Suppose we have the function f(n) = (n+1)3. Below are a number of statements regarding how the feature grows depending on n only B is true B and F is true B,C,D,F true B,D,F is true
Q: I'm trying to learn CSS and it isn't easy. Can someone help me with this problem? Modify or add one…
A: In this question we have to use CSS properties to change the color of the text using COLOR NAME RGB…
Q: Could you kindly describe the most significant components of the operating system? To summarise:
A: Introduction: Several computer system components rely on the components of an operating system to…
Q: Write an application for a lawn-mowing service. The lawn-mowing season lasts 20 weeks. The weekly…
A: Find the required code in java given as below and output :
Q: Take a look at the benefits and drawbacks of different system models.
A: Introduction: It is the construction of abstract models of a system, each of which provides a…
Q: 5)To connect the corporate networks which one of the following is true? a SSL is better since…
A: Remote access to systems and apps has grown commonplace in the workplace. Employees, customers,…
Q: Write in the programming language Julia a program to compute pi using a Monte Carlo simulation of N…
A: Julia is a dynamic new programming language for computer technology with a learning syntax similar…
Q: What is structure, and what is the difference between structure and array?
A: Basics C++ is a cross-stage language that can be utilized to make superior applications. It gives…
Q: What types of programming languages are there? Each one should be briefly explained.
A: Different types of programming languages are: Declarative language: These types of languages are…
Q: What are the advantages of CSS sprites?
A: Introduction: Because each picture generates an HTTP request on its own, a web page with a large…
Q: ou will need to sort a list of whitespace separated integers using three different sort algorithms.…
A: NOTE: As not mentioned I have solved the question in C++ Code: #include <bits/stdc++.h>using…
Q: Given a process with address space of size 32 bytes and page size of 8 bytes, if the CPU asks to…
A: As we know Physical address = page size*frame number + offset
Q: Task 2: Take a sequence of braces from user entered through the keyboard and tell the user whether…
A: The problem can be solved for traversing over the string and deleting every consecutive open and…
Q: Create a Flowchart //Java Source Code :- import java.util.Scanner; public class bExpert {…
A: Here is the Flow chart below: Please appreciate and Upvote thank you:
Q: What methods may be utilised to secure data while it is in transit or at rest? Computer science
A: Data at rest is static data stored on hard drives that are archived or not often accessed or…
Q: ments in MongoDB? Does MongoDB support nested documents? If yes, how? What is MongoDB Shell? What is…
A: IntroductionMongoDB is a free, open-source document-oriented database that can store a lot of data…
Q: U have a ram page of 3 This the string 1,2,1,8,1,3,1,8,11,5,8 Use first in first out page…
A: We are asked the number of page faults and hit rate for the given string. Using FIFO(First In First…
Q: How many non-isomorphic connected graphs are there with seven vertices, seven edges, and three…
A: The term "non isomorphic" means "not having the same form" and it is used in many branches of…
Q: When saving passwords in a file, why is it better to hash them rather than encrypt them?
A: Introduction: If a hacker obtained access to the database and stole the passwords table, the thief…
Q: Working on cables, connectors, cartridges, and software will have no effect on user interface.…
A: Introduction: It will have no influence on the user interface whether you are working on cables,…
Q: 4)In the following IPsec ESP Tunnel model, Which parts are authenticated? a ESP Header , IP…
A:
Q: m Call? How does the operating syst
A: Sorry for that as per the bartleby guidelines we can solve only one question for if you want to…
Q: Describe the process (activity) of a DHCP server automatically sending IPv4 configuration parameters…
A:
Q: This is owing to the fact that today's computers are extremely powerful. What reasons have…
A: Introduction: We must emphasise the importance of using computers in our educational system, as well…
Q: INSTRUCTIONS: Develop a java program and flowchart that utilizes methods, loops, conditions and…
A: Note :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: Define the shift from first to fifth generation computer technology in a few simple sentences.
A: Introduction: In computer jargon, generation refers to a change in the technology on which a…
Q: describe what vulnerabilities 'WannaCry' malware exploited to infect its target systems.
A: Intro WannaCry Ransomware The WannaCry ransomware is made up of several parts. It comes in the…
Q: Discuss the concept of a candidate key being an attribute that is part of a composite primary key.
A: Justification: A candidate key is a single or a collection of keys that uniquely identify rows in a…
Q: Problem Definition: • Apply and demonstrate the concept of the String & Array structure. • Create…
A: ALGORITHM:- 1. Declare and initialise the array with XCOMPUTERS. 2. Take input integer from user. 3.…
Q: What are four distinct features of the Mac OS operating system that distinguish it from the Windows…
A: mac-OS is the operating system that runs on all Mac computers. It allows you to perform things that…
Q: What is the distinction between a termination decision and a replacement or retirement decision?
A: Intro Termination decision Termination decision :- In general way , Termination means the provider…
Q: What are some of the network-layer services that a link-layer protocol can provide? What IP services…
A: Some of the services that a link-layer protocol can provide to the network layer are as follows.…
Q: Explain how expansion cards may increase the processing capabilities of a microcomputer.
A: Introduction: An expansion card (also known as an expansion board, adapter card, or accessory card)…
Q: What influence does virtualization have on host or guest scheduling?
A: Virtualization: Virtualization is planned and carried out to run numerous working frameworks on a…
Q: 12. Write a for loop that sums the odd values from the LIST_SIZE element array list. For example,…
A: I give the code in Java along with output and code screenshot
Q: fference between Entity and Ses
A: IntroductionJavaBeans is a portable, platform-independent Java programming language model. Beans are…
Q: Error SQL query: Copy create table login ( userid int AUTO_INCREMENT PRIMARY KEY,Username varchar…
A: Below is the answer to above query. I hope this will be helpful for you...
Q: What is the aim of networking software that allows teachers and students to communicate with one…
A: Introduction Networking software is a foundational element for any network. It helps administrators…
Q: Using an example, discuss IPV4 Header formats Flag and Fragment offset.
A: IPV4 Header formats Flag: The IPV4 Header format has a width of 20 to 60 bytes, which includes…
Q: What negative impact did 'WannaCry' malware have on its victims and their systems?
A: Introduction: When it comes to malware, WannaCry is a game changer.
Q: What factors may cause a network to stutter?
A: Introduction An overworked router might be a significant contributor to internet stuttering. When…
Q: Given the following statement, what will display to the screen? System.out.print("Sum is:" +…
A: In step2, I have provided correct answer with brief explanation--------------- In step3, I have…
Q: explain every line in phytone code in colab below pls: # f(x) = tanx, f'(x) = 1 / cosx^2, f'(1),…
A: I have provided the answer in step 2 with description.
Q: So, what exactly is the difference between active and passive vulnerability scanners when it comes…
A: Network activity is monitored by passive scanners, while active scanners are capable of simulating…
Q: What is the relationship between the components of the BI architecture to produce a unit system?…
A: Introduction: 1. A decision must be taken in order to properly coordinate the use of trade insights…
Q: What is the distinction between a socket and a port?
A: Intro A socket has three things: IP address Transport protocol Port number A socket means a single…
Q: What is the difference between static and dynamic memory allocation?
A: Introduction: Programs are used to communicate with the computer system and offer instructions. The…
Q: What form of 3-D graphics software is created for architects and engineers who utilize computers to…
A: Computer-Aided Design Computer-aided design software is a form of program that allows you to…
Q: 1. Which of the following is not part of the EC framework? A. People B. Places C. Public Policy D.…
A: as requested only answers are given and no explanation is given. please find answers in answer…
Q: computer science - Why is all-subsets regression better to stepwise regression?
A: Intro Stepwise regression chooses a model by automatically adding or eliminating individual…
Q: What kind of software architectural style would you employ when building a web-based mental health…
A: Introduction
Suppose we have the function f(n) = (n+1)3. Below are a number of statements regarding how the feature grows depending on n
only B is true
B and F is true
B,C,D,F true
B,D,F is true
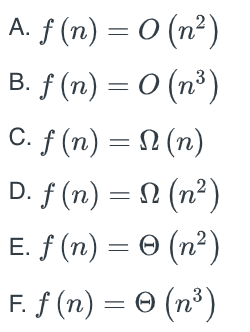
Step by step
Solved in 3 steps with 2 images

- Write a program to compute sin(x) for given x. The user should supply x and a positive integer n, where sin (x) = x - x 3 /3! + x5 /5! - x 7 /7! + x9 /9! +……+x n /n!Let A = {c, n, b}, B = {x, y} and C = {0, 1}. Find A)A X B X C B)C X B X A C)B X C X CWrite a program to compute the most frequent numbers in vectors ( x ), and ( y ) if x= a*b y=a* c a = [ 1 3 ] b = [ 2 3 5 ; 4 7 8 ] b = [ 2 3 3 ; 4 7 7 ]
- Find f(1), f(2), f(3), f(4), and f(5) if f(n) is defined re-cursively by f(0) = 3 and for n = 0, 1, 2, ... a) f(n + 1) = −2f(n).b) f(n + 1) = 3f(n) + 7.Write a program that reads N from the user and compute the following series: (N-1)-((N-2)^2) /8+ ((N-3)^3) /27-....................+1/N^3RSA How do you find a ‘p’ and ‘q’ given a number n and φ(n)? Using x^2 - [n-φ(n)+1]x+n = 0 to find p and q. p and q are relatively prime. n=pq Φ(n) = (p-1)(q-1) Give an Example.
- If f(n) = n^2 log n and g(n) = n^2, then f(n) is what O, Ω or Θ (g(n))Given a positive integer, N, the ’3N+1’ sequence starting from N is defined as follows: If N is an even number, then divide N by two to get a new value for N. If N is an odd number, then multiply N by 3 and add 1 to get a new value for N. Continue to generate numbers in this way until N becomes equal to 1. For example, starting from N = 3 the complete ’3N+1’ sequence would be:3, 10, 5, 16, 8, 4, 2, 1 Do the following: Write a code in C++ to ask the user to enter a positive integer (N) in the main() function. Write a function sequence() that receives the integer value N and display the ‘3N+1’ sequence starting from the integer value that wasreceived (entered by the user). The function must also count and return the numbers that the sequence consists of. The returned value must be displayed from the main() function. Example input and output is given in the following image.Consider a base 26 number system wherein the letters of the alphabet are the digits. That is, A=0, B=1, C=2, … Z=25 in base 10. Use the MAL as a number in the base 26 system, and KHA as another number in the base 26 system.Add these numbers together to obtain the sum in based 26. Example 1 — if your first name is “Peter” and your surname is “Pan”, then add up PET26 and PAN26, and show the sum in base 26.Example 2 — if your first name is “Peter” and your surname is “Pa”, then add up PET26 and PAA26, and show the sum in base 26.

