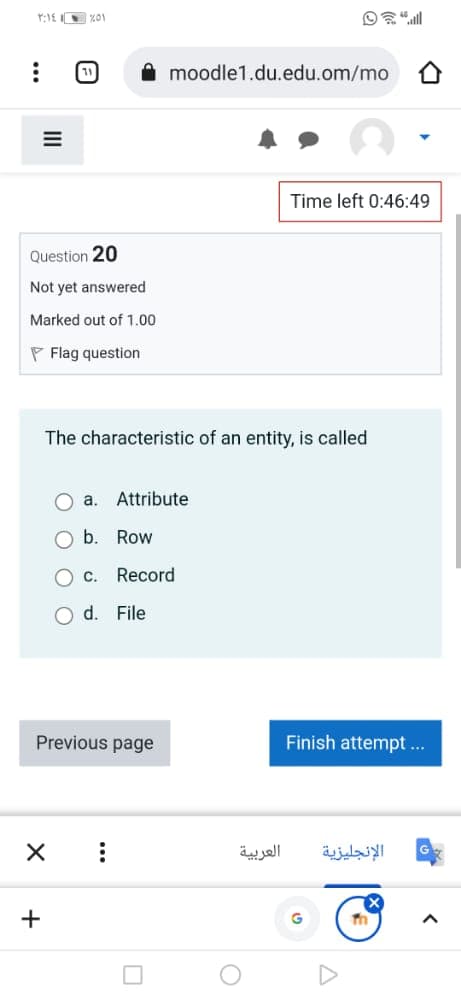
The characteristic of an entity, is called a. Attribute O b. Row O c. Record O d. File
Q: Which the following question,Subject_Code is a(n) __________ and Subject is a(n) __________?…
A: To find the correct option for the Subject_Code and Subject. Database: It is a collection of…
Q: How and why is user view often developed? Give an example?
A: The user views help the developer to ensure that no major database user is missed while developing…
Q: 3. Convert the following E-R diagram into a relational schema. UserID RegNo PublisherID Name Pubyear…
A: The design and structure of the given ER diagram has been shown below.
Q: Create the database name Company which consists of one Entity name Employee which consists of 10…
A: Note: As per the guidance can answer the first three sections. Please re-submit the question for the…
Q: def distance_between_entities(entity1, entity2): """ compute the haversine distance between the two…
A: import numpy as np def distance_between_entities(entity1, entity2): lat1 = entity1[3] lon1 =…
Q: 1.State TRUE or FALSE. A logical representation of the database structure is obtained by carefully…
A: 1. Interview: It is a good way to get feedback on the developed product, from the customer and…
Q: A)Which of the following are used to indicate cardinality symbols? a.WITH b.P c.None of the…
A: A) Cardinality symbols: Cardinality of a relationship defines the number of instances which can be…
Q: Exploratory Data Analysis a. Preprocessing The EDA process begins with loading the data into the…
A: First you need to see the series of panda in python.... Pandas .size, .shape and .ndim are utilized…
Q: TRUE or FALSE - A super-entity can only have two sub-entities and no more.
A: A SUPER-ENTITY CAN HAVE MORE THAN TWO SUB-ENTITES
Q: An application that includes data about countries, cities, hotels, ... etc. which provides location…
A: Now every organization contains a certain amount of data that needs to be stored for future use and…
Q: Course (course_id,sec_id,semester) Here the course_id,sec_id are Your answer The model is…
A: Here the course_id, sec_id and semester are Attributes.
Q: Explain why an index is only helpful if the values of an attribute are sufficiently varied
A: Introduction Use of an index with a wide range of values A file index is a table or other data…
Q: Airport Flight Arrive Num State ABC Select one: O a. ERD incorrect O b. The relationship Arrives…
A: The ER(Entity Relation) diagram is used to represent the relationship between the different entity…
Q: The set of 7 attributes is { desc, drought, price, sci, size, store, The attributes are for plants…
A: To find the key for all attributes for the given dependency.
Q: Explain the differences between variables and attributes in three pages.
A: Step 1) Variables : A variable is a characteristic of any entity being studied that is capable of…
Q: Create a new database and rename it with your name. Create a new table called "Courses". Set an…
A: 1. Create a database and rename Open Microsoft Access-> clicl on file-> click on save database…
Q: Complete Each Entity's relationship. ex) A CUSTOMER makes many ORDER And if ther is any errors or…
A: The following relations exists in the given Entity Relation Diagram: A CUSTOMER makes many ORDER. A…
Q: What is a private key? O a. A primary key of another entity b. An entity's unique identifier Oc. A…
A: Answer: The correct option is “(b) an entity’s unique identifier”
Q: The number of entities or instances that can participate in a relationship is called the Select one:…
A: The number of entities or instances that can participate in a relationship is called as Degree of…
Q: Veterinarian Office Case: Part 5 The veterinarian office created a database to keep track of owner…
A: 1. Answer : Option a. ALTER TABLE OWNER ADD PRIMARY KEY(OWNER_ID) ADD CHECK(OWNER_STATE='NV') 2.…
Q: Create a login screen description document for this system that contains at least eight basic…
A: the login form includes two inputs, links to alternative scenarios, and a submit button. Even though…
Q: For each item below, specify whether the statement is true (T) or false (F). A Database Schema keeps…
A: A database schema keeps the data in a database- True Each data model is based on a Database…
Q: QUESTION 3 An application that includes data about students' names and marks in a given course…
A:
Q: QUESTION 6 Meta-Data is a subset of the database that contains some information of user interest O…
A: Metadata is also a data Metadata provides information on other data. Refer step 2 for the answer.
Q: In a relational database, the students' records contain information regarding the Student Name,…
A: explanation: here out of all the records like student Name, Phone Number, GPA, and major. only phone…
Q: Q2- What is a composite entity, and when is it used?
A: Entity – Entities are actual world items that structure the essential locks around which the entire…
Q: What is the definition of an attribute?
A: An entity is a real object which can be identified separately Example of entity is student,…
Q: 99. The distribution in which each row denote some related values collection is classified as a.…
A: please see the next step for solution
Q: 1. Create the table with the following specification shown below: Database name: Oasis. Table name :…
A: We are using mysql for this. Create database as shown below: mysql> create database BB;Query OK,…
Q: The attribute of an entity is referred to as _______ of a table. Select one: a. Foreign Key b.…
A: Answer :-- option c) Field
Q: Complete the following task. Design a database to produce the following reports. Do not use any…
A: DBDL stands for the Database Definition Language. It has some particular standard format to…
Q: Please describe what is the purpose of the database. Your design
A: - The purpose of the database is to store and retrieve information about library materials. The…
Q: Šelect one: O a. ERD incorrect O b. Airport has no key O . There is no attributes in FlightNum O d.…
A: ER Diagram represents Entity Relationship Diagram. It shows the relationship of element sets put…
Q: ionary B- The attribute; the entity C- The entity; the attribute
A: given - Data standardization usually focuses on fixing _ of data while data cleaning usually…
Q: description. password Admin id id password Admin login Company login User name has password Android…
A: Below is the relational schema for given ER diagram:
Q: entities: Residential students which fields like student id, Student name, exam papers Transfer…
A: Given entities: Residential students which fields like student id, Student name, exam papersTransfer…
Q: Which of the following relationships models .15 the following statement: "The book contains * "300…
A: The relationship models the given statement the book contains 300 pages
Q: 6. The data type of an attribute is part of metadata in the database. Question 6 options:…
A: The given question is false.
Q: A collection of related information is known to be a. Database b. Reports c. Files d. Paging
A: 1) Database is a collection of related information stored on a computer. 2) These releated…
Q: What are Attributes ?
A: Attribute: Attribute refers to an entity property. It can also be referred to a database component…
Q: Employee (emplovee name street.city) Works (employee Name, company name, salary) Company (company…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Question 7 On ERD, you can create attributes with the same name in different Entities. Question…
A: On ERD, you can create attributes with the same name in different Entities.
Q: 4 tables for the database: PATRON, BOOK_COPY, BOOK, and CHECKOUT. (Since a book may have multiple…
A: Entity Relationship Diagram for the given case:
Q: ERD 3: The data requirements of the library application are summarized as follows: BOOK entity is…
A: Actually, database is a used to stores the data.
Q: Given the following WORKER schema in which id is the primary key. WORKER (id, name, rank, salary,…
A: Here I have first of all modified the prompt that will be displayed on executing the procedure, as…
Q: is a piece of information used to describe an entity. a. Attribute b. Associative Entity Cardinality…
A: Answering 4 and 5. According to the policies I can't solve multiple questions in one question…
Q: Computer science Explain why an index is useful only if there is sufficient variety in the values of…
A: Introduction: Basically ,Indexes are special lookup tables that can be used by the database search…
Q: An insertion anomaly occurs when a user who wants to insert data about an entity leads to delete…
A: Insertion anamoly means Inserting data into table in which all column is not filled . for an example…
Q: The information about data in a database is called _______ a. Metadata b. Hyper data c. Tera data d.…
A: The information about data in a database is provided in step2.
