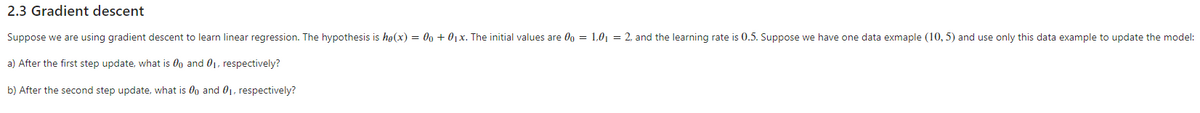
Suppose we are using gradient descent to learn linear regression. The hypothesis is ho(x) = 00 + 01x. The initial values are 0g = 1.0, = 2. and the learning rate is 0.5. Suppose we have one data exmaple (10, 5) and use only this data example to update the mo a) After the first step update, what is 0o and 01, respectively? b) After the second step update. what is 0o and 01. respectively?
Q: 223- Assume we have one-dimensional data like the following example. d1 d2 d3 d4 d5 d6 d7 d8 d9 d10 ...
A: A stride is the number of data skipped while selecting a next input in the convolution layer.
Q: Write a program that reads in a sequence of characters entered by the user and terminated by a perio...
A: The Answer is
Q: A linked list is developed with the following set of nodes in sequence: 25, 40, 66, 38 and 53. The l...
A: A linked list is a sequence of data structures, which are connected together via links. Linked List ...
Q: What is the most essential thing to remember when learning about computers?
A: Introduction The most important thing in the introduction to computers are, Hardware and Software
Q: What is the Compressed Form of Post Office Protocol on a Computer?
A: Introduction: The post office protocol is the most extensively used message request protocol on the ...
Q: Using a system call to print a string of text, Change this MIPS code to RISC-V Assembly code.
A: RISC-V assembly is similar to MIPS assembly code. It has an integer, floating-point, branching, logi...
Q: Compare interrupt-based and DMA-based IO in terms of performance and program complexity.
A: Data transfer: Data can be sent between the central computer and I/O devices in a variety of ways. A...
Q: Do the following questions: a. Create a function that takes a source file name and destination file ...
A: The solutions for the subpart A and B are given in the following steps with corresponding output. fi...
Q: What services does the SNMP protocol provide?
A:
Q: int f(int n) { if (n 9 10. What is the value of f2 (10)? a. 21
A: Please find the correct answers and corresponding source code in the following steps.
Q: software engineering
A: The currents world runs on softwares that are developed to reduce the problems of mankind.
Q: B= 3 - J4 Calculate the following and plot using the compass() function. Hint: Read help for compass...
A: % assign the A and B A = 1 + 2i; B = 3 -4i; hold on % plot A compass(A','r'); % plot A - B compass(A...
Q: Draw the basic building blocks of the following system. Explain briefly the operation/function(s) of...
A: INTRODUCTION: We need to draw the basic building blocks of the following system and also explain the...
Q: the following
A: We draw truth table for the given statements and rewrite them using NOR operation.
Q: What is the role of XLST in the development of a Web application?
A: Introduction: This aids in the implementation of machine learning models on websites. The route that...
Q: In C++, a variable that has been defined but not initialized may not be used as an 1-value Or r-valu...
A: A variable is a name of memory location.
Q: ose to compute a mode for a variable, which variability would you m
A: If you chose to compute a mode for a variable, which variability would you most likely report?
Q: For nodes 0000 and 1111, there exists four node-disjoint paths of length 4 (which happens to be the ...
A: I have answer this question in step 2.
Q: why would you use a for loop instead of a while loop?
A: Initialization, condition, and increment or decrement operations are all included in the for loop. T...
Q: Which Tab is used to add a "Header" in Excel?
A: which tab is used to add header in a excel
Q: You are given an array with following items in sequence: {14, 7, 3, 12, 9, 11, 6, 12} Sort the item ...
A: We are given an unsorted array and we are going to sort the array using Merge sort algorithm. Merger...
Q: What exactly does computer scalability imply?
A: Introduction: Scalability is tied to both computer systems and business transformation.
Q: 1 import java.util.Scanner; 2 3 public class DeclaringVariables { public static void main(String[] a...
A: import java.util.Scanner; public class DeclaringVariables { public static void main (String[] args) ...
Q: The purpose of this assignment is to use Python to manipulate and modify audio WAV files into a new ...
A: Sounds are waves of air pressure. When a sound is generated, a sound wave consisting of compressions...
Q: 4. Write definitions for the following two functions: sumN (n) returns the sum of the first n natura...
A: I give the required code in Python along with output and code screenshot
Q: create a new function that calls on the other two functions and outputs a password that is random wi...
A: // C++ program to generate all passwords for given characters#include <bits/stdc++.h> using na...
Q: Q2. What are the various access specifiers for Java classes?
A: Q2. What are the various access specifier for java classes? Answer: Access specifier for java class...
Q: What are some indicators that the operating system on a laptop has been compromised?
A: If you assume your system has been hacked or compromised. Here are some indicators given below:
Q: What is the distinction between Python and JavaScript programming?
A: Introduction: javascript It is a web programing language. it is a cross-platform language. Its code...
Q: Kaggie data se ice date Use the above data set Describe the data set • Use descriptive statistic Dra...
A: Introduction
Q: 9 import java.util.Scanner; 10 //Creating a class 11 - public class Main{ 12 // Driver code public s...
A: the output is tax calculation based onn input amount and then the total amount including tax.
Q: D. Single Phase Circuit Consider the circuit in Figure 2 - 1 Rídr Lfdr ZL Figure 2 -1 Given that Ra ...
A:
Q: Discuss the use of the term "accuracy" in categorization difficulties. Is it a good or terrible idea...
A: Discuss:- The accuracy in classification problem. Whether it is good or bad to measure the performa...
Q: Why is there a dual side to every transaction? Explain.
A: The dual side theory states that each business transaction impacts the business in two different way...
Q: What does it mean when a relationship is well-structured? In logical database architecture, why are ...
A: Given:
Q: Count the number of occurrences of substrings "baba" or "mama" * in the input string recursively. T...
A: PROGRAM CODE: class Main{ public static boolean isEmpty(String s) { return s == null || s.length()...
Q: What are the internals of a convolutional neural network How do you train a model with transfer lea...
A: answer is
Q: Write a program to implement Heap sort. Also implement one of the slow sorts (Bubble, Insertion...)....
A: Program:- #include <iostream>using namespace std; void max_heapify(int a[], int i, int n) /*th...
Q: Differentiate WIRED media and WIRELESS media in terms signal energy, functionality (when to used), c...
A: The category of wire communication medium includes any physical connection that may transmit data as...
Q: Explain how a VPN can disguise a user's internet habits and prevent personal browsing data from bein...
A:
Q: # A set of constants, each representing a list index for station information. ID = 0 NAME = 1 LATITU...
A: The Answer is
Q: he term cache pollution refers to the situation where more than one process is running concurrently ...
A: Introduction: Here we are required two choose the correct option of the question given above.
Q: Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-wei...
A: The Answer is
Q: Why isn't Level 3 Application Security Verification required for all applications?
A: Introduction: An Application An application is a computer software package that performs a piece of ...
Q: c routing protocols. What are the primary differences between the two and when would you use one ove...
A: given - OSPF and BGP are two of the most common dynamic routing protocols. What are the primary diff...
Q: node in the linked list is defined as follows: node begin data: element of any datatype link: pointe...
A: Here the statement p=f.link.link means take 3rd node with respect to f. That is p will be pointing...
Q: What is the Conceptual Framework for Cybercrime? In your answer, provide references.]
A: Introduction: Many people, organizations, and countries rely heavily on the Internet in their daily ...
Q: Consider a 32KB direct mapping cache with a 32-byte block size. The CPU generates addresses that are...
A: Consider 32 KB direct mapping cache with 32 byte block size .the cpu generate address that 32 bits l...
Q: Write the sequence of nodes produced by the inorder traversal of tree in figure. Write the name of t...
A: The question is to find the ignorer traversal for the given ternary tree.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- We want to build a regression model and have many observations and many predictors. (a) From a computational point of view, which of these two model building algorithms are preferable: best subset selection or forward stepwise selection? (b) True or false and explain: Best subset selection will result in a smaller prediction error than forward stepwise selection because every model that is considered in forward stepwise selection is also considered in best subset seSuppose you are using a Linear SVM classifier with 2 class classification problem. Now you have been given the following data in which some points are circled red that are representing support vectors. a) Draw the decision boundary of linear SVM. Give a brief explanation. b) Suppose instead of SVM, we use regularized logistic regression to learn the classifier circle the points such that removing that example from the training set and running regularized logistic regression, we would get a different decision boundary than training with regularized logistic regression on the full sample . why ?To train a binary logistic regression model, we used the delta rule to learn the weight of feature i using a training case j: ∆Wij = −ηxij yj (1 − yj )(tj − yj ), where η is the tunable learning rate. Please write down the delta rule for mini-batch gradient descent update assuming the size of mini-batch is n.Please answer the following question from above: What about the linear perceptron classi?er? (hint: activation function now changes from sigmoid to sign)
