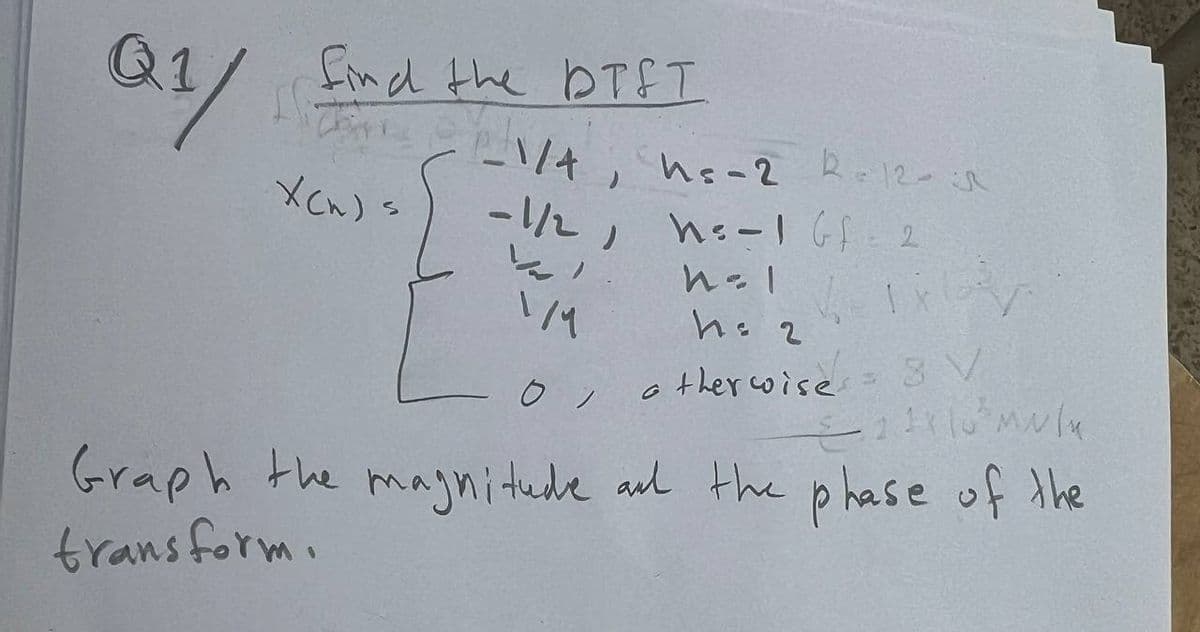
the DTST Q1/ find the 1/4, ne-2 2-12- XCW) X(n) s -1/2, hs-1 G2 ارا h=1 1/ h = 2 O, otherwise. 8 V Graph the magnitude and the phase of the transform.
Q: Alert dont submit AI generated answer.
A: I. FCFS (First-Come, First-Served):| P1 | P4 | P2 | P5 | P3 | P6 |0 11 21 49 65 67…
Q: 1. Let Σ be an alphabet. Prove or disprove that for every language L over alphabet Σ, if L2 = L,…
A: Given propertyIn this context, we're provided with a fundamental property of a language L. This…
Q: Suppose we have the instruction Load 1000. Given memory and register R1 contain the values below:…
A: To determine the value loaded into the accumulator (AC) when using indexed addressing mode with the…
Q: Without using excel.
A:
Q: You need to establish a procedure for your organization on how to validate a new forensics software…
A: FEEL FREE TO ASK FOR CLARIFICATIONS.
Q: Why is the pipelined hash join not commonly used in a conventional DBMS? (A) It immediately produces…
A: The question is asking about the reasons why pipelined hash join is not commonly used in a…
Q: If you are issued the computer to take outside of work, does that give you the right to use it for…
A: Approach to solving the question: Detailed explanation:Whether or not being issued the computer to…
Q: 3. Draw the combinational circuit that directly implements the Boolean expression on logisim/circuit…
A: Here we have solved the questions,Q1.Q2.Q3.Hope you understood well. Give me a good ratting.
