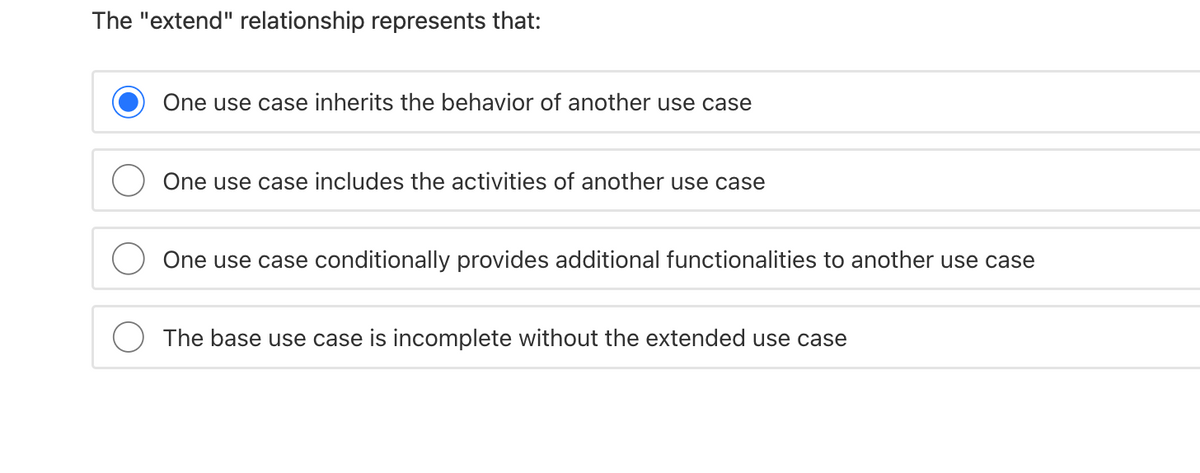
The "extend" relationship represents that: One use case inherits the behavior of another use case One use case includes the activities of another use case One use case conditionally provides additional functionalities to another use case The base use case is incomplete without the extended use case
Q: What may be the commonalities between the meanings of Feeling and Agreeableness? Do your scores on F...
A: According to the Bartelby guideline we are suppose to answer only one question at a time Kindly repo...
Q: nvert the following python regex to a DFA: ^(A?(B|CD)*A+
A: SUMMARY: -Hence, we discussed all the points.
Q: When compared to more rigorous, computer-aided algebraic methods such as those employed in process s...
A: When compared to more rigorous, computer-aided algebraic methods such as those employed in process s...
Q: Library Management Software Application will be implemented Draw the classes in the system and the r...
A: To elaborate on its principles, the Class Diagram for Library Management System is provided with an ...
Q: A circuit is constructed with four resistors, one inductor, one battery and a switch as shown. The v...
A:
Q: Decide on three new approaches to software development, each representing a shift away from rigid ad...
A: Multiple approaches and models for tracking the progress of a software project, as well as the proje...
Q: How Many? Code in C language
A: ALGORITHM:- 1. Take the input for the n. 2. Take n elements input in the array. 3. Take the value of...
Q: An interesting GUI component in Java is the Slider. Indeed, sliders allow a user to specify a numeri...
A: The thermometer can be implementer using the JSlider class and the label can be printed using the JL...
Q: What is the origin of the term "direct access device" for magnetic disks?
A: Introduction: A direct-access storage device (DASD) is another term for secondary storage devices, s...
Q: Describe block distribution. Parallel processing backs up your response with examples and graphics.
A: Parallel processing refers to the simultaneous processing of several assignments across multiple pro...
Q: What exactly is a microcontroller? Its constituents, shown in a tidy figure. Provide citations indic...
A: Intro It is called a integrated circuit which is used in many electronic devices .it is also called ...
Q: Which relational algebra operators can be used to join a pair of tables that are not union-compatibl...
A: Introduction: Relational Algebra: It is a procedural query language that accepts a Relation as input...
Q: Discuss why many IT professionals may disregard project cost management and how this may impact thei...
A: Intro It is usually discovered that within IT project management the stress on cost accounting is un...
Q: In what ways does a nonblocking cache benefit the user?
A: Answer : A non-blocking cache is a type of cache that can service multiple memory requests at the sa...
Q: What potential issues do you believe could occur in terms of ownership rights for software produced ...
A: Introduction: Open source is defined as anything that may be shared and modified by the general publ...
Q: What exactly is a memristor, and how does it save information on a computer?
A: Introduction: To go back to its original 1971 definition, a memristor is a fourth fundamental circui...
Q: What exactly is an operating system? Name a few popular operating systems.
