Sakhak / k 03 nucl when 20 you read 210
Q: anagement - Write a C program that demonstrate the suspend
A: Lets see the solution.
Q: When we make data-driven decisions there is always a risk we may be wrong. In binary situations, we…
A: A false positive means that you receive a positive test result when you expect a negative result.…
Q: TODO 10.1 reshaped_array = print(f"reshaped_array output: \n {reshaped_array}")…
A: Python: Python is a high level general purpose programming language. It was developed by Guido Van…
Q: 1. Use the bubble sort to sort 6, 2, 3, 1, 5, 4, showing the lists obtained at each step. Justify…
A: Given To know about the bubble sort .
Q: Define timing parameters: tWR, tWC, tCO, tRD, tRC.
A: The question has been answered in step2
Q: Mention 10 examples of daily life, the use of semaphores (related to operating systems).
A: Introduction: When a thread is finished utilising a token, it may release it by executing semaphore.…
Q: ackage edu.umsl; interface Jumpman { void jump(); default void swingHammer() { // Code to swing…
A: The answer is given below.
Q: Write an application to test the HuffmanTree class. Your application will need to read a text file…
A: The answer provided below has been developed in a clear step by step manner.
Q: what are the benefits associated with high broadband access connections? What do users like most…
A: Introduction: Fast download rates and the availability of massive amounts of data are the primary…
Q: The following is a list of what I consider to be the four most important aspects of continuous event…
A: The above question is solved in step 2 :-
Q: Answer in Python Code only Tom got a new sequence A1, A2,..., AN. He does not like the order wants…
A: I have written the code below:
Q: Question 9 Here are 3 binary numbers: 1110101 Working in binary, (a) add together the two smaller…
A: - We have to work with the binary numbers provided.
Q: Give an overview of the principles behind predictive analytics and illustrate how the method may be…
A: Prescriptive analytics predicts outcomes using comparable modelling frameworks and simulates several…
Q: Question 8 A binary number has 8 digits and is to be converted to base 10. (a) Convert the binary…
A: 1) Binary number is a number system where a number is represented by using only two digits (0 and…
Q: How do I print the Uppercase letters without the commas?
A: After updating the code, I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT…
Q: Define - ULP
A: ULP: In computer science and mathematical examination, the unit in the last place or unit of least…
Q: 2. Use the insertion sort to sort 6, 2, 3, 1, 5, 4, showing the lists obtained at each step. Justify…
A: Introduction Insertion Sort: The simplest sorting algorithm known as insertion sort works similarly…
Q: disk configuration
A: Given :- In the above given question , the statement is mention in the above given question Need…
Q: List various flags in the status Register.
A:
Q: Define - Moore's Law
A:
Q: Write a C program called bitflip to run on ocelot which will flip bits in an unsigned integer using…
A: #include <stdio.h> #include <stdlib.h> int main() { unsigned int input, result,…
Q: 4. 5. that class. ...is an anomaly or error that occurs during the execution of a program a.…
A: Here below we will give the answers of the above mcqs.
Q: Data buses, address buses, and control buses all function autonomously of one another.
A: Introduction: A bus is a kind of communication link that connects two or more devices together. It…
Q: Input/Output - Write a C program to demonstrate file and folder copy
A: I give the code in C to copy files.
Q: What do you think are the biggest differences between the internet and a traditional phone network?
A: The key distinctions between a phone system and the Internet are: 1. Unlike the phone system, which…
Q: Java 1. Need a list of 30 words, phrases and company names commonly found in phishing messages.…
A: Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: Write an application to test the HuffmanTree class for java. a. The application will need to read a…
A: The answer provided below has been developed in a clear step by step manner.
Q: How can collisions in hash tables be avoided? How can they be stopped, and what causes them? If it's…
A: Given: The issue of collisions in hash tables and how an example helped to overcome the problem.
Q: What is the use of PC register?
A: In this question we need to explain the uses of Program Counter (PC) register.
Q: Can minors less than 16 years old use the internet safely, given the current regulations? If this is…
A: introduction: No, the laws that are now in place do not provide enough protection for children under…
Q: Define - ULP
A: This question is concerned with ULP.
Q: The following statement is supposed to print the integers from 1 to 10, but it contains an error.…
A: A loop is used to perform a certain task repetitively until a particular condition is reached.
Q: What sets the Internet apart most from the World Wide Web?
A: The Internet is a network consisting of many computers that are connected to one another all over…
Q: Create another class called WordGUI that will be a complete JFrame with a menu bar and menus. There…
A: import javax.swing.*; import java.awt.event.*; import java.io.*; Public class FileChooserExample…
Q: How can collisions in hash tables be avoided? How can they be stopped, and what causes them? If it's…
A: INTRODUCTION: An instance of a collision in the hash table: Collisions in hash tables occur when the…
Q: What is DGC ? And how does it work?
A:
Q: How can collisions in hash tables be avoided? How can they be stopped, and what causes them? If it's…
A: Introduction: The collision issue in Hash tables is illustrated with an example When one or more…
Q: The data is maintained in a single container called a LinkedList because of the way our hash map was…
A: Introduction Utility Mapping: A utility map displays the location and identification of underground…
Q: What is meant by register file?
A:
Q: Which firewall configuration is currently most popular in businesses? Why? Explain.
A: INTRODUCTION: FIREWALL: A firewall is a network security device that monitors and filters traffic…
Q: What are the steps involved to make work a RMI program ?
A: Introduction: In this question, we are asked the steps to make work a RMI program
Q: 1. Write a SQL query to list the names all employees and their address who work for the department…
A: Please find the answers in the following steps.
Q: Assignment to Implement a Lexical Analyzer for simple C statement that can Analyze/Detect the…
A: Program: #include <stdbool.h> #include <iostream.h> #include <string.h> #include…
Q: What is the basic principle of RMI architecture ?
A: There are three layers in the RMI system: Client-side stubs (proxies) and server-side skeletons make…
Q: What is the most important function a firewall carries out? I'm currently developing a programme to…
A: Introduction: An essential purpose of a firewall is to restrict communication that carries…
Q: Question 7 A 4-digit binary number has 2 zeros and 2 ones. (a) Convert the binary numbers 11101 and…
A: We are given two binary numbers and asked to convert them into base 10 and also add them in base 10…
Q: how to use and gain access to cloud-based software and services.
A: INTRODUCTION: Hosting Network services and applications is made possible by cloud-based software. By…
Q: Based on Figure 4, write an SQL coding for the following questions. Table : CUSTOMER CCode 10010 Abu…
A: We need to find the query of the above problem. See below steps.
Q: What is the use of CallableStatement ? Name the method, which is used to prepare a…
A: SQL stands for Structured Query Language.
Q: Perform the following arithmetic operations in the 2's complement system. Use 8-bit numbers…
A: To convert the given number into its 2's complement form we follow the following steps: Step1:…
Construct PDAsfor the following:
L = {a^kb^2k/ k >=0}, push aa when you read an a
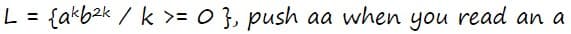
Step by step
Solved in 2 steps with 1 images

- .c## Write a Console Application that reads two integers, determines whether the first is a multiple of the second and displays the result. [Hint: Use the remainder operator.]c## please Write a Console Application that reads two integers, determines whether the first is a multiple of the second and displays the result. [Hint: Use the remainder operator.]Racket code only please - primeTest It takes as input any positive integer n and returns true if the absolute value of the polynomial 8n2 − 488n + 7243 is a prime number. For example, the invocation (primeTest 5) should return true. - primeTestSeq This takes two arguments, a low bound and an upper bound. It determines what percentage of the integers between the lower bound and the upperbound are, according to primeTest, a prime number. For example, the invocation (primeTestSeq 1 60) should return 100.
- Nice Number Programming: Nice program ask user to enter three integers from keyboard (java console), the three integers represent left bound, right bound and arbitrary digit 'm', where left bound is less than right bound. Program should print all nice numbers in the given range that doesn't contain digit 'm'. The number is nice if its every digit is larger than the sum of digits which are on the right side of that digit. For example 741 is a nice number since 4> 1, and 7> 4+1. with digit m=2. Write a complete program in Java that Call only One method (niceNumbers method) that will print all nice numbers excluding a given digit 'm' that also entered by user?Write a codeCode which accept four inte ger inti loop And divisible by 3 and 5
- please write a code for that(Phone key pads) The international standard letter/number mapping found on the telephone is shown below:Write a program that prompts the user to enter a lowercase or uppercase letter and displays its corresponding number. For a nonletter input, display an invalid input message. Here are sample runs: Welcome to PhoneKeypad Mapping Program by Mrs Jackson Enter a letter from phone keypad: 2 ** INVALID INPUT !! ** ---------------------------------------------------------------------------------------------- Welcome to PhoneKeypad Mapping Program by Mrs Jackson Enter a letter from phone keypad: F *The corresponding letter is 3True or False The order of operations dictates that the division operator works before the addition operator does.
- please name this cards.py. You may use the following code in your program: import random SUITS = "♠ ♡ ♢ ♣".split()RANKS = "2 3 4 5 6 7 8 9 10 J Q K A".split() def create_deck(shuffle=False): """Create a new deck of 52 cards""" deck = [(s, r) for r in RANKS for s in SUITS] if shuffle: random.shuffle(deck) return deck This code creates a random deck of cards (each card is a tuple consisting of a rank and suit). You are to ask the user how many 5-card hands to play and will keep track of the following poker hands. You will need to reshuffle the deck as many times as necessary to get the required number of hands. An example run of the program is as follows. Enter the number of hands to deal: 10000Hand % of Hands Hands of Type2 of a kind 41.290% 4129 3 of a kind 1.970% 197 4 of a kind 0.010% 1 2 pair 4.860% 486 Full house 0.150% 15 Flush 0.220% 22 If you deal enough…c code needs to ask user for a number sfasddasfasplease code in pythonis_phone_num: This Boolean function takes a string and returns True if it is in the formatddd-ddd-dddd, where d is a digit, False otherwise. Example calls:is_phone_num('123-456-7890') --> Trueis_phone_num('123-4556-7890') --> Falseis_phone_num('(123)456-7890') --> False