Q: A program is an active entity. a. True b. False c. May be d. Can't say
A: Given statement, A program is an active entity.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- EXPLORE FOUR EVERYDAY ETHICAL DILEMMAS RELATED TO CS Present an abbreviated case study with an ethical dilemma related to the field and discipline of Computer Science, Data Science, and Cybersecurity.1. Compare information security threats and attacks. Use instances to prove your argument."In web design, what are the most crucial factors to take into account?" The blockchain is a game-changing technology that offers privacy, authenticity, and integrity. Additionally, it is decentralized, open, and trustworthy. Hash functions and public key encryption are said to be used by blockchains in order to meet these essential security principles, as stated by many experts. Explain how these different cryptographic techniques help to ensure the confidentiality, authenticity, and integrity of the blockchain.
- 1. Why is phishing, and social engineering generally, difficult to address or prevent withtechnological controls?2. An internet site starts distributing a program that gets a popular word processor to send acopy of whatever files it produces to be emailed to a specific email address. Is this avulnerability, an exploit, or a security incident?3. Briefly explain the Cyber-Risk function below:���� ≜ � { Threats , Vulnerability,Asset Value}4. What is a hash function, and what can it be used for?5. a. A Banking systems analysts is reported to siphoning a customer’s account. Brieflydiscuss if this is a vulnerability, an exploit or a security incident?b. Based on the Asset Value, briefly discuss the statement: “Computer security should beperiodically reassessed”. You may be guided by the urgency and criticality of theinformation assets.6. Briefly discuss the extent to which insiders or “frenemies” may pose security challengesto the organization.7. What is a cryptographic key, and what is it…Unitaskers... Good or Bad? In cyber forensics, many tools have a distinct focus/function/role -- other tools do almost everything. --Provide an example, and explain if it is a multi or unitasker. -Provide an argument on whether being a uni or multi is good, bad, or indifferent.What is the rationale behind prioritising privacy preservation during social media usage? One possible approach to elucidate this matter is by providing an illustrative instance.
- Write an essay based on the following: Describe three (3) types of computer crime in detail and include examples of organizations that were impacted by each type of crime. Elaborate on how the impact of computer crime is quantified in these situations. Answers must be 100% original. You should use your own words and ideas. Word count requirement is between 200 and 500 words You may include quotes from outside sources that are up to one (1) sentence long only. All quotes must be cited with the appropriate format. Paraphrasing outside sources without the respective citations and failing to add your own ideas is plagiarism. Taking your own ideas that are published elsewhere and not properly citing them is plagiarism. Copying text generated by artificial intelligence such as ChatGPT is plagiarismCan software that predicts crime pass Constitutional muster? https://www.npr.org/2013/07/26/205835674/can-software-that-predicts-crime-pass-constitutional-muster Can the computer software “PredPol,” and the data it generates, be used by the police as a constitutional basis for stopping someone? Why or why not? Could the data being loaded into “PredPol” be biased and thus affect its usefulness? How can those entering the data be held accountable? Some say “PredPol” could take the biases out of some police stops (i.e., minorities) in that they (police officers) make stops based on what the computer says, not so much on their personal observations, and thus biases are taken out of the picture. What do you think of that argument? Valid or not? Why or why not? include a source1. Which of the following statements are true for artificial intelligence (AI)? [Choose all that apply] AI focuses on the broad idea of making a system execute a task Machine Learning or ML is a subset of AI AI learns on its own without any input data A self-driving car is an example of AI 2. Which of the following type of attack is a pre-cursor to the collision attack? Birthday Dictionary Brute-force Downgrade
- 1Define intellectual property. 2Explain copyright using an example. 3 When is your intellectual property copyright protected? 4 A patent protects an invention. An invention may be a process, amethod, a machine, a device, a new material, a chemical compoundor chemical composition. In South Africa, in order to be patentable,an invention must meet certain criteria. What 3 criteria must bemet.Choose an event; past or present. (from the computer age i.e. post 1985) Provide a full description of theevent and the ethical issues displayed. Relate these to theinfluence of IT and how it enabled unethical behavior and how it could have beenused to prevent it.dont dont dont post copied and existing one sure dislike and compliant strictly warning dont answer without 100% knowledge



