Show how the following floating-point additions are perf are truncated to 4 decimal digits). Show the results in norm a. 5.566 × 10² + 7.777 × 10² b. 3.344 x 10¹ +
Q: Why should we use the OSI Security architecture?
A: What is OSI Security Architecture : The security of an organisation is of the utmost importance to…
Q: Describe the function that is served by each layer of the OSI model when it comes to security.
A: In this question we have to describe the function that is served by each layer of the OSI model in…
Q: Write the code segment for each of the following tasks: a) Declare a structure type named Marks,…
A: Dear student, The solution is provided below.
Q: Think about the standard TCP/IP ports. To correctly build security, businesses need to be aware of…
A: A personal computer network is a collection of individual computers connected through various…
Q: 3. Let P(n) be the statement that 12 +2²+...+ n² = n(n+ 1)(2n + 1)/6 for the positive integer n. a)…
A: a) The statement P(1) is that 12 = 1(1 + 1)(2(1) + 1)/6 b) P(1) is true because 12 = 1 c) The…
Q: Assume Prit wants to send a message consisting of 1000 packets to John using Malav's 'Sliding…
A: The total elapsed time for Prit to be certain that the file has been successfully transmitted to…
Q: Which rules should effect exposed and traceable project components if a software industry uses…
A: Given: The software industry use a method known as the Software Development Life Cycle (SDLC) to…
Q: with 500 addresses, two organizations each with 250 addresses, and three organizations each with 50
A: The answer is
Q: Assume the following declaration: truct Student string name; int matricNo; Marks marks;
A: //Program: #include<iostream>#include<string>using namespace std;struct Student{string…
Q: What three factors are taken into account while choosing hardware?
A: The question has been answered in step2
Q: Which of the five memory management approaches has which benefits and drawbacks?
A: Memory management is the process of controlling and coordinating a computers main memory.
Q: Write c# code to reverse order of words in string Input : this is me Output : me is this…
A: As given, we need to write a C# code to reverse words in a string. I have provided the complete code…
Q: What advantages does utilizing virtual memory offer?
A: Electronic Memory: Virtual memory gives the user the impression of a very big main memory since it…
Q: What distinguishes firewalls from virtual private networks?
A: The question has been answered in step2
Q: Please re-write this code with NO IMPORTS. Thank you
A: Here is the code without IMPORTS:
Q: Why is software design's development phase so crucial?
A: A software design will go through some procedures, including planning, gathering requirements,…
Q: c programming Write a ccdel program that takes an item number as a command line argument and…
A: #include <stdio.h> #include <stdlib.h> #include <sys/file.h> #include "cc.h" int…
Q: URGENT NEED THUMBS DOWN COP ? 2: Take the username and password from a user and check the validity…
A: pseudocode: 1. Take username and password as input from user 2. Check if password contains username,…
Q: virtual machine (VM) and how does it work? Which benefits may virtual machines provide?
A: Introduction Virtual Machine:- A Virtual Machine, typically shortened to simply VM, is not any…
Q: In this project, you are asked to independently research and write a short report relating to our…
A: Here is the solution:
Q: Problem 2. Give a counterexample to the conjecture that if a directed graph G contains a path from u…
A:
Q: What circumstances make using conventional files for data storage effective?
A: Data storage which refers to the files and the documents that are used to recorded in the digitally…
Q: Python program to shuffle Deck of cards using list?
A: Python:- In day-by-day life, Python is near the English language we use. The consistency of the…
Q: I need to locate a book in the database. How do I do that?
A: About DBMS A database management system (DBMS) is a repository where an authorized user may build a…
Q: What logic operator is used to connect premises in logic arguments? What logic operator negates the…
A: Logical operators are the symbols which are used to connect two or more expressions where the output…
Q: C Programming
A: #include <stdio.h>#include <stdlib.h>#include <string.h>#include…
Q: Given the following code segment (assume is incomplete code and it is not indicative of the number…
A: question 1 part 1 ret = fork();if (ret == 0) {val++;} part 2 printf("a = %d", a);if (ret == 0)…
Q: 4. Consider the following grammar with terminals [, ], a, b, c, +, and -: a) S→ [SX] | a X +SY | Yb…
A: Dear Student, The detailed solution for your question is given in step 2 and the final table is…
Q: How should someone continue if they have forgotten both the administrator password and the system's…
A: The answer of the question is given below:
Q: dard TCP/IP ports. To correctly build security, businesses need to be aware of the services' goals…
A: Introduction: The Microsoft client and server operating systems, server-based applications, and…
Q: Implement the following Racket functions: Symmetric-Closure Input: a list of pairs, L.…
A: The code is shown below. It uses the symm helper and opp functions. (define (opp p) (list (car (cdr…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: A PC network is a group of computers that share resources on or given by the organization hubs. They…
Q: What is streaming data? please explain
A: Streaming data is information that is produced consistently by a huge number of information sources,…
Q: Address the following: DHCP is a very promiscuous service, and this can cause unplanned service…
A: 1) Improperly configured DHCP can cause downtime for the entire office and can put additional…
Q: MD5 hash can be applied to which of the following data streams?
A: MD5 hash can be applied to which of the following data streams? .ppt file .doc…
Q: Create a Java Program using the scenario below. You made a $6,000 purchase for a car using an…
A: We need to write a Java code for the given scenario.
Q: Write a program to generate the following pattern. (Sample input/output given below) Enter number of…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main method Step 2:…
Q: The definition of luminance What are the main distinctions between brightness and radiance?
