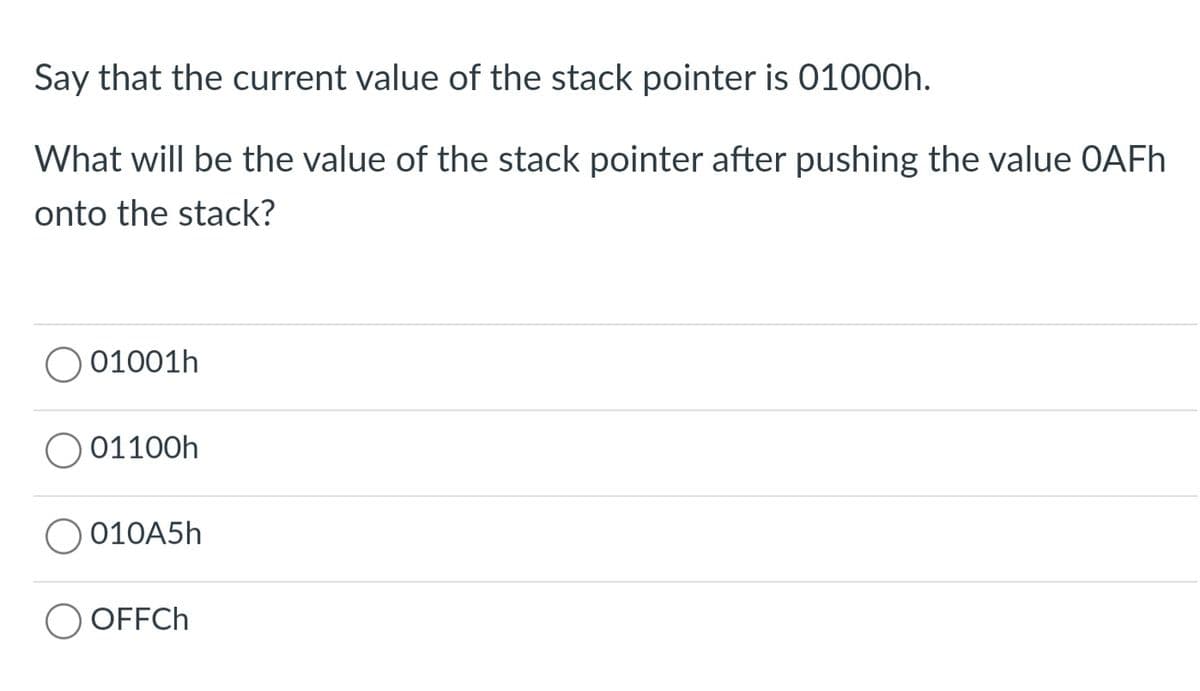
Say that the current value of the stack pointer is 01000h. What will be the value of the stack pointer after pushing the value OAFh onto the stack? 01001h 01100h 010A5h OFFCh
Q: Both ScoutSuite and Pacu are cloud-based security systems. What makes them apart? What methods may…
A: Cloud security requires adjusting some previous IT practices, but it has become more essential for…
Q: Write a program that prompts the user to input an integer and then outputs both the individual…
A: Note :- As per our guidelines we are supposed to answer only one question. Kindly repost for the…
Q: The biasing value in IEEE 64 bit (Double precision) floating point representation is
A: IEEE 64 bit double precision floating point representation conains: 1 : sign bit 11: exponent bits…
Q: What are the most significant parts of system development that need to be stated and explained?
A: INTRODUCTION: The process of conceiving, creating, testing, and implementing a new software…
Q: What are some of the goals of the authentication process? Is it feasible to weigh the merits of…
A: Given: Authentication is the a process of making sure that a user or piece of information is who…
Q: What is the final value of q after all statements are executed? Boolean q; int a = 1; q = (a==3);
A: The Solution for the following question is as follows:
Q: What are some of the reasons that have led to the development of computer security into the…
A: These elements have led to the transformation of computer security into modern information security.…
Q: import java.beans.Statement; import java.sql.Connection; import java.sql.DriverManager; import…
A: Given:
Q: Make an algorithm and flowchart of the following problem set. 2. Draw a flowchart that display the…
A: Flowchart is a method to depict an algorithm in form of a diagram.
Q: Q1 /write c++ program function to read five number and find summation of only number less than 10?
A: Input 5 numbers in an array. Then check if any number is less than 10, sum it.
Q: now available use various forms of artific
A: Artificial intelligence (AI) is intelligence shown by machines, instead of the normal intelligence…
Q: 4. Draw a flowchart which will read and print the names and individual scores of 100 students for a…
A:
Q: What is the value of the median-of-3 for the following list. [80, 47, 41, 21, 40, 68, 78, 18, 75,…
A: Find the required python code and sample output given as below :
Q: An input image has the size of 140x140 and we use a filter (kernel) with the size of 20x20. We then…
A: Given: Input image size(WxH) = 140x140 Filter kernel size(F) = 20x20
Q: Explain what application virtualization is a
A: Q)Explain what application virtualization is? Answer: Application virtualization is technology that…
Q: Match the condition indicated when the following status flags are set. Carry [Choose ] result is…
A: There are various flags which gets set based upon the results of the instructions executed.
Q: Stack operation in x86 is a O LIFO (Last-In, First-Out) FIFO (First-In, First-Out) operation.
A: What is LIFO? LIFO stands for Last-in, First-out. It is a method in data structures where the…
Q: 3 per minute and each is expected to use the software for 20 minutes (1 student stops using the…
A: The answer is
Q: If register AL contains the value 0x 89 and register AH contains 0x74, what is the hexadecimal value…
A: Here is the explanation about AX:
Q: When it comes to the capacity to work together, has cloud computing had an impact?
A: Introduction: Cloud computing is the delivery of numerous services through the Internet. Data…
Q: Rabenstein code was used to send a message with 4 information bits, you receiv
A: The answer is
Q: Q21. Make two separate plots of the function f(x) = 0.6x² - 5cos(x) + sin(x²) + 3; the first plot…
A:
Q: What steps can I take to reduce the risk that a data breach may cause my private information to…
A: Please find the detailed answer in the following steps.
Q: What's the difference between ScoutSuite, Pacu, and Powler, three popular cloud security solutions?…
A: The Scout Suite is a multi-cloud security auditing solution that is open source and enables security…
Q: Assuming that a 4-bit ADC channel accepts analog input ranging from 0 to 5 volts, determine the…
A:
Q: Q1: Distinguish between Short jump and Long Jump of 8051 Micro Controller.
A: Many microcontrollers have this option. One is an instruction that is short and fast. That is a…
Q: What other types of AI are there? Give instances of how artificial intelligence domains might be…
A: Introduction: The processes involved in human intelligence may be emulated by computers using the…
Q: When it comes to Linux, what are the kernel's key responsibilities in the operating system?
A: Abstract The Linux kernel is the most significant component of a Linux operating system since it is…
Q: What exactly are some of the goals of the authentication process? Compare and contrast the…
A: Authentication is used when a server wishes to determine precisely who is accessing its data or…
Q: Define a struct menuItemType with two components: menuItem of type string and menuPrice of type…
A: editable source code: #include <iostream> #include <string> using namespace std;…
Q: Given the following Date class public class Date { private int year; private int month; private int…
A: Answer: date d=new Date(2020,20,9);
Q: What are some of the reasons that have led to the development of computer security into the…
A: The following elements have been essential contributors to the development of computer security into…
Q: Which of the following statements assigns a random integer between 25 and 60, inclusive, to rn? int…
A: The solution to the given problem is below.
