symbolic form of the proposition
Q: What are the advantages of using automated testing in the workplace?
A: Overview: Automated security testing, vulnerability testing, and cyber testing are all terms…
Q: Explain why many IT professionals may disregard project expense management and how this may impact…
A: Define: Cost accounting is normally unbroken lower in IT project management. Most comes are oriented…
Q: Verifying and validating are two different things when it comes to testing software.
A: Verification and validating in context of software testing
Q: What is the difference between computer organization and computer architecture in broad terms?
A: Computer Architecture: A blueprint for the design and execution of a computer system is known as…
Q: Write the difference between a backdoor, a bot, a keylogger, spyware, and a rootkit? How to get rid…
A: ANSWER:-
Q: For a processor that can decode encrypted data and system instructions, a variety of approaches have…
A: Introduction: The ability of a contemporary computer to both receive and generate data is contingent…
Q: What is the impact of the mechanism used to handle interrupts on the machine's performance?
A: Legacy interruptions: Is the term used to describe incursions that are dependent on wires. In most…
Q: What are the differences between testing strategy and testing methodology?
A: Introduction: The differences between testing strategy and testing methodology are :
Q: mail server DoS attack is classified as: Attacks on interception, interruption, falsification, and…
A: Dos attack classification.
Q: Describe two problems that current information systems are seeking to tackle
A: Information systems are systems that gather, store, and exchange data among different systems. An…
Q: Why is there a layer for networks if they're already connected?
A: This layer's primary function is to deliver packets from the source to the source of most…
Q: There are several reasons why JMeter is the most often used tool for performance testing.
A: Introduction: There are several reasons why JMeter is the most often used tool for performance…
Q: The phrases "hardware" and "software" are sometimes used interchangeably.
A: Hardware Software: Hardware a and software are the two components of a computer system. The actual…
Q: How much better are hardware interrupts than software ones? Do you know when each one is…
A: Introduction: The microcontroller or an external GPIO that has been configured to act as an…
Q: Which of these statements is incorrect: 0 One key is used for encryption and another for decryption…
A: Public Key Cryptography: In public-key cryptography, one set of keys was used for encryption, while…
Q: Describe Information system analysis
A: answer is
Q: What exactly is a computerized information system? Explain and clarify things using just your own…
A: Information system : An information system is an integrated collection of components for acquiring,…
Q: Is it a concern if information systems aren't integrated
A: Several computer issues, such as computer loss and malfunction, lead to wasteful expenditures and…
Q: ever becomes true. A. True B. False 2. A loop that never ends is reffered to as a/an:. What it is?…
A: 1.) False.- If the condition keep becoming true again and again the loop will keep executing itself.…
Q: To learn more about White box testing, where can I go?
A: White box testing: The developer will do white box testing, in which they will examine each of the…
Q: Test Coverage" is a word used in manual testing.
A: What is Test Coverage in Manual Testing Test coverage determines if our test cases cover the…
Q: Provide examples of how the following criteria may be rewritten quantitatively. To convey the needs,…
A: A Library system is an enterprise resource system used to track and catalogue the books, items,…
Q: 12. The time interval from starting to fetch and instruction until its execution completes is…
A: The data in computer system is reside in the memory. The bus system which is basically network of…
Q: Is it possible to have concurrency in operating system threading without parallelism?
A: yes, it is possible to have the concurrency in the operating system threading without the…
Q: Why are interrupt handling systems so important for machines?
A: Operating system: An operating system (OS) is software that manages computer hardware and software…
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: What are the three major topologies for local area networks (LAN)?
A: There are three main LAN topologies: Circular bus Ring \sStar.
Q: The only restrictions I can think of are: The methods used to evaluate software are known as Is it…
A: Domain testing is subject to the following constraints: (1)General restrictions(2) Consequential…
Q: How do we define a "computer" in our everyday speech?
A: A computer is a gadget that acknowledges data (as digitalized information) and controls it for some…
Q: ative scales be used to assess cross-level
A: There are two distinct kinds of levels that make up the cross-level directing impact. These are…
Q: In the context of sequential decision making, does dynamic programming provide any advantages?…
A: Answer: Dynamic programming is an algorithmic method of solving problems that are often used to…
Q: i need the answer quickly
A: Let us see the answer below,
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: Why are data and processing models increasingly relying on DFDs?
