Solve Question 1, 2, 3 showing detailly all the steps with including all explanations Answer Should be typewritten using a computer keyboard!
Solve Question 1, 2, 3 showing detailly all the steps with including all explanations Answer Should be typewritten using a computer keyboard!
Chapter4: Processor Technology And Architecture
Section: Chapter Questions
Problem 2PE: If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the...
Related questions
Question
Solve Question 1, 2, 3 showing detailly all the steps with including all explanations
Answer Should be typewritten using a computer keyboard!
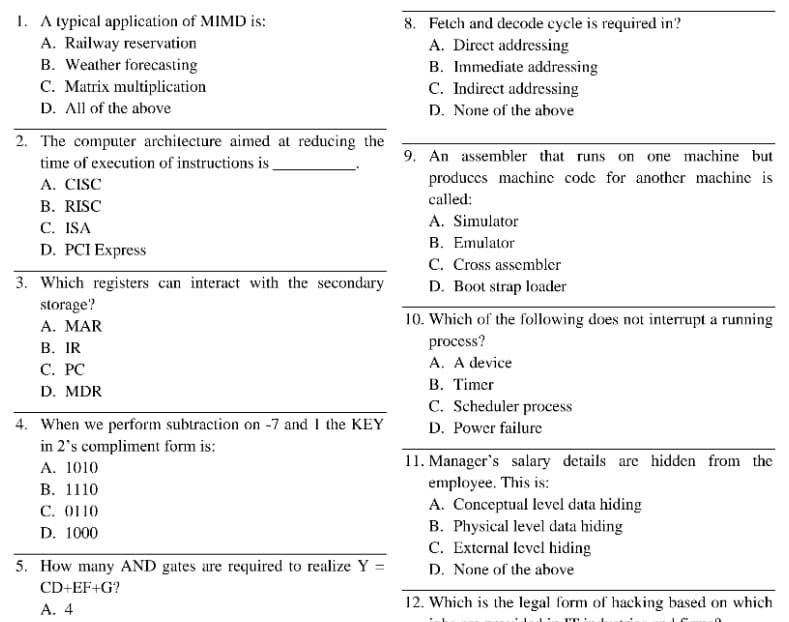
Transcribed Image Text:1. A typical application of MIMD is:
A. Railway reservation
B. Weather forecasting
C. Matrix multiplication
D. All of the above
8. Fetch and decode cycle is required in?
A. Direct addressing
B. Immediate addressing
C. Indirect addressing
D. None of the above
2. The computer architecture aimed at reducing the
9. An assembler that runs on one machine but
time of execution of instructions is.
A. CISC
produccs machine code for another machine is
called:
B. RISC
A. Simulator
С. ISA
D. PCI Express
B. Emulator
C. Cross assembler
3. Which registers can interact with the secondary
D. Boot strap loader
storage?
A. MAR
В. IR
С. РС
D. MDR
10. Which of the following does not interrupt a running
process?
A. A device
B. Timer
C. Scheduler process
4. When we perform subtraction on -7 and I the KEY
in 2's compliment form is:
A. 1010
В. 1110
C. 0110
D. Power failure
11. Manager's salary details are hidden from the
employee. This is:
A. Conceptual level data hiding
B. Physical level data hiding
C. External level hiding
D. None of the above
D. 1000
5. How many AND gates are required to realize Y
%3D
CD+EF+G?
A. 4
12. Which is the legal form of hacking based on which
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning