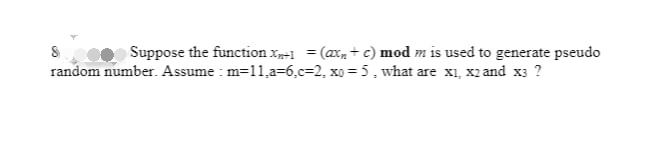
Suppose the function x1 = (a + c) mod m is used to generate pseudo random number. Assume: m=11,a-6.c-2, xo=5, what are x₁, x2 and x3 ?
Q: Remove all errors from the C++ program given below asap. #include using namespace std; int main(){ }…
A: Given C++ program is, #include <iostream>using namespace std;int main() { int…
Q: According to some political pundits, a person who is radical (R) is electable (E) if he/she is…
A: Please keep in mind that we are only supposed to help with the first question if students ask for…
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in…
A: Required:- How can I convert the temperature in Fahrenheit from the degree celsius which is entered…
Q: Which of the following is not the rule for writing PHP? A Whitespace sensitive B Case…
A: Which of the following is not the rule for writing PHP? We have four options White space sensitive…
Q: Statistics are often calculated with varying amounts of input data. Write a program that takes any…
A: Coded using Java.
Q: Explain a practical scenario why split tunneling is used
A:
Q: When the MPU starts up for the first time it goes to the Reset vector Interrupt vector General…
A: In this problem we need to identify When the MPU starts up for the first time it goes to the and…
Q: Design a Program for stepper motor and Calculate its angular speed and rotation Need Asap a short &…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Which of the following is not a PHP variable? A $a; B var a; C…
A: Introduction: In this question, we are asked to answer two MCQs on the basis of PHP
Q: java Write a method that returns the frequency of each characters of a given String parameters If…
A: // Java implementation to print the character and// its frequency in order of its occurrence public…
Q: Suppose that the roundtrip delay between sender and receiver is constant and known to the sender.…
A: I have mentioned answer in below step, please find in below
Q: Explain the impact digital technology has had on assistive devices for people with physical…
A: Assistive technologies (ATs) are any item, equipment, product, like reading glasses, crutches,…
Q: Install and compile the Python programs TCPClient and UDPClient on one host and TCPServer and UDP…
A: Install and compile the Python programs TCP Client and UDP Client on one host and TCP Server and UDP…
Q: Ex: If the input is: 5 25 51 0 200 33 0 50 then the output is: 25,0,33, (the bounds are 0-50, so 51…
A: new_list = range (0,10) for i in range (0,10) print "numbers are", new_list [5:9]
Q: What about routing? Is there a difference between IPv4 and IPv6?
A: Network routing selects a path that spans one or more networks. The principles of routing can be…
Q: Which VLAN is intended to provide administrative access to network devices?
A: The answer is provided below.
Q: Write a Python Program to take days from the user and covert it into years, week & 2 day
A: Required: Write a Python Program to take days from the user and covert it into years, weeks &…
Q: Suppose that the UDP receiver computes the Internet checksum for the received UDP segment and finds…
A:
Q: Play the following chord: I Lives: 7 I want this picture to be drawn cpp code drawing using OpenGL
A: #include <GL/glut.h> #include <GL/glu.h> #include <math.h> #include…
Q: Create a sequence diagram showing the interactions of objects in a group diary system, when a group…
A: The answer is given in the below step
Q: 49. Write a C# Sharp program to create a new list from a given list of integers removing those…
A: using System;// import Collections and Genericusing System.Collections.Generic;// creating a Driver…
Q: - A new movie has just been released " Interstellar"! There are a lot of people at the cinema box…
A: Below I have provided the python code of the given question. Also, I have attached the code snippet…
Q: Some signalling errors can cause entire ranges of bits in a packet to be overwritten by all Os or…
A:
Q: a e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using. JAVA…
A: CODE: import java.util.*; public class test { public static void main(String[] args) {…
Q: A stage of an n x n banyan network consists of (n/2) 2×2 switching elements. The first stage directs…
A: Here we have given solution for the question asked. You can find the solution in step 2.
Q: Use Assembly Language x86 (MASM) to Write an assembly code calculates the sum of all array elements…
A: Algorithm: Input the array size from the user Iterate loop from 0 to size of array do Input n…
Q: Create a c++ find function that finds a word or phrase within a string. This function should accept…
A: Here is the c++ code of above problem. Our input string was hello And the function will return 0,…
Q: Let's say that an employee's regular pay is rate times hours. If they work more than 40 hours, they…
A: Solution: Given, If they work more than 40 hours, they get time and a half. In that case, we…
Q: Complete the functions in the template to implement the formulas shown below. The formula to…
A: The solution to the given is: CODE: import math # An isotope has half-life T # Return the amount of…
Q: Explain the difference between Program Counter(PC) and Exception Program Counter in your own words…
A: Answer : Program counter ( PC) : It is used to store the address of the instructions that is…
Q: Compute a QR decomposition of the matrix
A: Question (a) We can compute a QR decomposition of the matrix using a Givens rotation as follows:…
Q: Which VLAN is intended to provide administrative access to network devices?
A: Solution - In the given question, we have to tell which VLAN is intended to provide administrative…
Q: What are the steps or components of the chosen SSL/TLS attack? What are the vulnerabilities this…
A: SSL/TLS attack: An SSL DDoS attack will targets the SSL handshake protocol either by sending…
Q: :. Software Application (screenshots of the system/simulation)
A: EMU8086 which refers to the microprocessor of the emulator which is the free emulator and used for…
Q: From a user's perspective, what is the difference between the download-and-delete mode and the…
A: The answer of the question is given below:
Q: Remove all errors from the C++ program given below asap. #include using namespace std; int main(){ }…
A: Remove all errors from the C++ program given below asap. #include<bits/stdc++.h> using…
Q: Consider the soda can game introduced in the class. Now suppose instead of a single circular table,…
A: The answer is written in step 2
Q: Q\ Write program in fortran to find the maximum number of (x,y,z)?
A: CODE : - !main program main implicit none !declaring three integers integer : : x, y, z !prompting…
Q: write Pattem. a Python program to print the A BC DEF GHIJ KLMNO PQRSTU VW X Y Z CY
A: Python is the programming languages and it is consider as the a high-level, interpreted,…
Q: class IntBTNode { private int data; private IntBTNode left;…
A: class IntBTNode { private int data; private IntBTNode left;…
Q: R12. Consider an e-commerce site that wants to keep a purchase record for each of its customers.…
A: When a user visits the e-commerce site for the first time, the website will return a cookie number,…
Q: Write a class called Animal with an default sound() method that does not output a specific animal…
A: Code is given below import java.util.Scanner; class Animal { void sound() {…
Q: The x86 includes the following instruction: IMUL op1, op2, immediate This instruction multiplies…
A:
Q: What enhancements would you make to the current safety and security provided by Windows OS? Do…
A: The correct answer for the above question is given in the following steps for your reference.
Q: Assume that a computer system is having 4-page frames for holding process pages in the main memory.…
A: Here is the explanation:
Q: Disk Parameters: Transfer size is 8K bytes, Advertised average seek is 6 ms, Disk spins at 3600 RPM,…
A: Disk A flat, spherical plate on which data can be encoded and stored is called a disc (or diskette).…
Q: What is constructor chaining and how is it achieved in Java ?
A: - We have to talk about constructor chaining in Java.
Q: A simple processor has four major phases to its instruction cycle: fetch, indirect, execute, and…
A:
Q: Suppose that the roundtrip delay between sender and receiver is constant and known to the sender.…
A: Assume that the sender and receiver have a constant roundtrip delay and that the sender is aware of…
Q: What is the difference between an external iterator and an internal iterator? Describe an advantage…
A: what is difference between external and internal operator describe advantage of external iterator.
Step by step
Solved in 3 steps

- Consider the following function someFunc::Integer -> Integer -> Integer -> Integer someFunc x y z = x *(y + z) Prove that someFunc a b c = sumFunc a c bConsider the code C={00010, 01100,01011,11010,01010}. What is the minimum distance of C? For what k is the code C k-error detecting? Write the set of error patterns that C can detect?Given a function f from {1, 2, … , n} to itself, using Python, write a program to determine whether f is onto.
- Using foldl, define a function num2int :: [Int] -> Int -> Int that converts a list of numbers and the number n into an integer of base n. >num2int [3,4,5,6] 10 3456 >num2int [1,1,0,1,0,0,0,1,0,1,0,1,1,0] 2 3456 num2int :: [Int] -> Int -> Int num2int x y = foldl (\acc (a,b) -> ___a___ + b*y^a) 0 (___b___ (\x y ->(x,y)) [0..] (___c___ x)) fill in blank spaces of a , b , and cGiven the following definitions: U={a,b,c, d, e, f, g} A={a, c, e, g} B={a,b,c,d} find A n BSimplify the complement of the following function: F(A,B,C,D)=(0,2,4,5,8,9,10,11) Your answer: F=((A'B'D)' (BC)'(AB)')' F=((A'BD)'(BC)'(AB)')' F=((A'B'D)'(B'C)'(AB)') F=((A'B'D')' (BC)'(AB)')
- If b is a unit modulo m and a is another unit with a=b^d (mod m), we say that d is the _________ of a modulo m to the base b and write d =___________.Consider a base 26 number system wherein the letters of the alphabet are the digits. That is, A=0, B=1, C=2, … Z=25 in base 10. Use the MAL as a number in the base 26 system, and KHA as another number in the base 26 system.Add these numbers together to obtain the sum in based 26. Example 1 — if your first name is “Peter” and your surname is “Pan”, then add up PET26 and PAN26, and show the sum in base 26.Example 2 — if your first name is “Peter” and your surname is “Pa”, then add up PET26 and PAA26, and show the sum in base 26.for C++ write a progam for the greatest common divisor of integers x and y is the largest integer that evenly divides both x and y. Write a recursive function gcd that returns the greatest common divisor of x and y. The gcd of x and y is defined recursively as follows. If y is 0 the answer is x; otherwise gcd(x, y) is gcd(y, x%y).
- Write a c++ program function that makes the base conversion. It takes two integers n and b as input (n >= 0 and b > 1, both in base 10) and expresses n in base b. For example, the decimal expansion of 345 in base 10 is 345=3×102 +4×101 +5×100.Sample input: n = 12, b = 2. Sample output: 1100 Explanation: (12)10 = (1100)2Let A = {c, n, b}, B = {x, y} and C = {0, 1}. Find A)A X B X C B)C X B X A C)B X C X CI need help with this question of Data Structures and Algorithmns 1 True of False a) For two functions f(n) and g(n) if f(n) =O(g(n)) then g(n) = Ω(f(n)) (True or False) b) For two positive functions g and h if f(n) =O(g(n)) then g(n) = O(h(n)) , then f(n)= O(h(n)) (True or False) c) If g1(n) = O(f(n)) and g2(n) = O(f(n)), then g1 + g2 = O(f(n)) (True or False)



