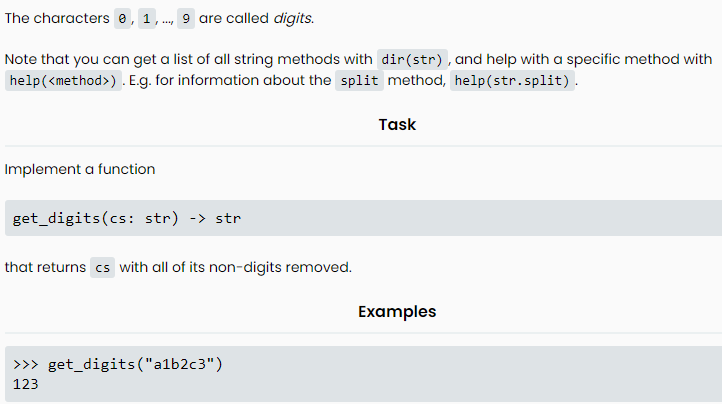
The characters 0, 1,..., 9 are called digits. Note that you can get a list of all string methods with dir (str), and help with a specific method with help (). E.g. for information about the split method, help(str.split). Implement a function get_digits (cs: str) -> str that returns cs with all of its non-digits removed. >>>get_digits ("a1b2c3") 123 Task Examples
Q: ose that L is a language on a
A: Say a group of languages is closed under an operation if the outcome of applying the operation to…
Q: Neumann architecture from other types of desi
A: Architecture by Von NeumannThe underlying design that almost all digital computers have been built…
Q: Assumptions... • Alphabet Σ = {a,b} f(w) = wR o where wΕΣ+ To do in this exercise... Construct a…
A: The Turing Machine is below:
Q: Why is transport layer packetizing required by the network layer protocol? Why can't the segments be…
A: System Layer: The OSI model's network layer is the layer that allows data to be sent between hosts…
Q: Create a Turing machine that computes the function f(x) = 2x + 3, where x is a positive integer…
A: Process Change left most 1 to blank and write two a's at the end of the string on the tape Repeat…
Q: How does assembly language function in the real world?
A: A single assembly language statement is one machine instruction. Assembly Language is…
Q: Domains of conflict When trunks do not form, the Cisco switch command broadcast domains may be used…
A: Use the show interface trunk command to determine whether or not the local VLAN and the peer-native…
Q: Describe the construction of botnets and the DDoS assaults that use them.
A: To be decided: Describe how a botnet is created and how a DDoS attack uses it.
Q: When several individuals attempt to shut down a website simultaneously, it is known as a distributed…
A: Introduction A distributed denial-of-service (DDoS) attack is a deliberate attempt to obstruct a…
Q: DoS attacks may be divided into five different groups
A: i. Smurf Attack: Smurf is actually a network layer distributed denial of service (DDoS) attack in…
Q: Are these five MIS software programs used by any food and beverage companies?
A: Introduction: Safety Chain is a plant management platform that was developed for the purpose of…
Q: How do logical and linear addresses differ from one another, and how do they connect to one another?
A: A botnet is like a network of compromised computers used to commit crimes. A DDoS attack uses…
Q: Instructions Create a program named FlexibleArrayMethod that declares at least three integer arrays…
A: Below I have provided a C++ program for the given question. Also, I have attached a screenshot of…
Q: Describe the relationship between the terms dependability and availability in the context of a…
A: Given: Reliability is a synonym for assurance in a network and denotes that the computer performs as…
Q: What key distinctions exist between the Harvard and von Neumann computer architectures?
A: The question has been answered in step2
Q: Describe the voting process used by the Hough Transform feature extraction technique to locate…
A: Edge detectors, which collect pixels from an idea that sit on a preset curve in the picture space,…
Q: Data communication is the transmission and reception of information between two sites using…
A: Two or more individuals connect and share ideas, thoughts, files, documents, etc., using electronic…
Q: Search for a DoS/DDoS event that took occurred in the preceding three years. It's time to review the…
A: explanation: AWS reported a February 2020 DDoS attack. At its zenith, this attack saw incoming…
Q: Assume you are a systems analyst developing a thorough test strategy. Describe the testing…
A: Network Analyst: A system analyst is someone whoa gathers and compiles data regarding the software.…
Q: in an IP address? What is it? Can mnemonic addresses truly be remembered so easily? How many…
A: Introduction: A device on the internet or a local network can be identified by its IP address, which…
Q: Where can I find out more about the protocols that SSL supports? What distinguishes SSL and SSH from…
A: The following are the differences between SSL and SSH: Answer: Transport layer security (TLS) or SSL…
Q: Is there a better way to defend against DDOS attacks?
