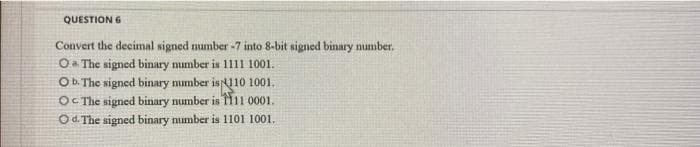
QUESTION 6 Convert the decimal signed number -7 into 8-bit signed binary number. OThe signed binary number is 1111 1001. OD The signed binary number isu10 1001. OC The signed binary number is Hii 0001. Od The signed binary number is 1101 1001.
Q: Q1: Design a Moore FSM to detect if an input sequence is divisible by 5. Each cycle a new bit comes ...
A: sequence detector is a sequential state machine that takes an input string of bits and generates an ...
Q: Nada is a student at Computer and Information Sciences College at Imam Mohammad Ibn Saud Islamic Uni...
A: Nada is a student at Computer and Information Sciences College at Imam Mohammad Ibn Saud Islamic U...
Q: What is the difference between hardware interrupts and software interrupts, and what are some exampl...
A: Answer :
Q: 2. Using Divide and Conquer technique, sort the given number using quick sort 9,1,3,5,2,6,4
A: Quick Sort: This technique uses the divide and conquer technique, this uses the pivot to make partit...
Q: 3. Write JavaScript codes for the following program: Declare 2 variables: FirstName and LastName Get...
A: I am using prompt command to take input from usernwhich works only on browsers so I have written the...
Q: In a binary search tree, how do you add a new item?
A: In a binary search tree, how do you add a new item? Here, know about how can we add new item in bina...
Q: If the English Philosopher Thomas Hobbes could be called 'grandfather' of artificial intelligence, t...
A: I have answered this question in step 2.
Q: To accelerate the processing, we would like to split the original list of messages into 3. Rewrite t...
A: CODE:- // Go program to illustrate how// to create an anonymous Goroutinepackage main import ( "...
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position...
A: If we talk about the future of technology factories speaking it would be uncertain we are not sure i...
Q: Identify three of the factors that EIGRP hub-and-spoke scalability relies on. (Choose three.) a. You...
A: EIGRP hub and spoke:- EIGRP hub and spoke network, in this, we have one or more stub networks are co...
Q: 2. Using Divide and Conquer technique, sort the given number using quick sort 9,1,3,5,2,6,4
A: check further steps for the answer :
Q: Write a JAVA Program to get the k largest elements in an user entered array.
A: // Java code for k largest elements in an array import java.util.Arrays; import java.util.Collectio...
Q: 2 Using Divide and Conquer technique, sort the given number using quick sort 9,1,3,5,2,6,4
A: As we know that in the quick sort we consider the pivot and then move the pivot to the end Then we ...
Q: What prompted the invention of the computer?
A: the answer is given below:-
Q: In a linked list, how do you look for a certain key
A: In Step 2, I have provided answer with explanation------------
Q: What is open source in computer science?
A: Here, I have to explain open source in computer science.
Q: Most widely used graphical user interface operating system for personal computers is Select one: a. ...
A: most widely use GUI for personal computer is
Q: Instructions QuartsToGallonsjava + 1 // QuartsToGallons.java 2 class Quarts ToGallons { public stati...
A: public class QuartsToGallons{ public static void main(String[] args) { int QUARTS_IN_GALLON; ...
Q: P and Q are two processes that share a set of variables that is common. The variable includes: seq, ...
A: The answer is given below:-
Q: Identify five (5) threats to modern security architecture and design and Identify the possible vulne...
A: the five threats to modern security architecture and design are Malware hidden backdoor program un...
Q: Part 2: Relational data model. Take a subset of the ideas from the conceptual model you constructed ...
A: The relational data model have the five entities and 24 attributes. pk - primary key fk - foreign...
Q: Why are analog calculators, op amps, and slide rules important to today's computers? Explain and giv...
A: The answer is given below:-
Q: Consider a neuron with a sigmoidal activation function. The input vector (x1,x2]=[1,1] and the weigh...
A: Given: The neuron is having sigmoidal activation function. The input vector = [1, 1] The weights are...
Q: Alternative 1: 6 outcomes Alternative 2: Step 1: Alternative 1: 4 outcomes Alternative 2: 1 outcome ...
A:
Q: Why are there so many different partitioning algorithms in use by operating systems, and why they di...
A: Given: Why are there so many different partitioning algorithms in use by operating systems, and wh...
Q: When does it make sense to break down large computer processes and programs into smaller subsystems?...
A: ==> Every software consists of processes/programs. ==> Breaking the process or program makes e...
Q: What is open source in computer science?
A: This question comes from Internet Technologies which is a paper of computer science. Let's discuss i...
Q: ease Use Python ## Given the stubs for the following function ## and the main program, complete th...
A: # Given the stubs for the following function# and the main program, complete them# to output the res...
Q: Question:: When does it make sense to break down large computer processes and programs into smaller ...
A: Answer - While any large process is assigned to the computer it will divide the task into small mod...
Q: The characteristics of a computer system that can think, reason, and learn are known.
A: Calculations performed by computers are substantially faster than those performed by humans. Million...
Q: Identify five (5) threats to modern security architecture and design and Identify the possible vulne...
A: a) The five threats that can occur to the security are: i) Malware: A cybercriminal can inject your ...
Q: Design a VI in LabVIEW to display the sum of first 'n' numbers using for loop, e.g., if user enters ...
A: here in this question we will develop program which will accept number from user and then it will ca...
Q: Texas Instruments, Inc. makes a cheap LISP machine called:
A: Texas Instruments, Inc. makes a cheap LISP machine called:
Q: Describe any 50 Port Numbers and their services
A: Step 1: Port number is defined as the logical address of each application that uses the Internet to ...
Q: Hello, the code task below has to be written in python 3 and the HTTP must show the html file from t...
A: The answer is given below:-
Q: Show that f(n) is Θ(g(n)) for the correct function g(n). Prove your result using the definitions fro...
A: f(n) = n 1.5 log(2n) + n 2 log(n 2 ) + √ n:-
Q: Given an array of shape (4, 1, 3, 2) ,which of the following array-shapes are broadcast-compatible?
A: The term "broadcasting" refers to how Numpy handles arrays of differing dimensions during arithmetic...
Q: Computer operating system is basically a Select one: a. system utility O b. package software C. syst...
A: Option (c) is correct. Computer operating system is basically a system software.
Q: Program in C Language to implement Gauss Elimination method
A: The Galerkin finite element strategy: Factorization is a procedure that involves the step-by-step re...
Q: What Is SDILC?
A: A software development life cycle or SDLC is a process that defines different stages that are neces...
Q: USING VIVADO Write and simulate
A: The answer is as follows.The testbench Verilog code for the ALU is also provided for simulation Veri...
Q: What is the difference between hardware interrupts and software interrupts, and what are some exampl...
A: Interrupts caused by hardware: Hardware interruptions are generated via physical signals generated e...
Q: Consider the data on your computer. Do you have any personal information on your computer? What woul...
A: "Yes," said the majority of individual users, who keep sensitive and secret information on their com...
Q: What is the primary purpose of business analysis? O To organize an information systems project in th...
A: Here is the detailed explanation of the answers.
Q: Write a Python program that asks the user for a quantity and takes that many marks out of 100 as inp...
A: PROGRAM EXPLANATION: Take quantity ( a number ) as input. Create three variables to find valid mark...
Q: What is the evolution of mobile phones?
A: I have written evolution of mobile phones below,
Q: Associations between variables: (Python + Report) Compute the sample correlation coefficient between...
A: Average time spent per page: (Python + Report) We would like to estimate the average time spent on a...
Q: What Is SDLC?
A: SDLC stands for Software Development Life Cycle. It contains many models and the examples of models ...
Q: If you wanted to know the position of the letter v (i.e. return 2) in the String str containing the ...
A: Ans: If you wanted to know the position of the letter v (i.e. return 2) in the String str containing...
Q: The solution for many vulnerabilities is proper encoding of user-supplied data. Compare and contrast...
