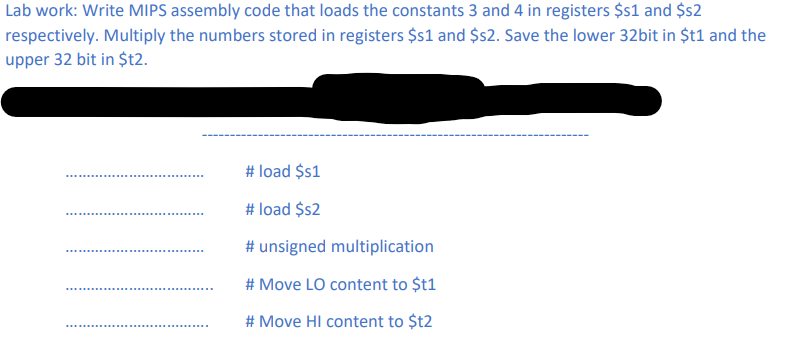
respectively. Multiply the numbers stored in registers $1 and $s2. Save the lower 32bit in $t1 a upper 32 bit in $t2. # load $s1 # load $52 # unsigned multiplication
Q: Classify each of the following attack situations to one of the main attack types (interception, inte...
A: An attack is an intrusion that is caused to a certain system. It can be caused by the malicious mind...
Q: Small monster scientists do a great deal of work to analyze small monster migratory and feeding patt...
A: # function to draw the 10X8 griddef drawGrid(horiz_mult, vert_mult, constant):# importing the turtle...
Q: Manage Your Health, Inc. (MYH) is a Fortune 500 company that provides a variety of healthcare servic...
A: Introduction: the given data
Q: g functions, write and submit the source codes that will solve the given problems. BLEM 1: Create a ...
A: Lets see the solution.
Q: Write a query against the Sales.Orders table that returns orders placed in June 2015. 2)Write a que...
A: Since you have asked multiple questions, so we have provided answer for first three questions. If yo...
Q: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark we...
A: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark ...
Q: in the tradeoffs involved in selecting TCP’s segment retransmission timer lengths.
A: The answer is given below.
Q: Write a python code to build regression models using the following learning algorithm
A: import matplotlib matplotlib.use('GTKAgg') import matplotlib.pyplot as plt import numpy as np f...
Q: What is the output of the following program? Explain why?
A: Program Explanation: Define a class for boy with the instance variable age having a default value o...
Q: The ubiquitous nature of mobile phones today brings tremendous convenience to our lives, but will mi...
A: In today's world of advanced information and technology, mobile phones and devices are being extensi...
Q: Create an ERD with the following Entities and Attributes. Entity: USERS - Attributes: Name of User,...
A: Create an ERD with the following Entities and Attributes. Entity: USERS - Attributes: Name of User, ...
Q: Sites like Zillow get input about house prices from a database and provide nice summaries for reader...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read current_price,...
Q: Question 39 OneDrive lets you keep your files in your home B. the cloud your USB Rash.arve. yourhard...
A: OneDrive is the Microsoft cloud service that connects a person to all his/her files. Using OneDrive ...
Q: Explain why database design is critical in the educational setting.
A: Answer: A well-designed database aids in Adapting to the needs of the user. Produce high-performanc...
Q: Give Description for ReadKey
A: Description for ReadKey
Q: ent of KimTay Pet Supplies (a supplier of pet supplies, food, and accessories located in Cody, Wyomi...
A: Task 1 - CREATE TABLE REP( repID int, LastName varchar(255), FirstName varchar(255), Address varchar...
Q: Task1:In the driver file (main.cpp), perform the following sub-tasks.1.Create two objects of this cl...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Who was the first to create the flash drive?
A: Introduction: Flash drives are portable storage devices. Almost every college student carries a flas...
Q: Write a program that first gets a list of integers from input. The input begins with an integer indi...
A: Lets see the solution in the next steps
Q: Determine whether the following line is accepted/rejected/partial using Cohen Sutherland line clippi...
A: Cohen Sutherland is used for line clipping in visible region. here points of line :(250,150) to (100...
Q: re some potential issues or roadblocks can you see in trying to get this information to address Inu ...
A: It is defined as a systematic method for determining what could go wrong in a plan under development...
Q: Problem Given the following memory values and a one-address machine with an accumulator, what value...
A: a) Immediate addressing mode loads the constant value 20 as an operand to accumulate. AC=20
Q: 3. Practice on the following NumPy functions to create arrays mun Numpy functions your code: Upe svi...
A: Python code for the given NumPy functions import numpy as np a = np.zeros(2, dtype = int)print("Mat...
Q: To restrict access to parts of a Web application, we use access filters. What does not describe acce...
A: You can create custom filter attributes by implementing an appropriate filter interface for which yo...
