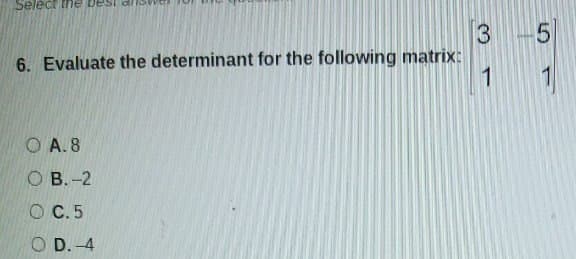
3 6. Evaluate the determinant for the following matrix: 1 O A. 8 оВ. -2 O C.5 O D. -4
Q: t routing is or h
A: Routing is the most common way of choosing a way for traffic in an organization or between or across…
Q: It is critical to classify DNS records based on their kind. Give a brief description of each, as…
A: Translating IP addresses into comprehensible domain names is the objective of the Domain Name System…
Q: What are the two main types of CPU design?
A: Introduction: CPU configuration is the outline constructing task of creating a chip, which is a…
Q: Explain what application virtualization is and why it is important.
A: With increase of cloud computing servers, application virtualization is highly used in organisation…
Q: Compile and explain a list of the five key areas/fields of internet governance, as well as the…
A: Introduction: A myriad of regulations control the security of aggregated data, fiscal…
Q: In computer science, what are the prerequisites?
A: Answer: You should have the option to peruse and compose, experience with a computer is an or…
Q: How critical is it to have a Master file that contains long-term data?
A: Master File: A master file is a file that includes data that is expected to last for a long time. A…
Q: Computer science What does it imply to say that a category of jobs is net of outsourcing?
A: Introduction: What does it imply to say that a category of jobs is net of outsourcing?
Q: What's the difference between a masked ROM and a one-time password (OTP)?
A: OTP is a kind of EPROM that is plastic-encased. The cheapest software is stored in ROM, but its…
Q: What exactly is "web services provisioning"?
A: Given: What exactly is "web services provisioning"?
Q: Does the transition from on-premise servers to an IaaS architecture provide any governance…
A: IaaS Architecture: IaaS architecture refers to the structural design of a computer network that…
Q: Need Program in C++ Write a templated function to find the index of the smallest element in an…
A: Step 1 : Start Step 2 : Define a templated function findMin() which accepts an array of any type and…
Q: What are the advantages and disadvantages of MySQL?
A: Introduction: It is a relational database management system that is free and open-source (RDBMS). A…
Q: Distinguish between wireless networking issues that may develop when two stations are visible at the…
A: Wireless networking refers to a network in which data is sent from one host to another host without…
Q: Discuss various software samples based on their categories?
A: Introduction: Software is a computer programme that delivers instructions and data to a computer in…
Q: What are a Data Dictionary and a Repository of Contrasts
A: Introduction Data Dictionary: In a database, information system, or research endeavor, a Data…
Q: While developing an information security strategy for your MIS, it is critical to recognize the…
A: The market of cybersecurity has grown an evolved and has increased the reliance of the IT business.…
Q: Do you have any tips for preventing cyberattacks on the company's network?
A: Introduction Cyberattacks are the attacks which are malicious activities to breach the…
Q: Demonstrate how to reorder cells in Excel.
A: The easiest way Select the range of data/cell you want to rearrange, including any row or column…
Q: Numerous benefits accrue from using RAID Level 2 in the university payroll system. What are the…
A: RAID 2 RAID 2 is a standard-level RAID setup that delivers extremely fast data transfer speeds. In…
Q: Why is it that, despite its beauty, the concept of a file has such strength?
A: Introduction: The term "beauty" refers to an object's ability to elicit pleasure in the senses.…
Q: your computer networking skills? describe the various uter networks
A: Below your computer networking skills and Descibe the various types of computer networks
Q: What is the purpose of a Master file, which is mostly composed of permanent data?
A: The Answer is in step2
Q: Define the attributes required for test-driven development. What improvements would you make to it…
A: According to the question essential principles of check pushed improvement TDD and assuming that you…
Q: Do you want to discuss Big Data and how organizations are using it today, and why
A: Big data is a combination of structured, semistructured and unstructured data collected by…
Q: Computer science Explain Common logic distributions?
A: Introduction: Logic distribution is also known as term distribution. The term of a proposition is…
Q: What is the operating system's approach to managing processors?
A: Introduction: It is possible for just one process to be active at a time. Because CPUs are so fast,…
Q: Provide a list of bullet points describing how the computer boots.
A: According to the question the boot start-up process done for the help to manage every task step by…
Q: An answer to this question: What does it mean to have a stable database state? There is no guarantee…
A: Stable Database: It is defined as a database that has all of the data integrity requirements,…
Q: What advantages and benefits can information systems provide?
A: Information system advantages and benefits: Businesses have grown more reliant on the successful use…
Q: What is the significance of the internet of things ? (IoT)
A: Introduction: The Internet of Things will generate data about linked items, evaluate it, and make…
Q: What are the integrity rules in DBMS?
A: Introduction A database management system, sometimes referred to as a DBMS, is a computerized…
Q: RAM and Register are two different types of memory.
A: A Memory: The cache memory of a device contains all of the device's frequently used data and…
Q: What is a balanced scorecard, and how does it work?Describe the four elements that make it up.
A: Introduction: According to the question, the first step is to define a balanced score card, which is…
Q: For application-level proxies, end-to-end encryption could be a concern. Propose a solution for a…
A: Introduction: A proxy-based system has a number of security challenges to contend with. In this…
Q: What is the difference between computer architecture and computer management in terms of computer…
A: Computer design: The framework in which components relate to one another is known as computer…
Q: Computer science Explain what social commerce is and why it is so popular.
A: social commerce and the reasons for its popularity
Q: Demonstrate how Cascading Style Sheets (CSS) work.
A: Cascading Style Sheets (CSS) is a style sheet language utilized for depicting the introduction of a…
Q: How challenging is it to design a user experience for a smartphone? Describe in detail the…
A: Given: How difficult is it to develop user interfaces?There are five tasks to implement user…
Q: What role does the operating system have in processor management?
A: Function does the operating system play in processor management
Q: Suppose that a SW ARQ system with 1-bit sequence numbering has a time-out value that is less than…
A: The Answer is in step-2.
Q: In which of these three qualities does TCP vary from UDP?
A: Introduction: The three qualities does TCP vary from UDP :
Q: Since the Master file contains long-term data, is it necessary?
A: Introduction: It is a collection of records that pertain to one of the primary subjects in the…
Q: What are the numerous cyber security dangers that you would anticipate and prepare for when building…
A: Cyber Security Any preventative step aimed to keep information from being stolen, hacked, or…
Q: Demonstrate the potential benefits of computers.
A: THank you _________ INPUT AND STORING DATA When an item is scanned, the check-out computer checks…
Q: Explain what virtualization is and the differences between the various types of virtualization…
A: According to the question Today, virtualization is a common practice in building IT business. It is…
Q: e must first compre
A: IntroductionRAID 5 is a setup that employs disc striping with parity to create a redundant array of…
Q: Is Ubuntu Linux based on a specific Linux distribution?
A: Ubuntu is a Linux-based operating system that is free to download and is open source.
Q: What is the difference between a logical and a physical data flow diagram in data flow diagramming?
A: Data Flow Diagram(DFD) A data flow model commonly called a data flow diagram (DFD), is a…
Q: Computer science a. Explain how to undertake a statistical attack on a monoalphabetic substitution…
A: Answer (a): A monoalphabetic figure is a substitution figure in which for a given key, the code…
Step by step
Solved in 2 steps

- Draw the following graph as represented in the adjacency matrix below. a b c d A 1 1 1 0 B 0 1 1 0 C 0 0 1 1 d 0 0 0 1Generate a 10x10 random matrix using the function randn() and name the matrix as matrix E. Using the function find(), replace all negative elements of matrix E by zero. Check the resulting matrix using the function sign(). MATLAB code:by using c++ .. 1)Find the multiplication matrix of 2 square matrices A and B of size n*n each. 2)Write the recurrence relation and solve it.
- Find Matrix Chain multiplication for following four matrices (M1, M2, M3 and M4) using dynamic programming matrix = m1 m2 m3 m4 order of matrix= 4*3 3*5 5*2 2*6Given an NxN matrix of positive and negative integers, write code to find thesubmatrix with the largest possible sum.What is the LU factorisation of the following matrix
- — lupdlipanpmtisie et tmts e R 5 A, ) B S S S et Given a 2-D square matrix: B mati31l31-{11, 2 3} 14 5 6}, (7,8,9}}. Write a function transpose which varts the matrix mat into its ftranspose 3np}ae t the transpose, IN C++ language.make an adjacency matrix for the following: E= {(1,2),(2,1),(3,2),(4,3),(4,5),(5,6),(6,7)}Problem 1. Draw the graph for the following adjacency matrix.