A: The question has been answered in step2
Q: Using examples, describe how traditional personnel practices are combined with controls and…
A: Information security: It is defined as the technique to save the data from unauthorized access.…
Q: What makes address alignment such a crucial concept in computer science?
A: Aligned Address: The address must be multiple of the transfer size in order for the access to be…
Q: How do you obtain an IP address? What is it? Can mnemonic addresses truly be remembered so easily?…
A: Introduction: Internet Protocol is a method, or set of guidelines, for addressing and routing data…
Q: hat is meant when someone refers to an operating system? What, in your opinion, are the two core…
A: Answer : It means that some want to use that particular thing so , here someone want to use…
Q: a) Assuming a 1 KB page size, what are the page numbers and offsets for the following logical…
A: Decimal Number:- Decimals are a set of numbers lying between integers on a number line.They are just…
Q: How do network services and applications that use the cloud reach their destination?
A: There are three primary methods to connect: Apps and websites can access cloud resources thanks to…
Q: The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists…
A: Solution: The size of the first set, n = (30+6+24+15+15) = 90 and, the size of the second set, m =…
Q: Please write a c++ programming code that can work on codechum according to the instructions below.…
A: Algorithm: Input the rate of consumption from the user Calculate the total cost as follows. If the…
Q: Expert Systems for the Processing of Natural Language in Relational Database Management
A: The question has been answered in step2
Q: One individual has the ability to launch a distributed denial of service (DDoS) attack.
A: The answer is;-
Q: . What is the output of the following code (assume all libraries are included): Answer: a) True b)…
A: Here we have given multiple question. In first question we need to find the output of the given…
Q: The use of multipurpose microcontroller pins has advantages and disadvantages.
A: Introduction: The pros and disadvantages of using multifunctional pins on a microcontroller are…
Q: What stands out about Ludwig M. von Neumann's architecture?
A: INTRODUCTION: In the majority of computer systems, the CPU receives instructions and data from an…
Q: We don't understand operating systems well enough to discuss how they operate. What is meant by the…
A: What is an operating system? An operating system (OS) is a program that, subsequent to being at…
Q: What is the importance minimum requirements system? of application of in building design
A: Introduction Software requirements artifacts are organized and structured using requirements…
Q: use Assimbly Language of 8086 MP to develop a program to find the greater number between two number…
A: In this question we have to use assembly language 8086 for programming to find greater number…
Q: Explain the development and application of a botnet for DDoS assaults.
A: to construct a botnet and then make use of it in DDoS attacks. to construct a botnet, one must: The…
Q: Describe the voting process used by the Hough Transform feature extraction technique to locate…
A: Definition: Edge detectors, which collect image pixels on desired curves in the picture space, are…
Q: Discuss Classical Ciphers
A: Classical ciphers were developed before computers were invented. These are in contrast to mechanical…
Q: How is the term "firewall" used in network topologies and what does it mean in terms of network…
A: Introduction: A firewall is a type of equipment used to filter network traffic in the context of…
Q: Is there a type of operating system that I am unable to utilize because I lack the necessary funds?
A: The answer is given in the below step
Q: ributed denial of service assault led by one person possible
A: How is a distributed denial of service assault led by one person possible?
Q: A firewall's function is to keep hackers out of your computer. When using packet filtering software,…
A: FIREWALL TYPES:- Protocol filtering Firewalls Gateways at the circuit level Gateways at the…
Q: b. c. (p Ar) (qVr) → r →r
A: Here we have given the propositions p, q, and r, p is true, q is false, and r's status is unknown…
Q: Draw an ER diagram for the following scenario: 1. A designer has a store of designer dresses both…
A: Here is the ER diagram of the above problem. See below steps
Q: Write the sentence in symbolic form. Use v, p, and t as defined below. v: "I will take a vacation."…
A: Given, v: "I will take a vacation." p: "I get the promotion." t: "I will be transferred." We need to…
Q: DoS attacks frequently overburden servers, systems, or networks with traffic, blocking access for…
A: In a Denial of Service attack, a person with malicious intent attempts to boost traffic to specific…
Q: In matlab 1. For the following 3-bit (Z-2¹) image, sketch its histogram, and then sketch it again…
A: Here is the matlab code. See below step.
please use python and the .isdigit() function if possible. thank you so much
Step by step
Solved in 3 steps with 1 images

- do the changes in this program according to the given instruction like coaches instead of teachers,sports name instead of courses etc, import java.util.*;class CourseManager{//toatl students each section can holdstatic int max_Students;//mapping of each sections w.r.t to courseHashMap<String,ArrayList<Section> > courses ; //constructor for CourseManagerpublic CourseManager(int max){max_Students = max;courses = new HashMap<>();}//class Person which will be used by teacher and students to inherit its propertiesstatic class Person{String name;int age;public Person(String name , int age ){this.name = name;this.age = age;}}//teacher classstatic class Teacher extends Person{int id;public Teacher(int id , String name , int age ){super(name , age );this.id = id;}}//student classstatic class Student extends Person{int id;public Student(int id , String name , int age ){super(name , age );this.id = id;}}//section classstatic class Section{int section;String course ;Teacher…I have to implement a SubstringGenerator (class) that generates all substrings of a string recursively. For example, the substrings of the string “rum” are the seven strings “rum”, “ru”, “r”, “um”, “u”, “m”, “” Hint: First enumerate all substrings that start with the first character. There are n of them if the string has length n. Then enumerate the substrings of the string that you obtain by removing the first character. Here is what your output should look like after your project is completed. (The order of your substrings is not important, if your generator produces all substrings correctly). Substrings of "ab" Actual: '' 'b' 'a' 'ab' Expected: '' 'b' 'a' 'ab' Substrings of "abc" Actual: '' 'c' 'b' 'bc' 'a' 'ab' 'abc' Expected: '' 'c' 'b' 'bc' 'a' 'ab' 'abc' Substrings of "abc123" Actual: '' '3' '2' '23' '1' '12' '123' 'c' 'c1' 'c12' 'c123' 'b' 'bc' 'bc1' 'bc12' 'bc123' 'a' 'ab' 'abc' 'abc1' 'abc12' 'abc123' Expected: '' '3' '2' '23' '1' '12' '123' 'c' 'c1'…Implement the Plates class buildMap function so that it populates the HashMap with the state abbreviations as keys and the counts of how many each appear in the file as values. Sometimes, the parking attendant will add special notation to help her remember something about a specific entry. There are just non alphabetic characters that she adds to the state - your program should ignore these characters so that an entry like NY* still counts toward the NY plate count. She is also very inconsistent with how she enters the plates. Sometimes she uses upper case, sometimes lowercase, and sometimes she even uses a mix. Be sure to account for this in your program. Only add information for plates in New England (Maine, New Hampshire, Vermont, Massachusetts, Rhode Island, and Connecticut). Plates.java import java.util.Arrays; import java.util.HashMap; import java.util.HashSet; import java.util.Map; import java.util.Set; public class Plates { private Map<String, Integer> plateMap;…
- The split method in the String class returns an array of strings consisting of the substrings split by the delimiters. However, the delimiters are not returned. Implement the following new method that returns an array of strings consisting of the substrings split by the matching delimiters, including the matching delimiters. public static String[] split(String s, String regex) For example, split("ab#12#453", "#") returns ab, #, 12, #, and 453 in an array of String and split("a?b?gf#e", "[?#]") returns a, ?, b, ?, gf, #, and e in an array of String.Please implement in Java implement a keyed bag in which the items to be stored are strings (perhaps people’s names) and the keys are numbers (perhaps Social Security or other identification numbers). So, the in- sertion method has this specification: public void insert(String entry, int key);// Precondition: size( ) < CAPACITY, and the // bag does not yet contain any item// with the given key.// Postcondition: A new copy of entry has// been added to the bag, with the given key. When the programmer wants to remove or retrieve an item from a keyed bag, the key of the item must be specified rather than the item itself. The keyed bag should also have a boolean method that can be used to determine whether the bag has an item with a specified key. In a keyed bag, the pro- grammer using the class specifies a particular key when an item is inserted. Here’s an implementation idea: A keyed bag can have two private arrays, one that holds the string data and one that holds the corresponding…Improve the given code below, make sure that the code will require input from the user. Problem: Write a JavaScript function that would accept a string and return the reverse of that string. const reverse = (str) => {const arr = []; //stores character in rev orderconst len = str.length; //finds the length of the stringlet i;for(i = len; i >= 0; i--)arr.push(str[i]); //adds the chars of str to arrreturn arr.join('');} let stringTest, reverseString; //for dummy stringstringTest = "john gabriel";reverseString = reverse(stringTest); console.log("Num3");console.log(`Reverse of the string "${stringTest}" is: "${reverseString}"`);console.log("\n");
- In java, Implement a method that removes all duplicates. Keep the first instance of the element but remove all subsequent duplicate elements.public void removeDuplicates() see the picture for the right output. Given files: Demo6.java public class Demo6 { public static void main(String[] args) { MyLinkedList<String> list = new MyLinkedList<>(); TestBench.addToList(list); TestBench.addToList(list); TestBench.addToList(list); TestBench.addToList(list); for (int x = 0; x < list.size(); x += 1 + x/3) { System.out.println("Removing element at index: " + x); list.remove(x); } System.out.println("Result"); System.out.println(list); System.out.println("Shuffling"); list.shuffle(7777); System.out.println(list); System.out.println("Removing duplicates (keeping first instance)"); list.removeDuplicates(); System.out.println(list); }} TestBench.java import java.util.AbstractList; public class TestBench { public static…Improve the given code below, make sure that the code will require input from the user. Problem: Write a JavaScript function that would accept a string and returns its letters in alphabetical order. function alpha(str){let res;var arr = str.split(""); //splits the strres = arr.sort().join(""); //sorts arr && forms to a strreturn res;}console.log("Num5");console.log(alpha("CSIT201"));Complete the method below that prints all elements that are in both Set<String> s and Set<String> t. Each matching element should be followed by a space. What can I change to make it work? import java.util.Set;import java.util.Iterator; public class Sets{ public static void printMatches(Set<String> s, Set<String> t) { System.out.print("{ "); while(in.hasNext()){ String next = in.next(); { if((s.contains(next))&& (t.contains(next))){ System.out.print(next+" "); } } System.out.println("}"); }} import java.util.Set;import java.util.TreeSet;import java.util.Arrays; public class SetsTester{ public static void main(String[] args) { Set<String> set1 = new TreeSet<>(Arrays.asList("Bob", "Bill", "Sally")); Set<String> set2 = new TreeSet<>(Arrays.asList("Sam", "Bob", "Frank")); Sets.printMatches(set1, set2);…
- Your tasks Implement the methods marked with ??? package percentiles: /** * Given a non-empty sequence of elements of type T, returns the smallest element e * in the sequence for which it holds that at least p percent of the elements in the sequence * are smaller or equal to e. * Note the special cases: * - when p == 0, the result should be the smallest element in the sequence * - when p == 100, the result should be the largest element in the sequence * If the sequence is empty, java.lang.IllegalArgumentException is thrown. * * For a sequence of length n, the method should make at most n*log(n) * [again, here log means base-2 logarithm] comparison operations between * the elements in the sequence. * Furthermore, assuming that comparison is a constant-time operation, * the whole method should run in O(n*log(n)) time. * Hint: you can assume that the "sorted" method of Seq performs at most n*log(n) comparisons for * sequences of…in python """Write a function get_new_grades, such that given a string of grades as an input parameter,returns two objects:the initial grades as a list of numerical valuesas well asa new list with the numerical values, where the scores that are less than 50 are replaced by 50. """The String class implements Comparable, which means that two strings can be compared to each other. However, the default implementation orders strings based on the ASCII values of their characters, which means that strings that begin with an uppercase letter are always ordered before strings that begin with a lowercase letter. This means that the string “Zoo” would be ordered before the string “aardvark”. Write a Comparator that compares two strings alphabetically so that “aardvark” is ordered before “Zoo”. Hint: convert both strings to upper or lowercase before comparing them.