Q: solve the quation: Manage Your Health, Inc. (MYH) is a Fortune 500 company that provides a variety ...
A: Recreation and Wellness Intranet Project Supports Business Strategies:- Employee health improving a...
Q: There are many problems with using algorithms. What is the main one?
A: Algorithm Development Ones of the most important phases of the software development process is the d...
Q: It is software that can be used on the web.
A: Software plays an important role in the web, there are a lot of tools and software that can help in ...
Q: Computer Science The language used here is C++ Develop a C program that processes a file called "gra...
A: So lets here we write the complete c code and we make this function inside the code and find the min...
Q: 9. Based on the below Verilog statements, how many bits are there in the variable Y? Reg [15:0] A; R...
A: Verilog, standardized as IEEE 1364, is a hardware description language (HDL) used to model electroni...
Q: Create a program that asks the user for the size of the array of fears and then integer inputs which...
A: We have to iterate over the array and when the element is found in array, we simply exit from execut...
Q: Question Consider a language defined over E={a,b} that accepts the strings starting with a. a. Give ...
A: Actually, program is an executable software that runs on a computer.
Q: Given an array nums of size n, return the majority element. The majority element is the element that...
A: PROGRAM INTRODUCTION: Start the definition of the function to find the majority element from the ar...
Q: Which authentication method requires the computer to be joined to either a domain or Azure AD? a. ...
A: Which authentication method requires the computer to be joined to either a domain or Azure AD? a. D...
Q: Hinclude Hinclude ciomanip> using namespace std; void test(int first, int& second); int main () int...
A: The output is below:
Q: s. Create a program that will allow a user to enter 2 numbers using input dialog boxes and calculate...
A: Introduction:
Q: ethod GetLarge
A: Syntax of GetLargestConsoleWindowSize: COORD WINAPI GetLargestConsoleWindowSize( _In_ HANDLE hConso...
Q: epresented by elements on a grid of squares, where a grid has an ar
A:
Q: Draw a flowchart that takes a number input from the user and checks if the number is even. If even i...
A: Flowchart:- It is a pictorial or diagrammatic representation of an algorithm using standard symbol...
Q: PROBLEM 4 ( ) Show that there is no formal proof of p → qF p.
A: Given that p -> q |- p
Q: please code in python You are given an array of strings arr. Your task is to construct a string fro...
A: Here I have created the function named finalString(). In this function, I have extracted the length ...
Q: When you think about data backup and recovery, what are some of the most important things you need t...
A: Introduction to backup and recovery: It play vital role to restore the data form the storage so tha...
Q: what is the Overview of Technology Industry?
A: Stocks responsible for the development, manufacturing, or distribution of technologically related pr...
Q: What kind of rule protect every right when we use each other content?
A: The rule to protect every right when we use each other content is Fair use. It is the rule which def...
Q: What does SCROLLLOCK ON stand for?
A: Introduction: Most IBM-compatible computer keyboards have a lock key (usually with an associated sta...
Q: Python A program to calculate the value of some change in dollars Code evaluation (What is the r...
A: Find the code implementation below.
Q: Create an essay about the given question. What can we do about the growing e-waste problem?
A: let us see the answer:- Introduction:- In our digital age, it appears that fewer and fewer customers...
Q: 1. Design a User Interface (UI) in visual basic programming to calculate a service charge of 2.5% o...
A: Using JavaScript, user experience: The element of your program that's also observable to a specific ...
Q: Computer Ścience The language used here is C++ Develop a C program that processes a file called "gra...
A: The file is opened using the method in C, which is fopen(). The file needs to be saved in the same f...
Q: Create a program where 10 'worker' threads are created. Set all of the worker threads to block on th...
A: Lets see the solution.
Q: Deep Fake in A.I
A: Solution:
Step by step
Solved in 2 steps

- Write the following in LC3 code: Write a program that compares two values stored at memory locations x30A2 and x30A3. If the value at x30A2 is larger than the value at x30A3 then store the value of 1 in R1, else store the value of 0 in R1.Use PC + offset addressing to load contents of x30A2 into R2 and x30A3 into R3. Repeat the previous using Base + offset (load register). Use the load immediate (LEA) instruction to set up the base (R4) with the address of x30A23) The 8-bit register AR, BR, CR, and DR initially have the following values: [5]AR = 11010110; BR = 11100111; CR = 10110001; DR = 10111010Determine the 8-bit values in each register after the execution of the following sequenceof microoperations.AR AR + BR Add BR + ARCR CR AND DR, BR BR + 1 AND DR to CR, Increment BRAR AR - CR Subtract CR from AR1- Perform an arithmetic shift right by two bits of the following bit pattern: 1001 1011 Select one: a. 0010 0110 b. 1100 1101 c. 0011 0111 d. 1110 0110 2- Which instruction moves the least significant bits of a product into register eight? Select one: a. mvlo $8 lo b. addu $B SO lo C. mfio $8 d. move $8 lo 3- What are the names of the two registers that hold the result of a multiply operation? Select one a. S0 and $1 b. high and low RO and R1 d. hi and lo 4- If you have two integers, each represented in 32 bits, how many bits might be needed to hold the product? Select one: a: 16 b. 64 C. 128 d. 32
- Topic: Computer Science, CPU Architecture and Assembly Programming 1. Write ASL programs in EMU8086 to accomplish the following tasks. a) Evaluate (5 + 4) * 36. Your solution should store the answer in the Ax register. b). Evaluate (420 + 312) *300 and explain where is the result of the multiplication. You need to use 2 bytes registers like Ax, Bx, Cx, Dx… to store these type of data that are greater than 255.For the following code, explain what the register file and forwarding unit are doing during thefifth cycle of execution. If any comparisons are being made, mention them. Remember, usethe forwarding unit from class, not the book. LOOP:LDUR X1, [X6, #40]ADD X5, X5, X8ADD X6, X6, X8STUR X1, [X5, #20]CBZ X1, LOOPAnswer the given question with a proper explanation and step-by-step solution. Create a MIPS code file with only the following 4 lines of assembly code: add $t0, $t1, $t2sub $s0, $s1, $s2addi $s2, $t8, 37sll $t0, $t1, 10
- Write assembly code snippet to extract exponent from single precision float sitting in rax register? Write assembly code snippet to detect if number sitting in rdx is negative or not? Write assembly code snippet to detect if number sitting in ah is even or odd? Write assembly code snippet to mimic push instruction, assume number to push is in rdx register. Write assembly code snippet to mimic pop instruction, return the number in rcx.In the Intel 8086 microprocessor, suppose the register AX contains the data 35AB H. What will be the contents of AX after executing the following programs? Assume that the initial content on the Carry Flag (CF) is one for all the calculations. You MUST clearly show ALL your steps in obtaining your final result for getting full and/or partial credit. Please present your final result in Hexadecimal format. (a) MOV CL,04H SHR AX,CL RET (b) MOV CL,04H RCR AX,CL RETQuestion Write an assembly code to implement the y = (x1+x2) * (x3+x4) expression on 2-address machine, and then display the value of y on the screen. Assume that the values of the variables are known. Hence, do not worry about their values in your code. The assembly instructions that are available in this machine are the following: Load b, a Load the value of a to b Add b, a Add the value of a to the value of b and place the result in b Subt b, a Subtract the value of a from the value of b and place the result in b Mult b, a Multiply the values found in a and b and place the result in b Store b, a Store the value of a in b. Output a Display the value of a on the screen Halt Stop the program Note that a or b could be either a register or a variable. Moreover, you can use the temporary registers R1 & R2 in your instructions to prevent changing the values of the variables (x1,x2,x3,x4) in the expression. In…
- 1. T/F - if (B)=006000 (PC)=003600 (X)=000090, for the machine instruction 0x032026, the target address is 003000.2. T/F – PC register stores the return address for subroutine jump.3. T/F – S register contains a variety of information such as condition code.4. T/F – INPUT WORD 1034 – This means Operating system should reserve 1034 bytes in memory5. T/F - In a two pass assembler, adding literals to literal table and address resolution of local symbol are done using first pass and second pass respectively.Using the AddTwo program from Section 3.2 as a reference, write a program that calculates the following expression, using registers: A = (A+B) - (C+D). Assign integer values to the EAX, EBX, ECX, and EDX registers. Set memory values that require support for signed and unsigned values. Verify your work by calculating by hand the result.NOTE: This is an assembly class, so these programs must be coded in Pi 5 - In a normal swap a temporary variable is needed, eg "r2 = r0; r0 = r1; r1 = r2; " swaps r0 and r1. A swap can be implemented without the temporary r2 register using xor operations (the eor instruction). Write a program to swap two registers using eor instructions. # Program File: Neg.s# Purpose: This program reads a number and prints out the negative value. .text.global mainmain: #Push stack SUB sp, sp, #4 STR lr, [sp, #0] #Prompt and read number LDR r0, =prompt BL printf LDR r0, =format LDR r1, =number BL scanf #Calc negative LDR r1, =number LDR r1, [r1] MVN r1, r1 ADD r1, r1, #1 #Print Answer LDR r0, =output BL printf #Pop stack MOV r0, #0 // Make the program return true LDR lr, [sp, #0] ADD sp, sp, #4 MOV pc, lr.data prompt: .asciz "\nEnter a number: " output: .asciz "\nThe negative value is %d\n" number: .word 0 format: .asciz "%d"

