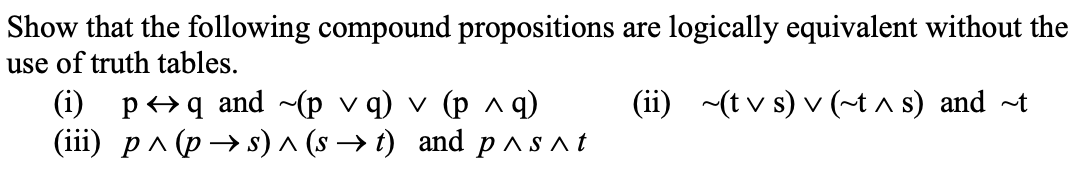
Show that the following compound propositions are logically equivalent without the use of truth tables. (ii) (tvs) v (~t^ s) and t (i) pq and (pvq) v (p ^ q) (iii) p^(ps) ^ (s→t) and p^s^t
Q: s there a name for the idea behind Object-Oriented Design? Object-oriented code: how to make it
A: Object-Oriented Programming (OOP) has gotten both love and disdain from individuals in the coding…
Q: Which part of the device's hardware enables a direct connection to a network?
A: --> The part of a device's hardware that enables a direct connection to a network is typically…
Q: A stack-ended queue or steque is a data type that supports push, pop, and enqueue. Articulate an API…
A: We have to discuss A stack-ended queue or steque is a data type that supports push, pop, and…
Q: A compiler's efficacy and precision are contingent on its capacity to account for a variety of…
A: A compiler is a crucial software tool that translates human-readable source code into…
Q: Virtual machines make it easier to run many operating systems on a single computer. How much do you…
A: I agree that virtual machines make it easier to run many operating systems on a single computer.…
Q: In what ways could data mining be advantageous? In the context of software development, what is the…
A: Data mining involves discovering models, parallels, and differences within large datasets to expect…
Q: System analyst software assessment methods should be outlined.
A: System analysts are crucial in understanding and designing solutions for business needs. An…
Q: Does the time it takes to switch between tasks depend on the interrupt latency?
A: Does the time it takes to switch between tasks depend on the interrupt latency?
Q: Which architectures of back-end compilers need testing?
A: Back- end compilers, also known as code generators, are responsible for translating high-level…
Q: How did the word "spool" come to be used to describe what comes out of a printer, and why is it…
A: Spool":1: a cylindrical device with a rim or ridge at either end and an axial hole for a pin or…
Q: Why copying someone else work is plagiarism? What are things to do to ensure you do not…
A: According to the information given:-We have to define above 2 scenarios about plagiarism.
Q: How does vertical code affect the creation of a control unit, and what steps do you need to take to…
A: The control unit in a computer is to blame for managing the operation of the CPU and the interaction…
Q: Virtual machines make it easier to run many operating systems on a single computer. How much do you…
A: I completely agree that virtual machines make it easier to run many operating systems on a single…
Q: What is considered a TCP loss event?
A: In computer networking, Transmission Control Protocol (TCP) is a widely used protocol that provides…
Q: List two ways software-defined networks outperform hardware-based ones. Which two advantages do…
A: Software-defined networks (SDNs) surpass hardware-based networks regarding flexibility and…
Q: John von Neumann came up with what theory for computers
A: In 1949, John von Neumann came up with what theory for computers?
Q: Some Linux functions are exactly the same as their Unix equivalents. So what's going on?
A: In the world of computer science, both Linux and Unix play significant roles. Linux is an…
Q: Suppose x is a linked-list node and not the last node on the list. What is the effect of the…
A: Linked lists are a fundamental data structure used in computer science and programming. They consist…
Q: What qualities does a compiler require to generate dependable and effective code? Explain?
A: A compiler is a fundamental tool used in the software development process, responsible for…
Q: How did John von Neumann make the first computer? In what year did he do it?
A: John von Neumann played a pivotal role in the development of the first computers, particularly…
Q: Create a fictitious authentication management scenario and describe it in detail. Select multiple…
A: In the context of a leading global financial institution, "Glob Bank," let's consider the challenge…
Q: Is there a name for the idea behind Object-Oriented Design? Object-oriented code: how to make it
A: The idea behind object-oriented plan is encapsulate in the idea recognized as "Abstraction."…
Q: Share some files managed in the three most common ways
A: When it comes to managing files, there are various approaches depending on the needs and preferences…
Q: Describe the complications that arise in wireless networking when one station is concealed and…
A: Describe the complications that arise in wireless networking when one station is concealed and…
Q: Of the five competitive forces presented in the chapter (Porter's model), which is the most…
A: Michael Porter's Five Forces model is a strategic management tool that helps organizations analyze…
Q: The linked-list implementation of Stack should have a new constructor created such that Stack t =…
A: To create a new constructor in the linked-list implementation of Stack that creates an independent…
Q: Who should have access to a private key within an authentication system employing both private and…
A: Private keys are basic to critical public infrastructures (PKIs). The private key is meant to be…
Q: Discuss the development of computers, the tools we use now, and what the future may hold.
A: Computers have come a long way from the days of mechanical computing machines such as the abacus to…
Q: What are the distinctive characteristics of computers?
A: Computers possess several distinctive characteristics that set them apart from other devices.
Q: Should database makers be aware of any specific methods that, based on the situation, could have a…
A: Database design is a severe aspect of a database's running. A no-nonsense design ensures data…
Q: What differences exist between networked and distributed operating systems?
A: Networked and distributed operating systems are both designed to enable communication and resource…
Q: Explain the purpose and functionality of a challenge-response authentication system. Not readily…
A: Challenge-response authentication is a security mechanism that aims to improve upon conventional…
Q: Matlab code asa sa.
A: MATLAB code for generating and plotting the output of a difference equation. Let's go through each…
Q: Can authentication help us achieve our goals? This section compares the pros and cons of various…
A: Systems for authentication are essential to the safety of our digital environment. Before giving…
Q: Create a class called Book that has the following attributes: Book () Book(author, publisher, title,…
A: SOLUTION-I have solved this problem in Java class with comments and screenshot for easy…
Q: When the parent process terminates, whether normally or unexpectedly, so do the offspring processes.
A: In computer systems, processes are essential entities that execute programs and perform various…
Q: Try to predict two OS alterations caused by virtualization.
A: Operating system virtualization refers to using frequent operating system metaphors on a lone piece…
Q: Create a new constructor for the linked-list implementation of Stack so that Stack t = new…
A: In the provided constructor Stack(Stack<T> stack), it checks if the original stack (stack) is…
Q: Private cloud services are more safe by nature than public cloud services. Which plan would help the…
A: When considering the safety of private cloud services compared to public cloud services, it's…
Q: Has the internet and other technology, like globalisation, made society more or less peaceful?…
A: On one hand, the internet has facilitated communication, information sharing, and collaboration on a…
Q: Part 3: Looping while(x<y) { If(z<0){ x=x+a; } Else{ x=x+z; z= -z } x=x+1; }…
A: The while loop is a fundamental control structure in programming that allows a block of code to be…
Q: ead the Design for America Design ProcessLinks to an external site. document from the Design for…
A: In the DFA Design Process, the BUILD phase focuses on prototyping and gathering user feedback. Here…
Q: Why is hashing superior to encryption when storing a passphrase in a file? The function and usage of…
A: When it comes to store passwords, hash is often deem superior to encryption due to quite a few…
Q: What is your underlying approach or guiding principle as an operating system designer with regards…
A: the microkernel architecture follows guiding principles such as minimization, modularity,…
Q: The term "store-and-forward network" is rarely used these days, and there are many reasons why.
A: Your answer is given below.
Q: Which paradigm poses the greater difficulty to compilers, VLIW or superscalar? Why?
A: VLIW (Very Long Instruction Word) and Superscalar are two paradigms of central processing unit…
Q: Discuss password administration and the importance of a robust password in light of your new system.
A: - We need to talk about password administration and the importance of robust password for a new…
Q: Think about all the ways someone could break the rules or not care about them. Because of changes in…
A: A Double-Edged Sword Technological advancements have unquestionably changed how we interact with the…
Q: What purpose do device drivers serve if the BIOS already allows the operating system to communicate…
A: As a subject matter expert, I can explain the purpose of device drivers in relation to the BIOS and…
Q: DIscuss the differences between Bitcoin and Blockchain and which in your opinion is better.
A: 1) Bitcoin is a digital currency or cryptocurrency that operates on a decentralized peer-to-peer…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Answer the given question with a proper explanation and step-by-step solution. Which color scheme would be the best to use to show the total population by state, showing states with the fewest number of people to the most, low to high on a choropleth (i.e. shaded or “filled”) map? 1.Diverging 2.Categorical 3.Sequential 4.Sequential-CategoricalConsider the following knowledge base in first order logic: p(X) ← q(X) ∧ r(X, Y ) q(X) ← s(X) ∧ r(Y, Y ) s(a) r(a, a) What is the result of the query p(a) using a backward chaining inference algorithm? Show the intermediary queries.Consider a Diffie-Hellman scheme with a common prime q = 11 and a primitive root α = 2. Show that 2 is a primitive root of 11. If user A has public key YA = 9, what is A’s private key XA? If user B has public key YB = 3, what is the secret key K shared with A?
- ¬P ∧¬Q≡¬(P ∨Q) Prove the following equivalency relation (Proof, Justification/explanation):Using Armstrong's axioms plus union and decomposition, prove the following: Given attribute sets A, B, C, and D, if A→D and C→B, B→A and D→C then B,D→A,C.Compare and contrast NP and P, and use real-world examples to highlight their differences.
- The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists of 25 As, 20 Bs, 15 Cs, 5 Ds and 35 Es. What is the mutual index of coincidence between sets S and T? Leave your answer as a fraction in lowest termsPlease answer this question and plz don't reject it under complex questionConsider the following knowledge base Prove that Q is true with: 1. P → Q 2. L ∧ M → P 3. B ∧ L → M 4. A ∧ P → L 5. A ∧ B → L 6. A 7. B Forward-Chaining Backward-Chaining Resolution Prove t → s: 1. p → q 2. [q ∧ r] → s 3. [t ∧ u] → r 4. u → w 5. t → y 6. y → u 7. r → p 8. p → m i. Express in clause form ii. Forward-Chaining iii. Backward-Chaining iv. Resolution
- Let c1, c2, and c3 be the confidence values of the rules {p}->{q}, {p}->{q, r}, and {p, r}->{q}, respectively. If we assume that c1, c2, and c3 have different values, what are the possible relationships that may exist among c1, c2, and c3? Which rule has the lowest confidence?prove the equivalence of the schemata:~(~(p • ~ q ) • ~ ( ~ p• q)) equal to ~(p • q) • ~(~p • ~q)May I see the 5 samples from the Bayesian network and then using these 5 samples to answer the following query: P(S = s1|L = l1) =?

