Question 3 Design a circuit to light red if the number of ones in input (5 bit) is odd & light blue if the zeros of the number is larger than the ones , and light yellow if the number is greater than 5 and less than 17
Q: Describe the many methods used by law enforcement authorities to investigate computer crimes and…
A: Law Enforcement: Computer technology enables law enforcement agencies to store and access large…
Q: 21. In the following code (number added), which will be the last line executés successi (1) astr -…
A: Correct Answer is a 1. After this second line will throw an error. Let us understand why
Q: he time of Executing a program have one instruction in 4 stage pipelining is equal to ----- of the…
A: Answer to the given question: The time of Executing a program have one instruction in 4 stage…
Q: What is the purpose of forensic software in investigations, and how does it provide specific…
A: Answer:
Q: What distinguishes a hacktivist from a cyberterrorist in your opinion? Is using hacktivists against…
A: Let's take a closer look at the solution. Hacktivism is the peaceful use of unlawful or legally…
Q: ways in which cybercrime is committed and the results To avoid cybercrime, devise a plan of action
A: Introduction: A computer programming language is a language that is used to show a certain set of…
Q: Describes the key component of OOP with examples.
A: let us see the answer:- Introduction:- In object-oriented programming, a group of data properties is…
Q: Sort DNS records based on the type. The rationales and examples for each should be provided. Is it…
A: Explanation: DNS servers preserve records. When a device submits a DNS query, DNS servers and…
Q: Write a program to find the sum for the following series: اكتب برنامج لايجاد المتسلسله التاليه :…
A: - We need to code for the sequence shown here. - We are using C++ here.
Q: Where does traffic analysis and traffic alert fit into firewall security?
A: A Firewall is a network security device that monitors and filters incoming and outgoing network…
Q: What role does intrusion detection and prevention play in network security and defense?
A: To mange the robust and resilient security feature by a user Intrusion detection systems are used.
Q: Write a C++ program to print the text "C++ Programming." in the output along with the quotes.…
A: Coded using C++.
Q: What does a virtual machine (VM) stand for? What is the benefit of using a virtual machine? What are…
A: A virtual machine (VM) provides a distinct environment for executing its OS and applications…
Q: Identity theft is a widespread kind of cybercrime. Tell us about the ways in which hackers might…
A: Introduction In today's digital environment, cybercrime is one of the most common crimes. Solution:…
Q: (3) Start with a 4 by 4 matrix A whose entries are integers in the range from 1 to 10 (output A).…
A:
Q: onsider the NFA shown in Figure 2.b and convert it to a DFA. Ensure you your working out…
A: To make DFA from NFA we use a method called as Subset construction method. When a Finite Automata…
Q: MCQS OF SOFTWARE QUALITY ASSURANCE 1.Testing the application as a whole for the modification in any…
A: Note: Since the question is multipart we are advised to do only first three parts. Kindly post other…
Q: If a "WORM" assault is used against a content delivery network, what are the ramifications? What can…
A: Define: A computers a piece of code that may propagate from one framework to another. An infection…
Q: Is it possible to explain low-level programming languages?
A: Low level programming language is close to computer hardware which directly interacts with hardware…
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Your answer is given below. Introduction :- A local area network (LAN) in computing is a…
Q: 1. The command stem(x,y) is used in matlab to obtain the graph in continues time. True False
A: A graph is pictorial representation of data that is used for data analysis. Graph can be discrete or…
Q: a.
A: Given:
Q: Put another way, what does wavelength division multiplexing do?
A: Wavelength division multiplexing (WDM): Wavelength division multiplexing (WDM) is a technique for…
Q: What can a corporation do to avoid being hacked or infected?
A: Solution: In order to obtain sensitive information about your corporation while also protecting your…
Q: The goal of forensic software is to give particular investigation skills, but how exactly does it…
A: Explanation: Forensic software can automate numerous review operations, in addition to taking disc…
Q: Exactly what do you mean by "network security," and how do you define it? What evidence do you have…
A: Start: Defining network securityThe word "network security" refers to a wide range of technology,…
Q: Name the three most important functions that information systems may play for a corporation,…
A: Name the three most important functions that information systems may play for acorporation,…
Q: When it comes to transferability, how may the blockchain work?
A: A blockchain collects information together in groups is known as blocks that hold sets of…
Q: -Problem -2 When you execute your program it should ask user to input any number then check if the…
A: Note: Programming language is not mentioned, so writing code in C++ In this question, we are asked…
Q: What is the purpose of authentication? Is it possible to compare and contrast the advantages and…
A: Start: Authentication is the process of identifying users who want to access a system, network, or…
Q: Changes to information systems are the focus of digital forensics, which seeks to record such…
A: Information systems: It is referred to as "digital forensics" when the process of preserving,…
Q: With the use of authentication, which of our objectives can we achieve? What are the advantages and…
A: List the advantages and disadvantages of different authentication systems. Advantages: For big…
Q: There is a feature known as __________________ in many programming languages, which means that,…
A: The question is to fill the blank for the given problem.
Q: Data = 100, 300, 500, 700, 900 Time= 1, 2 , 4, 6, 7 Perform least squares analysis using above…
A: You can find complete matlab code to perform linear regression in matlab.
Q: It is possible to transmit data in both ways at the same time utilizing this data transmission…
A: The sharing, transmitting and receiving of digital or analog data over a network or from one device…
Q: Write a program in the Python language to find the sum of all natural numbers in the range n to 150…
A: Write a program in the Python language to find the sum of all natural numbers in the range n to 150…
Q: Write a complete interactive program that displays the alphabet on the canvas. • Each time the user…
A: ANSWER:-
Q: Computer programming languages were created for what purpose?
A: Computer programming languages were created for what purpose?
Q: Attacks against proxy servers and attacks performed through proxy servers should be described and…
A: Proxy Servers and Attacks: Proxy hacking is a cyber attack method aimed to replace a legitimate…
Q: What are the three DHCP messages that are utilized in the protocol's operation?
A: Dynamic Host Configuration Protocol (DHCP): In the Internet Protocol (IP) world, Dynamic Host…
Q: Is learning new programming languages beneficial to programmers who are already familiar with a wide…
A: Introduction Programming language: A programming language is used to connect with computers by…
Q: You have to create a program in C language in which the user enters the mass M and length L of a…
A: I give the code in C along with output and code screenshot
Q: 5. We can express the relationship between the input and the output of a DSP system in time domain…
A: We can express the relationship between the input and the output of a DSP system in time domain as…
Q: When you execute your program it should ask user to input any number then check if the number is…
A: Introduction: Here we are required to create a program that will check the divisibility of an number…
Q: What is DHCP and how does it work?
A: Dynamic host-configuration-protocol DHCP is the application layer protocol that are used to provide…
Q: Given the PDA below determine whether the following string is accepted or not, write A if accepted…
A: 1) abba => NA(Not-accepted) , It would not be accepted by PDA 2) ε => NA, there is no direct…
Q: Give a thorough explanation of the DNS, including iterative and non-iterative searches,…
A: DNS: DNS is a worldwide system that converts IP addresses into human-readable domain names. When a…
Q: Is there a specific reason why computer programming has been so important to society?
A: Given: Programmers use computer programming languages to display the exact set of digital computer…
Q: III. The figure below shows synchronous TDM, the data rate for each input connection is 1 Mbps. If 1…
A:
Q: Face-to-face classes have been suspended in Hong Kong due to the coronavirus outbreak, forcing…
A: Define: Due to the coronavirus pandemic, students in Hong Kong must study through cloud computing.…
digital logic , pleaseeee solve question 3
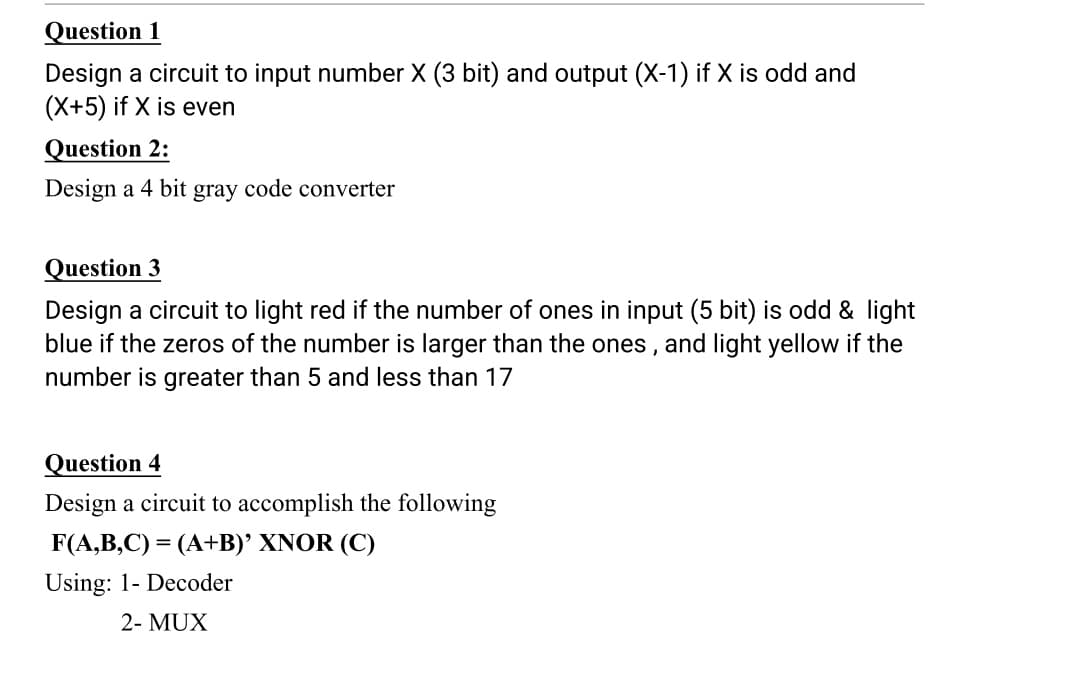
Step by step
Solved in 2 steps with 4 images

- Design a circuit that takes three bits, X2, X1, X0 as input and produces one output, F. F is 1 if and only if 2<=X<=5 when X = (X2, X1, X0) is read as an unsigned integer. For example, if X2=1, X1=0, and X0=0, then the unsigned binary value is 100, which is 4, so the output would be 1. Your Assignment For This Problem Includes the Following Design the necessary circuit using Logisim to implement the situation described above. Use Kmaps for simplification. Be VERY careful to get the correct functions for your output before simplifying and designing the circuit with Logisim. You should minimize the circuit. Your circuit should have three inputs and one LED output. All inputs (X2, X1, X0) and output (F) should be labeled (in Logisim, not by hand). Please use these names to indicate the inputs and output so all projects are consistent. You should also include your name as a label on the circuit. Test your circuit to be sure it is working correctly.Design a circuit that has two inputs X, and S, where X represents an 8-bit BCD number, S is a sign bit. The circuit has one output Y, which is the Binary representation of the signed-magnitude BCD number. A negative output is represented in the Binary 2’s- complement form. You need to think of two design alternatives. Submission guidelines: 1. You should write a report that at least contains the following sections: 1. Problem definition. 2. Design alternatives : 2.1. Alternative 1 block diagram 2.2. Alternative 2 block diagram 3. Design selection criteria 4. Detailed circuit design of the selected alternative. 5. Verilog modules, and simulation results for all modules, and for the whole circuit of the selected alternative .Design a circuit using a Multiplexer, (((USING A MULTIPLEXER NOT A DECODER))) that has two inputs X, and S, where X represents an 8-bit BCD number,S is a sign bit. The circuit has one output Y, which is the Binary representation of thesigned-magnitude BCD number. A negative output is represented in the Binary 2’scomplement form.
- Design a digital circuit that performs the sum of two ASCII-encoded numbers A and B standard in 7 bits. Both operand A and operand B contain two digits, that is, the ones and tens. Each digit is represented individually using ASCII encoding standard in 7 bits. For its part, the result will have 3 digits, that is, units, tens and hundreds, this for avoid overflow. These 3 digits will also be encoded in standard ASCII code in 7 bitsDesign a digital circuit that performs the sum of two ASCII-encoded numbers A and B standard in 7 bits. Both operand A and operand B contain two digits, that is, the ones and tens. Each digit is represented individually using ASCII encoding standard in 7 bits. For its part, the result will have 3 digits, that is, units, tens and hundreds, this for avoid overflow. These 3 digits will also be encoded in standard ASCII code in 7 bits. As an additional restriction, the sum of the two operands must be done in natural binary, A and are always psoitive4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement numberINPUT B: 4 bit 2’s Complement numberOUTPUT: the product of A x B represented as a 8 bit 2’s Complement number Do this:Build a 4 Bit UNSIGNED Multiplier as a subcircuit named UnsignedMultiplier use AND gate ,full and half adders for the circuit
- Consider a special purpose decoder that is called BCD to seven-segment decoder. The decoder takes a 4-bit Binary Coded Decimal (BCD) number X3 X2 X4 X0 (0-9) and produces 7 outputs a, b, c, d, e, f, and g The specification of this circuit is as follows: ⚫ The 7 outputs of the decoder are connected to LED segments as shown in the figure below. The LEDs are active low, ie, the LED emits light when it is connected to logic 0. • The decoder output is determined in a way so that the LED segments display the decimal representation of the input. For example, if the input X3 X2 X1 X0 is 0001 respectively (which is equivalent to decimal 1), the outputs a, b, c, d, e, f, and gare 1001111 showing the letter 1 on the display (remember the LEDs are active low). Decoder W- 4x7 e U Answer the following questions: a. Fill in the truth table of that decoder. Choose a good value for the output when the input is greater than decimal 9. b. Derive the simplified Boolean expressions for the outputs a, b, c,…Chose the correct answer for the output F of the following circuit ( Assume that A= 101010, B= 100101, C=111101 and D =110100 and the first bit out from the circuit is bit 0)*Design a circuit that compares two 3-bit numbers A and B to check if they are equal and less than. The circuit has two outputs X and Y, So that X=1 if A==B and X=0 if A!=B and Y=1 if A<B and Y=0 if A>B
- Create a circuit that converts NBCD code into 5311 code. If the input is not part of the NBCD code, the output is all 1. -Input should be 4-bit NBCD code, output should be 4-bits 5311 code -Create a Karnaugh map for each output bits.Design a combinational circuit that uses 4-bit adders and 2-to-1 MUXes. Given two 8-input signed 2s-complement numbers A and B and a binary input signal M, your circuit should produce an 8-bit signed 2s-complement result R, as follows: if (M == 0) R = A + 7; else R = B + 15;Design a circuit with a 4-bit BCD input A, B, C, D that produces an output W, X, Y, Z that is equal to the input + 3 in binary. For example, 9 (1001) + 3 (0011) = 12 (1100). The outputs for invalid BCD codes are don’t-cares. Write the truth table and the Karnaugh maps used to simplify the Boolean expression!