A: Operating System: The operating system (OS) is a graphical interface that connects a computer user t...
Q: 3) Given the grammar below, (a) list all the terminals and (b) list all the non-terminals. ASSIGN - ...
A: Please upvote me please. I need it badly. I am providing you the correct answer below. Terminals...
Q: Call method "calculateUpperSectionCategory"
A: When method call is executed, control jumps to method definition and executes statements within it. ...
Q: Advanced Physics Cisco's SAFE has several benefits. Which is NOT a benefit? 1. Collaboration of...
A: here we have given appropriate option for the given questions, you can find them in step 2:
Q: You've learned that Software Design is both a process and a model. It is a guide for an easier/bette...
A: In order to develop any software, the framework which is used to define the system is known as SDLC ...
Q: In terms of the bus that connects the CPU and the memory, would you propose using synchronous or asy...
A: Synchronous buses are clocked, and instructions are executed only at the clock ticks. Every device i...
Q: Which of the following statements is TRUE about abstract classes in Java? A. An abstract class imple...
A: An abstract method is a method which has only declaration and definition is provided in some other c...
Q: at exactly is seek ti
A: Below the exactly is seek time
Q: In the space below. create your own Mind Map. Add key information you have taken from activity 122.
A: Here is the detailed explanation of the mindmap.
Q: 6. What is the output of the following code class A { public int i; void display () { System.out.pri...
A: Below the output of the following code
Q: In a text editor, open index.htm. Enter your name and today’s date where indicated in the comment se...
A: Given; We need to write a html code that show Enter name field and date field .
Q: Solve the following KARNAUGH maps; C'D' C'D CD CD' C'D' C'D CD CD' A'B' 1 A'B' A'B 1 1 A'B AB 1 1 AB...
A: KARNAUGH MAPS
Q: Develop following C++ functions using doubly linked list (1) Find a key value from the user (2) Find...
A: Given:
Q: Explain how the set-associative cache concept combines the concepts of direct cache and fully associ...
A: Introduction: The set-associative cache is a compromise between entirely associative cache and direc...
Q: In this section, we will look at the function that wireless networks play in developing countries. W...
A: -The wireless network allows the average man in developing countries to connect to the rest of the g...
Q: Identify the seven different types of data instructions and describe each one.
A: Sorts of directions Diminished Instruction Set Computer (RISC)Complex Instruction Set Computer (CISC...
Q: What form of scanning could be used to determine whether Telnet is operating on a server?
A: Solution Port scanning is a sort of scanning that may uncover the presence of Telnet on a server.
Q: What is zoned-bit recording, and how does it work
A: Zone bit recording (ZBR) is a mechanism in use by disc drives to optimise the tracks for enhanced da...
Q: Type the program's output import java.util.Scanner; public class BreakAndContinue { public static vo...
A: As given, we need to find out the output of the given code. Given code - import java.util.Scanner;p...
Q: Which VLAN on a switch is responsible for managing untagged frames?
A: INTRODUCTION: It is possible to create a virtual local area network (VLAN) to link devices that are ...
Q: A class needs to contain two generic methods with different number of parameters. Explain the mechan...
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: For the following logic circuit, find the Boolean expression and the input output table A
A: Above is AND gate. For two inputs, it is true only if both the inputs are true. We write it as XY ...
Q: (Information technology and computer networking) Explain the similarities and differences between th...
A: Introduction: Is there a distinction between ICMP and ICMPv6? The Internet Control Message Protocol ...
Q: Write Java program that randomly generate two Integers between 1 and 10 as input and perform an oper...
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: Gene...
Q: To manage user security privileges, network administrators construct domain groups. What is the purp...
A: Purpose of creating domain groups is given below :
Q: You are organizing a big dinner party for your company retreat. To increase social interaction among...
A: Answer is given below-
Q: I want to throw an IllegalArgumentException type exception in my code even if it does not arise on i...
A: when illegal argument is passed within a method then at runtime an expception called illegalArgument...
Q: What gadget is required to be installed on a DSL network in order to protect the sound quality of ph...
A: Digital subscriber line (DSL):- Digital subscriber line (DSL) is the technology that is used to tran...
Q: On a single slide, summarise information security and upgrade requirements.
A: Firstly let us know about Computer Security: In recent years, the definition of computer security ha...
Q: (b) Given the following logical circuit with three inputs A, B and C: output i. Use the boolean alge...
A:
Q: Write a program which should consists of a user defined function “Task ()”. Pass 1D array to the ...
A: Let's see the code in the next steps
Q: How CPU registers are related with modern computers in terms of handling logic circuits
A: The CPU( Central Processing Unit ) is the brain, heart, tower and central part of the computer. CPU ...
Q: For the instruction being executed: add $s1, $s2, $t0 use the following delays for each block/action...
A: Explanation: First, read the registers. and, Instruction access memory. and, Decode and register fil...
Q: What is the advantage of using sliding window over the stop-and-wait protocol as a solution to the r...
A: Pleae refer below for your reference:
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Step by step
Solved in 2 steps

- The act of assigning a value to a variable or any other entity using the Assignment operator is a fundamental operation in programming. It involves the transfer of a specific value to the designated entity, thereby replacing any previous value that may have been stored in it.What are the distinguishing elements of a good use case? There are some similarities between use cases and their attributes.Job portal system: This system allows the students to search and apply for jobs etc. online. The manager can use the system for posting and deleting job offers etc. Create your own case study (problem statement) for the above application and Draw the use case diagram Class diagram with at least 4 classes and explain all the relationships Draw a DFD-0 for this application
- 1.Write all functional requirements which are required to implement “Search a cab” use case. 2.Explore any two high priority quality attributes which are very important for “Get a cab” application with brief rationale. 3. Write all possible testable non-functional requirements for above explored quality attributes. 4.Draw a use case diagram for “Get a Cab” application ‘Get a Cab’ is a Smartphone application. It will search cabs for the passenger, provide them with security by reminding them about their luggage and it will also allow the user to inform the police with the help of a one-click button. This application facilitates the guardians to trace the location of their loved ones. It also lets passengers locate a driver at any instance to overcome all time related issues. If the passenger wants to avail the services of the same driver in future, he/she can add the driver to the favorite list, stored in the application. 5.Write a detail use case for “Search a Cab” function. For…Job portal system: This system allows the students to search and apply for jobs etc. online. The manager can use the system for posting and deleting job offers etc. 1.Create your own case study (problem statement) for the above application 2.Draw the use case diagram 3.Class diagram with at least 4 classes and explain all the relationships 4.Draw a DFD-0 for this applicationwrite an expression that can be used to access the structure members in each of the following parts: d) Member firstName of the structure pointed to by customerPtr.
- Create a Sequence model (Application layer) for the following “Borrow Books” Use case for Students with a Valid ID and No Overdue Books or Fines from the Use-Case Description: Normal Flow of Events: 1. The Borrower brings books to the Librarian at the checkout desk. 2. The Borrower provides Librarian their ID card. 3. The Librarian checks the validity of the ID Card. If the Borrower is a Student Borrower, Validate ID Card against Registrar’s DB. If the Borrower is a Faculty/Staff Borrower, Validate ID Card against Personnel DB. If the Borrower is a Guest Borrower, Validate ID Card against Library’s Guest DB. 4. The Librarian checks whether the Borrower has any overdue books and/or fines. 5. The Borrower checks out the books. Alternate/Exceptional Flows: 4a. The ID Card is invalid, the book request is rejected. 5a. The Borrower either has overdue books, fines, or both, the book request is rejected.What does the relationship marked "extend" indicate in the use case diagram?What do you mean by Use cases and actors Define Use case and Actor
- A multinational company hired you to develop their employee management system. There are many employees working in different positions and departments. Make a structure for each department telling the number of employees in that department including the heads. Also each position has a reporting head defined in the chart given below also state the reporting head in the employee structure. Make a structure for all the employees holding their bio – data which includes: Name Employee ID CNIC Phone Number Age Department Position Add more necessary variables as required. Create functions to perform these operations: Add Employee Modify Employee Delete Employee Print All Employee Display Details of all Employees Search Employee using Position Search Employee using Department Search Employee using Employee idA multinational company hired you to develop their employee management system. There are many employees working in different positions and departments. Make a structure for each department telling the number of employees in that department including the heads. Also each position has a reporting head defined in the chart given below also state the reporting head in the employee structure. Make a structure for all the employees holding their bio – data which includes: Name Employee ID CNIC Phone Number Age Department Position Add more necessary variables as required. Create functions to perform these operations: Add Employee Modify Employee Delete Employee Print All Employee Display Details of all Employees Search Employee using Position Search Employee using Department Search Employee using Employee id I want this program code in C language Please.A multinational company hired you to develop their employee management system. There are many employees working in different positions and departments. Make a structure for each department telling the number of employees in that department including the heads. Also each position has a reporting head defined in the chart given below also state the reporting head in the employee structure. Make a structure for all the employees holding their bio – data which includes: Name Employee ID CNIC Phone Number Age Department Position Add more necessary variables as required. Create functions to perform these operations: Add Employee Modify Employee Delete Employee Print All Employee Display Details of all Employees Search Employee using Position Search Employee using Department Search Employee using Employee id Using C Language

