Solve by using MS Excel find the density at 21.6 degrees
Q: The concept of cloud printing has been established.
A: Introduction: Cloud printing is a kind of cloud computing that makes it possible to access printers…
Q: 5 cents (Z) 10 cents (Y) 25 cents (X) 35 cents (W)
A: Answer is given below-
Q: Computer Science One of the most common assumptions is that “defects are mostly found during the…
A: Introduction: One of the most common assumptions is that “defects are mostly found during the…
Q: Question 1: Implement the following arithmetic in assembly language, using 32-bit signed operands:…
A:
Q: Examine the following for statements and determine how many times each loop will be executed. (a)…
A: As per Bartleby rules, we are answering the first 3 questions. Please find the solution below along…
Q: Consider Lamport's OLP method and its security in light of the significance of the hash function's…
A: Introduction: This is the Lamport one-time password algorithm: Louis Iacona presents an OTP…
Q: Suppose that the data mining task is to cluster points (with (x,y) representing location…
A:
Q: Defining the basics of test-driven development You may use it as a teaching tool in many ways
A: Please find the answer below :
Q: t has not yet been introduced to the public, but it is being release to a select a few modul a…
A: Option D could be the answer. Gamma test is the final stage of testing process generally follows…
Q: Write a class having two private variables and one member function which will return the area of the…
A: The asked C++ program code is coded in the next step and is explained by using comments.
Q: provide a moral component for information systems?provide a moral component for information systems?
A: Start: The components of an information system are characterised as being five in number. Computer…
Q: a) Write a function to get the value of the Në node in a Linked List. [Note: The first (N=1) item in…
A: Program: class Node: def __init__(self, data=None): self.data = data self.next = None def…
Q: What is data sharing? What is a data subject?
A: Answer:
Q: To put it another way, what exactly is "parameterized testing"?
A: Introduction: JUnit, the most recent version of JUnit, has been updated to include a number of new…
Q: What is an information system's analysis and design process?
A: Introduction : Information systems analysis and design is a technique used by firms ranging from IBM…
Q: What's the difference between direct DDoS assaults and reflector/amplifier attacks?
A: Introduction: A direct denial of service attack (DDoS) may be said to be direct when it indicates…
Q: Does each operating system have its own own partitioning?
A: Introduction Hard drives may be partitioned in a way that operating systems (OS) and file systems…
Q: What traits are necessary for a software test engineer to succeed?
A: Introduction: A software tester is someone who looks for bugs, defects, or other issues in software…
Q: 1. Explain how social media can be a force of both goof and evil. Give specific examples. 2. How…
A: "Since you have asked multiple questions I am solving them first for you if you need answer for the…
Q: What are the four main sorts of audiences that are taken into consideration, and how does the…
A: The Four Kinds of Audience: When attempting to persuade a group to take action through your speech,…
Q: C program in x86-64
A: Given :- In the above question, the C code is mention in the above given question Need to recreate…
Q: ethods of testing differ?
A: There are two types of Testing Manual testing Automated testing
Q: What does it mean to have a virtual private network?
A: What exactly is a virtual private network (VPN)?
Q: Create two examples of a list: one using bullet points and the other using numbered items.
A: To create a bullet points as list , you need to use unordered list. put <ul> and <li>…
Q: USE GANTT CHART FOR SHOWING SOLUTION SEE NEXT IMAGE FOR THE EXAMPLE OF NEEDED SOLUTION Given the…
A:
Q: Identify two benefits of using electronic mail to communicate in today's society as opposed to…
A: Introduction Electronic mail (email or email) is a method of exchanging messages ("mail") between…
Q: For my C project: Bus ticket reservation. I want to create a function and one txt file for Passenger…
A:
Q: s) Please encode the following Turning Machine to create an universal Turning Machine. a/a, R a/a, R…
A: Turing Machine∑ = {a,b} = {1, 11}T = {a,b,Δ} = {1, 11, 111}states = {q0,q1,q2,ha} = {1,11,111,1111}
Q: Choose a real-world situation with at least three sets of Venn diagrams. Explain why a Venn diagram…
A: Establishment: a real-life example of a Venn diagram with at least three sets For this case, a Venn…
Q: Is there a way to distinguish fact from fiction on the internet?
A: Introduction: Talking to specialists about what should or should be done in a scenario can be…
Q: In your perspective, is website hacking a problem for any of the following reasons?
A: Hacking: The act of gaining unauthorized access to a computer system or network of computers. This…
Q: Example 4 Write a program to convert a character named (char): 1) from small to capital letter 2)…
A: Answer:
Q: Describe Information system analysis
A: answer is
Q: What should you do if you delete a file by mistake and then decide you want it back?
A: Introduction: If you delete anything by mistake, the first thing you should do is look in the…
Q: Is there a reason we require system engineering? How can system engineering be used to improve…
A: Introduction Systems engineering is an interdisciplinary field of engineering and engineering…
Q: Provide an explanation of the five prerequisites for wireless LANS.
A: Wireless LAN Requirements: A wireless LAN must have high capacity, short distance coverage, complete…
Q: Please answer the 4 questions. Thank you for the help
A: In Step 2, I have provided answers for all questions-----------
Q: The process by which objects of c acquire the properties of objects class is known as
A: Introduction: The process by which objects of one class acquire the properties of objects of another…
Q: iple signals need to
A: Answer is multiplexer.
Q: Please define each of the words listed below. a) Artificial intelligence; b) an agent; c)…
A: (a) Artificial Intelligence: Artificial Intelligence studies making computers think like humans. It…
Q: Q1: Define a class named Person that contains the data fields for the first name and last name.…
A: let us see the answer:-
Q: How many distinct types of memory are there in computer architecture?
A: Introduction: Memory is a system or component in computing that stores data for immediate use in a…
Q: Why are interrupt handling systems so important for machines?
A: Operating system: An operating system (OS) is software that manages computer hardware and software…
Q: he Ghana health service requested for a machine learning model to detect the presence of a new…
A: ANSWER:-
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: Different testing methodologies are needed at different phases of the software development life…
A: Describing the necessity for different: test methodologies at various phases of software development…
Q: n multimedia to: guide user in navigatir ll of the above menti leliver information fo
A: Text is used in multimedia to: A guide user in navigating through application C. deliver…
Q: In what ways are they different from one other?
A: Start: Deep learning is a subset of machine learning that uses artificial neural networks and…
Q: Different testing methodologies are needed at different phases of the software development life…
A: Introduction: Defining the need for diversity: techniques for testing software at various stages of…
Q: Why is there a layer for networks if they're already connected?
A: Given: The primary goal of this layer is to transport packets from the source to the destination of…
Solve by using MS Excel
find the density at 21.6 degrees
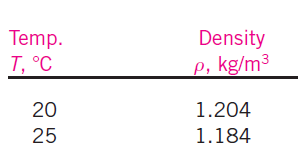
Step by step
Solved in 3 steps with 2 images