A: answers the previous question: Solution:- The benefits of DFDs have boosted their application in…
Q: Explain how DB administrators may utilize Views to allow users to interact with the DBMS effectively…
A: The database management system is an improved way of data storage, and the user does not need to…
Q: Please define each of the words listed below. a) Artificial intelligence; b) an agent; c)…
A: Artificial intelligence: Artificial intelligence is a hypothesis and advancement of Computer…
Q: Why not split down the whole design into many user views while doing user research?
A: Introduction: In general, a design process can assist a designer or design team in making rapid…
Q: Different testing methodologies are needed at different phases of the software development life…
A: Methodologies: Explain the necessity for different testing methodologies at different phases of…
Q: Equipment and training are essential for every professional to explore and resolve issues. An…
A: Introduction: Operating system technicians are in charge of installing, configuring, and maintaining…
Q: How may an IT system be implemented?
A: IT Systems means all electronic data processing, information, record keeping, communications,…
Q: mann Cycle is broken down? What happens to the CPU and the m
A: Introduction: Below the how the Von Neumann Cycle is broken down
Q: Please Educate Me on the Terms "Interrupt and "Disruption." Hardware malfunctions should be…
A: Introduction: The accumulation of dust is one of the most common reasons for the malfunction of…
Q: ple in this circumstance.
A: A real world example utilizing no less than three sets that utilization a Venn diagram. A Venn…
Q: What are the pros and disadvantages of information systems?
A: A system for gathering, processing, and analyzing information in an organized way. These are some of…
Q: What form of communication channel is created by connections established between ATM service…
A: The services supplied by ATM networks are those that transport subscriber sessions to the access…
Q: Let A ={1, 4, 7, 10, 6, 5}, B = {4, 8, 10, 2, 9}, and C = {2, 3, 4, 5} Write the Venn diagram…
A:
Q: Does it matter if you're in a production or testing environment?
A: Introduction: You may execute your update against a controlled set of data in a test environment…
Q: The SECI paradigm is compared to other knowledge management techniques.
A: Introduction To learn more about the SECI model, go here. Nonaka suggested it in 1991, and Nonaka…
Q: For example, what are the variations in software development in terms of the terms cohesion" and…
A: Introduction: The variations in software development in terms of the terms cohesion and coupling are…
Q: To put it another way, what exactly is "parameterized testing"?
A: Introduction: JUnit, the most recent version of JUnit, has been updated to include a number of new…
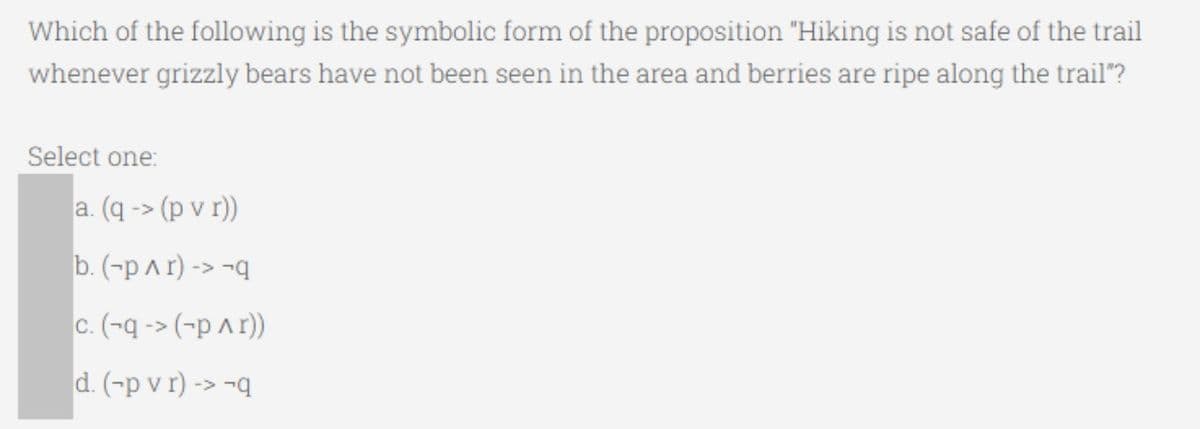
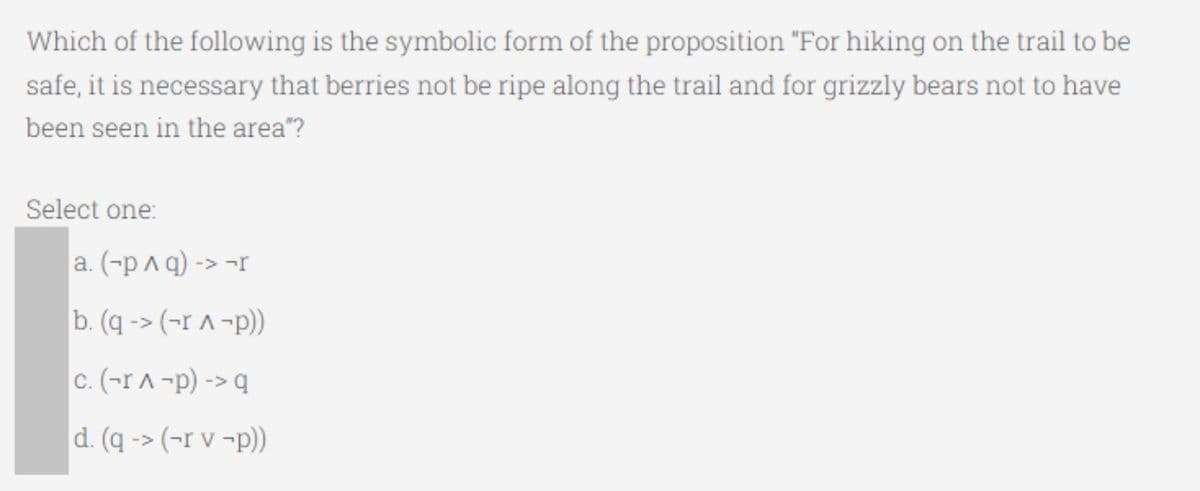
Give the correct answers. (Numbers 2 and 3 are the pictures shown)
1. Determine if the proporsotion (p→q) ↔ (q ∨ ¬p) is a tautology, contradiction or contingency.
Step by step
Solved in 2 steps

- You are given n users, and their times that they log in and out of a website: You are interested in which users are on the site at the same time. For example, you are given the following 5 users and their times: User 1- In: 1 Out: 4 User 2- In: 2 Out: 5 User 3- In: 7 Out: 8 User 4- In: 9 Out:10 User 5- In: 6 Out:10 This gives the distinct users that are on the site at the same time as (1,2), (4,5), and (3,5). Given n elements, write pseudocode for an algorithm that would take n^2 time to compute the number of pairs of users that are on the site at the same timehich of the following statements about Disability adjusted life years (DALYs) and Years of Life Lost (YLLs) due to a specfic disease in a specific location and year, is/are correct? a. To compute the DALYs, you will only need a list of all premature deaths in that location over the year, that were caused by the disease, age at death, and no further information b. To compute the YLLs, you will only need a list of all premature deaths in that location over the year, that were caused by the disease, their age at death, and no further information c. YLLs is expected to be a larger number than DALYs d. To compute YLLs, you will also need to know the period of time (in years) that people were not completely healthy due to the specific diseaseWhich of following K-map matches : f=∑(2,5)+d(3,7) Question 47 options: 0 1 d 0 1 0 d 0 0 1 d 0 0 d 0 1 0 0 d 1 0 1 d 0 0 0 d 1 0 d 1 0 Which statement is true about dynamic binding? A. the binding of a function call and the function definition occurs at compile time B. the binding of a function call and the function definition occurs at run time C. the binding of the type of a variable and the variable name occurs at run time D. the binding of the type of a variable and the variable name occurs at compile time
- In the language R: Which of the following statements is NOT correct about picking colors for your figures? Select one: The scale_fill_manual() function allows us to define different gradient colors for lower or higher numerical values We should pick a graded color scheme for an ordered categorical variable (e.g., level of education) We should pick distinct colors for an unordered categorical variable (e.g., country, gender…) We should pick colors based on their ability to express the data we are plottingTID items_bought 100 {M, O, N, K, E, Y} 200 {D, O, N, K, E, Y} 300 {M, A, K, E} 400 {M, U, C, K, Y} 500 {C, O, K, I, E} Which of the following are maximal itemset in the table above, when minsup is 40%? a. {K, C} b. {M, K} c. {O, N, K, Y}Computer Science Determine the output of the following queries. mystery2(L, [], []). mystery2(L, [H|T], [H|M]) :- member(H, L), mystery2(L, T, M). mystery2(L, [H|T], M) :- \+ member(H, L), mystery2(L, T, M). mystery2([a, b], [], L). mystery2([a, b], [], [a,b]). mystery2([a, b], [a, b], L). mystery2([a, b, c], [c, e, f], L). mystery2([], [a,b], L). In English, what does this rule do?