A: The solution for many vulnerabilities is proper encoding of user-supplied data. Compare and contrast...
with explational
Step by step
Solved in 2 steps

- Negative signed binary numbers What is the decimal representation of the 16-bit signed binary number 1111_1111_1001_0001? What is the decimal representation of the 9-bit signed binary number 1_0001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_0001_0001?Negative signed binary numbers What is the decimal representation of the 8-bit signed binary number 1001_0001? What is the decimal representation of the 16-bit signed binary number 1111_1111_1001_0001?Convert IEEE Single-Precision Binary Format Real number 11000100101001000010101000000000 to decimal. Please show all the steps. a) [1] What is the sign? b) [1] What is the biased exponent value? c) [1] What is the unbiased exponent value? d) [2] What is the normalized representation of the number in BINARY? e) [1] What is the unnormalized representation of the number in BINARY? f) [1] What is the decimal value of the whole number part of the number? g) [2] What is the decimal value of the fractional part of the number? h) [1] What is the real number in base 10
- Can I get help with this binary ? (a) Using number C and number D from (b), use binary arithmetic to calculate: numberC.375 + numberD.5 giving your answer in binary and decimal. Convert numberC.375 into IEEE-754 format. (b) Choose a number between 175 and 240 – this is numberE. Convert numberE into hexadecimal. Choose a number between 140 and 160 – this is numberF. Convert numberF into octal. Using 8- bit binary, calculate numberE AND numberF Give your answer in binary, octal, decimal and hexadecimal.With Fixed-length Binary Numbers: What is the decimal representation of the 10-bit signed binary number 01_0001_0001? What is the decimal representation of the 16-bit signed binary number 0000_0001_0001_0001?dont use others answers 3 a) Represent the decimal number -89 in binary using 8-bit: i.Signed magnitude: ____________________________ ii.One's complement: ____________________________ iii.Two's complement: ___________________________ b) What decimal value does the 8-bit binary number 10011110 have if: i.it is interpreted as an unsigned number? ___________________________ ii.it is on a computer using signed-magnitude representation? _______________________ iii.it is on a computer using one’s complement representation? _______________________ iv.it is on a computer using two’s complement representation? _______________________
- Determine the gi, pi, Pi, and Gi values of these two 16-bit numbers: a: 0001 1010 0011 0011two b: 1110 0101 1110 1011two Also, what is CarryOut15 (C4)?The binary number 1001 converts to the decimal number 9, with the 0th (zeroth) bit on the right representing 1 and the 3rd bit representing 8. If you're converting the decimal number 33 to binary, what is the highest numbered bit (counting from the 0th bit on the right) that will be set? a. 0th b. 1st c. 2nd d. 5th e. 6thWhat bit pattern is stored for the following characters assuming an 8-bit byte? a. A b. a c. 8 d. % 2. What character is represented by the following bit patterns? a. 0011 0000 b. 0100 0011 c. 0111 1000 d. 0010 1010
- Please solve only 4 part rest are already answered This problem covers floating-point IEEE 754 format. 1)List four floating-point operations that cause NaN to be created? 2) In the 32-bit (single precision) IEEE 754 format, what is the encoding for negative zero? 3) In the 32-bit (single precision) IEEE 754 format, what is the encoding for positive infinity? 4) Assuming 32-bit (single precision) IEEE 754 format, what decimal number is represent by this word: 1 01111101 001000000000000000000009. Answer the following questions about IEEE 754 32-bit single precision numbers. a. Draw a diagram of the number format. b. What’s the range of numbers that can be represented? c. What’s meant by normalization? d. What’s the implied bit? e. What’s meant by exponent overflow and underflow? f. What’s meant by significand overflow and underflow? g. How’s + ∞ represented? h. How would he following numbers be represented? i. 1.6328125 x 2^-20 ii. 1.6328125 x 2^20 iii. -1.6328125 x 2^-20 iv. -1.6328125 x 2^20a. What decimal number is represented by the following single precisionfloat?1 0111 1100 0110 0000 0110 0000 0000 000b. What decimal number is represented by the following single precisionfloat?1 0101 1100 0110 0010 0110 0000 0000 000c. How many bits are needed to represent 57B(Hex) in binary?

