicode valu...
Q: How were usability and user experience objectives broken down in the evaluation?
A: Please find the detailed answer and explanation in the following steps.
Q: When developing a multimedia streaming network application for a client-server communication paradig...
A: Introduction: Streaming is a technique that enables the transport of multimedia data between clients...
Q: Computer Science We know that JavaScript objects can be stored as redis hashes. We can use a JavaScr...
A: Redis is best suited to situations that require data to be retrieved and delivered to the client as ...
Q: Write a program using for-loop to display consecutive numbers exactly as follows. using python ...
A: Start Accept the integer Loop runs for all consecutive numbers If the number is last number in the s...
Q: What speeds for data transmission can be achieved using a particular type of cable?
A: The answer is given below.
Step by step
Solved in 2 steps with 1 images

- NEED CODE OF BANKERS ALGORITHM IN C LANGUAGE (i need code not algorithm so please be sure before you submitting any answer)WHICH CAN PRINT ALL SAFE SEQUENCES IF WE ASK P1 FOR (1, 0, 2) Need asap!!!!Determine whether the following is true or false. Please cite the brief explanation so that I can know why is it true or false. A) 1 ∈ {{1},{2},{3}} B) A\B = A ∩ B^c C) The contrapositive of p -> (p V ¬p) = (¬p∧ q) -> ¬pQuestion 2: Ʃ = {a, b} Give the regular expression for all strings in which any b’s that occur are in groups of an odd number at a time. Some sample strings in the language aabaabbbab, bbbbbabbbaab, aaaa, ababab Some sample strings NOT in the language abba, babbbb
- Find dfa’s that accept the following languages: (a) L (aa∗ + aba∗b∗). (b) L (ab (a + ab)∗ (a + aa)).An arithmetic sequence a starts 84,77,... Define a recursively Define a for the n th termFor the infix expression given below, obtain (i) the equivalent postfix expression,(ii) the equivalent prefix expression and (iii) evaluate the equivalent postfixexpression obtained in (i) using the Algorithm EVAL_POSTFIX(), with A = 1, B = 10, C = 1, D = 2, G = –1 and H = 6. (−(? + ? + ?) ↑ ?) ∗ (? + ?)
- Question 44 ddd Computer Science Prove that log(n!) = Θ(n log n). (Logarithms are based 2)3. Please Help me to solve the following all the subparts perfectly on word: PS: You just need to show the prove or disprove (for a) and show the prove or show if it is true (for b).Describe the following in CFG: S --> sS | bC C --> cC | eGenerate a bunch of example, you will see that they are: Any number of a's followed, optionally followed one b and any number of c'sHence the answer is a*|a*bc* Calculation of power using recursion: 52^847 = 52 * 52^846

