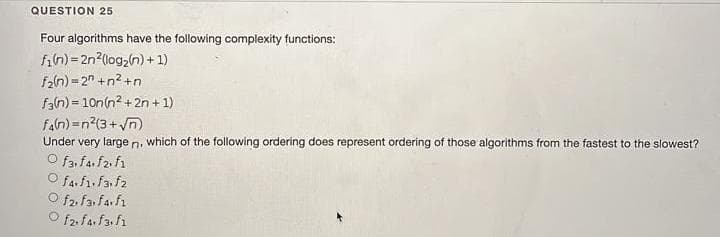
QUESTION 25 Four algorithms have the following complexity functions: fin)=2n2(log,(n) + 1) fan) = 2" +n? +n fan) = 10n(n? + 2n + 1) faln) =n?(3+ yn) Under very large n. which of the following ordering does represent ordering of those algorithms from the fastest to the slowest? O f3,fa.f2. f1 fa.f.fa f2 O f2. fa: fa fı O f2. fa. fafi
Q: What are the advantages of using programming approaches that run asynchronously? What are some of…
A: Given: Asynchronous a programming is a method of parallel programming in which little portions of…
Q: What does the term context switch mean? Preemption?
A: Your answer is given below. Introduction :- Context Switch : When the OS code (running proactively)…
Q: Examine the roles that each member of the team plays in the agile methodologies of Scrum and Extreme…
A: The Answer is in step2
Q: Problem: A Hamiltonian cycle, also called a Hamiltonian circuit, Hamilton cycle, or Hamilton…
A:
Q: It has been asked, "What is the point of architecture?" Consider a project and map it both in terms…
A: As is common knowledge, software architecture is the mapping between strategic requirements and…
Q: Create a script file with displaying the result after running the following codes:
A: Given:
Q: The great majority of today's appliances are wirelessly connected thanks to technological…
A: Yes it does affect Better communication Enhanced communication is one of the most significant…
Q: Im really interested in learning the names of the three basic frequency bands that are used in…
A: The names of three basic frequency bands utilised in wireless communication systems are discussed…
Q: Describe a few different methods that may be used to hijack a session. How would one defend…
A: Attackers may hijack a user's session based on their location and vector. This is how a session may…
Q: Increased adaptability is a significant benefit of multiprocessor systems. This benefit, however,…
A: Two-dimensional materials are flexible, allowing them to be readily integrated into wearable devices…
Q: Create an ERD for the given scenarios. Thank youu!! The loan office in a bank receives from various…
A:
Q: What are the benefits of using a computer that has logical divisions as well as subsystems?
A: You may spread resources inside a single system using logical partitions to make it work as if it…
Q: Regarding the incident handling procedure, this activity is done: "check that the antivirus…
A: Antivirus are tools that are made to protect a system from various kinds of fraudulent attacks.
Q: What function does MVC play in the building of web applications in the big scheme of things? What…
A: Introduction: What function does MVC play in the building of web applications in the big scheme of…
Q: Fibonacci principle states that: If we let Xn be the nth integer of the sequence, then the next…
A:
Q: Q8/ To draw a sawtooth signal as shown in figure below, a MATLAB code -- is used:
A: Given:
Q: In what circumstances is dynamic scoping useful, and how may it be enhanced?
A: Dynamic scoping, Dynamic refers to anything that is constantly changing.Dynamic scoping is a…
Q: If a host on a network has the address 172.16.45.14/30, what is the subnetwork this host belongs to?
A: In the question A network address 172.16.45.14/30 is given and we have to calculate the subnetwork…
Q: (Digital Electronics-CLC) Give two to three types of 7-segment displays and differentiate them…
A: INTRODUCTION: The 7-segment display, often known as a "seven-segment display," is made up of seven…
Q: The distribution of keys was the first challenge that public key cryptography had to contend with.…
A: Public key cryptography: It is a type of encryption that involves two distinct keys, one of which…
Q: In the context of computer security, how exactly does ransomware function?
