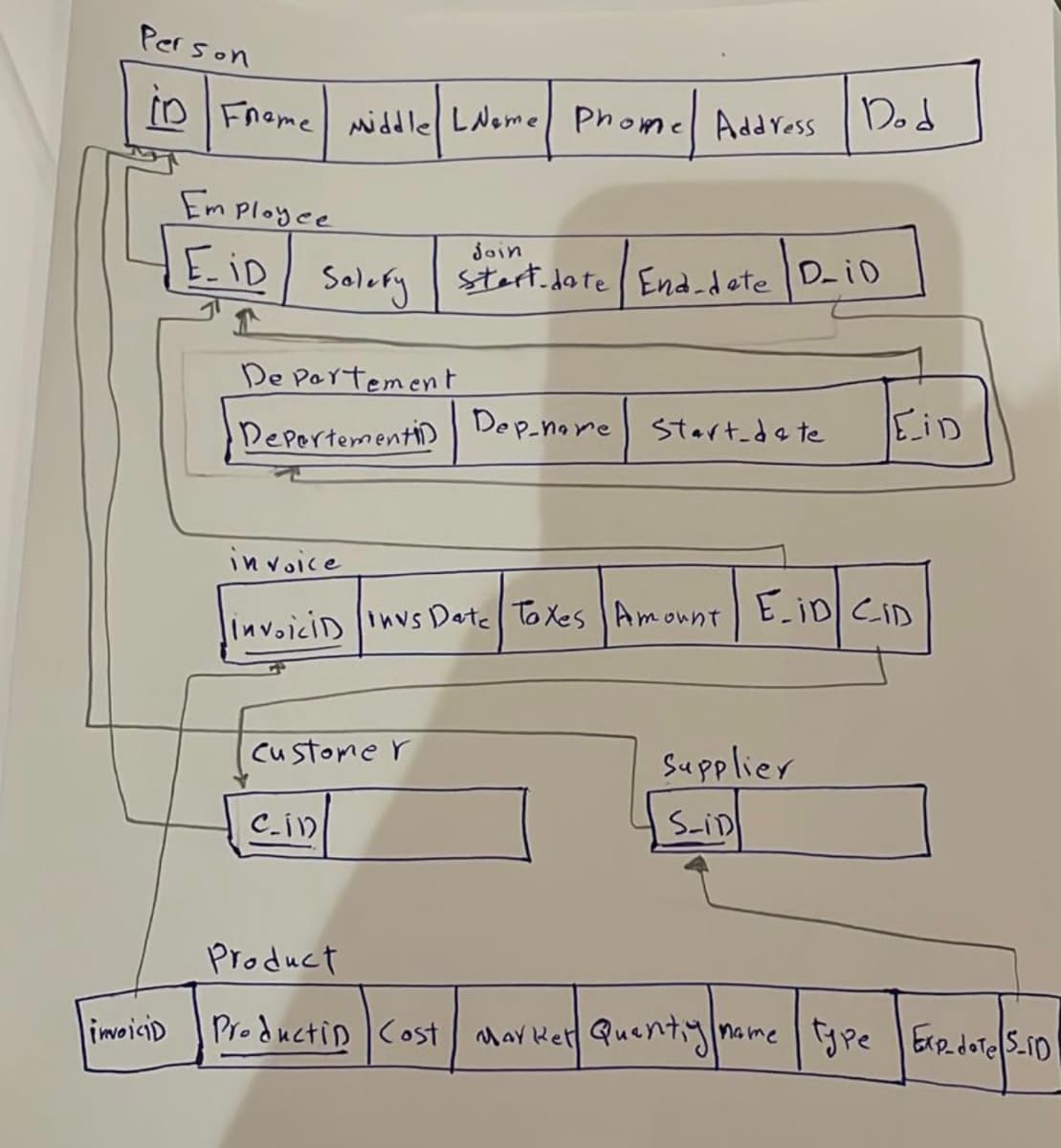
Schema Implementation( create table and insert )
Q: As more computers connect to the internet, network security becomes increasingly important. Discuss
A: Network security becomes more crucial as many machines connect to the Internet. The potential for…
Q: Java programming-see attached
A: Ask the user to enter a word or phrase. Create a tool to separate vowels from the input. Remember…
Q: Again, I'll ask: how much space does a computer require?
