Suppose the destination not stored in the MAC table, what will happen O no option is correct the switch send request to all ports the switch send request to all except the port that is came from the switch send request to the port that is came from the switch will not send request to all ports
Suppose the destination not stored in the MAC table, what will happen O no option is correct the switch send request to all ports the switch send request to all except the port that is came from the switch send request to the port that is came from the switch will not send request to all ports
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter9: Supporting Mobile Devices
Section: Chapter Questions
Problem 9TC
Related questions
Question
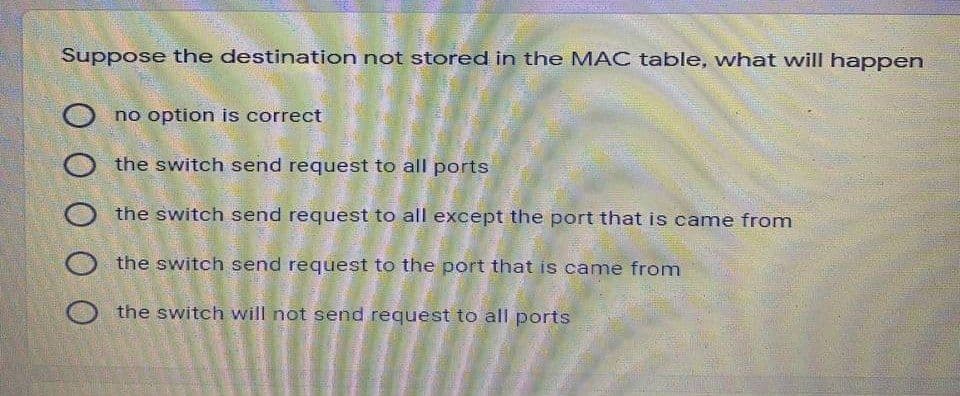
Transcribed Image Text:Suppose the destination not stored in the MAC table, what will happen
no option is correct
O the switch send request to all ports
O the switch send request to all except the port that is came from
the switch send request to the port that is came from
the switch will not send request to all ports
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning