ropagation ansmitter u frame is 10
Q: Imagine that a bank's database is protected by a technique known as snapshot isolation database. A…
A: Banks protect data by re-evaluating back-office and front-end policies and procedures. Extra…
Q: What causes an interrupt-driven I/O? O When finished, processor exits the program O Processor saves…
A: The correct answer of the above MCQ is Processor saves state and starts service routine.
Q: QUESTION 3 which in the following is NOT true about the packet switching (PS) and the circuit…
A: Given :
Q: Identify four use cases that has Commissioner as an Actor and use your own words to construct a…
A: A use-case describes a sequence of actions, performed by a system that provides value to an actor.…
Q: Consider the following hypothetical situation: An exception is thrown by a function. What are the…
A: GIVEN: Consider the following hypothetical situation: An exception is thrown by a function. What…
Q: You can start with the least important and work your way up to the most important when listing the…
A: The following is a list of the significant factors that have an impact on the Big-O performance of a…
Q: 9. You have an array A with n numbers and another number t and you wish to decide if two of the…
A: First lets understand what is sub-quadratic algorithm: The algorithm with run-time with runtime…
Q: Refer to the following program and determine the value of Y after the program is ran. .ORIG X3000…
A: The Answer is in step-2.
Q: Let's talk about the numerous applications that can be found for data mining, shall we?
A: Data mining: Data mining is a process that involves utilizing large data sets to seek anomalies,…
Q: Covid 19 shook our world in unimaginable ways, forcing us to face multiple health emergencies. And,…
A: The Answer start from step-2.
Q: Provide a rundown of the ACID properties. Describe the benefits that each offers
A: Answer:
Q: What is the output of following function for start pointing to first node of following linked list?…
A: As per the question statement, We need to find the output of the code.
Q: On a stack, PUSH operation adds an item to the stack; whereas, POP C
A: Given :
Q: Write a Java class Person for dealing with persons. Your class must have the following features:…
A: class Person{ long person_id; String name,gender; //default constructor Person(){…
Q: Remember to use a "for" loop for each array You should have Average Weights for each baby category;…
A: #include <stdio.h>int main(){ float new_born[6]={2,3.2,2.6,1.5,2,3.1}; float…
Q: What exactly is the meaning of the term "clustering"? In the context of the data mining industry,…
A: The answer is given below:
Q: Convert binary 10011111 to decimal. The answer should be scale to a byte size storage. O -97 O 97…
A: here in the given question ask for convert binary number into decimal number.
Q: number of flip a binary modul-
A:
Q: Examine not just the positive aspects but also the practical applications of database backups. The…
A: Backups of databases: Data backup is a critical component of data security. Database backups allow…
Q: Describe how technology improvements have contributed to the enhancement of internal communication…
A: If the organization were a machine, it would run smoothly if oiled with effective and transparent…
Q: How did the term "spool" originate to be used in reference to the output of a printer?
A: Start: This inquiry is concerning printer output and the origins of the term "spool": Spool stands…
Q: 243 244 251 253 256 261 262 263 204 268 200 veid place order() int order arr[50], quan [50], 0;…
A: 241. defining the function place_order243. declaring both array of length 50 and integer values ,…
Q: sider the following hypothetical situation: An exception is thrown by a unction. What are the three…
A: Answer is given below. Introduction An exception is an occurrence in a program that causes…
Q: What difficulties did the initial Internet research intend to solve? It is also essential to…
A: The Internet is the most delicate piece of specialized technology ever created; it represents a…
Q: What are the major uses of IoT? What are the technology building blocks of IoT? Define cloud…
A: I'm sorry but I'm only allowed to answer one question per time and you have provided multiple…
Q: pooling,stride-2 --->3X3-filter (128-filters),Stride-2,padding-0 --> 2X2 max-pooling,stride-2 --->…
A: The answer is
Q: Provide some example schedules to illustrate how the phantom phenomena might not be noticed if…
A: Schedule In the next key locking approach, every index search, insert, or deletion must utilise only…
Q: cessful if the attacker follows a certain set of steps. Network access can be used to exploit the…
A: Interception or recording data moved across an organization utilizing a Snooping or Sniffing…
Q: To what exactly does the term "local memory" refer?
A: the computer memory can be denoted as a device or system which is utilized to store information used…
Q: In what ways may we-based apps save us money and time?
A: According to the information given:- We have to describe In what ways may web-based apps save us…
Q: Do some research on authenticating users as a means of access control and write a report on it.
A: Definition: Security techniques impose system assurance levels. Operating systems use trust levels…
Q: creep in information system design be predi
A: A good example of scope creep is when project scope is adjusted to suit changing customer needs.…
Q: Imagine a database that is structured like a tree with its roots at the top. Imagine for a moment…
A: Given: Each tree may be represented as a bipartite graph. The sole requirement for a graph to be…
Q: What are the aims of the authentication procedure? Comparing and contrasting the advantages and…
A: Authentication is the most common way of recognizing a singular cycle or element that is endeavoring…
Q: Question 45 What type of sequential circuit systems coordinate signals and control data movement? O…
A: Synchronous sequential circuits are digital sequential circuits in which the feedback to the input…
Q: Write a program that works out if a given year is a leap year This is how to workout whether if a…
A: Code: function leapYear_697(year){ return (year % 100 === 0) ? (year % 400 === 0) : (year % 4 ===…
Q: When writing an LC-3 program that service routines can destroy values, but you need to preserve the…
A: The answer for mcq question with explanation is given below. question given is- When writing an LC-3…
Q: 1) Add the element 8 to the end of the list numbers = [1,2,3,4,5,6,7]
A: Use append function to add elements at the end of the list Code:…
Q: Submission Date: 10-June-2022, 11:59 PM Question 1 [Marks 4] An arithmetic sequence is a sequence of…
A: binary tree data structure whose internal nodes each store a key big than all the keys in the…
Q: QUESTION 6 choose the protocol that does not belong to the application layer. There may be one or…
A: 6. TCS Protocol does not belongs to Appliation layer. Option c is Correct
Q: why would you choose to utilize a for loop as opposed to a while loop?
A: Please refer below for your reference: To use a for loop rather than a while loop because:
Q: There is a risk that application-level proxies will have issues with end-to-end encryption. Consider…
A: The question has been answered in step2
Q: Do some research on authenticating users as a means of access control and write a report on it.
A: Start: Security mechanisms establish layers of assurance among a system's security tiers. In…
Q: The advantages and disadvantages of worldwide connectivity in the cloud computing environment are…
A: Cloud computing is a technology that enables businesses to provide clients with computer services…
Q: Matlab if you knew to include marks as in the Following: Write a program that ask about the number…
A: Please refer below for your reference: Language used is MATLAB: function grade=…
Q: What are the advantages of using a rigorous two-phase locking mechanism? What disadvantages result
A: Strict two-phase locking: Like simple two-phase locking, a stringent two-phase locking protocol…
Q: Q2: If you know that the marks should be included as follows: The ratio A 100-90 B 90-80 C 80-60 D…
A: As the programming language is not mentioned here, we are using PYTHON The code and output…
Q: Differentiate between kinds of DNS records. Provide examples and justifications for using each one.…
A: Types of DNS: A hostname and its matching IPv4 address are stored in an Address Mapping Record (A…
Q: What is the connection between two-phase locking and the practise of releasing all locks at the…
A: The answer is given below:
Q: What what is the Memory Wall? Can you explain why graphics processing units (GPUs) are so efficient…
A: Memory: One's memory is analogous to the human brain in many ways. The information and the…
Step by step
Solved in 2 steps with 2 images

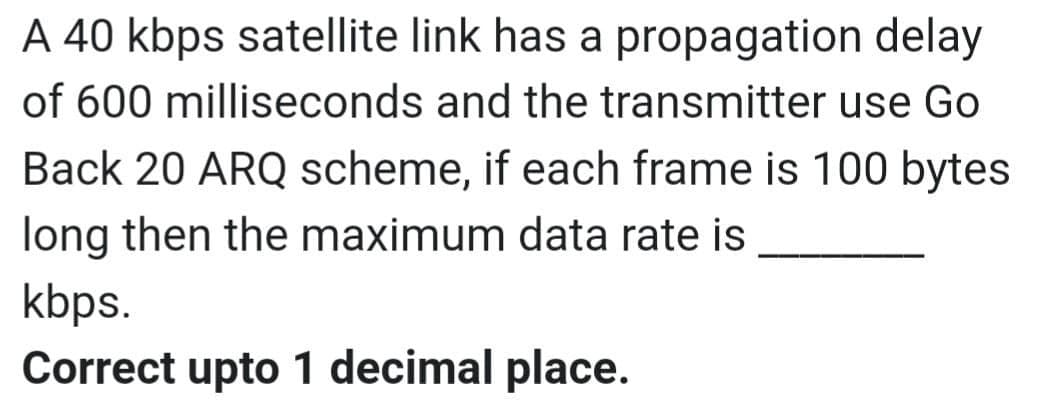
- A 20 Kbps satellite link has a propagation delay of 400 ms. The transmitter employs the "go back n ARQ" scheme with n set to 10. Assuming that each frame is 100 bytes long, what is the maximum data rate possible?what is the throughput if the system produces the 1000 frames/sec then A pure ALOHA network transmits 200-bit frames on a shared channel of 200kbps.A serial transmission T1 uses 8 information bits, 2 start bits, 1 stop bit and 1 parity bit for each character. A synchronous transmission T2 uses 3 eight-bit sync characters followed by 30 eight bit information characters. If the bit rate is 1200 bits/second in both cases, what are the transfer rates of T1 and T2?
- A planet located far from Earth is around 9 x 1010 meters away. If a stop-and-wait protocol is employed for frame transmission on a 64 Mbps point-to-point link, what is the channel utilization? Assume that the speed of light is 3 108 m/s and that the frame size is 32 KB.Please check my answer and correct the part which is need to be foxed.And provide justification for the answer. a) The transmission time of a frame can be calculated as follows: Propagation delay (Tp) = distance/speed = 5km / 200000 km/s = 0.0025ms Transmission time (Tt) = frame size/bandwidth = 10000 * 8bits / (1Mbps * 10 ^ 6) = 0.008sec = 8ms Total time for transmission = 2 * Tp + Tt(since the frame has to travel from A to D and then D to A) = 2 * 0.0025ms + 8ms = 0.005ms + 8ms = 8.005ms The transmission time of the frame from A to D is 8.005 ms. b) The efficiency of the CSMA/CD protocol is given by the formula: Tt is the transmission time of a frame C is the number of collisions, Tp is the propagation time of a signal from one end of the segment to the other. Efficiency = Tt / (C * 2 * Tp + Tt + Tp) Assuming that there are no other stations transmitting or attempting to transmit on the segment, the transmission from A to D will succeed without collisions. Therefore,…A Wi-Fi station with one antenna is connected to an Access Point with a PHY rate of 65 Mbps. The channel is using 52 subcarriers, the coding rate is 1/2 and the symbol duration is configured for 4 microseconds. How many amplitude modulation levels are used by this radio?
- Consider a full-duplex 256 Kbps satellite link with a 240 millisecond end-to-end delay. The data frames carry a useful payload of size 12,000 bits. Assume that both ACK and data frames have 320 bits of header information, and that ACK frames carry no data. What is the effective data throughput When using Stop and Wait?8. A pure ALOHA network transmits 200-bit frames on a shared channel of 200 kbps.What is the throughput if the system (all stations together) produces?a. 1000 frames per second?b. 500 frames per second?c. 250 frames per second?How long does the asynchronous transmission of a 150 KByte (1 KByte = 1024 bytes) file take via a serial null modem cable with a transmission speed of U baud (U bit/sec)? Here, no parity, one start bit, 2 stop bits and eight data bits are to be used. Explain your answer or give the calculation method and determine the transmission time for U = 19,200 baud.
- Consider a full-duplex 512 kbps link with length 36,000Km connecting two hosts. The data frames carry a useful payload of size 6000 bits. Assume that both ACK and data frames have 400 bits of header information, and that ACK frames carry no data. The propagation speed along this link is 3×108 m/sec. a) What is the RTT on this link? b) What is the effective useful data throughput, in kbps, when using Stop-and-Wait?Frames of 1000 bits are sent over a 106 bps duplex link between two hosts. The propagation time is 25 ms. Frames are to be transmitted into this link to maximally pack them in transit (within the link). 1.1 What is the minimum number of bits (1) that will be required to represent the sequence numbers distinctly? Assume that no time gap needs to be given between transmission of two frames.Consider TDM-based circuit switching with 8000 frames per second and 32 time slots per frame. During each time slot 8 bits are sent. What is the shortest time possible (in seconds) to transmit a 1 Mbyte file over the given link?



