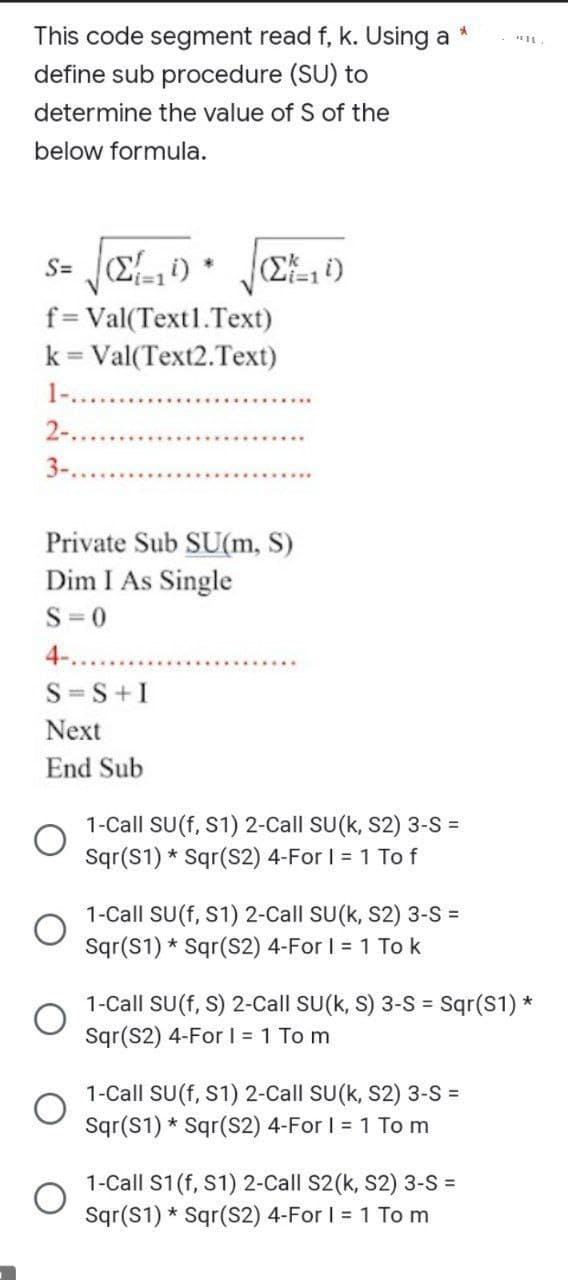
S= Σ(10) f= Val(Text1.Text) k = Val(Text2.Text) 2-...... 3-.......... (Σ=1 ) Private Sub SU(m, S)
Q: In this side-by-side comparison, the Rational Unified paradigm is placed against the Classical…
A: SDLC includes these two models: Cascade programming involves substantial advance planning and…
Q: * * To write mathematical equations we :go the menu View Insert Review Home File To change the line…
A: Answer:
Q: Assume the part of an IT analyst who is tasked with the creation of a comprehensive testing…
A: Systems Analyst: A system analyst collects and arranges information about software. The user…
Q: What do you consider to be the four most important traits for developing software? Please offer your…
A: Given: What are four key software development characteristics? Please give your opinions on four…
Q: . In the last section, we discussed a multithreaded tile server and demonstrated why this kind of…
A: Multithreading: It is a central processor unit's capacity to provide many operating system-supported…
Q: Examining the similarities and differences between processes and threads should
A: Given: Threads have priorities. Thread Priority is assigned to CLR threads. Normal. Threads retain…
Q: Is it possible to prioritise a large number of jobs with the same importance?
A: Introduction: Many attempts have been made to satisfy business needs and convince company workers to…
Q: CD has more storage capacity than .DVD False True O
A: Compact discs, or CDs, offered many improvements over earlier storage technologies including…
Q: ch is also a bina ements. The tre esentation of bin the array indices
A:
Q: Loop is used to repeat a sequence of actions or statements many times. Simply describe the…
A: Dear Student, Differences Between For Loop and While loop is given below -
Q: Power-hungry components abound in gaming PCs. At its peak, how much power does it have?
A: Introduction: If you intend on building your own gaming computer, the first thing that should be…
Q: The DNS, including requests that are repeated, authoritative and root servers, and DNS entries, is…
A: DNS: DNS is the Internet's telephone directory, which is why it is so important. People use domain…
Q: What is the correct combination of function and parameter to create a pie chart in Matplotlib?
A: The correct answer for the given question is option c: Function = plot, and parameter = kind with…
Q: When using Windows 8 on a gaming machine that already has a video card installed and has room for a…
A: Given: You must create a gaming PC from scratch to ensure that it will satisfy your demands. You…
Q: The Internet is often portrayed as a cloud, but is this a true representation? Isn't the Internet…
A: Introduction: Third-party cloud providers provide cloud services. These service providers can…
Q: What sets it different from the Internet of Things? Where can you find apps for the Internet of…
A: Explanation: Internet of things? IOT is a network of physical items integrated with software,…
Q: If you have a gaming system with built-in video and an available PCI Express video card port, you…
A: Graphics card: A graphics card, also known as a video card, display card, graphics adapter, or…
Q: What is the Effective memory access time for a machine with a cache hit rate of 90%, where the cache…
A: The answer is in step 2
Q: Create a Visual Basic project to find the Perimeter and area of any triangular using the equation…
A: visual basic project to find perimeter and area of triangle using formula perimeter =a+b+c area =…
Q: Which of the lines of code below will create the following scatter plot, given the pandas dataframe,…
A: Correct Option is C
Q: Rational Unified and Classical Waterfall models are compared to determine which is superior.
A: Solution: Due to the waterfall model's sequential approach, software development is broken down into…
Q: Describe the Internet of Things (IoT) and the cloud computing revolution.
A: Cloud Computing and IoT are related by the Internet; therefore, let's first discuss the Internet.…
Q: * Satellite communication in LEO earth orbit mostly used for the following ?applications TV signal…
A: TV signal communication
Q: Interpret these two statements: number = 3 diary_str = "I ate %s cakes today" % number Which is/are…
A: STATEMENTS: (a) dairy_str becomes a string "I ate 3 cakes today" - CORRECT As we can see above (b)…
Q: The goal of Trace Requirements is to ensure that requirements and designs at different levels are…
A: The following solutions are
Q: Why aren't we able to use an object from the Parent Class in the Child Class and still have access…
A: Please refer below for your reference: We are not able to use an object from the Parent Class in the…
Q: An insurance company wants to know your thoughts on the most effective technique to get access to…
A: INTRODUCTION Access control – In essence, access control is a part of data security that specifies…
Q: This program inputs ten integers into an array (a) and then create a new array (b) that represent…
A: Let us see the answer below,
Q: Is it possible to prioritise a large number of jobs with the same importance?
A: Introduction: Numerous attempts have been made, on the part of many firms, to fulfil business needs…
Q: Eight input signals, each of bandwidth 4 kHz are timely multiplexed, quantized and binary PCM coded.…
A: The solution to the given question is:
Q: a java program - A Libary book rental syst
A: Program Approach: 1- As mentioned in the assignment library rental book system, created a…
Q: In the Amazon RDS which uses the SQL Server engine, what is the maximum size for a Microsoft SQL…
A: Asking for maximum size for a Microsoft SQL server instance with sql server express edition.
Q: Make clear what you mean when you use the phrase "internet of things." In what ways is the internet…
A: Answer: The Internet of Things links everyday objects to the internet or tells other phones what a…
Q: What type of transport layer protocol do you use for video streaming?
A: Start: One of the most critical jobs you have as a network administrator is to ensure that all of…
Q: The transactional and analytical approaches to data management are diametrically opposed.
A: Given: The goal of data management is to gather, store, and use data in a secure, effective, and…
Q: When someone refers to the internet as a "cloud," what exactly are they referring to? What use does…
A: Cloud Computing: The supply of infrastructure, platforms, and software-as-a-service through the…
Q: Locate the keyword that is used in the process of joining columns having the same column names but…
A: Given: Find the term that is used to link columns that have the same columns but distinct data…
Q: Rational Unified and Classical Waterfall models are compared to determine which is superior.
A: Answer:
Q: This program print all unique elements in an array of 10 elements. For example: The array elements…
A: The code needs to print all unique elements in array: lets analyse the given code: For i=1 To 10…
Q: Explain how the cloud can be scaled. We need to know how cloud computing is expanding.
A: Explain how the cloud can be scaled. We need to know how cloud computing is expanding.
Q: What are the responsibilities of a data scientist? If you want to be a data scientist, do you need a…
A: The above question is answered in step 2 :-
Q: Explain the idea behind an authentication challenge–response system in more detail. Why is this…
A: Challenge–response system Using passwords to protect databases in a client-server architecture is…
Q: How can people make positive changes to their health by making use of the internet? How does…
A: Answer:
Q: You are building a solution for a customer to extend their on-premises data center to AWS. The…
A: Given that, required a feature in AWS for dedicated speed to connect VPC.
Q: Is it feasible to build a single protocol that covers all of the difficulties that might arise while…
A: Different network devices can communicate with one another thanks to communication protocols. They…
Q: The resources sought by those who are stuck are made available to those who have been notified that…
A: Start: A deadlock occurs in an operating system when a process or thread enters a waiting state as a…
Q: Explain how the cloud can be scaled. We need to know how cloud computing is expanding.
A: Answer: cloud scalability is expanding or descending the IT resources as per requirement. This…
Q: the result of command (linspace(0.9.6.7))is:* 1234567 O6543210 O 01.63.2486.489.6 O 0134689 O…
A: Answer:- The correct option is , 0.00000 1.60000 3.20000 4.80000 6.40000 8.00000 9.60000
Q: The Internet is often portrayed as a cloud, but is this a true representation? Isn't the Internet…
A: Introduction: Cloud services are offered by third party cloud providers. These providers are able…
Q: The life cycle of a system can be represented by five methodical steps.What exactly are they?
A: Introduction: A secure SDLC contains five phases, which are as follows:-
Step by step
Solved in 2 steps

- In C language, write a simple substitution code for an alphabetic string. That is, declare a permutation of the 26 alphabetic characters i.e. char perm[] = “qjczieaungsdfxmphybklortvw” Now, given a message string e.g. char msg[] = “secret message to encode”; Replace all occurrences of ‘a’ with ‘q’ (since perm[0]=’q’) Replace all occurrences of ‘b’ with ‘j’ (since perm[1]=’j’) Replace all occurrences of ‘z’ with ‘w’ (since perm[25]=’w’)So that, the message is modified to “bicyik fibbqai km ixcmzi” This programme should only convert lowercase letters. Any input character that is not a lowercase letter should be left unchanged.Encryption is commonly used to disguise messageson the internet. A Caesar cipher performs a shift ofall of the characters in a string (based on their ASCIIvalues, see Table 2.1), e.g.h e l l o → m j q q tThe example shows a shift with a distance of 5characters, i.e. h(ASCII:104) → m(ASCII:109)Write a C/C++ program that asks the user to input aline of plaintext and the distance value and outputsan encrypted text using a Caesar cipher, with theASCII values range from 0 through 127. Useunderscores (ASCII: 95) to represent spacecharacters.Underscore characters should not be encrypted,and any character that is encrypted may notbecome an underscore. In this case, the charactershould be changed to the next character in theASCII table.The program should work for any printablecharacters.NB: No strings (datatype) or library functions maybe used.See Figure 2.1 for example output.If f(n) is the number of times that y=y+A[i]; is executed in the code segment below, which of the following is the correct big-Oh notation for f? y=0;for(j=0;j<n;j++) { i=n; while(i>0) { y=y+A[i]; i=floor(i/2); }} Group of answer choices O(n2‘) O(n) O(2n) O(nlog2n)
- The concatenation of strings s1 and s2, written s1+s2, modifies s1 by appending string s2 to it. Select one: True FalseConvert the following infix expression into postfix notation. (A*B+(C/D))-F (A+B)*C/ A*B+(C/D) Evaluate following prefix expressions /-AB*+DEF *^+A/BD-EFG /*-AB/DE**FGH Where, A=1, B=2, C=3, D=4, E=2, F=2, G=4, H=3Convert the following string from INFIX to PREFIX: (A+B)^(C-D^E) + (F+G)/H* +^+AB-C^DE / +FGH +AB^-C^DE / +FGH AB+CDE^- ^ FG+H/+ AB+CDE^- ^ +FGH/ (AB)+CDE^- ^ (FGH)+/
- Using Python PLY implement the RE to DFA conversion algorithm. Once the DFA is constructed, prompt the user for input strings and report "MATCH" if the string is accepted by the DFA and "NO MATCH" otherwise. Needs to take an input string. RENode.py, RELexer.py, REParser.py, RE.pyTrue or false set{(x,x2):x∈Z}canbeseeasafunctionZ→Q. set{(x2,x):x∈Z}canbeseeasafunctionZ→Q.z1 and z2 are integers and z1 < z2.Which of the below finds the sum of all numbers from z1 to z2 (both inclusive)? Lütfen birini seçin: a.n = z1 sum = 0 while n <= z2: sum += n b.n = z1 sum = 0 while n <= z2: sum += n n += 1 c.n = z1 while n <= z2: sum += n n += 1 d.n = 1 sum = 0 while n <= z2: sum += n n += 1 e.n = z1 sum = 0 while n < z2: sum += n n += 1
- z1 and z2 are integers and z1 < z2.Which of the below finds the sum of all numbers from z1 to z2 (both inclusive)? Lütfen birini seçin: a.n = z1 sum = 0 while n <= z2: sum += n b.n = z1 sum = 0 while n <= z2: sum += n n += 1 c.n = z1 while n <= z2: sum += n n += 1 d.n = 1 sum = 0 while n <= z2: sum += n n += 1 e.n = z1 sum = 0 while n < z2: sum += n n += 1 can u help me ?)Write script program if this function such that x0=2 n=( 4 8 16 20)A list of positive and negative numbers are in A2 through A400, and the square root of the absolute value is needed for each cell. Which function typed into B2 and copied through B400 will provide this information? a. =A2^(1/2) b. =SQRT(A2) c. =SQRT(ABS(A$2)) d. =SQRT(ABS(A2))