Q: What value will be displayed by the println statement and why?int [] first = {5, 7, 3, 2, 9, 11};int…
A: When you assign int[] second = first;, you're not creating a new array. Instead, you're just…
Q: Based on the photo attatched, list each step in simple terms and explain each step in simpler terms
A: To map problem domain objects to object-persistence formats, such as RDBMS tables, the following…
Q: what Items to consider and include methods for measuring success for a cyberattack program and who…
A: The objective of the question is to understand the key considerations and methods for measuring the…
Q: a Java method that takes an array of integers as its only parameter and returns the "centered"…
A: Step 1: You can achieve this by sorting the array, removing duplicates, and then calculating the…
Q: Don't use ai Describe the concept of ACID properties in database systems
A: ACID properties are the fundamental principles that ensure data reliability and integrity within…
Q: part b) Draw the circuit
A:
Q: w |w Consider alphabet Σ = {0,1} and language L = = {wες : Σw # i=1 i=1 regular. Σ (1 - w;)}. Prove…
A: Let's dive deeper into the explanation of why the language L defined as L = {Σ^i: Σ(1-0)^i} is a…
Q: For the duration of this course, you will be the Chief Data Officer (CDO) of a fictional firm of…
A: References:Luengo, J., García-Gil, D., Ramírez-Gallego, S., García, S., & Herrera, F. (2020).…
Q: Consider alphabet Σ = {0,1}. Prove or disprove that for all languages L₁,L₂, L over Σ, if L₁ CL C L2…
A: Case 1: Proof You correctly identified that if L₁ and L₂ are decidable (meaning there are Turing…
Q: Create a PDA that recognizes the following context free language with terminals {a,b,c} L= {wck | wE…
A: (i) Algorithm:The algorithm for the PDA is to read in the string of symbols from the input stack and…
Q: In JAVA
A: It seems like the text you provided is a mixture of project requirements, course descriptions, and…
Q: Provide the full C++ main.cpp, mystring.cpp and mystring.h. Part of the output is provided below
A: Step 1:Extraction Operator (>>): This operator reads input into a temporary non-dynamic array,…
Q: Don't use AI to do it.Given the modified single-cycle processor shown below, what are the values (in…
A: To determine the values of the main control signals and other processor components at 1950 ns in the…
Q: Help with question #3 please
A: Data Segment:Defines the array arr containing integers {3, 5, 8, 4, 1, 9, -2}.Defines the integer n…
Q: Please identify the correct statement(s) for the following code snippet from the script: while…
A: Let's break down the code snippet and identify the correct statements:It saves the address of the…
Q: Hello, would you be able to help me withpart C? I'm having difficulty with them and would really…
A: Sure, I'd be happy to help you with part C. Let me first label the parts:(a) f(x,y) = xy + xy(b)…
Q: For the given Two Link Manipulator (Fig 1), If 11=1m and 12=1m 01-40° and 02=10° Calculate the…
A: The objective of the question is to calculate the coordinates of the end effector of a two-link…
Q: IN JAVA PLEASE REST OF THE SAMPLE RUN: --------------------------------------------------- Main Menu…
A: Sure, let's start by developing the Java program step by step. We'll begin with the basic structure,…
Q: Please help me with this Operating systems principles homework project (NOT GRADED) Job Object Class…
A: References: Androulaki, E., Barger, A., Bortnikov, V., Cachin, C., Christidis, K., De Caro, A., ...…
Q: Make a Python Program That Accomplishes the Following Three Parts Based on the Given Chart of…
A: Approach to solving the question: Detailed explanation: Examples: Key references:Computer Science
Q: 19. In NLP this refers to the separation of words from a phrase. In Python, this often results in a…
A: The answer is B) Tokenization. Tokenization in NLPIn Natural Language Processing (NLP), tokenization…
Q: Can you run the code and provide an interpretation to all the graphs.
A: Let's break down the code step by step to understand its workings: 1. **Imports**: The code imports…
Q: overview of SQLJ and JDBC.
A: FOR MORE INFORMATION, PING ME HAPPY LEARNING
Q: Given integer inputs howMany and maxNum, generate an array of howMany unique random integers from 0…
A: Introduction: In this program, we aim to generate an array of unique random integers within a given…
Q: Student Name: 8) Consider the following ciass definitions. public class LibraryID{ private String…
A: To compare `LibraryID` objects `one` and `two` inside the if statement, you would just call the…
Q: Given main(), complete the program to add people to a queue. The program should read in a list of…
A: Approach to solving the question: Here's the completed Java program that adds people to a queue,…
Q: A heap is stored using an array as follows: INDEX C ONTENTS 0 1 2 3 4 5 6 90 80 75 60 78 30 20 Show…
A: Approach to solving the question:To insert the value 85 into a max heap correctly and solve this…
Q: Alert dont submit AI generated answer. please help! 1. Consider the following graph. Find the…
A: Given Dijkstra's algorithm finds the shortest path from one vertex to all other vertices. To find…
Q: Refer to image and provide correct solution for positive feedback Computation and Automata
A: The correct solution for positive feedback would be: G=({S,A,B}, {a,b}, S, {S→BB|b, A→a|b|SS,…
Q: This is a lesson from applied cryptography (institute of information security)
A: Let's break it down step by step: Step 1: Apply the Euclidean algorithm to find the GCD of 23 and…
Q: What is the function of a ModelGen operator? A It identifies fundamental conflicts and devises…
A: The ModelGen operator is a concept used in computer science, specifically in the field of data…
Q: PLEASE DON'T USE STRUCTS Using C programming language write a program that simulates a variant of…
A: Here's a C program that simulates the Tiny Harvard Architecture as described:```c #include…
Q: Given integer inputs howMany and maxNum, generate an array of howMany unique random integers from 0…
A: Generating an Array of Unique Random Integers : Approach: To design this program, you need to create…
Q: IN JAVA PLEASE In the course menu of the final project, don't delete class if a student is enrolled…
A: Step 1: Understand the problem The problem requires you to create a Java program that handles…
Q: Would you be able to help me with this issue? I'm finding it challenging to grasp and would…
A: To show that the set T={(i,j,k)∣i,j,k∈N} is countable, we can establish a bijection between T and…
Q: Alert dont submit AI generated answer.
A: The objective of the question is to design and configure a network for two offices using Variable…
Q: The "MULTIEQUAL" p-code operator has not been considered in the script. Please identify the correct…
A: 1. One can simply add PcodeOp.MULTIEQUAL into 'binary_operators' and the resulted script will be…
Q: Develop a logic network for the sequence of activities listed in the table. Activity PIB…
A:
Q: Method: Back up MySQL Database Using the Binary Log. M ril-
A: ----------------------------------------------------------------------Detailed…
Q: 8. Please write in complete sentences and in as much detail as possible What is the principal…
A: Unveiling the Depths of Network Traffic: RMON2's Layer 2 ProwessRemote Network Monitoring (RMON) has…
Q: 2. Assume a computer that has 32-bit integers. Show how each of the following values would be stored…
A: Let's break down how each value would be stored sequentially in memory, starting at address 0x100,…
Q: Please check the answer twice and add explanation to.every step Note - don't use AI answer ( i will…
A: The hexadecimal number is:0001 -> 10111 -> 71000 -> 81111 -> F0000 -> 00000->…
Step by step
Solved in 2 steps with 4 images

- Normalize the spectra data set to unity: For X= [0.23, 0.025, 0.54, 0.58, 0.18, 0.64, 0.29, 0.012, 0.72, 0.35] ?Q2(b) A signal travels from point A to point B. At point A, the signal power is 300 W. At point B, the power is 280 W. What is the attenuation in decibels?a) Draw the graph of the NRZ-I, Manchester & differential Manchester using data stream01010101, assuming that the last signal level has been positive
- Draw the graph of the NRZ-L, NRZ-I, Manchester scheme, differential Manchesterscheme using each of the following data streams,assuming that the last signa11evel has been positive. From the graphs, guess thebandwidth for this scheme using the average number of changes in the signal level.a. 00000000b. 11111111c. 01010101d. 001100115.Calculate the Qexp of the outlying result in the data set: 7.88, 5.25, 5.55, 5.81, 5.86, 5.38, 5.64, 6.03.Draw the graph of the NRZ-L scheme using each of the following data streams,assuming that the last signa11evel has been positive. From the graphs, guess thebandwidth for this scheme using the average number of changes in the signal level.Compare your guess with the corresp.onding entry in Table 4.1.a. 00000000b. 11111111c. 01010101d. 00110011
- If true, then Codewords (n) and datawords (k) are dissimilar because k=n+FCS (Frame Check Sequence).A computer need to send three data items EB716, C5D16 and AC916. By using checksum error detection method, find the checksum that need to be sent to the receiver (show yourwork).Please plot. y = -2pi to 2pi (1) x1 = sin(y)cos(y) (2) x2 = sec(y)sin(y) (3) x3 = sin(y-0.5)*cos(y) in a frame
- MCQ 3116: In a time-domain plot, the horizontal axis is a measure of ________. a. TIME b. frequencyQUESTION 11 The 8284 PCLK frequency is ______ the CLK frequency. half twice 3 times 1/3The data word 10101110001101 is given for transmission. Draw the following encoding formats. NRZ-L NRZ-I Bi-phase Manchester RZ Differential Manchester

