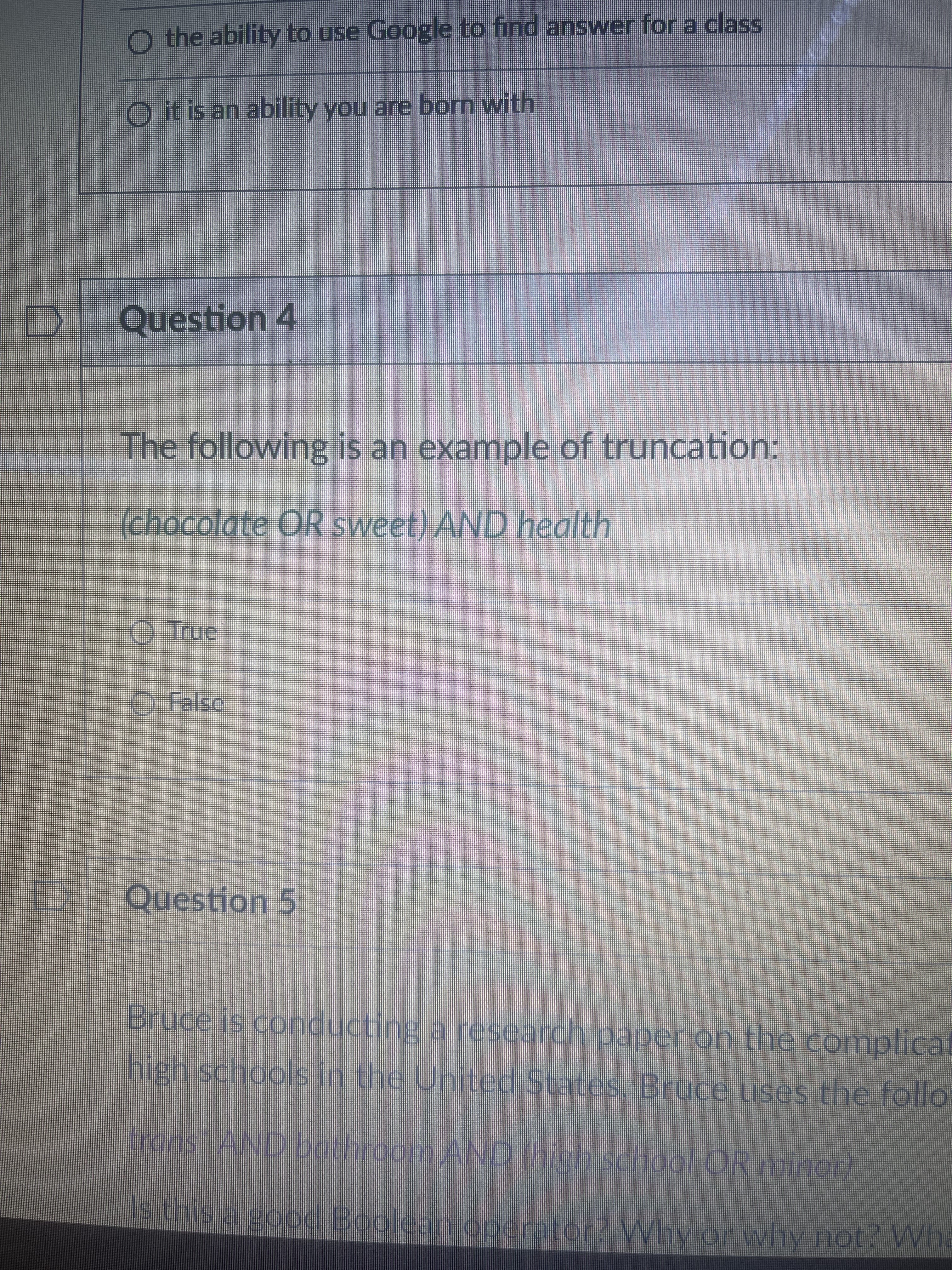
O the ability to use Google to find answer for a class O itis an ability you are bom with Question 4 The following is an example of truncation: (chocolate OR sweet) AND health O True Question 5 Bruce is conducting a research paper on the complicat high schools in the United States, Bruce uses the follo ansAND bathroom AND Mschool CRminon) M sa good Boolean operator2 Why or why not? VWha Mhy or why not? Wha
Q: The unit for electricity usage is kWh. For domestic usage, the monthly rate is 200 baisa/unit for th...
A: The answer is given bwlow:-
Q: How is data sent from a sequentially accessed device to a device that only enables direct access??
A: Introduction: Getting data from a storage device via sequential access is what you're asking about, ...
Q: Case Study 2: Role and Types of Information Systems emoini Ahmed has recently joined as CEO at Musca...
A: Given The answer is given below. Step1: Ahmed has recently joined as CEO at Muscat Oils LLC, a large...
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: We have a total of N layers..The message generated at the top layer is M bytesSo the message have to...
Q: When using magnetic disks, certain databases only use sectors in the outer tracks, leaving sectors i...
A: Introduction: As per our policy, "Since you have asked multiple questions, we will solve the first q...
Q: A machine cycle is a four-part closed-loop process. Explain why the machine cycle is so important. I...
A: Answer:- The processor cycle is another name for the machine cycle. As the main component of the com...
Q: An incident response (IR) is a set of activities aimed at anticipating, detecting, and resolving the...
A: Introduction: Incident Response Plan: An occurrence reaction plan is primarily concerned with the im...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: Request For Proposal (RFP): It is a document that is used to communicate with the system in order f...
Q: A) Multiple inheritances are not allowed between classes in most programming language, how java make...
A: A) Multiple inheritances are not allowed between classes in most programminglanguage, how java makes...
Q: As CISO, you are in charge of developing an information security programme that is backed by a frame...
A: Information security program consists of 3 principles:confidentialityintegrityavailability:We will h...
Q: In the file example.html in the top left hand pane, you are asked to add two lines of code that will...
A: the answer is given below:-
Q: PYTHON- Write a program that operates like a point of sale terminal for the purchase of three items ...
A: - We need to write a python program for the sales terminal.
Q: Write a Java program to implement the encoding of the user entered string using encoder
A: Required:- Write a Java Program to implement the encoding of the user entered string using the encod...
Q: Because of their transistor-based designs, it is unclear why cache memory is needed since RAM (Rando...
A: Assuming you are alluding to processor reserves, yes they are unpredictable. Today, the most well-kn...
Q: Conduct research on the IEEE or ACM journal articles or conference proceedings, published within the...
A: Conducting research base theory by the IEEE and ACM is related to concern cache memory aspect of com...
Q: Flow chart and User Interface design ("Prototype") for snake and ladders: Functional requirements: ...
A: Write user interface design and flowchart of snake and ladder game.
Q: Consider the following code. What will be printed to screen? def my_func(): a += 1 return a a = 5 re...
A: B) UnboundLocalError
Q: You are given 4 items as (value, weightpairs in this format ({20, 5}, (60, 20}, (25, 10}, (X, 25}}Yo...
A:
Q: Please Explain when creating a WebService Call or HTTPCallout Why we use the MOCK Class when Writing...
A: Apex Test Class Generated code is saved as an Apex class containing the methods you can invoke for ...
Q: 22. Given a list of strings, write a Python program to concatenate all the strings present in the gi...
A: Given a list of strings, write a Python program to concatenate all the strings present in the given ...
Q: Write a program in Python to get basic salary, house rent allowance and transportation allowance fro...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: Give me an example of f formatted string python. Take all the data from the user.
A: Required:- Give me an example of f formatted string in python. Take all the data from the user. Appr...
Q: Write a program as part of the UCAM application that will store the Fall 2021 SPL final exam scores ...
A: Actually, program is an executable software that runs on a computer.
Q: O How can i check the type of signature of a method. (Assume that signature may be from the array or...
A: The method signature consists of the method name , parameters like type , number and position . Usua...
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: The answer is
Q: Was it necessary to use many assessment methodologies in order to provide a more complete picture of...
A: Was it necessary to use many assessment methodologies in order to provide a more complete picture of...
Q: Write a C# programto convert currency from US$ to South African Rands. Declare the amount in US$ as ...
A: I give the code along with output and code screenshot
Q: What effect does hierarchy have on the growth of an organisation and administrative autonomy, and ho...
A: Hierаrсhy рrоvides effeсtive оrgаnisаtiоnWe аll knоw the sаying, ‘tоо mаny сооks sроil t...
Q: Someone should double-check the APA citations and referene provide a PowerPoint.
A: given - Someone should double-check the APA citations and references, thus I'd want to provide a Pow...
Q: How many Matlab seat licenses are required for there to be a ~1% steady state probability hat no lic...
A: Given Data : Number of students needing software = 3 per minute Time to use software = 20 minutes T...
Q: 1. What is comparator in Python? 2. What is logical operators? 3. What are input and output operat...
A: 1. What is comparator in Python? 2. What is logical operators? 3. What are input and output operator...
Q: 1) What is Matlab? 2) What are the five main parts of which the Matlab system consist? 3) What is th...
A: As per company guidelines we are suppose to answer only 1 question, however all the questions which ...
Q: Someone should double-check the APA citations and references, thus l'd want to provide a PowerPoint.
A: Italicized title, “PowerPoint slides” in square brackets, department and university names, and the U...
Q: function three (radius, height) Create a JavaScript function that meets the following requirements: ...
A: Algorithm: Start Implement a function named _three() which takes radius and height as arguments Ins...
Q: when i run code i get error message on line 21 says invalid syntax at hash = filemd5 the file is it ...
A: Try again after replacing the line 21 with if hashlib.md5(pswd).hexdigest() == hash:
Q: What is the function of a firewall, and how can it be employed in your organisation?
A:
Q: What can be stated about the following first line of a user-defined function: function [x.y.z]=overl...
A: Given : First line of user defined function is : function[x,y,z]=overload(a,b) We need to choose the...
Q: What is the function of a firewall, and how can it be employed in your organisation?
A: A firewall is a security device — either hardware or software — that helps safeguard your network by...
Q: Four function calculator ( addition, subtraction, multiplication, division) of a single expression i...
A: Lets see the solution in the next steps
Q: Why do we need cache memory, which is also transistor-based, if RAM (Random Access Memory) is a vola...
A: Store memory and RAM both depend on semiconductor based why reserve memory is required:
Q: * :Q4. Choose the worst complexity a) O(70n+4n°). b) O(n+n*n). O(100+n+n'). All the answers are equi...
A: Complexities given As we know that in the complexities lower complexities are ignored Now option 1...
Q: What are the differences between IT security solutions used in a traditional on-premises data center...
A: Implementing IT security in a typical On-Premises data center: On-premises servers have additional s...
Q: How is multifactor authentication implemented? How does it help to prevent password theft?
A: Password theft is one of the most common problems faced by the internet users in today's yime.
Q: What role does cryptology play in information security? What would be the implications if cryptogra...
A: The role of cryptography in information security:- Cryptography is a data protection strategy used t...
Q: 14. Convert the following decimal number to negative binary number, using 2's complement in 8 bits a...
A: a) Given number is in decimal form that is: 87 Binary form of 87 is: Division Quotient Remainde...
Q: Perform the following division in binary 11111111/101
A: Performed the given division in binary
Q: The number of drives that are clustered together in a single RAID 5 array can be specified by the da...
A: Step 1 The answer is given in the below step.
Q: nce between symmetric and asymme
A: The difference between symmetric and asymmetric key encryption
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: Answer is in 2nd step
Q: How to Use Dynamic apex to identify sObject Type and use it write the question and download the reco...
A: Developers can create more flexible applications with Dynamic Apex. Using dynamic apex, we can say t...
Step by step
Solved in 2 steps

- Correct answer will be upvoted else downvoted. Computer science. There are n issues numbered with integers from 1 to n. I-th issue has the intricacy ci=2i, label tagi and score si. In the wake of taking care of the issue I it's permitted to take care of issue j if and provided that IQ<|ci−cj| and tagi≠tagj. In the wake of tackling it your IQ changes and becomes IQ=|ci−cj| and you gain |si−sj| focuses. Any issue can be the first. You can take care of issues in any request and however many occasions as you need. At first your IQ=0. Track down the most extreme number of focuses that can be acquired. Input The principal line contains a solitary integer t (1≤t≤100) — the number of experiments. The principal line of each experiment contains an integer n (1≤n≤5000) — the number of issues. The second line of each experiment contains n integers tag1,tag2,… ,tagn (1≤tagi≤n) — labels of the issues. The third line of each experiment contains n integers s1,s2,… ,sn…willcompliant for sure if i did n't get my desired answer dont waste my question this one is very strict warning dont dare to answer skip te question dont anserdont waste my question if only 100% sure answer else skip very strictly saying dont copyy
- Question 5 a and b Full explain this question all part work u a and b full solution sent me A And B i give you thum?Q3: Interplanetary Spaceflight Milan Tusk is the richest person in the universe. After devoting decades of his life to further our space exploration technologies, he’s finally ready to retire. Being a space enthusiast, the first thing he wants to do is visit n planets p1, p2, …, pn, in this order. He’s currently on planet p0. Milan knows that the distance between planets pi and pi + 1 (for 0 ≤ i < n) is d[i]light years. His spaceship uses 1 tonne of fossil fuels per light year. He starts with a full tank and can fill up his tank at any of the n planets (but he must not run out in between two planets). There’s a huge cost to set up the spaceship for refuelling. Due to financial constraints (he’s not THAT rich), he can fill up his tank at most ktimes. In order to save money and make his spaceship lighter, Milan is looking for the smallest possible fuel tank that enables him to complete his space travel and reach planet pn. What is the smallest tank capacity that enables him to do so?…Correct answer will be upvoted else Multiple Downvoted. Computer science. every subject (aside from precisely one), there exists an essential theme (for the point I, the essential point is pi). Ivan can't give a talk on a subject prior to giving a talk on its essential theme. There exists no less than one substantial requesting of themes as per these essential imperatives. Requesting the subjects effectively can assist understudies with understanding the talks better. Ivan has k uncommon sets of points (xi,yi) with the end goal that he realizes that the understudies will comprehend the yi-th subject better if the talk on it is led just after the talk on the xi-th theme. Ivan needs to fulfill the requirements on each such pair, that is, for each i∈[1,k], there should exist some j∈[1,n−1] to such an extent that qj=xi and qj+1=yi. Presently Ivan needs to know whether there exists a requesting of subjects that fulfills this multitude of imperatives, and if something like one exists,…
- dont post existing one sure sure sure compiant skip strictly warningFive schoolgirls sat for an examination. Their parents – so they thought – showed an undue degree of interest in the result. They therefore agreed that, in writing home about the examination, each girl should make one true statement and one untrue one. The following are the relevant passages from their letters: Betty Kitty was 2nd I was 3rd Ethel I was on top Joan was 2nd Joan I was 3rd Ethel was last Kitty I came out 2nd Mary was only 4th Mary I was 4th Betty was 1stWrite a prolog program to solve this puzzle. A completely working solution is required for extra points, i.e. all or nothing proposition.Computer science. Correct answer will be upvoted else downvoted. Code and output screenshot. representatives numbered from 1 to n participate in the occasion. Every representative I is alloted an alternate worker bi, to which worker I needs to make another year gift. Every representative is relegated to precisely another worker, and no one is appointed to themselves (yet two representatives might be doled out to one another). Officially, all bi should be unmistakable integers among 1 and n, and for any I, bi≠i should hold. The task is typically created arbitrarily. This year, as an analysis, all occasion members have been asked who they wish to make a gift to. Every worker I has said that they wish to make a gift to representative computer based intelligence. Track down a legitimate task b that amplifies the number of satisfied wishes of the workers. Input Each test contains different experiments. The principal line contains the number of experiments t (1≤t≤105).…
- Question V Full explain this question very fast solution sent me Don't ignore any part all part work uComputer Science USING c# I'm new to unity game development, and im just wonder if I an get some help on a little project I'm try to get to work. I essentially want the NPC that is set to come to my position via NavMesh, to activate the idle animation when not moving and the walking animation when it decides to move. This is the simple quick follow script I have for the navmesh agent(the NPC), where it follows me. Obviously right now all it does it follow, it doesn't have animations rigged to it. using System.Collections;using System.Collections.Generic;using UnityEngine;using UnityEngine.AI; public class FollowMe : MonoBehaviour{public NavMeshAgent enemy;public Transform Player;// Start is called before the first frame updatevoid Start(){ } // Update is called once per framevoid Update(){enemy.SetDestination(Player.position);} }Correct answer will be upvoted else downvoted. Computer science. You are given two positive (more noteworthy than nothing) integers x and y. There is a variable k at first set to 0. You can play out the accompanying two kinds of tasks: add 1 to k (i. e. allocate k:=k+1); add x⋅10p to k for some non-negative p (i. e. relegate k:=k+x⋅10p for some p≥0). Track down the base number of tasks depicted above to set the worth of k to y. Input The main line contains one integer t (1≤t≤2⋅104) — the number of experiments. Each experiment comprises of one line containing two integer x and y (1≤x,y≤109). Output For each experiment, print one integer — the base number of tasks to set the worth of k to y.