A: answer is
Q: Consider a virtual memory system providing 32 pages for each user program; the size of each page is…
A:
Q: Consider how important wireless networks are in poor nations. Why are some businesses abandoning…
A: Introduction: Question-wise WiFi networks provide greater commercial advantages than wireless…
Q: Write a PYTHON program that will repeatedly display your name according to the user input value.…
A: Answer:
Q: Wireless networks are quicker than wired networks in terms of throughput speed, but they are slower…
A: Start: Wired networks are faster than wireless networks.Wired connections transmit more data than…
Q: t is very difficult to create a mobile network that does not make use of wireless technology at any…
A: According to the information given:- We have to define a mobile network that does not make use of…
Q: The purpose and nature of telecommunications network protocols are described.
A: Protocols for telecommunications networks A network protocol for telecommunications is a collection…
Q: Describe the difference between integration and interoperability and show instances of both
A: Integration is the act of linking different types of applications to one another in such a way that…
Q: What are your thoughts on DMP, and how will these gadgets help or hinder mobile device…
A: What are your thoughts on DMP, and will these gadgets help or hinder investigations into mobile…
Q: Consider how important wireless networks are in poor nations. Why are some businesses abandoning…
A: Answer:
Q: When redistributing a route into EIGRP, what is the necessary parameter? Administrative distance is…
A: EIGRP EIGRP stands for Enhanced Interior Gateway Routing Protocol. It is a network layer protocol…
Q: Where does the Model-View-Controller pattern fit into the greater framework of web applications?…
A: Given: Where does the Model-View-Controller pattern fit into the greater framework of web…
Q: Q. A router has the following IP address on Ethernet0: 172.16.2.1/23. What can be valid host IDs on…
A: INTRODUCTION: The internet protocol address (IP address) is a unique number that is connected with…
Q: Suppose a bank's database is safeguarded using a snapshot isolation database technology. Do you…
A: Banks safeguard their data: Banks must first reevaluate their existing back-office and front-office…
Q: What are the benefits of using a WYSWYG editor, as well as any potential drawbacks?
A: A WYSIWYG editor is a kind of content editor. Edit the information, whether it's text or visuals,…
Q: When it comes to the design of the infrastructure for a data warehouse, why is it so vital to ensure…
A: Given: When it comes to the design of the infrastructure for a data warehouse, why is it so vital…
Q: Q.2.1 Classify each of the two software packages as either application or systems software. (a)…
A: NOTE: Student asked only either or option in first question. So I answered as per student needed…
Q: What exactly is meant by the term "virtualization" in reference to cloud computing?
A: The solution for the above given question is given below:
Q: Why is multithreading more common than a multitude of background processes? Explain
A: Introduction: Multitasking means at a time more tasks are run in the CPU by shared the processor.…
Q: Because microprocessors' central processing units (CPUs) cannot understand mnemonics in their native…
A: Machine code, in other terms, is binary code that represents the machine's native machine…
Q: Provide a concise summary of the many advantages afforded by the connection of various worksheets…
A: Given: List the advantages of connecting numerous worksheets inside a workbook. Please be specific.
Q: What exactly is meant by the term "virtualization" in reference to cloud computing?
A: Given: Cloud computing uses virtualization. This programme isolates computing environments from…
Q: ting systems that are n
A: An operating system (OS) is a kind of system software that is utilized to oversee PC hardware and…
Q: Explain how a backup produced with double parity in RAID systems works and how much of the original…
A: Introduction: By establishing two sets of parity data on an array of hard discs, double parity RAID,…
Q: Why is it necessary to rearrange the database structures?
A: Introduction: Database: It is a logically organized collection of data stored on a computer and…
Q: Compilers have a tough time implementing either the VLW or the superscalar architecture. Which…
A: The acronym "VLIW" stands for "Very Long Instruction Word." It is a kind of instruction set…
Q: Consequently, what does "cooperative" multithreading entail in the context of a multithreading…
A: Answer: Cooperative Multi Threading is a kind of computer multi threading in which one process is…
Q: Consider how important wireless networks are in poor nations. Why are some businesses abandoning…
A: Wireless Networks: According to the question, WiFi networks provide greater commercial advantages…
Q: S → Aa А > bdB | eB B → cA | dB |E
A: Given grammar is: S->Aa A->bdB | eB B->cA | dB | ε Variables in the grammar are {S, A, B}…
Q: euse patterns. Why not
A: Patterns of frequency reuse: Frequency reuse alludes to allocating and reusing channels across an…
Step by step
Solved in 2 steps with 2 images

- A computer science student designed two candidate algorithms for a problem while working on his part-time job The time complexity of these two algorithms are ?1(?) = 3 ? log ? and ?2(?) = ? 6/5a) Which algorithm is better? Why?b) If we run both algorithms at the same time with an input size of 105 which algorithm produces results faster than the other one? Why?Consider the following non-recursive algorithm:Algorithm Euclid2(m, n)//Input: Integers m and n where m >=n//Output: Greatest Common Divisor of m and nwhile n ≠ 0 do r ← m mod n m← n n ← r return ma) What does this algorithm compute?b) What is the input size for this algorithm?c) What is the basic operation of this algorithm?d) How many times the basic operation is executed worst case scenario?e) How many times the basic operation is executed in best-case scenario?Consider the following non-recursive algorithm: Algorithm Euclid2(m, n)//Input: Integers m and n where m >=n//Output: Greatest Common Divisor of m and nwhile n ≠ 0 do r ← m mod n m← n n ← r return m a) What does this algorithm compute?b) What is the input size for this algorithm?c) What is the basic operation of this algorithm?d) How many times the basic operation is executed worst case scenario?e) How many times the basic operation is executed in best-case scenario?
- Consider the following algorithm and answer the following questions. procedure Algo1(a1, a2, . . . , an: integers) k := 0 for i := 1 to n if ai is even then k := i return k{k is the desired location(or 0 if there are no evens)} What does the given algorithm compute??? Execute the given algorithm and complete the following table by using the list 3, 5, 8, 10, 5, 2, 1, 7, 3, 13. i ai k 1 3 2 5 3 8 4 10 5 5 6 2 7 1 8 7 9 3 10 13What is the leading term for the following expressions and specify the lowest Big O Complexity for each algorithm?Write an efficient algorithm for the following problem, and describe your reasoning. Determine the Time complexity and if you cannot find any polynomial time algorithm, then give a backtracking algorithm. Problem: Tower of Hanoi with Every Tower having some Disks Input: Each of the three towers contains roughly n/3 disks. Tower A contains floor(n/3) largest disks. Tower C contains ceiling(n/3) smallest disks. Tower B contains the remaining disks. The disks at each tower are already sorted according to the typical Tower of Hanoi rule. Output: A set of moves that transfers all the n disks to C maintaining the Tower of Hanoi rule that after each move, the smaller disks at a tower will always be above the larger ones.
- You will analyze three algorithms to solve the maximum contiguous subsequence sum problem, and then evaluate the performance of instructor-supplied implementations of those three algorithms. You will compare your theoretical results to your actual results in a written report. What is the maximum contiguous subsequence sum problem? Given a sequence of integers A1, A2, ..., An (where the integers may be positive or negative), find a subsequence Aj, ... , Ak that has the maximum value of all possible subsequences. The maximum contiguous subsequence sum is defined to be zero if all of the integers in the sequence are negative. Consider the sequence shown below. A1: -2 A2: 11 A3: -4 A4: 13 A5: -5 A6: 2 The maximum contiguous subsequence sum is 20, representing the contiguous subsequence in positions 2, 3, and 4 (i.e. 11 + (-4) + 13 = 20). The sum of the values in all other contiguous subsequences is less than or equal to 20. Consider a second sequence, shown below. A1: 1…Select the asymptotic worst-case time complexity of the following algorithm:AlgorithmInput: a1, a2, ..., an, a sequence of numbersn, the length of the sequencex, a numberOutput: ??For i = 1 to n-1For j = i+1 to nFor k = 1 to nIf ((ai)^2 + (aj)^2 = (ak)^2) Return( "True" )End-forEnd-forEnd-forReturn( "False" )a. ?(1)b. ?(?)c. ?(?2)d. ?(?3)Solve This D&AOA Question. Analyze your algorithm and find its complexity class.
- Please provide at least one example of an algorithm for each of the following complexity classes: log2n, n, n log2n, n2, n3, 2n, n!, Undecidable..Q10. Consider the following algorithm: g1 = 7 g2 = 6 For k starting at 3 and ending with 8: gk = (k-1)·gk-1 + gk-2 What is the last term, g8, of the recursive sequence generated as a result of executing this algorithm?(a) What “better-known”/simpler complexity class is equivalent to O(N log N2); briefly explain why. (b) Explain under what conditions sorted(set(l)) runs faster than set(sorted(l)) for a list l (they both produce the same answer); state the worst-case complexity class of each.