A: What is computer: A computer is an electronic device that processes data and performs tasks based on…
Q: The development of TPS utilising Android Studio. The SQLite database browser displays the user's…
A: The development of a Transaction Processing System (TPS) using Android Studio involves creating a…
Q: What differences exist between web-based and conventional software development?
A: Software development alludes to the method involved with making PC software or applications. It…
Q: 200 workstations and four servers are connected to switches through a LAN. You need to reduce…
A: Any Local Area Network (LAN) communication protocol must include broadcast packets. They generally…
Q: The potential of the Internet to support two distinct categories of applications remains uncertain.…
A: The potential of the Internet to support two distinct categories of applications can refer to…
Q: Given the choice between the classic and iterative waterfall models, which one would be preferred…
A: The classic waterfall model is a linear sequential life cycle model. It is a very straightforward…
Q: How reliable are sentiment analysis outcomes? I hoped you could explain the standard procedure for…
A: Sentiment analysis is a natural language processing (NLP) technique used to determine the sentiment…
Q: Examine the industries that are utilising web-based technology and identify the challenges that…
A: Web-based technology is widely utilized across various industries, enabling businesses and…
Q: What would happen if an email provider checked users' inboxes?
A: In today's digital age, email has become an indispensable tool for communication, both personal and…
Q: This inquiry pertains to an evaluation of the relative merits and demerits of the prevalent server…
A: Server operating systems play a critical role in managing and coordinating various resources within…
Q: Solaris is an operating system designed for servers that boasts a range of features. These features…
A: The vigorous security actions of the Solaris operating system are intended to safeguard data and…
Q: Implement a binary tree by utilising the chapter's recursive method. In this technique, each node is…
A: A binary tree allows each node to have a maximum of two children, referred to as the left child and…
Q: es a packet with destination adc
A: The answer is
Q: Justify and provide examples of the use of centralised software modules in a distributed system. How…
A: In distributed systems, the use of centralized software modules can bring various advantages and…
Q: Define a. Tuscan Order b. composite order
A: In the field of architecture, various stylistic elements, known as 'orders', are used to classify…
Q: Digital transmission via copper telephone lines and other media is governed by ISDN standards. Or…
A: A set of communication guidelines known as an ISDN, or Integrated Services Digital Network, enables…
Q: Analyse the utilisation of information systems by a variety of businesses.
A: Information systems play a crucial role in today's business landscape, enabling organizations to…
Q: Discuss the objectives of software engineering prototyping.
A: What is software engineering: Software engineering is the systematic approach to designing,…
Q: Descriptive models' characteristics are listed
A: Descriptive models are analytical tools used in various fields to understand and describe the…
Q: Could you please provide a comparative analysis of the primary distinctions between the two most…
A: The two most prevalent server operating systems currently are Microsoft Windows Server and Linux.…
Q: What are different operations available in queue data structure?...
A: A data structure is a way of organizing and storing data in a computer system to efficiently perform…
Q: Consider a 32-bit computer with the MIPS assembly set, that executes the following code fragment…
A: Hi. Check below for your answer.
Q: In cases where the data size exceeds the cache capacity, a write buffer is utilised to facilitate…
A: In computer systems, caching is an essential technique used to improve memory access times and…
Q: How does the concept of Big-O notation aid in understanding and analyzing the efficiency and…
A: In this question we have to understand how does the concept of Big-O notation aid in understanding…
Q: Make a code that reads a statement entered by the user and produces it with the characters for each…
A: code that reads a statement entered by the user and produces it with the characters for each word in…
Q: is article undertakes a comparative analysis of the characteristics, pricing, and user-friendliness…
A: In today's digital age, wireless routers play a crucial role in providing internet connectivity to…
Q: In the event that the central processing unit (CPU) is in the process of transferring a block from…
A: CPU, Write Buffer, and Cache Interaction The Central Processing Unit (CPU), write buffer, and cache…
Q: Describe four pros and cons Agile & waterfall
A: Software development methodologies are approaches used to manage the process of creating software.…
Q: 1. Does the technology you are implementing / deploying affect the char answer 2. What is the…
A: 1. Technology plays a very important role in implementing/deploying the change complexity.…
Q: This section compares LoT with M2M using a health band. M2M vs. IoT.
A: The linking of devices is the basis for the notions of machine-to-machine (M2M) and the Internet of…
Q: You are familiar with the basic principles of social media. To what extent does cloud computing…
A: Cloud computing has revolutionized the way businesses and individuals utilize technology by…
Q: What specifically does the waterfall approach to SDLC cover? This location has been suggested as…
A: Software Development Life Cycle (SDLC): The Software Development Life Cycle (SDLC) is a systematic…
Q: The most basic form of peer-to-peer networks involves the interconnection of two computers either…
A: The primary advantage of a peer-to-peer network is that it allows computers to share resources with…
Q: Is it feasible for the Internet to potentially facilitate various initiatives? What are the notable…
A: The Internet, a global network of interconnected computers, has become an integral part of our…
Q: Implement the counter increment before returning to the loop's beginning. After completing these…
A: In this problem, we are tasked with implementing a counter control loop in MIPS assembly language.…
Q: There exists variability among compilers and interpreters.
A: Understanding Compilers and Interpreters Compilers and interpreters are key components in the world…
Q: Discover which industries rely on web engineering and the obstacles they face in developing and…
A: Web Engineering: Web engineering is a discipline that encompasses the design, development, and…
Q: Network administration and troubleshooting apps and tools are user-friendly. Explain how you would…
A: Network performance evaluation involves assessing various metrics such as bandwidth, latency,…
Q: Kindly provide me with the paragraph you want me to summarise.
A: The discipline identified as Natural Language Processing (NLP) encompasses a extensive choice of…
Q: why is endpoint security so important to an organization?
A: Endpoint security plays a crucial role in safeguarding an organization's information and systems. By…
Q: This inquiry pertains to the comparative analysis of the salient features of the two preeminent…
A: An operating system (OS) is a program on a computer that runs everything else. A boot program loads…
Q: The two most recent operands are popped in the postfix expression evaluation example whenever an…
A: Let's consider a case study to exemplify the significance of swapping the order of operands when…
Q: List various software possibilities, including conventional and online development.
A: Traditional software development methods naturally involve a well-disciplined, linear method. These…
Q: Does the following page reference string: 1 2 3 4 2 1 5 6 2 1 2 3 7 6 3 2 1 2 3 6 suffer from…
A: Belady's anomaly, also known as the FIFO anomaly, refers to a situation where increasing the number…
Q: Is it probable that the utilisation of mobile applications will surpass that of internet usage?…
A: What is Mobile: Mobile refers to the ability to be easily carried or accessed while on the move,…
Q: Given the database schema below, write a relational algebra expression to get the count of records…
A: A procedural query language known as "relational algebra" accepts relation instances as input and…
Q: This paper aims to provide an overview of the different software acquisition processes, encompassing…
A: Off-the-shelf or specially built software installed and used on local hardware is the mainstay of…
Q: The advent of spreadsheets solidified the personal computer's status as a fundamental instrument for…
A: The emergence of spreadsheets played a pivotal role in establishing personal computers as essential…
Step by step
Solved in 5 steps with 9 images

- Question text4. Data value tool is used to enforce constrains to enter specific data type in excel cell (for example only to enter number).Select one:a. False b. TrueQuestion text5. Area of the chart that graphically displays the data being charted.Select one:a. PivotTable b. Plot area c. Data marker d. Data label6. ______________ is represents a data point or value that originates from a worksheet cell.Select one:a. Legend b. Data marker c. Data series d. Data labelQuestion text7. Built-in tool in excel which helps you out to summarize selected rows and column of data in a spreadsheetSelect one:a. PivotTable b. Sparklines c. PivotChart d. Plot areaLili Company 1 (Use C programming language and struct)Lili has a company, so it has a lot of employees.However, many of Lili employees have changed, resigned, and retired, causing the databasethat Lili has not synchronized properly. For that reason, Lili asks for your help to helpher make a list of Lili employees.Each employee has 3 attributes:• Name (max 20 character)• Gender (Laki-laki / Perempuan)• Division (Management / Accounting / HRD)There are several things you can do on the Lili database :1. Add EmployeeIn the add employee feature, the new employee will be after the old employee (ifall positions are full). Because Lili does not like to have employees who have thesame name, if there are employees who have the same name, the employee will notbe accepted to work at Lili’s company. New employees will always fill the leftmostplaces in the database to get a large salary.2. Change PositionThe employee’s position determines the employee’s salary, if the employee is in thefirst…uint16_t data = wiringPiI2CReadReg16(adc, 0x00); low = (data & 0xFF00) >> 8; high = (data & 0x00FF) << 8; value = (high | low)>>4; return value; I know this stables the value some how but how and why
