What is the primary purpose of business analysis? O To organize an information systems project in the most effective way To determine the ways in which a proposed information systems project will change the way an organization conducts its business. O To determine the best possible technical implementation process for the planned information systems
What is the primary purpose of business analysis? O To organize an information systems project in the most effective way To determine the ways in which a proposed information systems project will change the way an organization conducts its business. O To determine the best possible technical implementation process for the planned information systems
Fundamentals of Information Systems
9th Edition
ISBN:9781337097536
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter1: An Introduction To Information Systems In Organizations
Section: Chapter Questions
Problem 6SAT: Managers have an essential role to play in the successful implementation and use of information...
Related questions
Question
Transcribed Image Text:What is the primary purpose of business analysis?
O To organize an information systems project in the most effective way
To determine the ways in which a proposed information systems project will
change the way an organization conducts its business.
O To determine the best possible technical implementation process for the planned
information systems
O To determine the most cost-effective way of running an information systems
project
O None of these
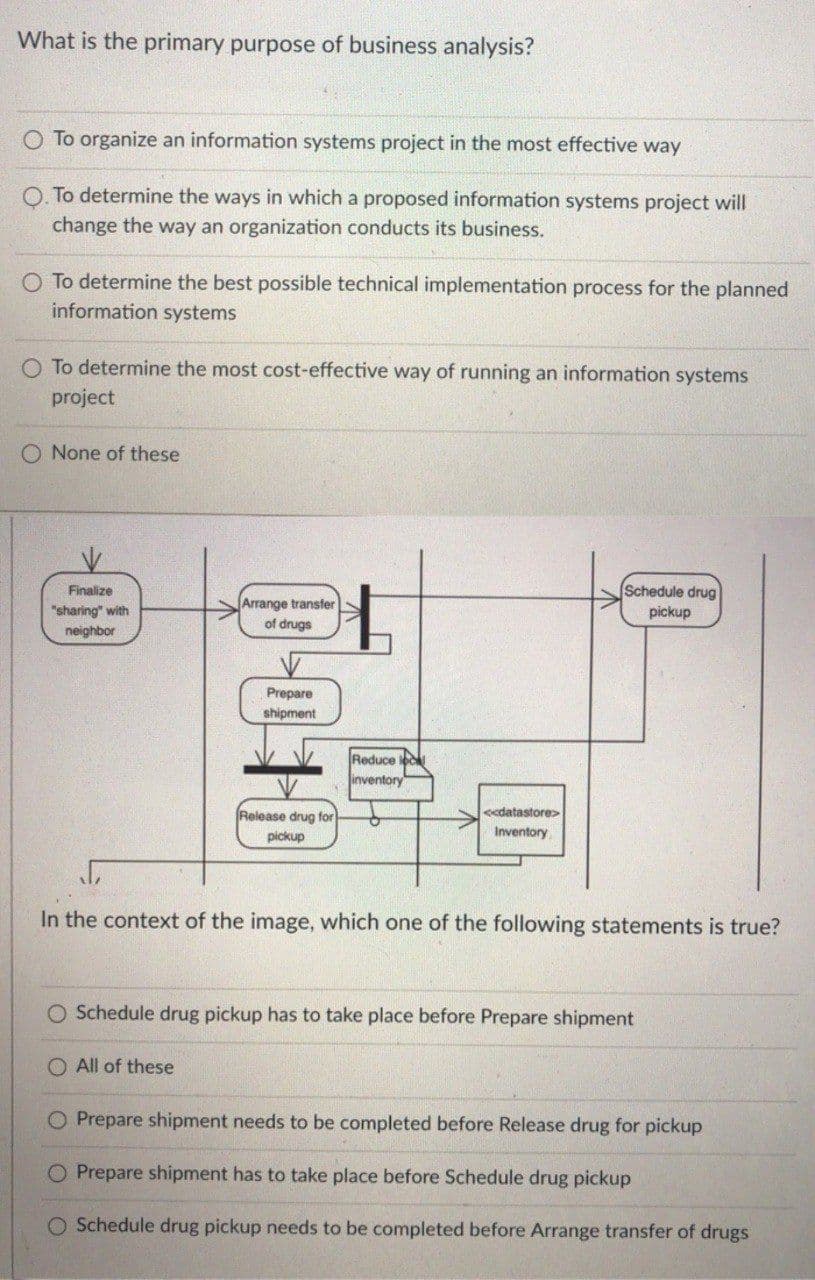
Finalize
Schedule drug
Arrange transfer
of drugs
"sharing" with
pickup
neighbor
Prepare
shipment
Reduce loc
inventory
Release drug for
<<datastore>
pickup
Inventory
In the context of the image, which one of the following statements is true?
O Schedule drug pickup has to take place before Prepare shipment
All of these
Prepare shipment needs to be completed before Release drug for pickup
O Prepare shipment has to take place before Schedule drug pickup
O Schedule drug pickup needs to be completed before Arrange transfer of drugs
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Information Technology Project Management
Computer Science
ISBN:
9781337101356
Author:
Kathy Schwalbe
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Information Technology Project Management
Computer Science
ISBN:
9781337101356
Author:
Kathy Schwalbe
Publisher:
Cengage Learning