One computer acting as client sends the following 16 bits to a server using UDP: 10001010 10101111 The server receives the the following string: 10001010 10101111 Show the steps taken by the client and the server to create and use a 8 bits checksum code to check the integrity of the data, i.e. whether there was an error or not in the transmission.
One computer acting as client sends the following 16 bits to a server using UDP: 10001010 10101111 The server receives the the following string: 10001010 10101111 Show the steps taken by the client and the server to create and use a 8 bits checksum code to check the integrity of the data, i.e. whether there was an error or not in the transmission.
A+ Guide to Hardware (Standalone Book) (MindTap Course List)
9th Edition
ISBN:9781305266452
Author:Jean Andrews
Publisher:Jean Andrews
Chapter8: Connecting To And Setting Up A Network
Section: Chapter Questions
Problem 22RB
Related questions
Question
I need the answer as soon as possible
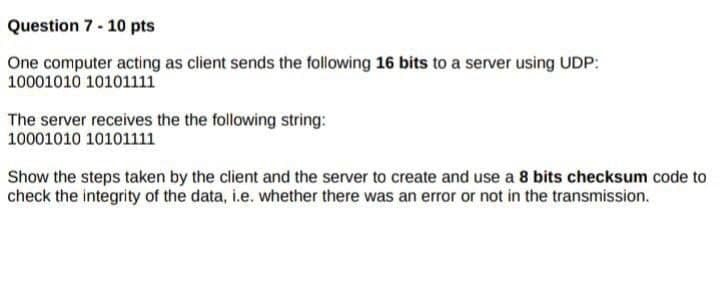
Transcribed Image Text:Question 7 - 10 pts
One computer acting as client sends the following 16 bits to a server using UDP:
10001010 10101111
The server receives the the following string:
10001010 10101111
Show the steps taken by the client and the server to create and use a 8 bits checksum code to
check the integrity of the data, i.e. whether there was an error or not in the transmission.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning