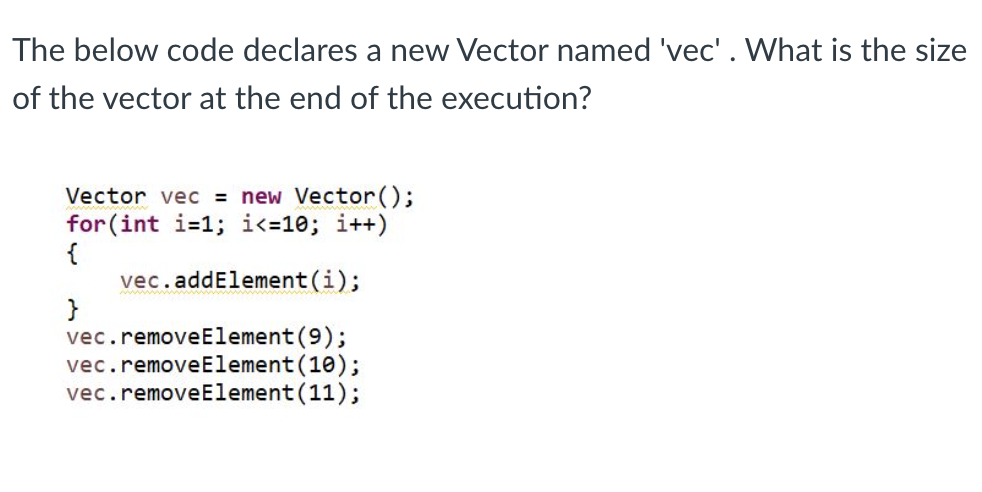
The below code declares a new Vector named 'vec'. What is the size of the vector at the end of the execution? Vector vec = new Vector(); for(int i=1; i<=10; i++) { vec.addElement(i); vec.removeElement(9); vec.removeElement(10); vec.removeElement(11);
Q: The goals of a security incident response strategy should include the prevention of theft and…
A: The question has been answered in step2
Q: What are the most effective ways for guaranteeing the network's continuing availability and…
A: LAN (Local Area Network): A local area network (LAN) consists of small computers or other…
Q: The following statement always evaluates to 1 (True or False): x > 0 || -x >= 0 True False
A: It is defined as a low-level programming language for a computer or other programmable device…
Q: In this lab you will construct an assembly routine that puts the ASCII representation of an input…
A: // C# Program to interpolate using Bessel's interpolation
Q: Do you have any recommendations for mitigating the risk posed by the network?
A: Network security. Network security. -> Network security is crucial for every firm nowadays, since…
Q: This layer is referred to as "intermediary" and is responsible for connecting our client servers to…
A: The layer between the database and the client servers is called the "intermediary layer." The…
Q: When precisely should a network upgrade be scheduled, and for how long?
A: Introduction: As a result of developments in technology, business operations may now be conducted…
Q: Explain the benefits and drawbacks of connectionless protocols as an alternative to connection-based…
A: To Do: to discuss the advantages as well as the disadvantages of connectionless protocols. About…
Q: Specify in further detail how establishing a wireless network may be useful in the case of a…
A: According to the information given:- We have to define establishing a wireless network may be useful…
Q: On behalf of a financial institution, participate in the Risk Management Process. Please explain…
A: Start: Conduct a financial institution's risk management process. In 300 words, explain your…
Q: Clarify why online applications must be safe. Why is having a secure application essential? SQL…
A: Introduction Web application security uses several strategies and procedures to secure browsers and…
Q: Are you able to distinguish between inherent hazards and those that can be managed?
A: In this question we need to explain the differences between inherent hazards and hazards that can be…
Q: Why is it better to analyze risk using intervals of chance and consequence rather than precise…
A: Introduction: When doing a risk assessment, it is best to work with a range of possible outcomes…
Q: When precisely should a network upgrade be scheduled, and how long will it take?