- Create Second Image Now that we have fit our model, which means that we have computed the optimal model parameters, we can use our model to plot the regression line for the data. Below, I supply you with x_fit and y_fit that represent the x- and y-data of the regression line, respectively. All we need to do next is ask the model to predict a z_fit value for each x_fit and y_fit pair by invoking the model's predict() method. This should make sense when you consider the ordinary least squares linear regression equation for calculating z_fit: ????=?̂ 0+?̂ 1????+?̂ 2????zfit=θ^0+θ^1xfit+θ^2yfit where ?̂ ?θ^i are the computed model parameters. You must use x_fit and y_fit as features to be passed together as a DataFrame to the model's predict() method, which will return z_fit as determined by the above equation. Once you obtain z_fit, you are ready to plot the regression line by plotting it against x_fit and y_fit. Any dataset would be great. I just want to understand it.4 the task is to estimate two models1. Cobduglus (after taking log to convert it into log-linear)2. Estimate the linear model without logIn R, write a function that produces plots of statistical power versus sample size for simple linear regression. The function should be of the form LinRegPower(N,B,A,sd,nrep), where N is a vector/list of sample sizes, B is the true slope, A is the true intercept, sd is the true standard deviation of the residuals, and nrep is the number of simulation replicates. The function should conduct simulations and then produce a plot of statistical power versus the sample sizes in N for the hypothesis test of whether the slope is different than zero. B and A can be vectors/lists of equal length. In this case, the plot should have separate lines for each pair of A and B values (A[1] with B[1], A[2] with B[2], etc). The function should produce an informative error message if A and B are not the same length. It should also give an informative error message if N only has a single value. Demonstrate your function with some sample plots. Find some cases where power varies from close to zero to near…
- below is the xample file # ================= Polynomial Regression =================== # Thus far, we have assumed that the relationship between the explanatory # variables and the response variable is linear. This assumption is not always # true. This is where polynomial regression comes in. Polynomial regression # is a special case of multiple linear regression that adds terms with degrees # greater than one to the model. The real-world curvilinear relationship is captured # when you transform the training data by adding polynomial terms, which are then fit in # the same manner as in multiple linear regression. # We are now going to us only one explanatory variable, but the model now has # three terms instead of two. The explanatory variable has been transformed # and added as a third term to the model to captre the curvilinear relationship. # The PolynomialFeatures transformer can be used to easily add polynomial features # to a feature representation. Let's fit a model to these…GD algorithm Consider Linear Regression with single variable (univariate) problem. What will be the (approximate if can’t say accurately) values of derivatives of cost/loss function ‘J’ w.r.t. all the parameters by considering one at a time, and why? What is the significance and/or usage of these θj* for the cost function ‘J’ and hypothesis ‘h’? Given a dataset where first column is the label ‘y’ while other columns represent factors ‘xi’ as follows: X = [ 1 0 1 0 1 0 ] Using GD algorithm, find the linear model. Show all the calculationsQuestion 1 1)When our predictor variables have ranges and units that are quite different, it is pertinent to scale them before using them in a regression. Which of the following statements regarding scaling is FALSE? a)Normalisation is a scaling process which is inherently sensitive to outliers in the data. b)Standardisation is the process of squeezing a range of values to into the range [0,1]. c)Standardisation centres and scales a set of values such that they all have a mean of 0 and standard deviation of 1. d)Normalisation is the process of squeezing a range of values to into the range [0,1]. 2) The R-squared measure is said to take on a 'proportion' of some attribute associated with the model. What is that proportion? a)Proportion of observations used for training. b)Proportion of variance explained. c)Proportion of outputs correctly predicted. d)Proportion of predictor variables contributing to output.
- Assume that your hypothesis function is of the form f(x) = w0 + w1x and that the current values of w0 and w1 are 1 and 2 respectively. Further assume that you are using a learning rate (alpha) of 0.001 What is the gradient update for w0 (only the change) associated with the point (1, 12)?Please help with the artificial intelligence question below thanks! Given a number of data samples (X, Class) in the attached file where each data sample consists of a variable X and a Class whose value is 1 or 2. (1) Using the given sample data, use the Gradient Descent algorithm to predict the logistic regression model (Note: the logistic regression model is NOT a regression model). (2) Using the logistic regression model as a solution to point (1) above, predict the Class of a sample that has a value of X = 5.6Assume the following simple regression model, Y = β0 + β1X + ϵ ϵ ∼ N(0, σ^2 ) Now run the following R-code to generate values of σ^2 = sig2, β1 = beta1 and β0 = beta0. Simulate the parameters using the following codes: Code: # Simulation ## set.seed("12345") beta0 <- rnorm(1, mean = 0, sd = 1) ## The true beta0 beta1 <- runif(n = 1, min = 1, max = 3) ## The true beta1 sig2 <- rchisq(n = 1, df = 25) ## The true value of the error variance sigmaˆ2 ## Multiple simulation will require loops ## nsample <- 10 ## Sample size n.sim <- 100 ## The number of simulations sigX <- 0.2 ## The variances of X # # Simulate the predictor variable ## X <- rnorm(nsample, mean = 0, sd = sqrt(sigX)) Q1 Fix the sample size nsample = 10 . Here, the values of X are fixed. You just need to generate ϵ and Y . Execute 100 simulations (i.e., n.sim = 100). For each simulation, estimate the regression coefficients (β0, β1) and the error variance (σ 2 ). Calculate the mean of…