Q: In your perspective, what function does the internet serve to serve in the lives of persons who have…
A: They have the following alternatives on the internet: Visually impaired or blind people may benefit…
Q: A user enters a list of positive integers until it enters -1 which marks the end of input and wants…
A: The program is written in C Programming. Check the program screenshot for the correct indentation.…
Q: Directives are commands that are recognized and acted upon by the assembler but are not part of the…
A: Assembly code is code that is much more human readable than machine code. Machine code is just zeros…
Q: a machine is 30 bit way block set Asso
A:
Q: What steps can you take to guarantee that the code will be submitted into the source control system…
A: Committers should have sufficient privileges to push branches to a remote repository and set their…
Q: Make an algorithm and flowchart of the following problem set. 3. Draw a flowchart that calculates…
A: ALGORITHM: Declare the required variables. Start the loop by taking the value of loop variable from…
Q: ple of Data Analytics. Explain the variables in your example describing the Independent and the…
A: Introduction: Below the variables in your example describing the Independent and the Dependent…
Q: Consider the scenario in which one computer sends a packet to another computer by using the…
A: The issue at the transport layer concerns the exchange of packets between two computers. A package…
Q: What are the key differences between authenticating a distant user and authenticating a local user?…
A: What is the difference between remote and local user authentication? Which one was the most…
Q: Question 5 a) Timmy just starts to watch a video on YouTube. After 0 seconds, the screen turns off…
A: YT video turn off in θ seconds. Here θ = 14 sec And motion estimation of full, window, logarithmic,…
Q: Why do we need authentication in the first place? Analyzing the advantages and disadvantages of the…
A: Introduction: Authentication identifies users who access a system, network, or device. User identity…
Q: How are authentication and authorization handled in the cloud?
A: Given: A "cloud provider" is a term that refers to an independent company that offers a platform,…
Q: Make an algorithm and flowchart of the following problem set. 1. Draw a program that display the…
A: Dear student, you have not mentioned any programming language name here so, I am using C language to…
Q: A GSM system uses 124 channels and each channel is divided into 8 time slots. What is the maximum…
A: GSM uses a combination of both TDMA and FDMA techniques. The FDMA element divides the assigned…
Q: 1. Use MATLAB to plot direction fields for the following: a. y' = xy. b. y' = 2y(3-y). c. y' =…
A: We need to use Matlab to plot direction fields of given equations.
Q: How might regions and availability zones be used to improve application resilience, availability,…
A: Given: You are able to develop and run applications and databases that seamlessly transition between…
Q: Using matlab by the use of the derivative property discover the Fourier transform of the following…
A: The Answer is given below
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Can you explain in detail, line by line, what the attached algorithm is doing? I need further understanding. For further clarification the prompt asks the following: Write an algorithm Replace that takes a stack and two items. If the first item is in the stack, replace it with the second item, leaving the rest of the stack unchanged.TRUE or FALSE? Please answer the following question and state the reason why: Thank you! In a Dynamic Stack, the pointer top stays at the head after a push operation. During a Pop operation in Static Stack, the elements are being moved one step up. In a dynamic implementation of stack, the pointer top has an initial value of null. STL empty function will yield a value of true if the stack has elements.So what happens if a stack resource can't be created?
- TRUE or FALSE? Answer the following question and state the reason why: In a dynamic stack, the node that was popped is deleted. In a dynamic stack, the pointer top stays at the head after push operation. STL function top returns a reference to element at the top of the stack. STL empty function will yield a value of true if the stack has elements.A stack has following variables initialized, answer question 5 &6 using these values int size = 7; int top = —1; int [ ] arr = new int [size] ; Q5. What will be value of the top variable when the stack is empty? Q6. What will be value of the top variable when the stack is full?If a resource in a stack cannot be created, what happens?
- Write a program that inputs a list of numbers already stored in a stack STACK and sorts them, making use of a temporary stack TEMP. The sorted list of numbers should be made available in STACK.A stack is very useful in situations when data have to be stored and then retrieved in the —- order. A) same B) reverse C) ascending D) descendingSuppose that stack is an object of type stackType<string> and six elements are pushed in an initially empty stack.a. What is the value of stack.top?b. What is the index of the last element pushed in stack?c. Write the statement that outputs the top element of stack.d. Write the statement that adds "StacksAndQueues" to stack.
- write a function that takes a pointer to the top of a stack <double> and creates and returns a new stack double where the new stack contains all nodes from the original stack with data == 0 c++Suppose you have a stack with a maximum size of 1000 elements and you want to perform the following operations: Push 500 elements onto the stack. Pop 200 elements from the stack. Push 800 elements onto the stack. Pop all remaining elements from the stack. What is the final size of the stack after performing all these operations?The following operations are performed on a stack:PUSH A, PUSH B, POP, PUSH C, PUSH D, POP, PUSH E, POP, POP, PUSH FWhat does the stack contain after the PUSH F?a. Fb. A B C D E Fc. A C Fd. A Fe. none of the above.