A: The definition of luminance: The quantity of light that is emitted from a surface in a certain…
Q: A nonpipelined processor has a clock rate of 2.5 GHz and an average CPI (cycles per instruction) of…
A: Answer:-
Q: Based on the codes given in Program-4, illustrate the memory address of the po current values for…
A: Introduction: Below run the C++ program and get output illustrate the memory address of the…
Q: What is streaming data?
A: Data Streaming: The term "streaming data" refers to data that is produced continually by thousands…
Q: (a) IPsec uses ESP transport mode. (b) IPsec uses ESP tunnel mode. (c) What if we use PAT (Port…
A: IPSec (Internet protocol security) is a type of algorithm which provides security to data from…
Q: How should someone continue if they have forgotten both the administrator password and the system's…
A: The question has been answered in step2
Q: A computer consists of a processor and an I/O device D connected to main memory M via a shared bus…
A: It is given that on a normal a guidance requires 6 cycles and the CPU is occupied 95% of the time in…
Q: How can the practical use of virtual servers and services be shown and explained?
A: Virtualization is becoming more substantial in the world of innovation as people realize how it may…
Q: When you mention network security, what do you mean? Describe the operation of the data encryption…
A: network security The idea of network security is quite all-encompassing, and it encompasses a broad…
Q: Where exactly are the weaknesses in the security architecture located?
A: Security architecture forms the foundation of a good cyber security strategy.
Q: What is streaming data? please explain
A: Streaming data is data that is continuously generated from thousands of data sources and typically…
Q: Explain what is meant by the term "caching" when referring to shared memory.
A: Shared memory is the memory that may be simultaneously accessed by multiple programs with an intent…
Q: Discuss the influence of cookies on internet security in detail, mentioning at least four (4)…
A: The answer is as below:
Step by step
Solved in 2 steps

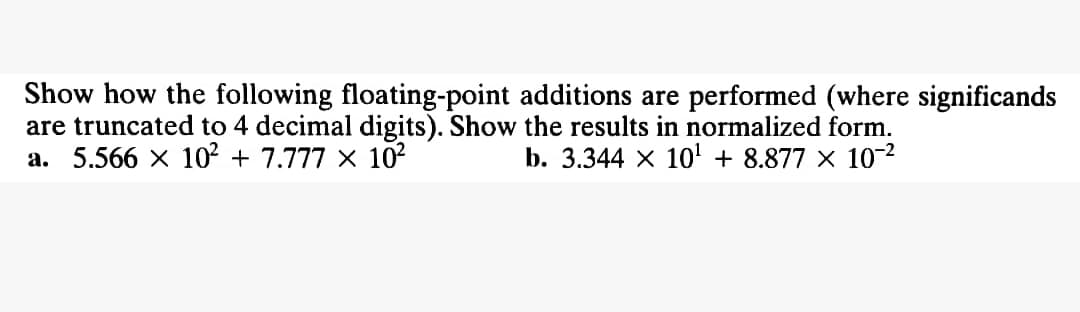
- Show how the following floating-point additions are performed (where significands are truncated to 4 decimal digits). Show the results in normalized form. Know the solution but can explain more details about this question in words? a) 5.566 x 10² + 7.777 ×10² b) 3.344 x 10' + 8.877 x 10-2Convert the following hexadecimal expansion ( CA2 ) base 16 to an octal expansion. Then, convert the following binary expansion ( 1111 0101 0110 1100 ) base 2 to a hexadecimal expansion. Please show step by step solutions.Show how the following floating-point additions are performed (where significands are truncated to 4 decimal digits). Show the results in normalized form. a) 5.566 x 10² + 7.777 ×10² b) 3.344 x 10' + 8.877 x 10-2 Can I know how to explain this type of question?
- Fill in the following table to show how the given integers are represented, assuming that 16 bits are used to store values and the machine uses two’s complement notation. Integer Binary Hex 4-Byte Big Endian (Hex value as seen in memory) 4-Byte Little Endian (Hex value as seen in memory) 28 2216 −18675 −12 31456Please answer step by step and thank you so much! Complete the following addition in base-2: 1011 + 110What is the number of bits needed to represent the double of a number represented in 5 bits in the binary system? Please Show working out - in steps
- What is the decimal value of the following number (which is in single-precision IEEE floating point format?) Show your work and explain what each part of the representation is and how you achieve your final answer. 00111111010000000000000000000000J - For the IEEE 754 single-precision floating point, what is the number, as written in binary scientific notation, whose hexadecimal representation is the following? FF80 0000Convert the following decimal number into equivalent binary number and hence write the binary number in 64- bit long real format (53.36755) i need the answer by same way example through picture please.!
- Perform the following calculations on hexadecimal numbers. Assume 24-bit unsigned integers, and discard the overflow bit from the result if any. 6A72B3+171137=???Add the following pairs of 16-bit numbers (shown in hexadecimal) and indicate whether your result is “right” or “wrong.” First treat them as unsigned values, then as signed values (stored in two's complement format). 12cc+ed34 8000+8000 07c0+782ePLEASE INCLUDE STEP BY STEP EXPLANATION52) For IEEE 754 single-precision floating point, what is the number, as written in binary scientific notation, whose hexadecimal representation is the following:a) 4280 0000b) B350 0000c) 0061 0000d) FF80 0000e) 7FE4 0000f) 8000 0000

