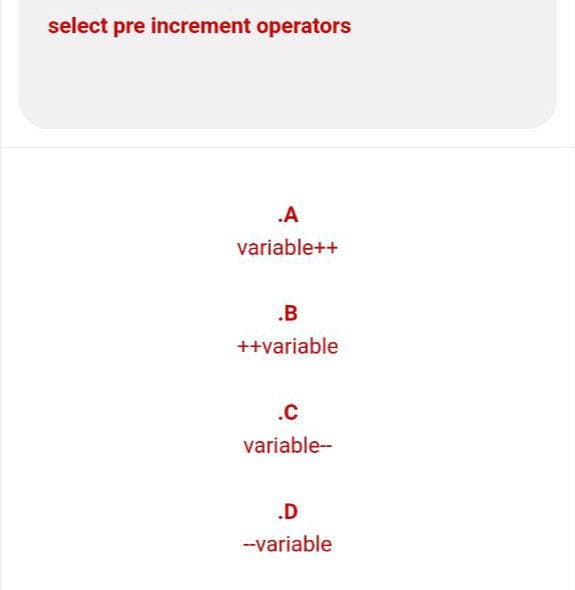
select pre increment operators .A variable++ .B ++variable .C variable-- .D --variable
Q: Create a program in C++ that accepts sales for the week ( Monday - Friday ) and display the highest…
A: C++ Program: #include <iostream>using namespace std; // function for lowest Salesfloat…
Q: What is the most important mechanism that database designers can employ to influence database…
A: Introduction: Database designers utilise many mechanisms to impact database performance.…
Q: It's important to know the four essential components of every computer.
A: The desktop computer consists of the computer system unit keyboard, mouse and the monitor. The…
Q: Twisted pair cable and fiber-optic cable have significant differences (at least three).
A: Introduction: The diameter of twisted pair cable is significantly bigger than that of optical fibre…
Q: The basic objective of software engineering, if it were to be condensed, how would it look? What led…
A: Answer: Software configuration refers to the process of describing the architecture, components,…
Q: How Do We View The Patches And Hot Fixes That Have Been Installed On Our Computer?
A: Introduction: We are all aware that the patch is a piece of software that, when loaded on a…
Q: Describe the advantages of the deep web for firms that rely on information technology.
A: Sections of the internet that are not accessible by traditional search engines like Google, Yahoo,…
Q: The most often used two technologies in wireless networks are: Mesh networks as well as ad hoc…
A: Introduction: In everyday life, several sorts of technology are employed.
Q: What kinds of consequences may an organisation suffer if its cyber security is compromised?
A: Introduction: An information break happens when delicate data that has been put away on a further…
Q: Which of the following software development elements is the most important in terms of importance?…
A: Intro A software developer utilise computer programming to build software. They construct software…
Q: tablished TCH and sending da hs and there are ng transmission rtised window is at the client is 6
A:
Q: Explain in detail cloud computing and the benefits of adopting it.
A: Introduction: Cloud computing refers to the delivery of numerous services through the Internet.Data…
Q: What standards are JUnit tests written to, and why?
A: JUNIT: A unit check could be a piece of code written by a developer that executes a particular…
Q: Identify and explain two of the internet's first pioneers.
A: Introduction: The World Wide Web and the Internet's rapid expansion give the impression that the…
Q: Does the discipline of software engineering have anything that I'm not aware of that I should be?…
A: Given: Software engineering is a branch of engineering that focuses on developing software products…
Q: What different types of storage are there? Differentiate between the several categories provided.
A: Introduction: There are two categories of storage devices, which are as follows:
Q: Write the correct output (C++) #include using namespace std; int main(){ int num=1;…
A: Let us see the answer below,
Q: What are the various methods for structuring page tables? Describe hierarchical paging.
A: Introduction: Page table layout basically refers to how a page table may be designed. Yes, paging is…
Q: What is the size of an IPv6 address in bits and bytes?
A: Given that we have to answer the size of ipv6 address.
Q: Write the steps / procedure to be followed while writing the user documentation and technical…
A: So Below I provide the answer to this question
Q: Two of the predicted virtualized operating system effects should be identified and explored.
A: Introduction: Operating system virtualization (OS virtualization): It is a server virtualization…
Q: Create a structure named MyStruct containing two fields: field1, a single 16-bit WORD, and eld2, an…
A: Given Structure name: MyStruct Fields: filed1, a single 16-bit WORD field2, an array of 20 32-bit…
Q: Explain why firewalls are such a crucial component of network protection and cybersecurity. In a…
A: Introduction: As a vital component of network defense and cybersecurity, network scanning and…
Q: 2- Briefly explain Exploration and Exploitation in AI.
A: Exploration :- Exploration means that you search over the whole sample space (exploring the sample…
Q: The relationships between the ISA and HASA classes.In a class design, how would you implement each?
A: Intro Explain The Isa And Hasa Class Relationships. How Would You Implement Each In A Class Design?
Q: UDP offers which of the following benefits relative to TCP? O UDP supports a self-regulating…
A: According to the Bartleby guideline, we are supposed to answer only first 3 MCQ at a time. Kindly…
Q: Polymorphism - abstract class Banking Account class. Create an application with an abstract class…
A: Find the required code in java as language not mentioned given as below and sample output :
Q: 2) Consider the following D and G bit-strings D = 1001, G=1011 Compute the frame to be transmitted…
A: For polynomial generator G = 1011 and data fragments (message) D = 1001First by getting the CRC and…
Q: Explain the differences between procedural and object-oriented programming with one sample programme…
A: Intro In this question we have to understand the difference between procedural programming and…
Q: Which of the following loops would correctly add 1 to to all but the first element in values? Choose…
A: Problem is find all loops : that would correctly add 1 to all but first element in values lets…
Q: ain the differnece between soql and sosl sales
A: Introduction: Below the differnece between soql and sosl salesforce.
Q: Take into consideration the relevance of wireless networks in nations that are still in the process…
A: Given: A WLAN creates a wireless network (LAN) between two or more devices in a small space, such a…
Q: What are the key differences between a local-area network and a wide-area network in terms of…
A: Introduction: This topic highlights the primary differences between a local area network (LAN) and a…
Q: What exactly is a subinterface, and how does it function? Is it feasible for a user interface to…
A: Introduction: A sub-interface is a virtual interface formed by dividing a physical interface into…
Q: What are the most compelling reasons for using layered protocols?
A: Introduction: Layered Protocols: A protocol is a set of rules and practices that describe how two…
Q: Specifically, how should one approach dealing with the ethical issues raised by technology such as…
A: Intro What strategy should be used to address the ethical issues that computer, information, and…
Q: Is there a manner in which data profiling may increase the quality of data?
A: Data profiling: The process of reviewing source data, understanding structure, content and…
Q: How can we avoid a central processing unit from wasting processing cycles by processing a high…
A: Intro Because of the large number of instructions that are processed by the CPU, there are instances…
Q: A) Write a program to read a number and calculate if it is prime or not? Your answer
A: A positive integer that is only divisible by one and itself is referred to as a prime number.
Q: Why do we even bother talking about how rasterizing decreases the output's visual quality?
A: NOTE: OUTPUT' VISUAL QUALITY COMES UNDER IMAGE QUALITY IN COMPUTER SCIENCE Introduction…
Q: What are the goals of authentication? Different authentication mechanisms have different…
A: Intro Authentication Authentication is the process of determining whether someone or something is,…
Q: First question: Why am having an error pop up when running my program that says: "Editor does not…
A: First question: Why am having an error pop up when running my program that says: "Editor does not…
Q: What are the different sorts of transmissions, and can you give an example of each?
A: Introduction: The following are the many modes of transmission: Transmission mediums are classified…
Q: What is the most important aspect of a data warehouse, and why is it known as MetaData?
A: Introduction: Metadata is data about data or documentation about data that consumers want. Metadata…
Q: Do you plan to deploy any high-availability DHCP solutions in your firm, and if yes, for what…
A: Foundation: For example, DHCP is a network technique that gives each host its own IP address…
Q: Mossaic Tiles, Ltd. Gilbert Moss and Angela Pasaic spent several summers during their college years…
A:
Q: Describe the predictive analytics method and offer an example of how it is applied in practise.
A: Intro Predictive analytics is the process of using using the data analytics to make the data…
Q: When contrasted with wired networks, wireless networks have a lesser throughput.
A: Introduction: When properly configured, wired networks offer more longevity and stability than…
Q: A lift calling system is to be programmed for an organization building having 4 floors. The CEO of…
A: ASSUME that lift reaches CEO 3rd floor be A, 1st floor be B and 2 nd floor be C and D Ground floor…
Q: A. What is the maximum data rate that a medium of 20 KHz and signal-to-noise ratio (SNR) of 10 dB?…
A: Answer to both the parts have been provided in subsequent steps.
Step by step
Solved in 2 steps

- The dblBonus variable contains the number 1234.75. Write the assignment statement to display the value with a dollar sign, a thousands separator, and no decimal places in the lblBonus control.The __________ contains a numeric value, which indicates the control’s position in the tab order. a. IndexOf property b. TabIndex property c. ControlOrder property d. TabOrder propertyThe strItem variable contains the string “XMredBQ”. Write a statement that uses the Substring method to assign the string “red” to the strColor variable.
- Variable scope is the area in your code where a variable can be accessed? True or FalsePlease color the code? Identifier (RED) Expression(BLUE) Statement(Yellow) Reserved words(dark red) Please helpThis is an operator used to assign a value to a variable. It works by transferring the value on its right to the variable on its left. greater than / equal (>=) equal (= =) less than / equal (<=) assignment (=)
- Write a statement that displays the intQuantity variable’s value in the lblQuantity.Text property.The AND operator takes two Boolean expressions as operands and creates a compound Boolean expression that is true only when___. Question 11 options: O or 1 expressions are true the first expression is true the second expression is true both subexpressions are trueTrue or False : You can change the same property for multiple controls simultaneously.
- Q3: Design a form with a text box in visual basic . Use select statement so that when user enters g, b, r and respectively. y then form colored to green, blue, red, and yellowIf the intTotalScore and intTests variables contain the numbers 200 and 0,respectively, the statement dblAvg = intTotalScore / intTests will_________ .a. assign 0 to the dblAvg variable b. result in a syntax error c. result in a logic error d. result in a run time errorName Formatter Create an application that lets the user enter the following pieces of data: • The user’s first name • The user’s middle name • The user’s last name • The user’s preferred title (Mr., Mrs., Ms., Dr., etc.) Assume the user has entered the following data: • First name: Kelly • Middle name: Jane • Last name: Smith • Title: Ms. The application should have buttons that display the user’s name formatted in the following ways: Ms. Kelly Jane Smith Kelly Jane Smith Kelly Smith Smith, Kelly Jane, Ms. Smith, Kelly Jane Smith, Kelly