A: Technology advancements have made it possible for the business to operate more quickly and…
Q: Two instances of this are the repetition of information and the inability to define data. Explain…
A: The correct answer is given in the following steps for your reference.
Q: To comprehend compilers, you must understand six things.
A: According to the information that has been provided: We are required to specify the compilers, since…
Q: What are the benefits of using the exception handling technique?
A: Introduction: The handling of exceptions is what ensures that the normal operation of a programme is…
Q: Here, the distinctions between "connectionless" and "connection-based" protocols are examined.
A: This comparison examines the benefits and drawbacks of connectionless protocols versus…
Q: how to present many to many relationship
A: When records from one table are linked to those from another, there is a many-to-many relationship…
Q: On disk, operating systems endeavor to store files in sequentially arranged blocks. The usage of…
A: Given: Operating systems by default save subsequent blocks of a file on succeeding disc sectors.…
Q: 4. List and briefly define the four most commonly cited operational areas for KPIs.
A: The question has been answered in step2
Q: Various operating systems arbitrarily install disk folders in various locations on the hard drive.…
A: Introduction: A Hard drive's directories Disc directories transfer data from logical files into…
Q: What kind of statements are often included inside a try block?
A: Exception Handling: An exception is a problem that occurs during the execution of a programme; it…
Q: Describe briefly five techniques for mitigating the risk of an information security compromise.
A: Risk Control Strategies are used by IT and InfoSec teams to limit vulnerabilities and manage risks…
Q: Information technology in the twenty-first century: boon or bane? - 1000-word essay
A: "Technology that is free from hatred may be a benefit. The technology used in contempt is usually…
Q: We are using the simple model for floating point representation which is a 14-bit format, 5 bits for…
A: ANSWER:-
Q: The operating system organizes the file blocks on the hard drive in sequential order. What function…
A: Given: The physical elements, such as magnetic media, motors, and controllers, as well as the…
Q: What are, in your view, the six most compelling reasons to learn about compilers?
A: Compilers: A compiler transforms a programmer's or computer language's type into another. Some…
Q: What are the appropriate steps to take in the event of a breach of healthcare data?
A: Breach of health care data can have adverse effect on health care organizations and technology.
Q: s Anyone Know How To Create A Boot Disk That Is Compatibl tiple Operating Systems?
A: Introduction: When discussing computers, the terms "booting," "starting," and "powering on" are…
Q: Does it make sense to have rewritable optical discs? How is it possible to overwrite the disc if…
A: Laser Disc A circular (usually) and flat optical disc is used to store data on an optically readable…
Q: What are the most effective ways for guaranteeing the network's continuing availability and…
A: Regional Area Network: A local area a network (LAN) is group of small computers or other…
Q: When precisely should a network upgrade be scheduled, and for how long?
A: A network update is a change or addition of integrated transmission-related infrastructure…
Q: Discuss the distinctions between primary, candidate, and superkey.
A: Introduction In this question, we are asked to distinguish between primary, candidate, and super key
Q: What is a challenge-response authentication system? Specify it here. Why is this method more safe…
A: Given: Describe Challenge Response Authentication system and details around why it's more safe then…
Q: Suppose there exists a catch handler that matches the exception object type perfectly. Under what…
A: The normal flow of a program's execution is interrupted by an occurrence known as an exception. The…
Q: Why is it better to analyze risk using intervals of chance and consequence rather than precise…
A: The potential that an occurrence will occur is referred to as the probability, while the amount to…
Q: Does it make sense to have rewritable optical discs? How is it possible to overwrite the disc if…
A: Laser Disc Data is stored on an optically readable medium using an optical disc, which is typically…
Q: The multiple aspects of a compiler must be taken into consideration in order to generate efficient…
A: The steps listed below a could lead to the answer:- A group of the guiding principlesThe creators…
Q: The LC-3 provides two output TRAPS for strings: PUTS (TRAP x22) and PUTSP (TRAP x24). Both of these…
A: Answer1 As the given assignment is large so it is unable to answer full assignment in a single…
Q: The layer between the database and client servers is referred to as the "middle layer."
A: Database architecture: A DBMS architecture permits dividing the database device into character…
Q: Create a structure TimeStamp which has the following private members: • Time time; • Date day;…
A: #include <iostream> using namespace std; struct Time{ // structure to hold time int…
Q: Presbyopia is a condition in which a person's ability to adjust to changes in visual acuity…
A: Introduction: Presbyopia is caused by the ageing of the eye, which makes it harder for the eye to…
Q: Please include the names of the three distinct exception-handling processes.
A: Given: Name three exception-handling techniques. Answer: Three exception-handling strategies: Then…
Q: What are the benefits of doing regular code audits?
A: There are many benefits to doing regular code audits, including: 1. Ensuring code quality: Code…
Q: This layer is referred to as "intermediary" and is responsible for connecting our client servers to…
A: We have to explain which layer is referred to as an "intermediary" and is responsible for connecting…
Q: Two students are enrolling in the same course, but there is only one open seat. Is it feasible to…
A: Given: There are two college students that must sign up for the course. However, there is just one…
Q: Why do different operating systems store disc directories in different locations on discs? What are…
A: 8 advantages of travelling for health It's excellent for your mental well-being. As a result, you'll…
Q: Using NetBeans, perform the following. 1. Convert one (1) sample Python script in 02 Handout 1 into…
A: SOLUTION: -->We need to have the code for the recursive function. -->For the name A-F, we…
Q: What are the MDM approaches for database management
A: MDM full form is master data management. There are two forms of master data management that can be…
Step by step
Solved in 3 steps with 1 images

- void getVectorSize(int& size); void readData(vector<Highscore>& scores); void sortData(vector<Highscore>& scores); vector<Highscore>::iterator findLocationOfLargest( const vector<Highscore>::iterator startingLocation, const vector<Highscore>::iterator endingLocation); void displayData(const vector<Highscore>& scores); The size parameter from the given code won't be needed now, since a vector knows its own size. Notice that the findLocationOfLargest() function does not need the vector itself as a parameter, since you can access the vector using the provided iterator parameters. The name field in the struct must still be a c-string The focus of this assignment is to use iterators. You must use iterators wherever possible to access the vector. As a result, you must not use square brackets, the push_back() function, the at() function, etc. Also, the word "index" shouldn't appear in your code anywhere. You won't get full credit if…A vector contains the grades obtained by students of a class in an assessment, with the following characteristics: Notes are actual values between zero and ten.If the value is equal to -1.0, then this means that the student has missed the assessment.The average approval rate at this University is 6 (six).Write a program that reads two vectors: the note vector described and a vector containing the students' names of the same size. As an output, print the following information in the console in this order: How many students missed the evaluation?How many students have been approved?Among the students present, how many students failed?Among the students present, what was the average grade, with up to two decimal places of accuracy?What's the name of the student who got the highest grade in the class?TipsCreate different counters to find the value of outputs 1 through 4. These counters are different from the loop counter that traverses the vector;Within the while loop, use five independent…In c++ i’v read a text file and stored a string from the text file in to a vector, now i will like to accest a specific string in the vector how will i do this? Example of the text file A B C D I wil like to access “B” which is part of the vector i created.
- Write a program in C++ using a vector to create the following output. Declare a vector named numbers - Don’t specify a size and don’t initialize with values. Starting with 2, pushing these into the back of the vector: 2, 4, 6, 8, 10 vector capacity (array size) changes and is dependent on the compiler. The size of the list is now 5. The vector capacity (array size) is 6. The back element is: 10 The front element is: 2 Now deleting the value at the end of the list . . . The size of the list is now 4. Note: The swap() function is defined in the <algorithm> header, and is not a vector function. No object calls the swap() function. Do it like this: swap(numbers.first(), numbers.last()); After deleting, here is the list: 2, 4, 6, 8 Now swapping the first number with the last number. After swapping, here is the list: 8, 4, 6, 2 Now inserting 0 at the beginning of the list. After inserting, here is the list: 0, 8, 4, 6, 8 The…C++ Provide a different implementation of ChoiceQuestion. Instead of storing the choices in a vector, the add_choice function should add the choice to the question text. For this purpose, an add_line function has been added to the Question class. Complete the following file: choicequestion.cpp Use the following files: choicequestion.h #ifndef CHOICEQUESTION_H #define CHOICEQUESTION_H #include <string> using namespace std; #include "question.h" class ChoiceQuestion : public Question { public: /** Constructs a choice question with a given text and no choices. @param question_text the text of this question */ ChoiceQuestion(string question_text); /** Adds an answer choice to this question. @param choice the choice to add @param correct true if this is the correct choice, false otherwise */ void add_choice(string choice, bool correct); private: int num_choices; }; #endif question.h #ifndef QUESTION_H #define QUESTION_H #include <string> using namespace std; class Question {…A) Write a program and define a class of Student. Student has these attributes :Age (an int)FirstName (a string)LastName (a string)Social Security Number (an int)Add the default constructor Add a second constructor that sets the attributes of the class Add the copy constructor that creates a copy of the student and override assignment operator. B) Create a vector of 100 students. Use a for loop to fill the vector . C) Add a function to your program that sorts the vector using selection sort in ascending order . D) Add a function to your program that searches the vector using binary search to find the youngest student .
- Write a function that removes duplicates from a vector. For example, if remove duplicates is called with a vector containing 1 4 9 16 9 7 4 9 11 (use these numbers) then the vector is changed to 1 4 9 16 7 11In C++ programming Language using Visual Studio(Not Visual Studio Code) Suppose you have a vector of integer data, say { 1, 5, 4, 2, 3 }The data may eventually need to be transformed into some other form, say by sorting the data values for instanceThis would turn the vector into { 1, 2, 3, 4, 5 }Or say I wanted to take the original vector { 1, 5, 4, 2, 3 } and remove all the even numbers from itThis would turn the vector into { 1, 5, 3 }So in general terms, we start with an input vector, and it somehow gets transformed into its transformed vectorThe options really are almost limitless, but we will keep things simple for this checkpoint assignmentWe will be developing a base/derived class relationship that can perform custom transformations of data at runtimeYour submission must follow OOP best practices that incorporates topics in Gaddis' textbook chapters 13 through 15 { 1, 5, 4, 2, 3 } ==========(SORT)==========> { 1, 2, 3, 4, 5 }{ 1, 5, 4, 2, 3 } ======(REMOVE EVENS)======>…when analyzing data sests such as data for human heights or for human weights a common step is to adjust the data this adjustment can be done by normalizing two values between 0 and 1. write a code block that reads(from user input) a list of 5 numbers and stores them in a vector of doubles. then, the block adjusts the values by dividing all of them, by the largest value. output each floating point value with two digits after the decimal point, which can be acheived by execeuting cout << fixed << setprecision(2); once before all other cout statement.
- Assume you have a non-empty vector vec in your Matlab workspace. Will the following command: >> length(vec(vec == max(vec))) count all elements in vec with values equal to the maximum value in vector vec? Yes NoIn PYTHON Write a function that prints multiple times a vector from its first element up to the next occurrence of an element having value equal to a provide number Each print stops at the i-th occurrence of the provided number Use while loop(s) Function Name:vec_multi_print_to_number Parameters:a_vector,a_value Return:none Example: Input:my_vector=[5,6,7,8,9,5,6,7,8,9] Invokefunction:print_up_to_value(my_vector,7) Output:[5,6,7,8,9,5,6,7]Which of the following is NOT a correct instantiation of the Vector class? Select one: a. Vector v1 = new Vector(4); b. Vector v2 = new Vector(4, 1); c. Vector v = new Vector(); d. Vector v2 = new Vector(4, 1, 2);

