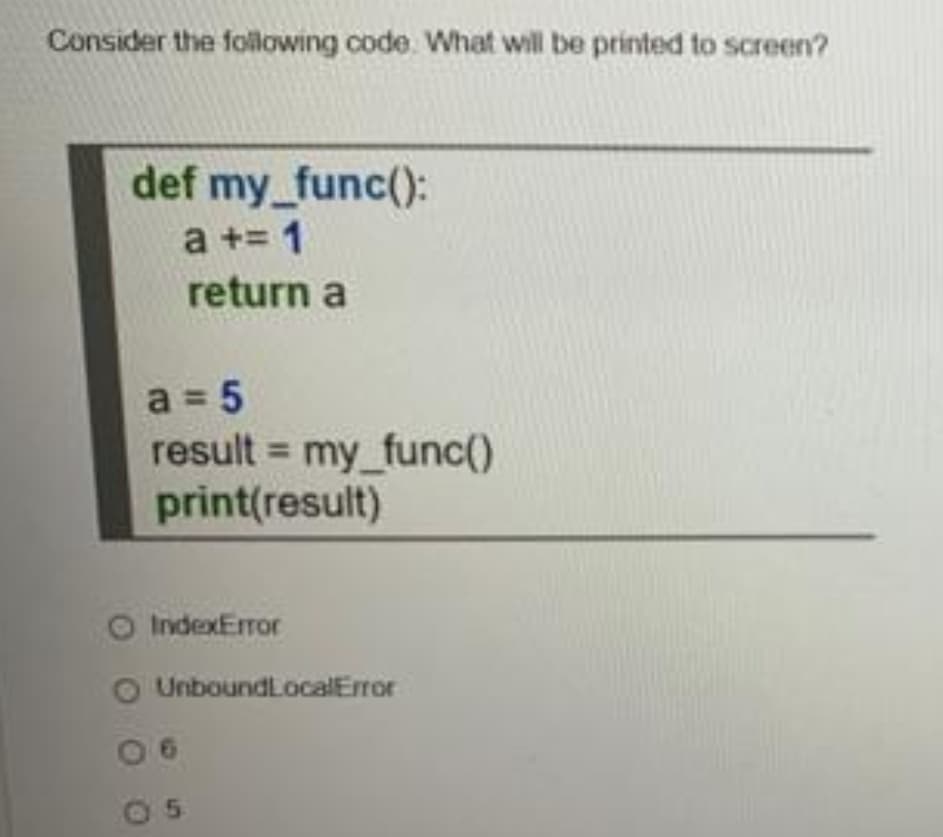
Consider the following code. What will be printed to screen? def my_func(): a += 1 return a a = 5 result = my_func() print(result) O IndexError UnboundLocalEror
Q: Write a function that takes a match, mismatch and gap score, as well as two ungapped sequences as in...
A: This is a problem of Sequence Alignment so first off all you need t see the defination of this kind ...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: A request for proposal (RFP) is a document that asks vendors to submit proposals for hardware and sy...
Q: What is the purpose of routing, and how does it work? Differentiate between two commonly used routin...
A: Your question is about routing which is given below :
Q: Give regular expressions that describe the following languages containing the set of all strings ove...
A: A.) { w | w a word in which 3rd symbol from RHS is ‘a’ and 2nd symbol is 'b' }. aaa , aab , aaab , a...
Q: Why do compilers perform optimizations in code and why do compilers use Abstract Syntax Trees instea...
A: Given: Why do compilers make code optimizations and why do they utilize Abstract Syntax Trees rather...
Q: Input given: interval[0,1] , divide the interval into 10 segments. Then output "x' for each segment....
A: We have given a interval :Input given: interval[0,1] ,we have asked to write a C code which will div...
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: Introduction: The arrangement of a network's connections and nodes, or its topology, is referred to ...
Q: If you're conducting user research, why not separate the overall design into multiple user viewpoint...
A: Introduction: If you're conducting user research, why not separate the overall design into multiple ...
Q: What do you consider to be critical infrastructure?
A: Critical infrastructure: Critical infrastructure play a vital role in supporting modern society. It ...
Q: How can using a model, rather than a tangible thing or circumstance, allow you to examine and explor...
A: Introduction: There are two types of models: physical models (such as students who inspire their pee...
Q: Write a C# program to fin
A: Coded using C#.
Q: Add and multiply the following numbers without converting them to decimal. (a) Binary number 1011 a...
A: a) here 1+0=11+1 = 0 with carry 1 as 1+1=2(10) so using that while adding we get 10000 = 16 1011=...
Q: Filter programmes such as sed and awk are often used to format data in pipelines. Is this a true or ...
A: Explaination As the name suggest filter programs . We already know what is filtering right ? Filter...
Q: What does the first compound notation mean?
A: Introduction: MicrocontrollerMicroprocessor8085. Signed integers may be represented in computers in...
Q: Write the final output generated by the following program: b. #include #include void main() { int...
A: This question comes from Programming Language in C which is a paper of Computer Science. Let's discu...
Q: Develop a hypothetical architecture with illustrative instruction and data formats, instruction sets...
A:
Q: What are the foundations for considering edge computing and cloud computing in an loT system? What i...
A: Edge computing, a strategy for computing on the location where data is collected or used, allows IoT...
Q: Using three iterations of the Bisection method to determine the zeros of the f(x) within the interva...
A: Here in this question we have asked to use bisection method to determine the zeros of function F(x)=...
Q: convert temperature specified in Celsius in one class into Fahrenheit in another class. In c
A: According to the question we have to write code to convert temperature specified in Celsius in one c...
Q: Exercise 1: Write a program to calculate the volume and surface area of a sphere from its radius, gi...
A: For the given problem, we need to implement a program that calculates volume and surface area of a s...
Q: Cache memory is important in today's computers. Explain how cache memory works and why there was no ...
A: Cache Memory Introduction: Cache memory is a chip-based computer component that retrieves data incre...
Q: Discuss possible countermeasures against Man-in-the-Middle (MITM) attacks that intercept wireless cr...
A: A man in the middle attack is a kind of eavesdropping assault in which attackers intercept communica...
Q: when i run code i get error message on line 21 says invalid syntax at hash = filemd5 the file is it ...
A: arrangement
Q: What's the difference between symmetric and asymmetric key cryptography?
A:
Q: What factors influenced the evolution of computer security into current information security?
A: Introduction: Computer security, alternatively referred to as cybersecurity or information technolog...
Q: Label the Recursion Requirements. int fact (int n) 1fin--1)
A: Given :- label the recursion requirements
Q: Network Address: 192.70.10.0 Number of needed hosts: 8 Default subnet mask: New subnet mask: Number ...
A: Answer : Given data : Network address : 192.70.10.0 Number of needed hosts : 8 Note : The la...
Q: Write a simple C# console application to accept the item name and item price. The program should cal...
A: Here is your code with an output .
Q: The number of drives that are clustered together in a single RAID 5 array can be specified by the da...
A: RAID is defined as a collection of redundant independent discs. It is a virtualized data storage env...
Q: 1001110, + 10101012
A: Answer : The addition of two binary numbers are as follow : 1 0 0 1 1 1 0 1 0 1 0 1 0 1 ----------...
Q: The touch command can be used to:
A: Your question is about touch command can be used to
Q: What exactly is multifactor authentication and how does it work? What role does it play in password ...
A: Introduction: Multifactor authorization is a type of security that requires the use of multiple secu...
Q: Is backup the responsibility of the database administrator or the database user? a person who manage...
A: Data is the new oil in this 21st century and hence backup is very important in case of databases.
Q: What are the benefits and drawbacks of caching disc write operations?
A: Caching disc write operations has many benefits and drawbacks.
Q: As CISO, you are in charge of developing an information security programme that is backed by a frame...
A: Answer Information security program is based on following 3 principles: confidentiality availability...
Q: In today’s IT environment organizations have many different types of databases to choose from. Two o...
A: Relational database and data warehouse both store data. They difference lies in the purpose for whic...
Q: Need help wit
A: Coded using C language.
Q: 1. Go to https://imsdb.com and find any movie script of your choice. 2. Copy one or two paragraphs f...
A:
Q: 6. Given the following directory tree structure, write the full command you can use to move the “dum...
A: For the given question, we need to write a command that moves the "dumpling" directory to "asian_foo...
Q: table a - menu of oceanside burger and fries in vb.net programming
A: ALGORITHM:- 1. Print the menu as given in question statement. 2. Use writeline() method to write on ...
Q: 8. Why does the following cell return an error? U t- (1, 2, 3, 4, 5) [-1) -6 Typetrror Traceback (mo...
A: Introduction: Tuple: It is a datatype in python that is used to group the data. It is immutable in n...
Q: When using magnetic disks, certain databases only use sectors in the outer tracks, leaving sectors i...
A: Introduction: As per our policy, "Since you have asked multiple questions, we will solve the first q...
Q: Please Explain when creating a WebService Call or HTTPCallout Why we use the MOCK Class when Writing...
A: The answer is given below:-
Q: Rewrite the program with alittle bit of changes in this code
A: C programming is a general purpose, course of action computer programming language supporting struct...
Q: he knowledge of an expert system is given as follow: male(john). male(sam). male(peter). male(david...
A: Find a possible solution below.
Q: EXPLAIN THE FLOW OF THE MAIN CODE (THE CODE IS ALREADY CORRECT YOU JUST NEED TO EXPLAIN THE FLOW) #...
A: The code is written in C++.
Q: What is the difference between using +/- versus when setting file permissions? Is there any benefit ...
A: For setting file permission in linux terminal in operating systems , we use these commands:- Lets d...
Q: A approach that has not been tried is ineffective. Recognize the many testing approaches that may be...
A: Description of an employment test:- Employment tests are usually standardized measures designed to ...
Q: C programming Develop a proxy HTTP server that can accept HTTP requests from clients and convert th...
A: I have answered this question in step 2.
Q: Give a minimal state DFA that recognizes the language of strings which encode natural numbers in dec...
A: There are only three choices when dividing an integer by three. Either 0 or 1 can be used as the rem...
Step by step
Solved in 3 steps with 1 images

- Not allowed to add variables in brackets next to originIndex * @return index of the point that is closest to the origin, which is (0, 0) In * case of a tie, return the lowest index */ public int closestToOriginIndex() {Simple Student Management System Build the following app using Python Tkinter library. Using this app, user can • add student information • view all students • search student(s) by name • remove student by id Add • First name, last name, date of birth cannot be blank while adding a specific student information. • However major can be blank, which gets set to "Undefined" if left out blank. • Student Id is automatically generated by the program (ex: 1001, 1002, 1003, 1004 ….) If the user keeps a mandatory field blank (ex: First name) and presses "Add Student" button, it displays the following message box: first name is required If the user successfully enters all the necessary information and presses the "Add Student" button, it displays the following confirmation message box: student added View All When the user presses the "View All" button, it displays all the student’s information (Id, First name, Last name, Date of birth, and Major) in a nice formatted way. Example below: • Must…Create a CompanyDriver application. You will have at least 2 methods in this application, Create a menu. main() – setCompanyData() - this reads the data from the file (call the file CompanyData.txt) displayCompanyData() - this displays the data to the screen, calling the toString() method of all objects //sortData() - This will sort the data by choice either name of stock or current price / This will be part of lab 7. //Create an arraylist of the 10 Company objects and display them. You may want to make this a method. This will be part of lab 7 Create an array of the 10 Company objects and display them. You may want to make this a method. Read the data from a file (see below) Call each method as described above CompanyData.txt (the data is set up like this: (Company name, lastprice, current price - copy and paste this into a .txt file) GoPro, Inc.10.7113.69Starbucks59.5358.46JC Penney7.7310.78Amazon531.07576.32Adams Resources and…
- Which of the following statement(s) are true for the above code? Group of answer choices the code allocates space for a local variable and a global array the code allocates space for a local variable and a local array The code utilizes the index register the code utilizes the stack pointer the code uses 5 different addressing modesWrite an Add method that adds the contents of the decPrice variable to the lstPrices control.Write a program which should handle books information for a book shop. It should be able to handle atleast 100 records. Your program should store following information against a book. Book Id (you may use index number as book ID) Book Code Book Name Author Name Publish Date Price No of copies in hand No of Copies sold Initialize 10 Books and initialize remaining with 0 and spaces. Create a menu, as given below, which should use above information to perform selected action from the given menu on the screen Add book (One book will be added. User will enter book id i.e. index number Record will be placed if code at that index is 0) Display book (Display Books in tabular format with nonzero codes only) Delete book (Place an empty record with 0 code and spaces at the selected index) Search book Sale book (First locate the book Id and check if code is not 0 then update No of Copies in hand and No of Copies sold accordingly) Exit Your assignment will be evaluated on the following basis:…
- Help me fix my c programming error. #include <stdio.h>#include <stdlib.h>#define _CRT_SECURE_NO_WARNINGS void addContact();void viewContact();char firstName();char lastName();char phoneNumber[10]; int main(){int selection;printf("\n\t---Contact Mangement System--");printf("\n\t[1] Add New Contact");printf("\n\t[2] View Contact");printf("\n\t[3] Help");printf("\n\t[4] Exit");printf("\n\tEnter Your Selection");scanf("%d", selection);switch (selection){case 1:addContact();break;case 2:viewContact();break;case 3:exit(1);break;default:printf("Enter Your Selection");main();}}void addContact();{printf("Enter First Name: ");scanf("%s", firstName);printf("Enter Last Name: ");scanf("%s", lastName);printf("Enter Your Phone Number: ");scanf("%s", phoneNumber);if (strlen(phoneNumber) == 10){FILE* fp;fp = fopne("contacts.txt", "w");fputs(firstName, fp);fputs(lastName, fp);fputs(phoneNumber, fp);printf("\n\tContact Added");fclose(fp); } main();} void viewContact(){system("cls");char…/** * Returns {@code true} if a given cell of the board is filled and {@code false} * otherwise. The top row (corresponding to 'a' moves) is row 0. The leftmost * column (corresponding to 'v' moves) is column 0. * * @param row the row of the cell being querried * @param col the column of the cell being querried * @return {@code true} if the cell is filled and {@code false} otherwise. */ public boolean isFilled(int row, int col) { throw new RuntimeException("Not implemented"); } The board is 5 X 5.Calculate 2nd element of ??=[?,??,??,??] divided by 1st element of ??=[?,??,??,??]. Use two def and return commands instead of indexing. Print the result and store it as a variable (float or integer).
- Evaluate the following expressions a. foldFromLeft(minus, 6, map(RemoveTwo, [3, 4, 8])) b. foldFromRight(minus, 6, map(RemoveTwo, [3, 4, 8]))Please fix this JAVA code so that it will not overwrite the contents of the file every time I click on a row @Overridepublic void valueChanged(ListSelectionEvent event) {File file = new File("sample json file");int row = table.getSelectedRow();JSONObject obj = (JSONObject) jsonArray.get(row);ObjectMapper mapper = new ObjectMapper();mapper.enable(SerializationFeature.INDENT_OUTPUT);try {JsonGenerator g = mapper.getFactory().createGenerator(new FileOutputStream(file));mapper.writeValue(g, obj);g.close();} catch (IOException e) {throw new RuntimeException(e);}}});How many bytes does creating this template reserve in memory? Struct phone{ char brand[51]; char model[101]; float prices[6]; float screenSize; int ramSize; }







