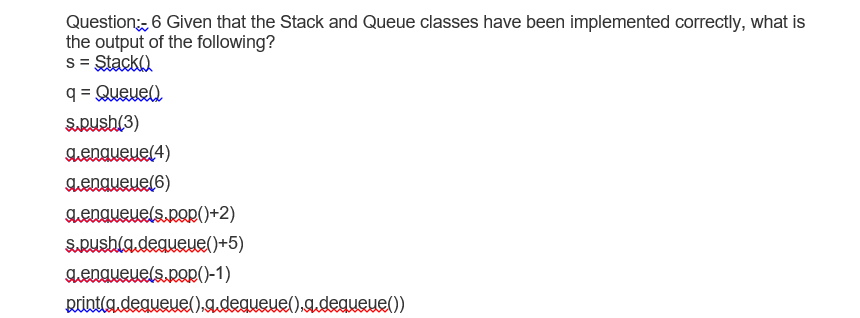
Question, 6 Given that the Stack and Queue classes have been implemented the output of the following? s = Stack) q = Queuel SRush(3) Aengueue(4) Aengueue(6) aenaueuels.pop()+2) SRushladequeue()+5) genaueuels.pop()-1) print(g.degueue().g.degueue().g.degueue())
Q: Is CBIS suitable for all businesses? How did CBIS come into being? What's the point of a company…
A: Introduction: An enterprise computer-based information system (CBIS) is a sort of technology that…
Q: Test Coverage" is a word used in manual testing.
A: What is Test Coverage in Manual Testing Test coverage determines if our test cases cover the…
Q: Are there any examples of cybercrime that have occurred in the real world?
A: Defining cybercrime: Cybercrime classifications. Invasion of privacy and identity theft Internet…
Q: dvantages of using automated testin
A: Automated Testing is the procedure for mechanizing the manual testing process. In this interaction,…
Q: Explain why many IT professionals may disregard project expense management and how this may impact…
A: Define: Cost accounting is normally unbroken lower in IT project management. Most comes are oriented…
Q: int functionC (int n) { int i, j, sumC = 0; for (i=n; i > 0; i=i-5) for (j=1; j 0) { if (functionC…
A: The solution of the above question is:
Q: Software Test Engineers need to have the following qualities:
A: Given: The field of technology is one that is always undergoing change as new innovations are…
Q: Does it matter if you're in a production or testing environment?
A: Introduction: You may execute your update against a controlled set of data in a test environment…
Q: Investigate and evaluate two encryption and intrusion detection approaches. no similarity no…
A: Encryption: The process of encoding data in cryptography is known as Encryption. This technique i.e.…
Q: Explain in a few words what it means to learn in a group.
A: Write about cooperative learning in response to the prompt: Cooperative learning is a teaching style…
Q: Describe how DIGITAL SIGNATURES secure the message against tampering but not eavesdropping. (create…
A: Introduction: Describe how DIGITAL SIGNATURES secure the message against tampering but not…
Q: ween authentic and fabricated stuff on
A: What Exactly Is Fake News: Fake news is separated into two categories:1) False information. These…
Q: A processor may decode encrypted data and system instructions in a variety of methods and then…
A: Introduction: The piece of electronic hardware known as a central processing unit (CPU) is…
Q: Where can you get trustworthy information online, and how can you tell when you've found it?
A: Trustworthy information: The capacity of an information system to create accurate and genuine…
Q: Choose a real-world situation with at least three sets of Venn diagrams. Explain why a Venn diagram…
A: A real-world example using at least three sets that use a Venn diagram. A Venn diagram is beneficial…
Q: The initial operation in the AES decryption algorithm is which of the following? Substitution of…
A: AES encryption standard: Encryption and decryption are critical components of data security while…
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: Is there anything I need to keep in mind before making the switch? Then why don't you provide…
A: Additional Information: Any applicable talents, credentials, or traits that might complement your…
Q: Whether there are no defects in the programme, how can software testing tell if there are any?
A: Software Testing Software testing is a comprehensive process that is made up of multiple…
Q: Testing in a "BLACK BOX" is exactly what it entails, as the term is often used. What are some of the…
A: Black Box: A black box is a mechanism, system, or item in science, computing, and engineering that…
Q: In your opinion, what are a computer's three most important features?
A: Introduction: A machine is composed of a few key components. A machine is composed of a few key…
Q: Using formal approaches in the development of medical and aviation software has many benefits.
A: Development: Personal development goals are targets you establish for yourself to better your…
Q: Choose a real-world situation with at least three sets of Venn diagrams. Explain why a Venn diagram…
A: Establishment: a real-life example of a Venn diagram with at least three sets For this case, a Venn…
Q: What traits are necessary for a software test engineer to succeed?
A: Software Tester A software tester is a person that examines software for bugs, faults, flaws, or…
Q: we define a "computer" in our every
A: A computer is a computerized electronic machine that can be customized to do arrangements of…
Q: How can you tell the difference between a domain and a workgroup?
