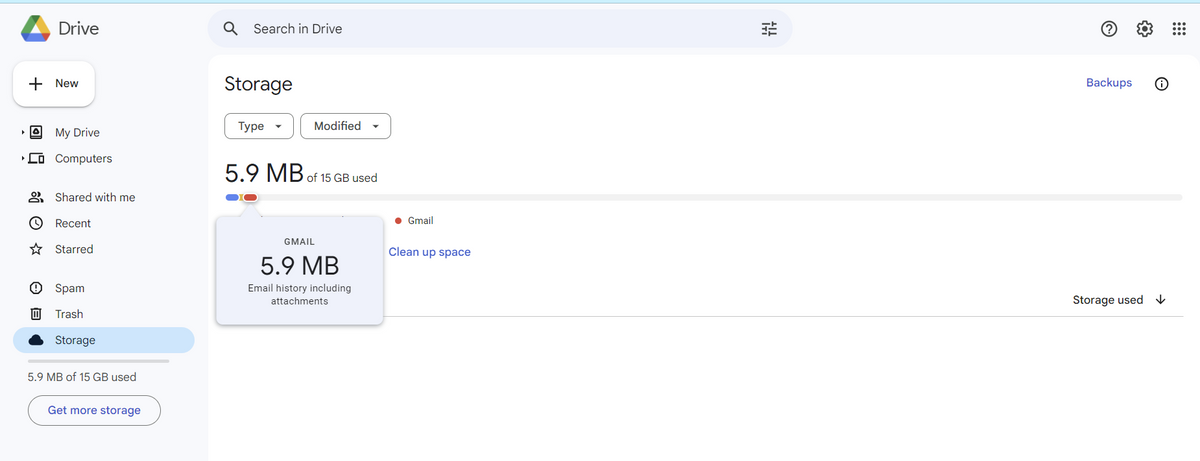
So in my google drive, what does gmail represent? Does it show how many gmails are currently in my account? Does it show how many messages I've sent? what does it show?
Q: Discuss the concept of RAID (Redundant Array of Independent Disks) and its various levels,…
A: RAID, which stands for Redundant Array of Independent Disks, is a technology used in data storage to…
Q: Explain how load balancing enhances WAN reliability.
A: In the dynamic landscape of Wide Area Networks (WANs), ensuring reliable and efficient connectivity…
Q: Explain how pipelining improves the overall throughput of a processor.
A: Pipelining is a technique used in computer architecture to boost the performance of a processor by…
Q: What are the key components of a WAN architecture, and how do they contribute to the network's…
A: WAN is a computer network that covers the large geographical area consisting of two or more Local…
Q: Describe the impact of pipeline depth on the performance of a processor and trade-offs involved in…
A: In this question we have to understand about the impact of pipeline depth on the performance of a…
Q: Explain the role of a virtual machine operating system and its advantages.
A: A virtual machine operating system is a key element in virtualization technology, enabling the…
Q: Analyze the role of hypervisors in virtualized environments and their impact on system performance
A: Hypervisors, also known as virtual machine monitors (VMMs), play a crucial role in virtualized…
Q: Describe the role of routers in WANs and how they facilitate communication between different…
A: Routers have a role, in Wide Area Networks (WANs) as they ease communication between networks.Unlike…
Q: Explain the concept of data hazards in pipelining and discuss various methods to mitigate these…
A: 1) Pipelining is a technique used in computer architecture to enhance the throughput and efficiency…
Q: Explain the concept of a storage area network (SAN) and its significance in enterprise-level storage…
A: In the digital age, organizations need storage infrastructures that are scalable, high-performing,…
Q: List and explain the functions of common WAN devices such as routers, switches, and modems.
A: Common WAN (Wide Area Network) devices are essential for interconnecting and fostering communication…
Q: Write out the addition and multiplication tables for Z6 (where by addition and multiplication we…
A: Arithmetic operations defined on Zm as, the set of non-negative integers less than m, i.e set {0,…
Q: Given the following memory values and a one-address machine with an accumulator, what values do the…
A: The task mentioned here involves simulating the execution of instructions on a one-address machine…
Q: Create a "Branflake" program that will accept two integers in the form of a string "x+y", add the…
A: I have provided PYTHON CODE along CODE SCREENSHOT and OUTPUT SCREENSHOT....
Q: Explore emerging storage technologies, such as holographic storage or DNA storage, and their…
A: The world of data storage is witnessing a remarkable transformation driven by cutting-edge…
Q: Discuss the importance of adhering to standards in WAN implementation and maintenance.
A: A wide area network, or WAN, is a network that connects several local area networks (LANs) or other…
Q: Explain the concept of branch prediction and its role in improving pipelined processor performance.
A: Branch prediction plays a role in computer architecture, especially when it comes to pipelined…
Q: python help Q9: Sub All Write sub-all, which takes a list s, a list of old words, and a list of new…
A: In this question we have to write a python code to write a sub-all which replaces words in the input…
Q: Describe the key components and technologies involved in establishing a WAN connection.
A: Wide Area Network (WAN) connections are essential for networking because they allow data exchange…
Q: Make a relational diagram with the following data: 1. Patient Entity: RUT (Primary Key): Integer…
A: In this question we have to understand about the given relation ships and design a relationship…
Q: Explore the microkernel architecture and discuss its advantages in terms of system reliability and…
A: The microkernel architecture represents a paradigm shift in the design of operating systems,…
Q: Evaluate the pros and cons of exokernel and nanokernel architectures.
A: In this question we have to understand about the pros and cons of exokernel and nanokernel…
Q: Discuss the distinctive features and functionalities of real-time operating systems (RTOS) compared…
A: Operating systems that are designed to fulfill certain needs of various applications are known as…
Q: Discuss the key functions and characteristics of a time-sharing operating system.
A: An operating system that allows several users to share a computer's resources at the same time is…
Q: Evaluate the differences between magnetic and optical storage technologies, considering their…
A: There are two methods used for storing and retrieving data; magnetic storage and optical…
Q: Analyze the trade-offs involved in designing a deep versus shallow pipeline in a processor…
A: In the world of processor architecture, the design of pipelines plays a role, in deciding how…
Q: Explain the concept of RESTful APIs and how they facilitate communication between client and server…
A: A RESTful API (Representational State Transferful API) is an architectural style used in web…
Q: Discuss the role of optical storage devices in modern computing.
A: Modern computing refers to the current state and practices of using advanced technologies, hardware,…
Q: you are to implement a multithreaded program that will allow us to measure the performance (i.e.,…
A: A multithreaded program to simulate CPU scheduling involves handling concurrent tasks like reading…
Q: Explain the purpose and usage of CSS (Cascading Style Sheets) in the context of web design,…
A: In this question we have to understand about the purpose and usage of CSS (Cascading Style Sheets)…
Q: performance tuning: if your condition is P_PRICE +12= 27, in order to make your query more…
A: Performance tuning in a database refers to the process of optimizing the performance of a database…
Q: Define the concept of pipelining in computer architecture. How does pipelining enhance the…
A: Pipelining in computer architecture is a technique that allows a processor to execute instructions…
Q: Draw the diagrams of an 2-3 tree as the following items are inserted into an empty tree in the…
A: 2-3 Tree: A particular kind of self-balancing search tree data structure in which there can be two…
Q: Explain the need of having three different type of subroutines: function, method, and constructor in…
A: In object-orientated programming (OOP), subroutines are used to organize related code collectively…
Q: Discuss the role of routers in WANs and how they facilitate communication between geographically…
A: Routers stand as indispensable components in Wide Area Networks (WANs), playing a pivotal role in…
Q: Discuss the role of WebAssembly in web development and provide examples of scenarios where it can be…
A: Web Assembly (Was) is a format for instructions that acts as a target for compiling programming…
Q: Discuss the role of network operating systems and their key features.
A: Network operating systems (NOS) play a role in managing and coordinating network resources enabling…
Q: Given the test example = 5, please answer the following questions: and a) Assume that the likelihood…
A: In the pattern recognition, various estimation and prediction techniques are employed to categorize…
Q: Create instances (objects) for the classes, involved in the "requesting a package to be delivered"…
A: All the questions 4.1, 4.2, 4.3 explanations will be answered in a single sequence diagramFour…
Q: Determine the big Θ for each and put the functions in their order from fastest time complexity to…
A: The given function n log n+n has a time complexity of Θ(n log n),indicating that its growth is…
Q: Code the promts in python language: 1.Assume list1 is a list of integers. Write a statement that…
A: Dear student, you have asked multiple questions in a single question. As per our guidelines, experts…
Q: Explain the concept of cookies in web technology and their use in maintaining stateful interactions…
A: In web technology, cookies are small pieces of data stored on a user's device by their web browser.…
Q: Explain the significance of feedback in a dynamic system model.
A: When it comes to system models feedback plays a role in maintaining stability, improving performance…
Q: XYZ Company Case XYZ is a large organization well known for their consumer products and the…
A: Code inspection, or code review, is pivotal in XYZ Company's e-commerce platform development. Given…
Q: Define a system model in the context of computer systems.
A: In computer science, a system model is a simplified representation or description of a computer…
Q: Explore the concept of exokernels and their potential applications in modern computing.
A: The term modern computing describes the state of computing today, which is marked by sophisticated…
Q: Discuss the concept of pipeline hazards and provide examples of different types of hazards that can…
A: Pipeline Hazards A pipeline is a technique where the processing of multiple instructions overlaps to…
Q: Explore the challenges associated with scaling WANs and propose potential solutions
A: When it comes to expanding Wide Area Networks (WANs) there are challenges that need to be…
Q: Examine the various types of non-volatile storage devices, such as SSDs, HDDs, and optical drives,…
A: Let's now examine the many types of non-volatile storage devices, including solid-state drives…
Q: Provide full C++ Code: Your code must have the following three files: Playlist.hpp - Class…
A: In this question we have to write a C++ program for printing the txt file songs in node and timings…
So in my google drive, what does gmail represent? Does it show how many gmails are currently in my account? Does it show how many messages I've sent? what does it show?
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Please check google drive for the question... There shouldn't be any plagiarism. Please don't submit the answer from chegg or others platform! Do it by yourself. Please answer the whole question (Discrete mathematics)https://drive.google.com/file/d/10go7EAsOuYalg0sUbhkKcI9Gu3-kBF3L/view?usp=sharinghttps://cleveronly.com/brainbucket/index.php?route=common/home Navigation bar Desktops Create scripts for test cases: Opening PC will show all PCs. If there are no PCs available, then the message "There are no products to list in this category." is displayed Opening Mac will show all Macs. The number of items should match the number in the dropdown option: Clicking on all desktops will show available desktops.TOPIC: It is questing of the foundation of computing This is for the Reference (https://drive.google.com/file/d/1PTXr2EHHUpfudoaEYE_Xtc2R9lJLtLmr/view?usp=sharing)
- 4. which of the following is false concerning the cryptographic keys associated with an APK? Select one: a. Keys have a lifetime b. An app's initial APK upload to the Google Play app store and all subsequent update uploads must be accompanied by the same key c. There are advantages to using the same key for all your apps d. A key is not required to install debug build variants on an emulator e. An advantage to using Google Play App Signing is that losing your upload key does not compromise your app signing keyandroid studio question use java ( API 26 :Android 8.0(Oreo) ): You can modify this code or write a new code https://drive.google.com/file/d/1ZhbEY38gYNuaH2yARMDINk0qOsZGBc55/view?usp=sharing ___________ Create Android App that manipulate the use of Database . The App enables user to add and delete students to database. Students information are [stID, stFName, stLName, stMajor, stGPA,stPhone ]. Mandatory information about the user all of them except stPhone. The App allows user to do the following: 1-Add student Button: will display new fragment that includes required information about students. The fragment includes save and cancel button. once the user entered the required details and save it, then it will show a toast message that a new user has been added.Cancel, shows toast message that the operation has been canceled. 2-Delete First Button: will delete the first student in the list.Toast message should be displayed to show the status 3-Delete All: will delete all students stored…Introduction Portfolio Assignment Use this zip file https://drive.google.com/file/d/1P5-FvqTohUa1zw7-dc-2O159rIrrQOON/view?usp=sharing This paper will be in APA version 7 format. Why Windows Registry is important in Computer Forensics Body Choose 10 Windows Registry Key/Value pairs from Windows 10 For each Key/Value pair provide the following Why this is important in Computer Forensics. Provide an example from the registry files provided with this assignment (See Above URL). References are required Primary references are preferred Secondary references are acceptable when Primary references are unavailable 10 registry keys 10 pictures of those keys in a viewer 10 descriptions of how those keys are useful Introduciton Conclusion Title Page References Should be around 12-14 pages as counted in MS Word including title and reference pages. APA will be enforced.
- QUESTION 1 Which of the following can be used to deploy UWP apps? a. Group Policy b. MSI files c. The setup.exe file d. Microsoft StoreWhere could information be acquired from a browser which is opened in the 'private' mode? O a. Internet Cache and Temporary files O b. Live memory O c. It is impossible to gather any information if a browser is opened in the 'private' mode O d. Browsing history Oe. CookiesQuestion 15 kk .How to get the pdf file path from uri like this(Uniform source indentifer) like in android 10/11/12 /storage/emulated/0/Download/pdfchoos.pdf Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
- True or False? - S3 provides settings for access points, buckets, and accounts to help with the management of public access to Amazon S3 resources. a. True b. FalseTask 1: Demonstrate how to install some user and system applications such as firefox, and Dolphin file manager) is user applications and (nmap, and conky) as administrator applications. Task 2: Install, configure Samba service and demonstrate how to connect to your server from remote computer. Task 3: Install, configure Web Server and demonstrate how to browse a simple website hosted in your server. You may deploy a simple website (or web application) – from the Internet, in your server. Task 4: Install, configure FTP Server and demonstrate how to browse files hosted in your server.I need help installing / understanding myphpadmin for mac and if i need to install wamp aswell. Also how to create a database from the code below

