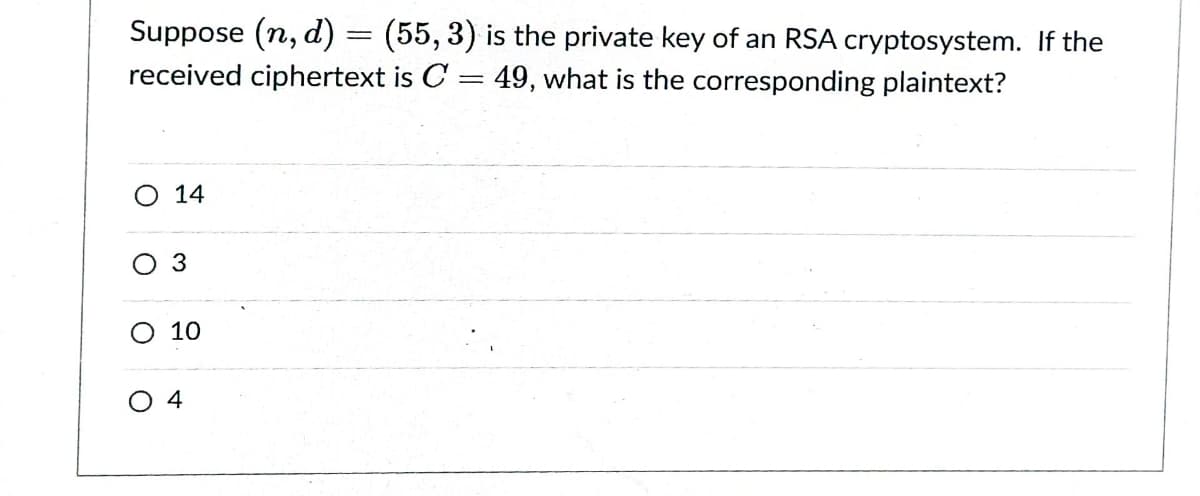
Suppose (n, d) = (55, 3) is the private key of an RSA cryptosystem. If the received ciphertext is C = 49, what is the corresponding plaintext? O 14 3 10 O 4
Q: Decrypt the message XUPPWFIDD which was encrypted using the athine cipher f(p) = (15p + 6) mod 26…
A:
Q: The following parameters are chosen to generate the public and private keys for the RSA…
A:
Q: Without using Calculator or other mechanical tools, find the Decryption function of the following…
A: Given encryption function is : fp=7p+3 mod26
Q: Suppose p = 5 and q RSA cryptosystem with public key (n, e) = (55, 7)? 11. Which of the following is…
A:
Q: Let's say that Alice and Bob are exchanging keys using Diffie-Hellman key exchange using…
A: Here, we have p=499 (which is a prime number) g=7 a=23 (which is a secret exponent of Alice) and b…
Q: Solve the following problems: (a) How many ways can a store manager arrange a group of 1 team leader…
A:
Q: Exercise 9.2.26. Given that 3 4 (;). A = and b = 2 3 (a) Use the encryption function f(p) = Ap + b…
A:
Q: Alice wants to send to all her friends, including Bob, the message “SELL EVERYTHING” so that he…
A:
Q: Hill Cipher for m=2, then correct key is
A: This is a problem of Cryptography, Number Theory, and Modular Arithmetic. Therefore it is a problem…
Q: What is the Plaintext of the following Ciphertext, based on Caesar cipher algorithm, if the KEY=5?…
A:
Q: 2. Decrypt the following messages using RSA cryptosystem. a) Message : 0667 1947 0671 , with p=43,…
A: Given message is 0667 1947 0671 Given that, p=43 , q=59 and d=937 Therefore we get, n = pq = 43(59)…
Q: Encrypt the message ATTACK using the RSA system with n = 43 · 59 and e = 13, translating each letter…
A:
Q: Assume they are used for an encryption in Hill ciphers. In each case, find two plaintexts that…
A: The matrices given are as follows: 1322 and 131242351 For 1322 Let x1y1 and x2y2 be two plain…
Q: What is the secret message produced from the message “MEET YOU IN THE PARK” using the Caesar cipher?
A:
Q: 2. Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29. R
A:
Q: (a) Suppose Alice and Bob use the simple encryption scheme in which c = (m + k) mod N and m = (c –…
A: Suppose Alice and Bob use the simple encryption scheme in whichc=m+kmodN and m=(c-k)modN. Suppose…
Q: 13. Let (n, e) = (16504217646971, 78893) be Alice's public key, where e represents the %3D…
A:
Q: Find integers X, E > 2 such that XE = X (mod 74329). How does this illustrate a potential problem in…
A: Given : E ≥ 2 such that XE ≡ X (mod 74329). To find integer X.
Q: npojd Assume that a person has ElGamal public key (2633, 3, 1138) and private key k = 965. If the…
A:
Q: Arthur and Dara are exchanging messages using the RSA Cipher system and the following information:…
A: We have to verify that Arthur's private exponent 43 is correct given the following information…
Q: Let (P, C, K, E, D) be a cryptosystem such that #K = #P = #C. Show that if this cryptosystem has…
A:
Q: Decrypt the message "WFLRV" which is encrypted by the encryption function f (p) = (3p + 11) mod 26.…
A: Given: Encryption function is f(p)=3p+11mod26. Encrypted message is "WFLRV". For W, P=22.…
Q: 3. The message NOT NOW (numerically 131419131422) is to be sent to a user e a EIGamal system who has…
A:
Q: Encrypt the message GRIZZLY BEARS using blocks of five letters and the transposition cipher based on…
A:
Q: 3. (a) Suppose that you have an alphabet of 26 letters how many possible simple substitution ciphers…
A:
Q: (7) Which of the following formulas represent the process of encryption in Caesar Cipher? (Choose…
A: Option B M=(C-3)mod26
Q: Suppose a community of RSA users share the same encryption exponent e but each user i has their own…
A: Show that if k>e, then a cryptanalyst can recover the plaintext x without factoring any of the…
Q: Solve the following problems: (a) How many ways can a store manager arrange a group of 1 team…
A: a) No of ways to choose 4 from 25= 25C4 = 12650 No of ways to choose 1 from 3= 4C1 = 4 Therefore No…
Q: If the given encrypted text is " VTXDUH" then the decrypted text using Caesar cipher will be, O…
A: The correct option is SQUARE. Use the given options to decrypt the given text. All the options has…
Q: (b) If the public key for an RSA cryptosystem is (N, e) = (69,5), find the private key d.
A: We follow the standard techniques use in the RSA algorithm. The detailed typeset solution is…
Q: Bob wants to send Alice the message, "JAW," which he plans to encrypt using Alice's RSA cypher with…
A:
Q: Which of the following is the decryption function of an RSA cryptosystem having public and private…
A: We Know that, The RSA algorithm can be used for both public key encryption and digital signatures.
Q: Suppose an RSA cryptosystem is used to send the plaintext "4" with public key (n, e) = (33, 3). What…
A: RSA algorithm is an encryption method that uses two types of keys namely private and public and,…
Q: Determine the encryption and decryption codes of the indicated messages. A) Apply Shift Cipher to…
A:
Q: 6| Alice wants to send message HELLO using the RSA system with p = 7 and q = 11 and n= 53 by…
A:
Q: 2. If the Caesar cipher produced RDSSB ELUWKGDB, WIlal Is uic plumno 3. (a) A linear cipher is…
A:
Q: (a) Use the Atbash cipher to encrypt the following messages: in Alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ…
A: Since the second question is independent of the first question so I am the answering the first…
Q: 13, Let (n, e) = (16504217646971, 78893) be Alice's public key, where e represents the encryption…
A:
Q: Recall that an affine cipher, fa,b(n) = an + b( mod 26), where a, b ∈ {0, 1, 2, . . . , 25}, is said…
A: For the encryption, use the following conversion table for the English alphabet: 0 1 2 3 4 5 6 7…
Q: Having chosen primes p and q, and suitable integers d and e, what is the public-key of our RSA…
A: There are primes p and q and integers d and e, the public-key of RSA cipher is: n,e=pq, e
Q: In a lengthy ciphertext message, sent using a linear cipher C = a P +b (mod 26), the most frequently…
A:
Q: Use the RSA cipher with public key n = 713 = 23 · 31 and e = 43. Decrypt the given ciphertext…
A: To decrypt the ciphertext 476 089 048 129 and find the original message. When given n = 713 = 23 ·…
Q: 1. The following sentence was encoded using the Cesar Cipher, your job is to decode it: KRZ DUH BRX.
A: 1. The following table is used to decrypt the message.
Q: Suppose the RSA system that is used for sending secret messages has private key (15, 3) and the…
A: Given that, private key=15,3 Cipher text=3
Q: Decrypt the message EABW EFRO ATMR ASIN, which is the ciphertext produced by encrypting a plaintext…
A:
Q: Use the cipher: f(x) = (x + 10) mod 26,0 ≤ x ≤5 to decrypt "SD SC XYD PKSB".
A: To Use: The cipher: f(x) = (x + 10) mod 26, 0≤x≤25 to decrypt "SD SC XYD PKSB".
Q: The ciphertext letter for T when the congruence is C =( P + 10 ) mod 26 is
A:
Q: Construct an affine cipher that uses only uppercase letters of English alphabet encoded as elements…
A:
Q: Suppose that when a string of English text is encrypted using a shift cipher f (p) = (p + k) mod 26,…
A:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Suppose that in an RSA Public Key Cryptosystem, the public key is e=13,m=77. Encrypt the message "go for it" using two-digit blocks and the 27-letter alphabet A from Example 2. What is the secret key d? Example 2 Translation Cipher Associate the n letters of the "alphabet" with the integers 0,1,2,3.....n1. Let A={ 0,1,2,3.....n-1 } and define the mapping f:AA by f(x)=x+kmodn where k is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of a through z, in natural order, followed by a blank, then we have 27 "letters" that we associate with the integers 0,1,2,...,26 as follows: Alphabet:abcdef...vwxyzblankA:012345212223242526Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "algebra" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?
- Suppose that in an RSA Public Key Cryptosystem. Encrypt the message "pascal" using the -letter alphabet from Example 4. Use two-digit blocks. Use three-digit blocks. What is the secret key?Suppose that the check digit is computed as described in Example . Prove that transposition errors of adjacent digits will not be detected unless one of the digits is the check digit. Example Using Check Digits Many companies use check digits for security purposes or for error detection. For example, an the digit may be appended to a -bit identification number to obtain the -digit invoice number of the form where the th bit, , is the check digit, computed as . If congruence modulo is used, then the check digit for an identification number . Thus the complete correct invoice number would appear as . If the invoice number were used instead and checked, an error would be detected, since .Suppose the alphabet consists of a through z, in natural order, followed by a blank and then the digits 0 through 9, in natural order. Associate these "letters" with the numbers 0,1,2,...,36, respectively, thus forming a 37-letter alphabet, D. Use the affine cipher to decipher the message X01916R916546M9CN1L6B1LL6X0RZ6UII if you know that the plaintext message begins with "t" followed by "h". Write out the affine mapping f and its inverse.
- a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?Use the alphabet C from the preceding problem and the affine cipher with key a=11andb=7 to decipher the message RRROAWFPHPWSUHIFOAQXZC:Q.ZIFLW/O:NXM and state the inverse mapping that deciphers this ciphertext. Exercise 7: Suppose the alphabet consists of a through z, in natural order, followed by a colon, a period, and then a forward slash. Associate these "letters" with the numbers 0,1,2,...,28, respectively, thus forming a 29-letter alphabet, C. Use the affine cipher with key a=3andb=22 to decipher the message OVVJNTTBBBQ/FDLWLFQ/GATYST and state the inverse mapping that deciphers this ciphertext.Rework Example 5 by breaking the message into two-digit blocks instead of three-digit blocks. What is the enciphered message using the two-digit blocks? Example 5: RSA Public Key Cryptosystem We first choose two primes (which are to be kept secret): p=17, and q=43. Then we compute m (which is to be made public): m=pq=1743=731. Next we choose e (to be made public), where e must be relatively prime to (p1)(q1)=1642=672. Suppose we take e=205. The Euclidean Algorithm can be used to verify that (205,672)=1. Then d is determined by the equation 1=205dmod672 Using the Euclidean Algorithm, we find d=613 (which is kept secret). The mapping f:AA, where A=0,1,2,...,730, defined by f(x)=x205mod731 is used to encrypt a message. Then the inverse mapping g:AA, defined by g(x)=x613mod731 can be used to recover the original message. Using the 27-letter alphabet as in Examples 2 and 3, the plaintext message no problem is translated into the message as follows: plaintext:noproblemmessage:13142615171401110412 The message becomes 13142615171401110412. This message must be broken into blocks mi, each of which is contained in A. If we choose three-digit blocks, each block mim=731. mi:13142615171401110412f(mi)=mi205mod731=ci:082715376459551593320 The enciphered message becomes 082715376459551593320 where we choose to report each ci with three digits by appending any leading zeros as necessary. To decipher the message, one must know the secret key d=613 and apply the inverse mapping g to each enciphered message block ci=f(mi): ci:082715376459551593320g(ci)=ci613mod731:13142615171401110412 Finally, by re-breaking the message back into two-digit blocks, one can translate it back into plaintext. Three-digitblockmessage:13142615171401110412Two-digitblockmessage:13142615171401110412Plaintext:noproblem The RSA Public Key Cipher is an example of an exponentiation cipher.
- Suppose the alphabet consists of a through, in natural order, followed by a blank, a comma, and a period, in that order. Associate these "letters" with the numbers, respectively, thus forming a -letter alphabet,. Use the affine cipher to decipher the message if you know that the plaintext message begins with "" and ends with ".". Write out the affine mapping and its inverse.Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse.Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?