- Create a SuffixArray client that, given a string, determines the smallest lexicographically feasible cyclic rotation in linear time. This issue occurs in databases for circular molecules in chemistry, where each molecule is represented as a circular string and a canonical representation (smallest cyclic rotation) is used to enable searches with any rotation as the key. Create a SuffixArray client that, given a string, determines the smallest lexicographically feasible cyclic rotation in linear time. This issue occurs in databases for circular molecules in chemistry, where each molecule is represented as a circular string and a canonical representation (smallest cyclic rotation) is used to enable searches with any rotation as the key.The Fibonacci numbers are the numbers in the following integer sequence. For example, 0, 1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, ... In mathematical terms, the sequence ?? of Fibonacci numbers is defined by the recurrence relation. ??=??−1+??−2 with seed values ?0=0 and ?1=1. Write a function named problem5 to find the sum of Fibonacci numbers that are even and less than 20000. Call your function and display the return result Subject: Python ProgrammingWhat will the following code return? (R) V1 <- c (1, 22, 33) V2 <- c (“Hi”, “there”, “friend”) V3 <- c (11, 3, 2016) D <- rbind (V1, V2, V3) D [3,2]
- As a software engineer, you are hired to arrange cricket players based on their country and type. You have given all the player’s information in a tuple called my_tuple. The players are from 3 countries which are Bangladesh, Australia and England. There are 2 types of players which are “Batters” and “Bowlers” You are given the following nested tuple where each element in the my_tuple is a tuple consisting of a name and a 4 digit ID. my_tuple = (("Mominul", 1101),("Mustafiz", 1202),("Bell", 2101),("Cook", 2103),("Smith", 3101),("Finch", 3102),("Starc", 3203), ("Imrul", 1103), ("Taijul", 1204)) Write a python program that will convert this tuple into the following dictionary using the process described below: Your code should work for all types of similar tuple if the sample input is changed. Output dictionary (You just have to print the resultant dictionary. No need to follow the pattern below) { 'Bangladesh': { 'Batters': ('Mominul', 'Imrul'), 'Bowlers':…As a software engineer, you are hired to arrange cricket players based on their country and type. You have given all the player’s information in a tuple called my_tuple. The players are from 3 countries which are Bangladesh, Australia and England. There are 2 types of players which are “Batters” and “Bowlers”You are given the following nested tuple where each element in the my_tuple is a tuple consisting of a name and a 4 digit ID.my_tuple = (("Mominul", 1101),("Mustafiz", 1202),("Bell", 2101),("Cook", 2103),("Smith", 3101),("Finch", 3102),("Starc", 3203), ("Imrul", 1103), ("Taijul", 1204))Write a python program that will convert this tuple into the following dictionary using the process described below: Your code should work for all types of similar tuple if the sample input is changed.Output dictionary (You just have to print the resultant dictionary. No need to follow the pattern below){'Bangladesh': { 'Batters': ('Mominul', 'Imrul'), 'Bowlers': ('Mustafiz', 'Taijul')…I. Let P (x) be the statement “2x = x2 .” If the domain consists of the integers, what are the truth values? a) P(0) b) P(1) c) P(2) d) P(−1) e) ∃x P(x) f ) ∀x P(x) 2. Let Q(x) be the statement “x > x - 1.” If the domain consists of all integers, what are the truth values? a) Q(10) b) Q(−2) c) Q(999) d) ∃x Q(x) e) ∀x Q(x) f) ∃x ˺Q(x) g) ∀x ˺Q(x)