- myBytes BYTE 10h,20h,30h,40hmyWords WORD 8Ah,3Bh,72h,44h,66hmyDoubles DWORD 1,2,3,4,5myPointer DWORD myDoublesUse html, php and Mysql to design a Library Managment web based System The system should be able to do the following:1) Add/Remove/Edit book2) Search Catalog3) Register new account/ cancel membership4) Check-out book5) Reserve book6) Renew a book7) Return a book Three main users for the system:1) Librarian2) Member3) SystemC1. Create a sequence diagram for the use case ‘Create New Online Library Account’ for a library system. The sequence of steps to carry out this use case is following: The librarian request the system to create a new online library account The librarian then selects the library user account type The librarian enters the user’s details The user’s details are checked using the user Credentials Database The new library user account is created A summary of the of the new account’s details are then emailed to the user
- Database homework_1SCENARIO A manufacturing company produce equipments and sell them. The company needs a system to manage stock operations. It is explained below. Equipments are manufactured by using parts. Name, manufacturing date, current status of manufacturing must be known. Some of the equipments must be tested.We want to define all parts with their name, description and type. Only the defined parts can be bought. Once parts are bought, they are located into shelves in warehouses. Each physical part uniquely identified with number. We want to know when each part is bought. Each bought part may have different warranty period. We have to use the bought part in manufacturing by taking this into account.Warehouses are located in different part of the company. Size, type of the warehouses may be different. Each parts can be bought from same or different suppliers. We want to know in which city they are located. Also for how many years we are working with each supplier. We also give…DescriptionARENA Game System: ARENA is a multi-user, Web-based system for organizing and conducting tournaments. ARENA is game independent in the sense that organizers can adapt a new game to the ARENA game interface, upload it to the ARENA server, and immediately announce and conduct tournaments with players and spectators located anywhere on the Internet. Organizers can also define new tournament styles, describing how players are mapped to a set of matches and how to compute an overall ranking of players by adding up their victories and losses (hence, figuring out who won the tournament). To recoup their operational costs, organizers can also invite potential sponsors to display advertisement banners during games.Create a class diagram for the Arena Game System based on your use-case diagram that embodies the primary classes. This should be a high-level class diagram with the important objects and their relationships. Make sure to include properties and behavior (high-level) for the…Web technology Question: Professor don't reject this....I need this answer otherwise I will report to administration....please answer it according to asked question. Q.No.2. Suppose there is a MySQL database named MyDatabase, the name of database server is DatabaseServer, User Name for the database server "Ghazi Messam" and Password is “1121” There is one table named tbl_Projects (ProjectSID, ProjectTitle, ProjectSupervisor,CellNo,Email). As project title is: Student Registration form As project supervisor is: Ghazi Messam As cell no: 03137025001 As Email is: ghazimessam@gmail.com You are required to design a HTML page to get the value for each of these attributes. Then finally post the data to next page and store the input data to database. Add Screen Shot of Creating database, Database Table and Sample Data.
- Create 3 new users (provide screenshots for each): Name: Thomas Jefferson Username: thomas Password: Monticello Name: Abraham Lincoln Username: abe Password: 4score&7years Name: Benjamin Franklin Username: ben Password: Early2bedEarly2rise b. Create 3 new groups: presidents (members: thomas, abe) continental_congress (members: thomas,ben) us_currency (members: thomas,ben,abe)uint16_t data = wiringPiI2CReadReg16(adc, 0x00); low = (data & 0xFF00) >> 8; high = (data & 0x00FF) << 8; value = (high | low)>>4; return value; I know this stables the value some how but how and why Please give explanationA Web service is a software system designed to support interoperable machine-to-machine interaction over a network. It has an interface described in a machine-processable format. Select a current healthcare database software and describe its application in healthcare databases. Include references.