A: Domain and Work group: Organisations with extensive networks and users with varying degrees of…
Q: is defined as the mixture of different content forms such as texts, music, photos or images,…
A: Note: This is a multiple-question-based problem. As per company guidelines, only the first question…
Q: upports Two Addr Id size is 5 bits. If t of One Address ins
A:
Q: Is CBIS suitable for all businesses? How did CBIS come into being? What's the point of a company…
A: Given: Is CBIS appropriate for usage by a company at all times?Yes An enterprise computer-based…
Q: Explain each of the four levels that make up the TCP/IP abstraction stack.
A: The four abstraction layers consist of the connection layer (lowest layer), Internet layer,…
Q: Why are data and processing models increasingly relying on DFDs?
A: answers the previous question: Solution:- The benefits of DFDs have boosted their application in…
Q: When it comes to testing, what are the differences between test criteria and test requirements?
A: Introduction: It's critical to specify your test criteria and requirements while creating tests.…
Q: 3. What is the unction of computer drivers?
A: A driver, or gadget driver, is a bunch of documents that advises a piece of equipment how to work by…
Q: Create two examples of a list: one using bullet points and the other using numbered items.
A: ALGORITHM:- 1. Create a HTML webpage. 2. Use <ul> tag for bullet list. 3. Use <ol> tag…
Q: An information system may be described using object-oriented analysis.
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You !!
Q: Your organisation is attempting to enhance its capacity to generate funds. What type of information…
A: Business intelligence technologies.
Q: List the two well-known data transfer protocols that the Transport Layer provides. Give a short…
A: Transmission Control Protocol (TCP): A network communication protocol that allows applications and…
Q: According to the criteria, which of the follo wing is an example of inappropriate behavior? O An…
A: Software failure Explanation Software bug: It is an unexpected software activity experienced by the…
Q: Scus practical example for ea
A: Interrupting is the exhibit of ending a ceaseless connection in its execution. In digital figuring,…
Q: Your software's resilience may be measured in a variety of ways.
A: Introduction: Reliability metrics are used to assess software dependability. The metric utilized is…
Q: ever becomes true. A. True B. False 2. A loop that never ends is reffered to as a/an:. What it is?…
A: 1.) False.- If the condition keep becoming true again and again the loop will keep executing itself.…
Q: Do you know what may be done to lessen the likelihood of a network outage?
A: Introduction: What steps may be made to lessen the chances of a network failure? Network outages…
Q: The most important part of the SDLC, and can you back it up with at least two instances of…
A: Software Development: Software engineers make many different kinds of solutions, such as desktop and…
Q: How would you compare horizontal and vertical partitioning?
A: GIVEN: Compare horizontal and vertical partitioning. Distinguishing horizontal from vertical…
Q: ii)Explain TCP/four IP's abstraction layers. ii) Describe a hypothetical situation in which two…
A: TCP/IP's abstraction layer: It is used to depict, in the broadest sense, how information changes…
Q: In your perspective, is website hacking a problem for any of the following reasons?
A: Hacking: The act of gaining unauthorized access to a computer system or network of computers. This…
Q: What are the four main sorts of audiences that are taken into consideration, and how does the…
A: The Four Kinds of Audience: When attempting to persuade a group to take action through your speech,…
Q: Explain why many IT professionals may disregard project expense management and how this may impact…
A: IT Project Management: IT project management, the emphasis on cost accounting is unbrokenly reduced.…
Q: [Undecidability and Reductions] OVERLAPPING = {{M, D) : | M is a Turing Machine and D is a DFA such…
A: A reduction from ATM to Overlapping is : Input : <M,w> Create a DFA D which accepts only one…
Q: Write a python program to find the potentia energy using the total energy & kinetic energy. All the…
A: Total energy=potential energy + kinetic energy potential energy=total_energy- kinetic energy…
Step by step
Solved in 2 steps

- S and Q are integer stacks and priority queues, respectively. C mod 3 is the priority of an element C joining the priority queue Q. In other words, the elements' priority numbers are either 0 or 1 or 2. What is the output of the following code if A, B, and C are integer variables? However, the queue procedures have been modified to work on a priority queue. 1.A = 102.B = 113.C = A+B4.while (C < 110) do5. if (C mod 3) = 0 then PUSH (S,C)6. else ENQUEUE (Q,C)7. A = B8. B = C9. C = A + B10.end11.while not EMPTY_STACK (S) do12. POP (S,C)13. PRINT (C)14.end15.while not EMPTY_QUEUE (Q) do16. DEQUEUE (Q, C)17. PRINT (C)18.endIN JAVA This triple-ended queue exercise can be found at https://open.kattis.com/problems/teque. The requirements for this program are compatible with those of the Kattis problem, so a solution should produce correct results when submitted on Kattis. The Triple-Ended QUEue supports four operations: push_back x: inserts the element x at the end of the TEQUE push_front x: inserts the element x at the front of the TEQUE push_middle x: inserts the element x so that the insertion index for x is (k + 1)/2 for a 0-based indexed TEQUE. get i: prints out the ith index element (0-based) of the TEQUE. The TEQUE will be implemented as a linked list. The usual implementation requirements apply along with a screenshot of the results from Kattis. Sample input 10 push_back 1 push_front 2 push_back 3 push_front 4 push_middle 5 push_back 6 get 3 push_middle 7 push_middle 8 get 5 Sample Output 1 1 Subject: Java ProgrammingStarting with an empty Circul Queue, what will be the state of Circular Queue, front, rare, size and number of elements after each of the following operations performed in the order ( i ) enque(A) (ii) enque (B) (iii) enque (C) (iv) dequeue( ) (v) dequeue( ) (vi) enque(D) (vii) enque(E ) (viii) dequeue( )
- In the lecture we studied IntStack, a class that implements a static stack of integers. Write a template that will create a static stack of any data type. Demonstrate the class with a driver program. #pragma once class IntStack{private: int *stackArray; int stackSize; int top; public: IntStack(int size); void push(int num); void pop(int &num); bool isFull(); bool isEmpty();}; Queue Exceptions: Modify the static queue class provided in our lecture as follows. Make the isFull and isEmpty member functions private. Define a queue overflow exception and modify enqueue so that it throws this exception when the queue runs out of space. Define a queue underflow exception and modify dequeue so that it throws this exception when the queue is empty. Rewrite the main program so that it catches overflow exceptions when they occur. The exception handler for queue overflow should print an appropriate error message and then terminate the program. #include…Create Pseudocode for this class Queue { private static int front, rear, capacity; private static int queue[]; Queue(int c) { front = rear = 0; capacity = c; queue = new int[capacity]; } static void queueEnqueue(int data) { if (capacity == rear) { System.out.printf("\nQueue is full\n"); return; } else { queue[rear] = data; rear++; } return; } static void queueDequeue() { if (front == rear) { System.out.printf("\nQueue is empty\n"); return; } else { for (int i = 0; i < rear - 1; i++) { queue[i] = queue[i + 1]; } if (rear < capacity) queue[rear] = 0; rear--; } return; } static void queueDisplay() { int i; if (front == rear) { System.out.printf("\nQueue is Empty\n"); return; } for (i = front; i < rear; i++) { System.out.printf(" %d <-- ", queue[i]); } return; } static void queueFront() { if (front == rear) { System.out.printf("\nQueue is Empty\n"); return; } System.out.printf("\nFront…ALL TRUE OR FALSE QUESTIONS 1. A "deque" allows an application to enqueue and dequeue from both front and rear of a queue. 2. The Queue ADT of the text is defined to hold elements of type Objec 3. Java supports inheritance of interfaces. 4. The text's array-based queue implementations use the fixed-front approach. 5. If N represents the number of elements in the queue, then the dequeue method of the ArrayBoundedQueue class is O(1). 6. When an object of class LinkedQueue represents an empty queue, its rear variable is 0. 7. A standard linked list provides a good implementation of a "Deque". 8. When implementing a queue with a linked list, the front of the queue is also the front of the linked list. 9. Our LinkedQueue class implements the QueueInterface interface. 10. The text's array-based queue implementations use the floating-front approach.
- In C++, Write a program which is menudriven ( i) Enque, ii) Deque, iii) Peek iv) Print). It will create a circularQueue of integer type data using array. You have to implement the followingoperations.a. Enqueue (Insert a data to the queue)b. Dequeue (Remove an item from the queue and printit)c. Peek (Print the item at the Front)Print (Print the elements present at the queue)Determine if the following are true or false A "glass" queue allows an application to peek at the front or rear values of a queue. The enqueue and dequeue queue operations are inverses of each other. Therefore, performing an enqueue followed by a dequeue is always equivalent to performing a dequeue followed by an enqueue. A "glass" queue allows an application to peek at any value in a queue. A java interface can inherit from at most one other interface.There is one stacks and one queue q and then following operations are performed upon these two. Push A, enqueue B, push C, pop, pop, enqueue D, push E, dequeue, enqueue F .What is the total number of elements, which are left in the queue and stack in the end.
- In Javascript an array can be treated like a queue---a FIFO (first-in, first-out) data structure. Which two array operations that we studied in class can be used together to treat an array as a queue? a. isEmpty() and isFull() b. queue() and unqueue() c. unshift() and pop() d. push() and pop() e. unshift() and shift()This question involved the use of stack and queue (like u see below) Those are the class definitions for stacks and queues of integers (like u see below) Need the solution of the program step-by-step please!Given a pointer based queue below: A B C D E F G Assuming the front is on A and the rear is on G, what is the result of enqueueing X and dequeueing one element?

