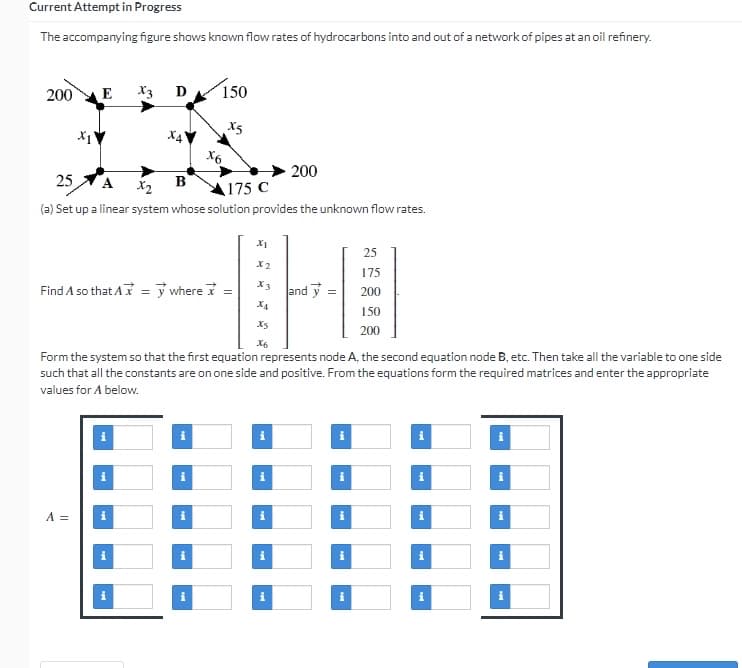
The accompanying figure shows known flow rates of hydrocarbons into and out of a network of pipes at an oil refinery. E 200 X3 D 150 X5 X4V 200 25 A X2 B 175 C (a) Set up a linear system whose solution provides the unknown flow rates. XI 25 X2 175 X3 Find A so that A = y where = 200 and y= 150 X5 200 X6 Form the system so that the first equation represents node A, the second equation node B, etc. Then take all the variable to one side such that all the constants are on one side and positive. From the equations form the required matrices and enter the appropriate values for A below. A = X₁ x6 Mi
The accompanying figure shows known flow rates of hydrocarbons into and out of a network of pipes at an oil refinery. E 200 X3 D 150 X5 X4V 200 25 A X2 B 175 C (a) Set up a linear system whose solution provides the unknown flow rates. XI 25 X2 175 X3 Find A so that A = y where = 200 and y= 150 X5 200 X6 Form the system so that the first equation represents node A, the second equation node B, etc. Then take all the variable to one side such that all the constants are on one side and positive. From the equations form the required matrices and enter the appropriate values for A below. A = X₁ x6 Mi
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter11: Nonlinear Programming
Section11.10: Quadratic Programming
Problem 7P
Related questions
Question
Transcribed Image Text:Current Attempt in Progress
The accompanying figure shows known flow rates of hydrocarbons into and out of a network of pipes at an oil refinery.
200
E
X3 D
150
X5
X₁'
200
25 A
B
x2
175 C
(a) Set up a linear system whose solution provides the unknown flow rates.
25
X2
175
X3
Find A so that Ax=y where =
and y
= 200
THO
150
200
Form the system so that the first equation represents node A, the second equation node B, etc. Then take all the variable to one side
such that all the constants are on one side and positive. From the equations form the required matrices and enter the appropriate
values for A below.
A =
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole